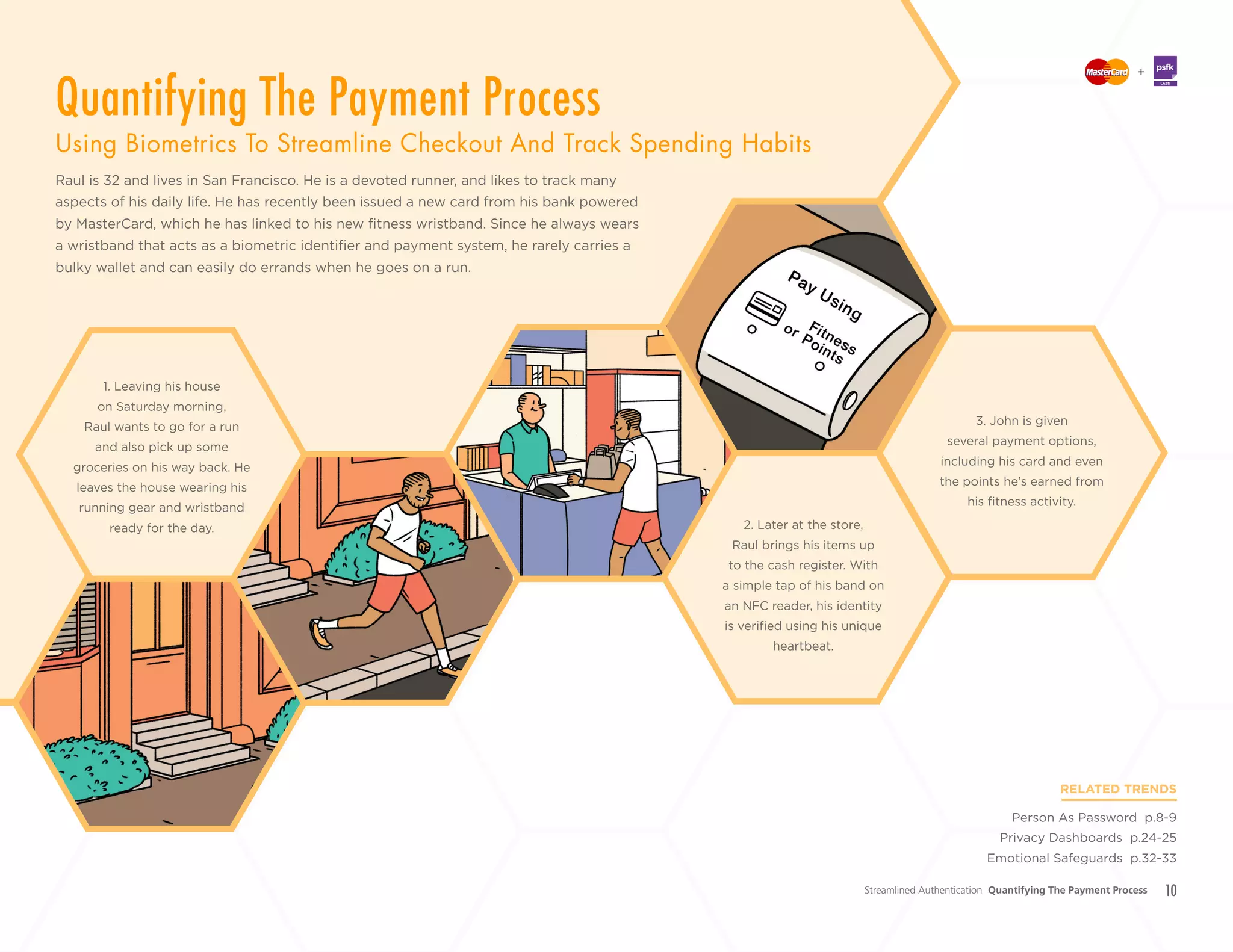
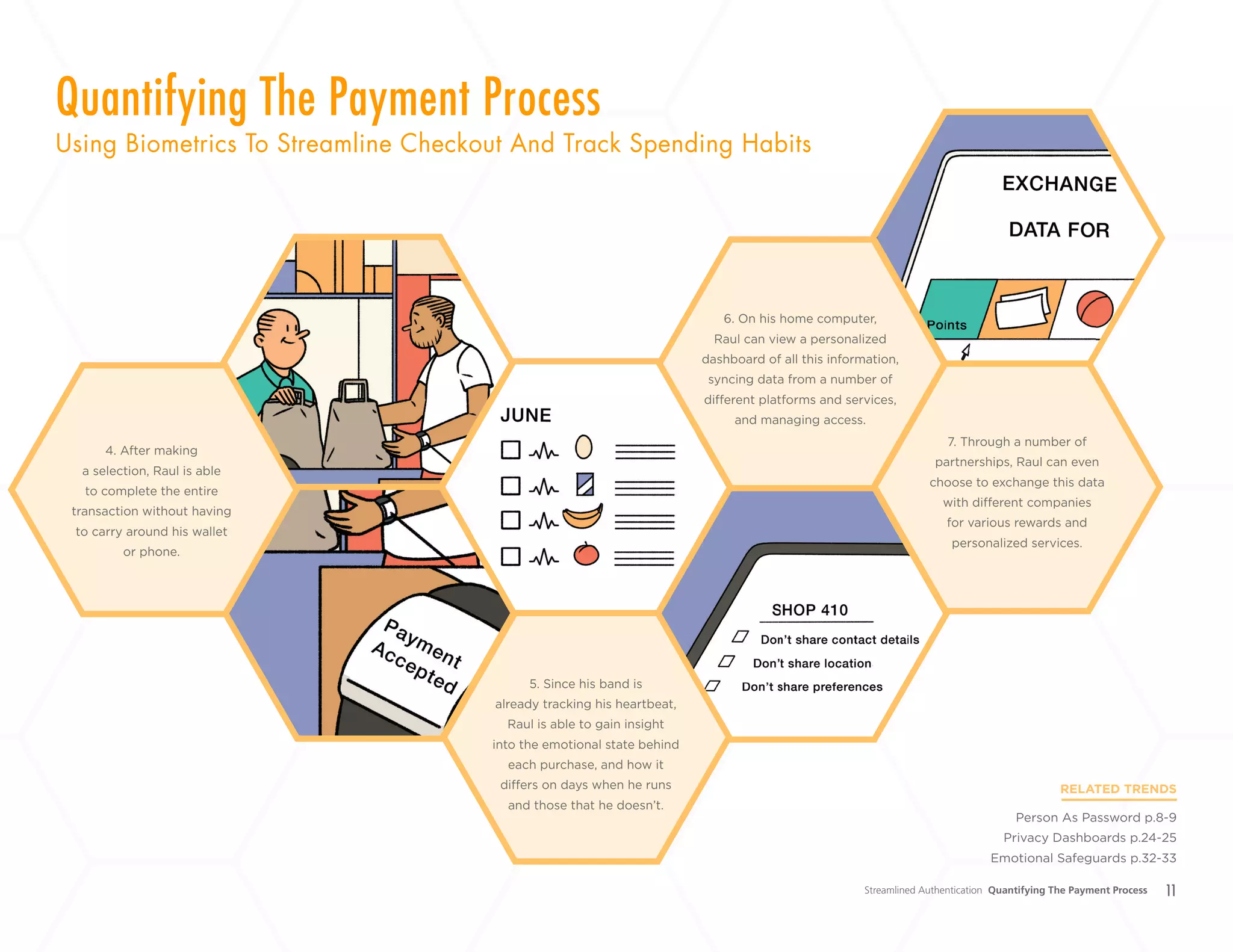
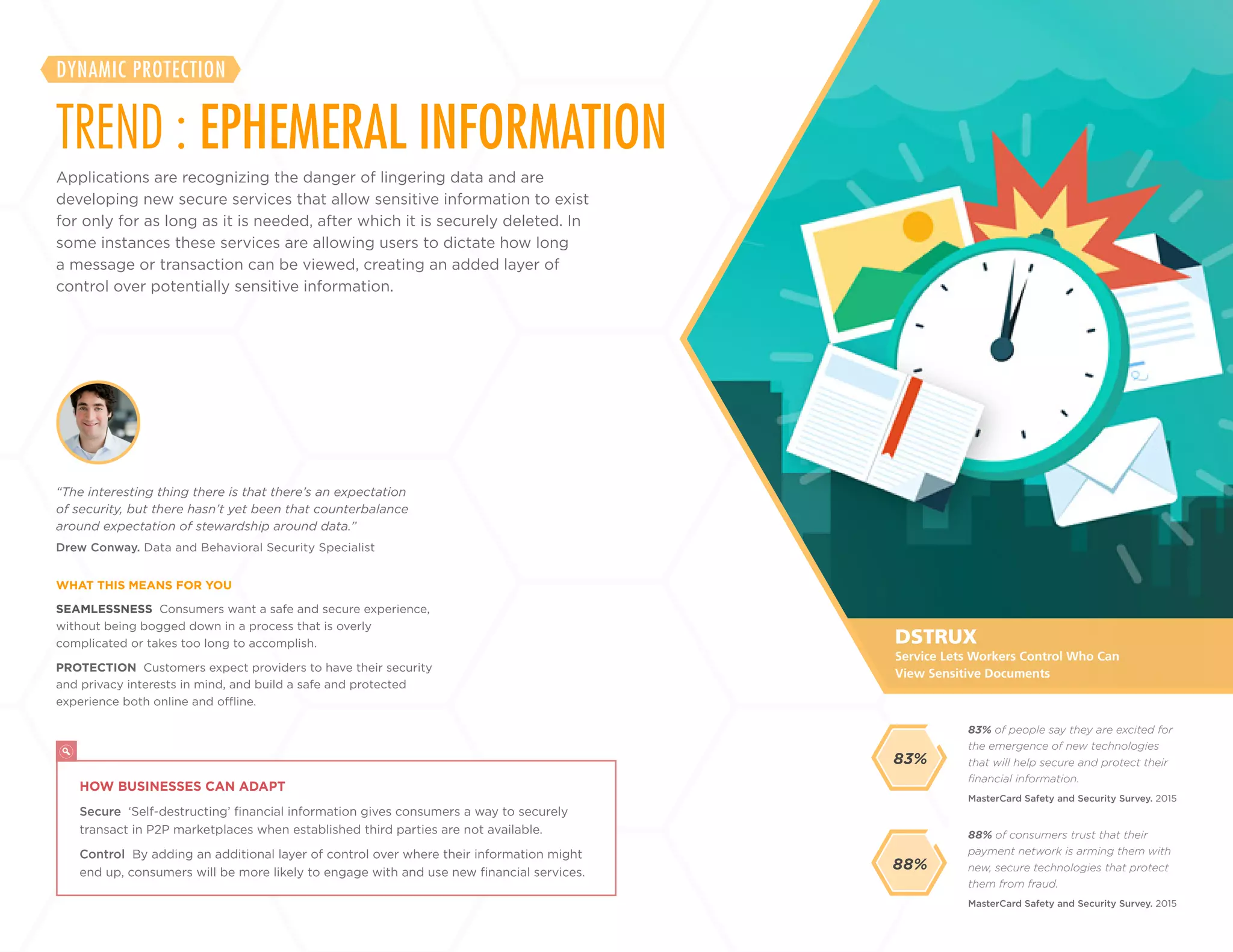
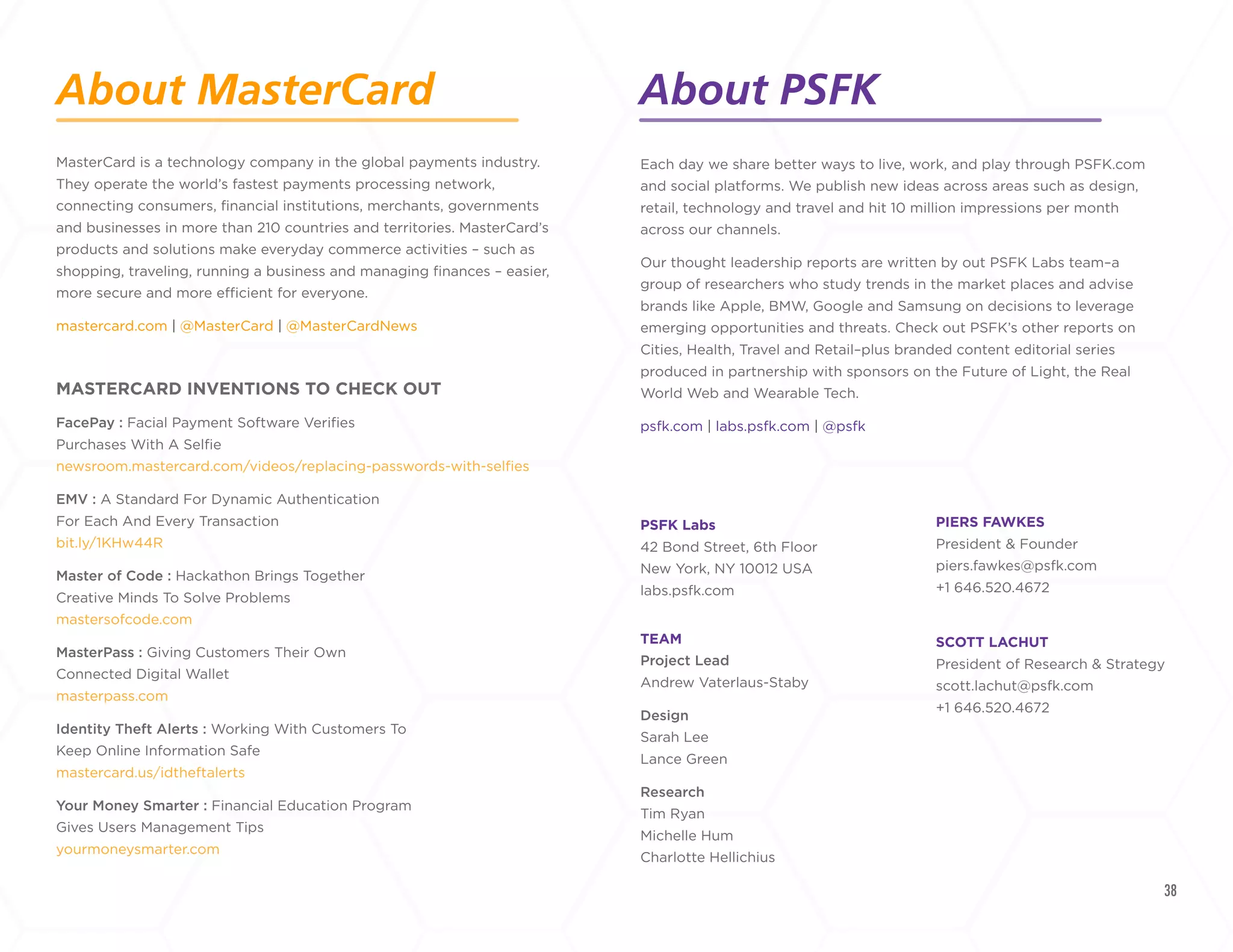
The report discusses advancements in digital safety and security, focusing on innovative authentication methods like biometrics and ephemeral data to enhance user protection and streamline access. It highlights the importance of consumer control and transparency in managing personal information, advocating for tools like privacy dashboards and personalized support. Companies are urged to evolve their offerings to meet growing consumer expectations for security and flexibility in a digital marketplace.


