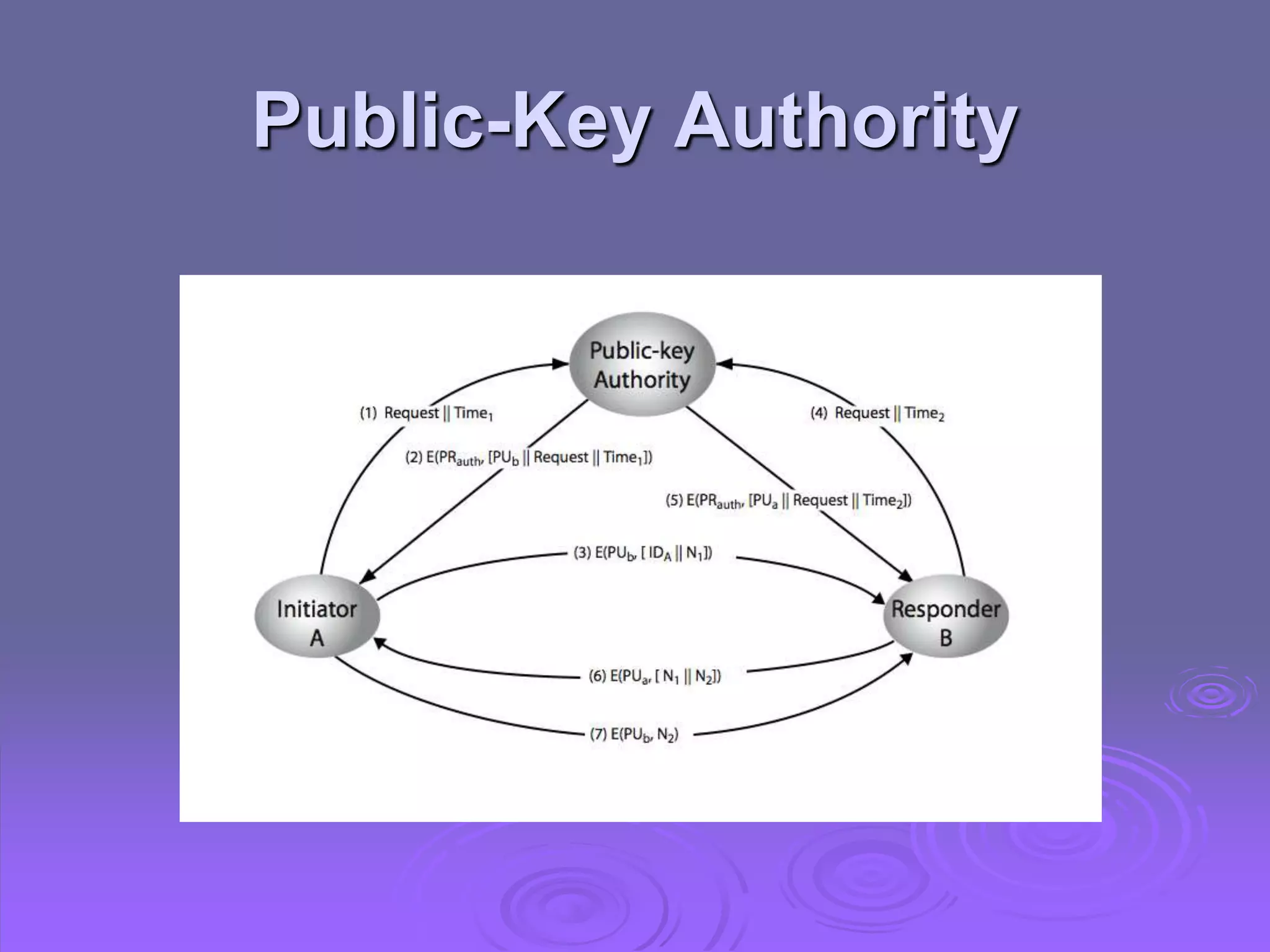
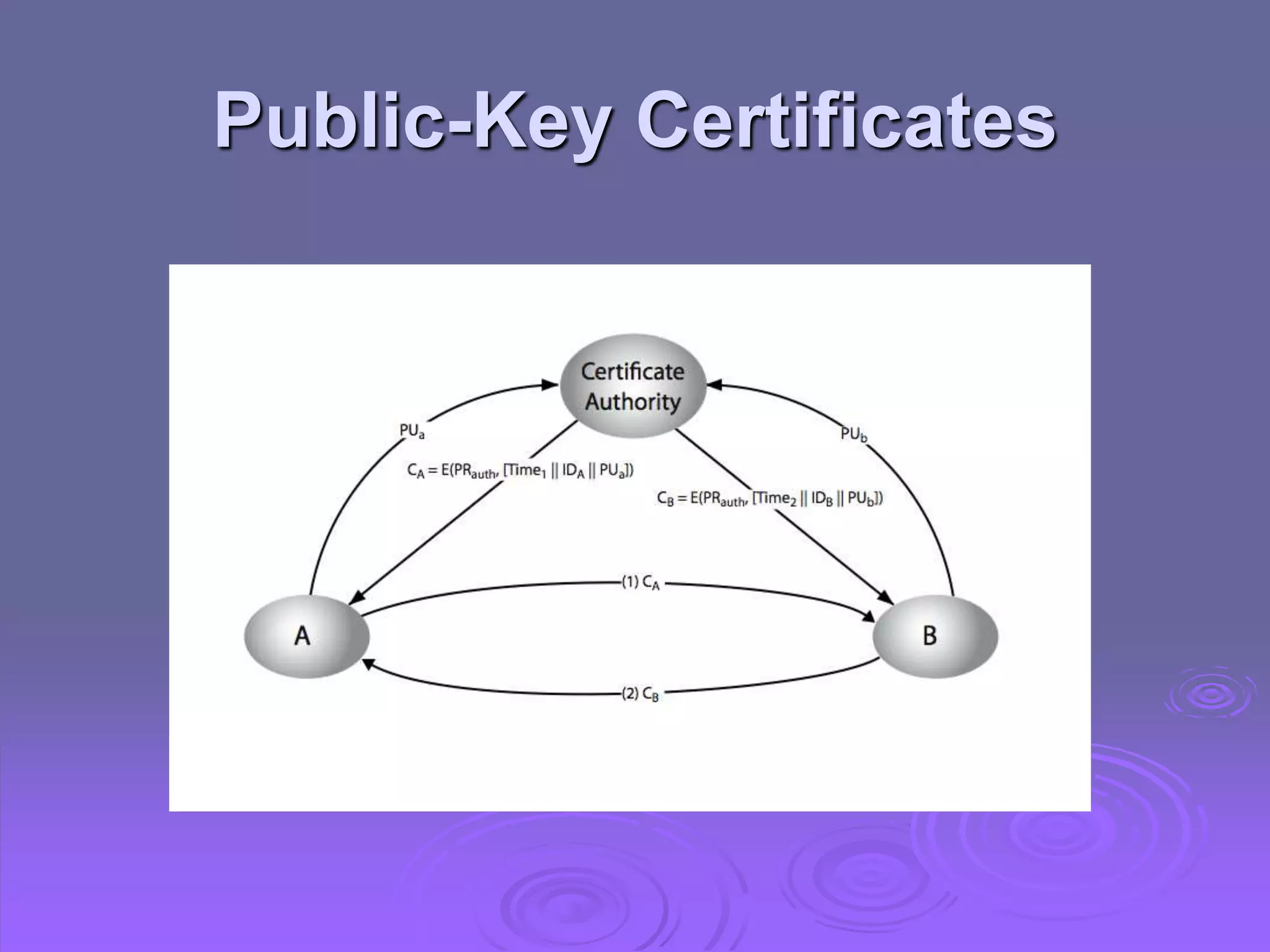
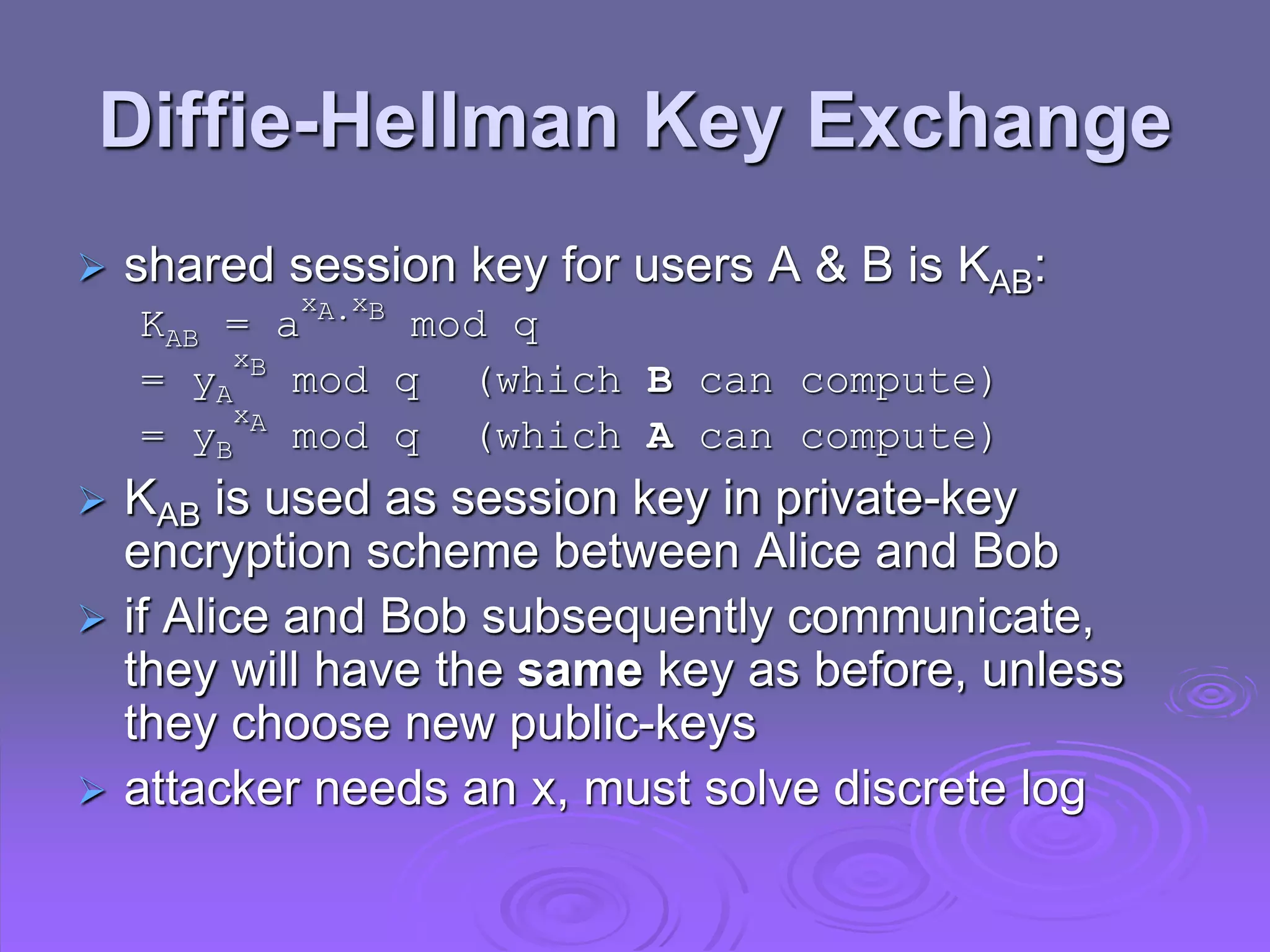