![9
ICICI BANK
Voice Recognition Password Logs
Customers Into Their Accounts
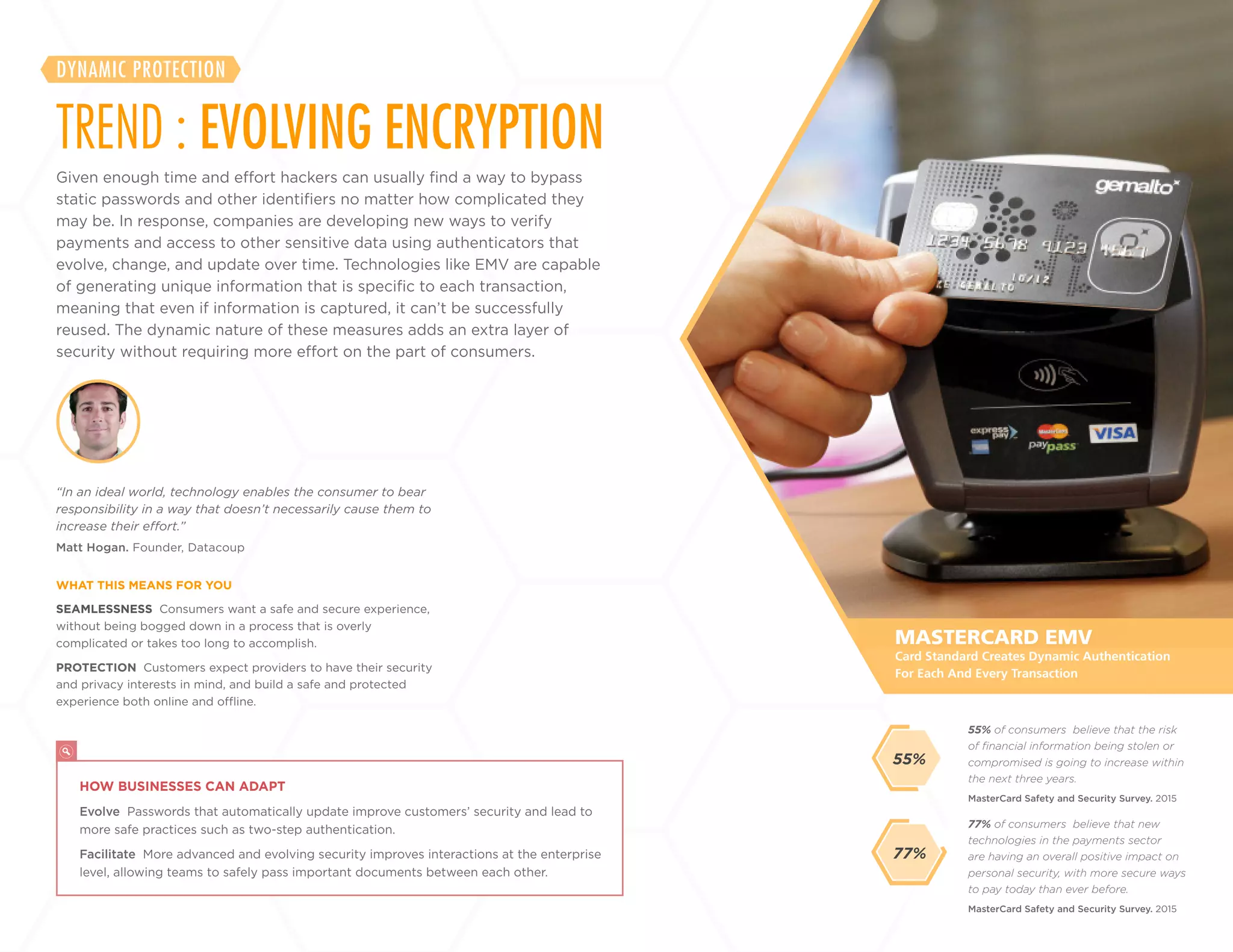
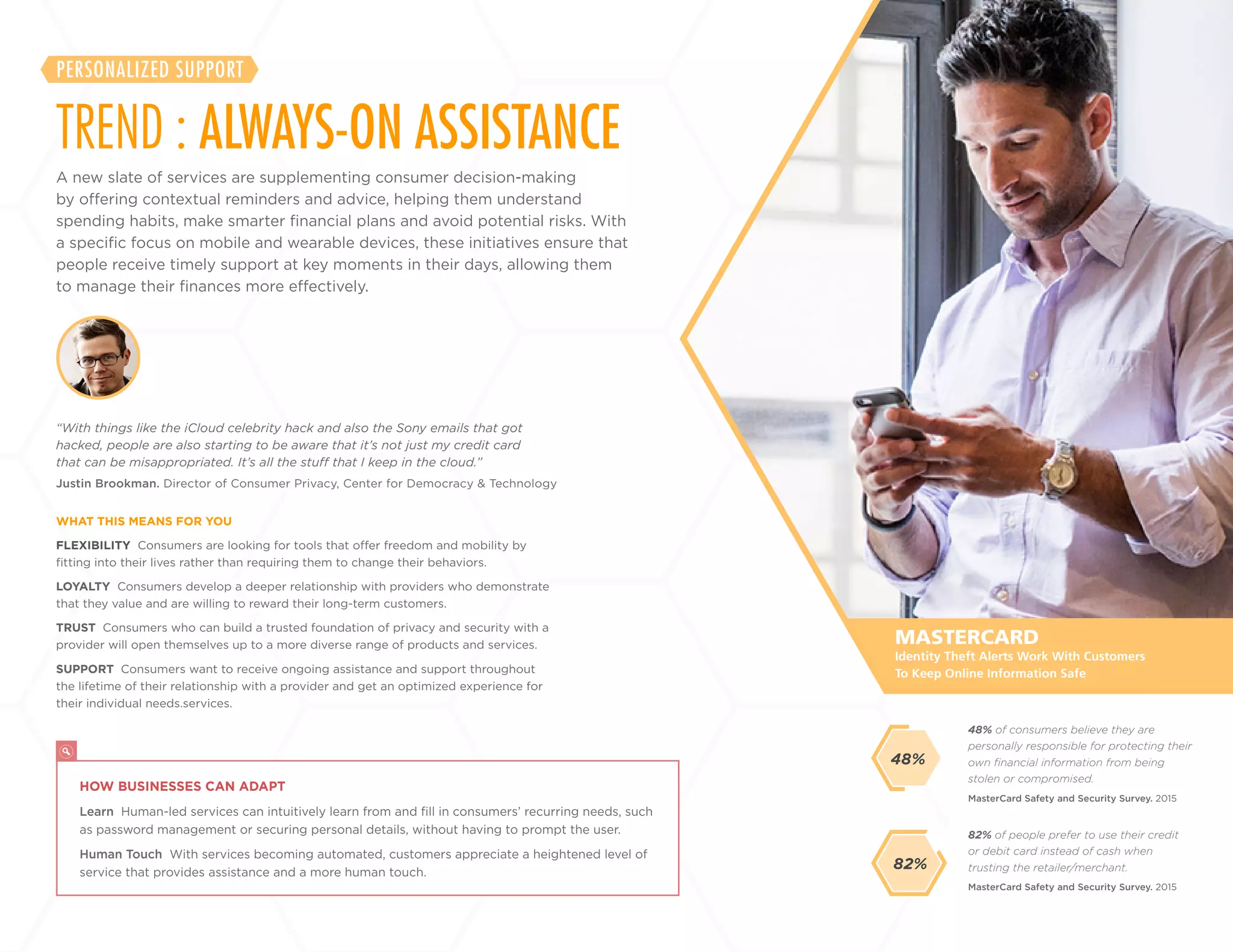
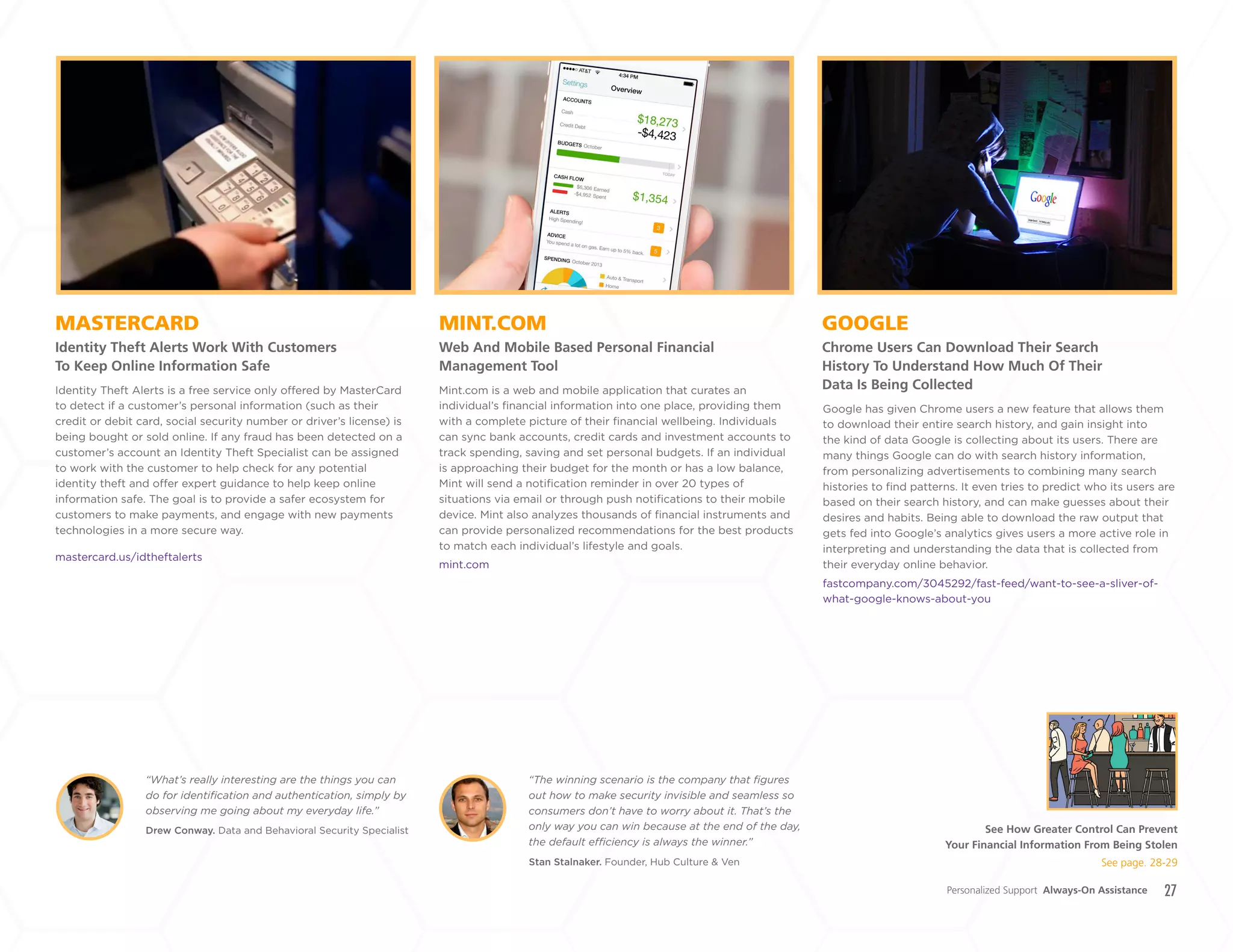