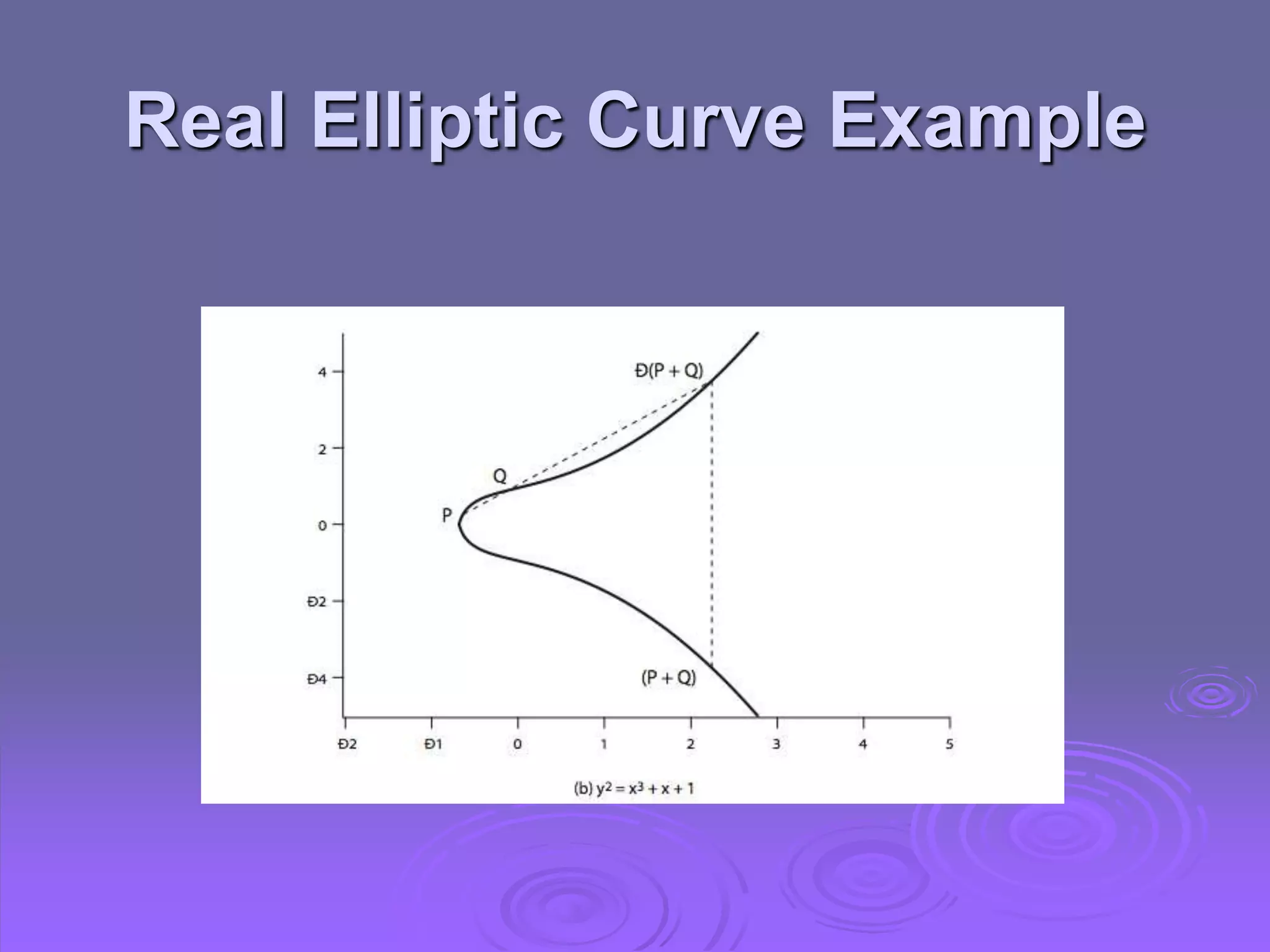
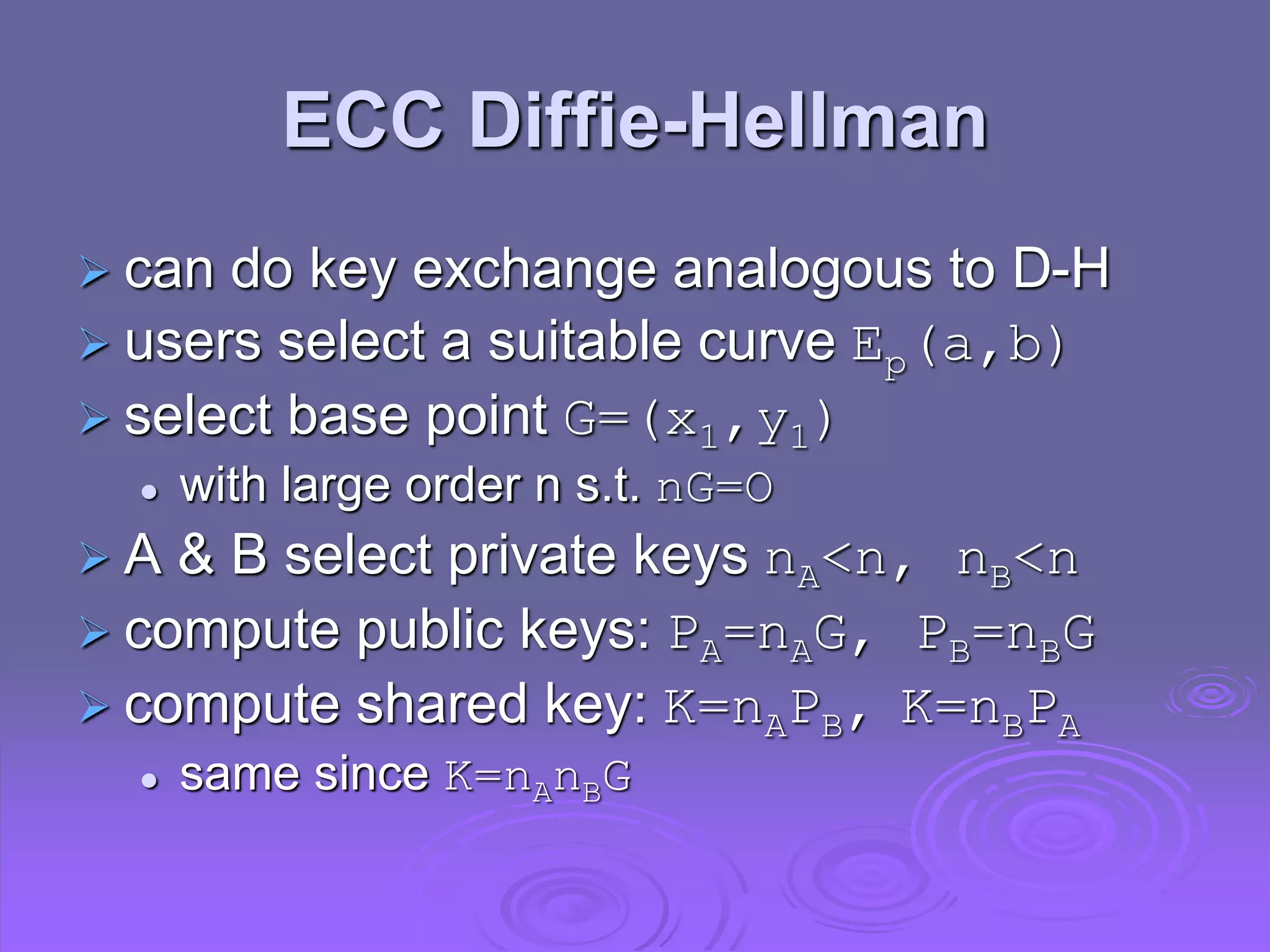
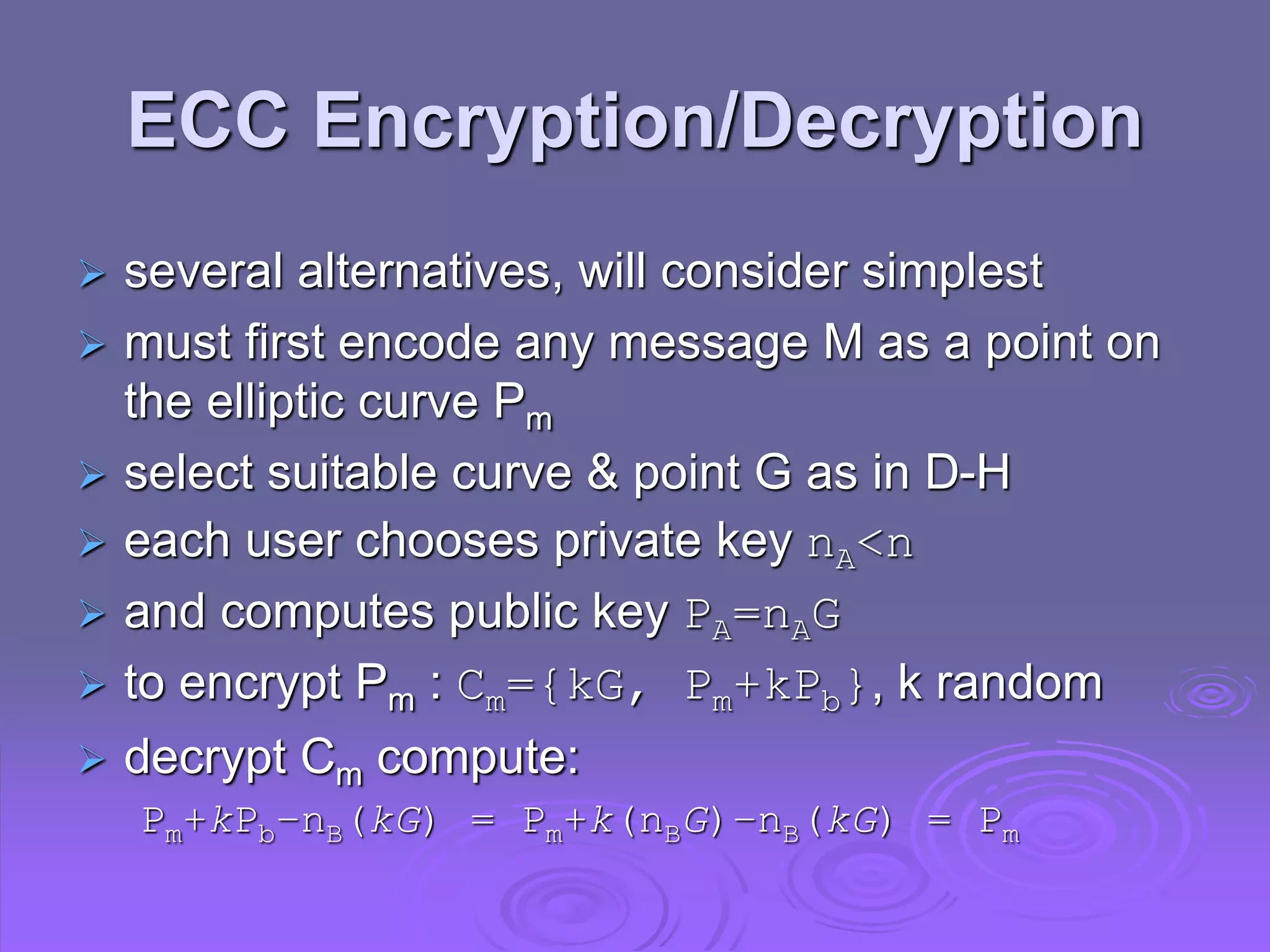
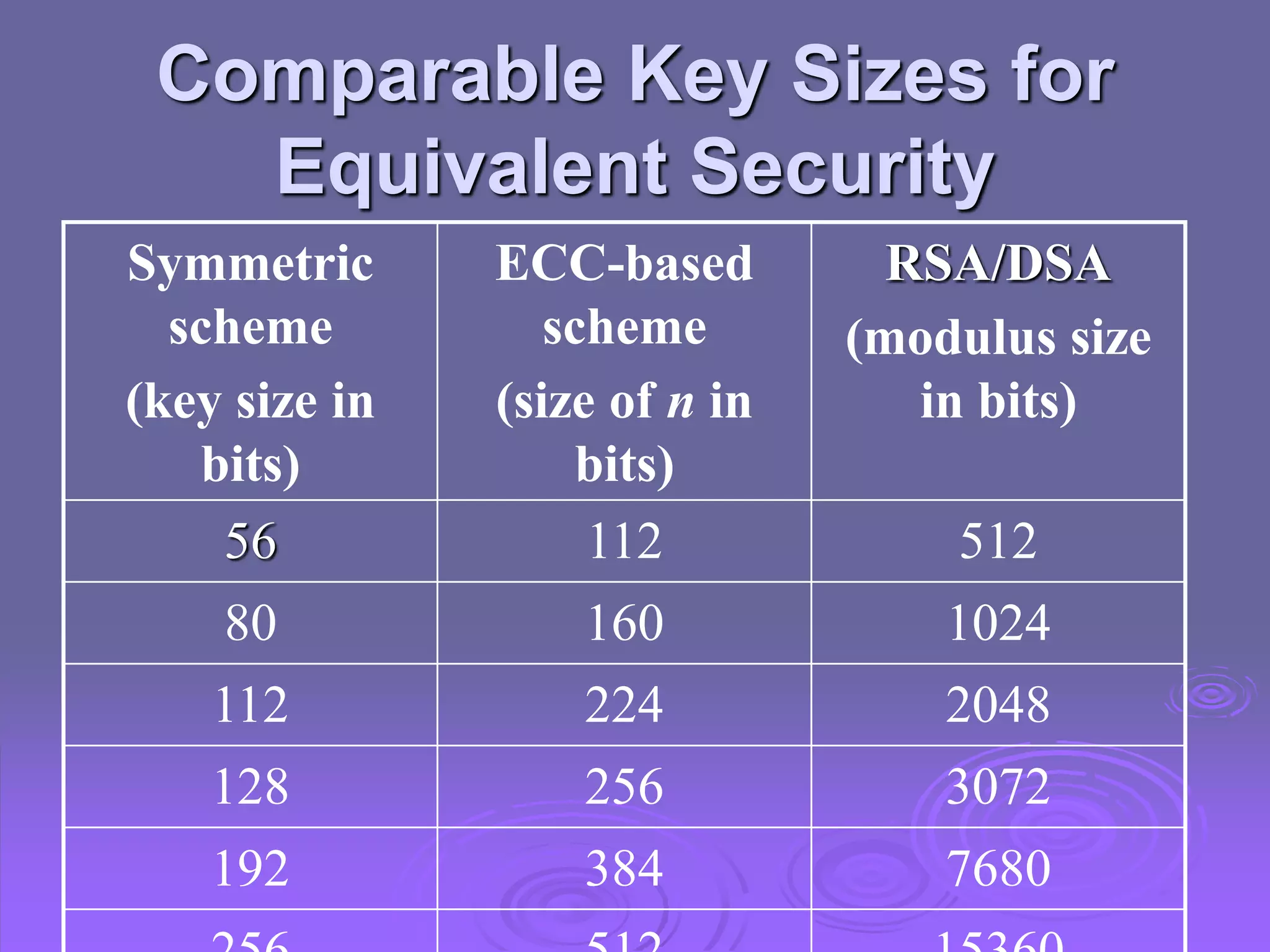
This document discusses key management and distribution in public-key cryptography. It covers several methods for distributing public keys including public announcement, directories, certificates. It also discusses using public keys to distribute secret keys, including Diffie-Hellman key exchange and hybrid encryption. Finally, it introduces elliptic curve cryptography as an alternative to systems like RSA that allows equivalent security with smaller key sizes.