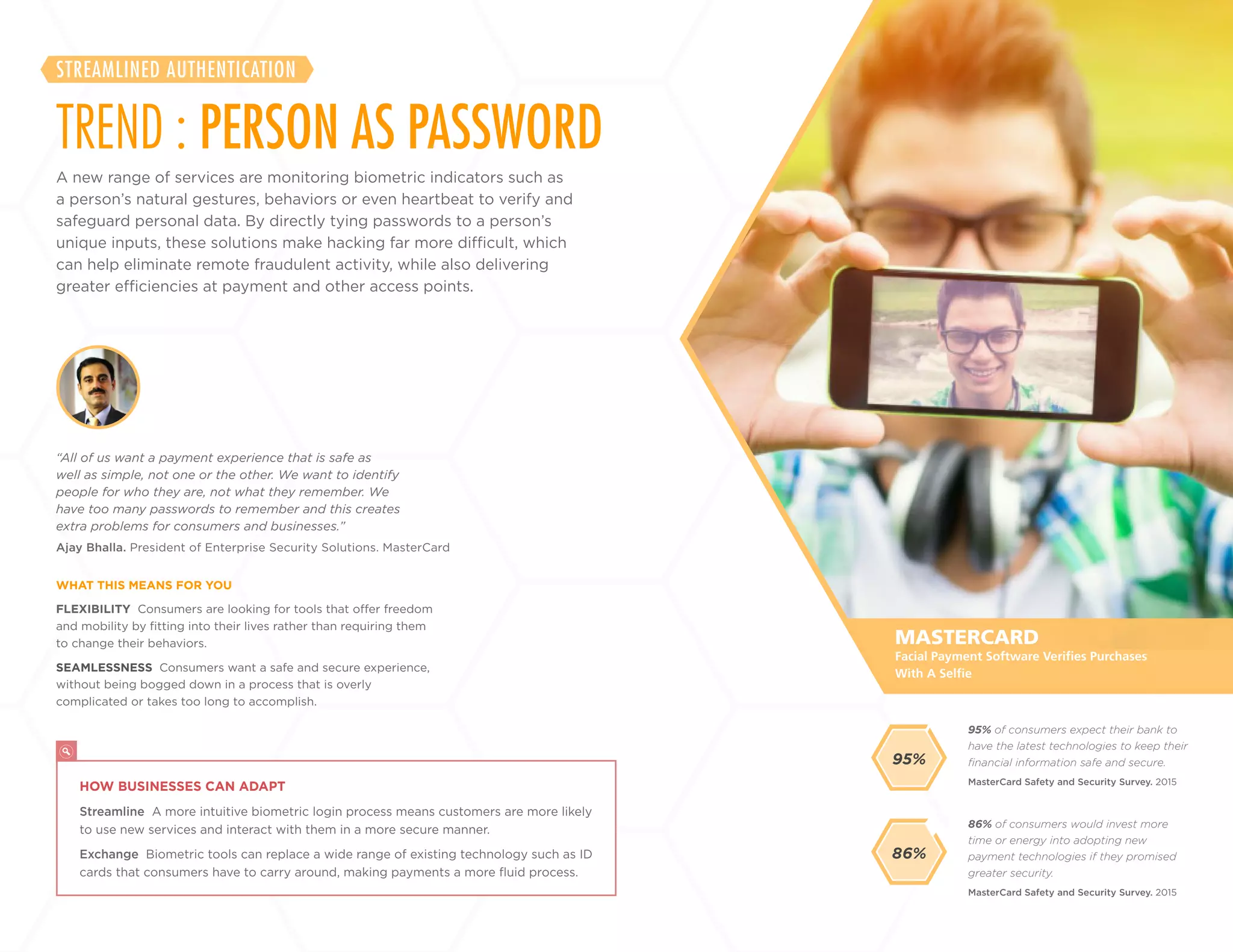
MASTERCARD
Facial Payment Software Verifies Purchases
With A Selfie
BEHAVIOSEC
Authenticator Analyzes Unique Behavioral
Biometrics Like Speed, Temperature And Rhythm
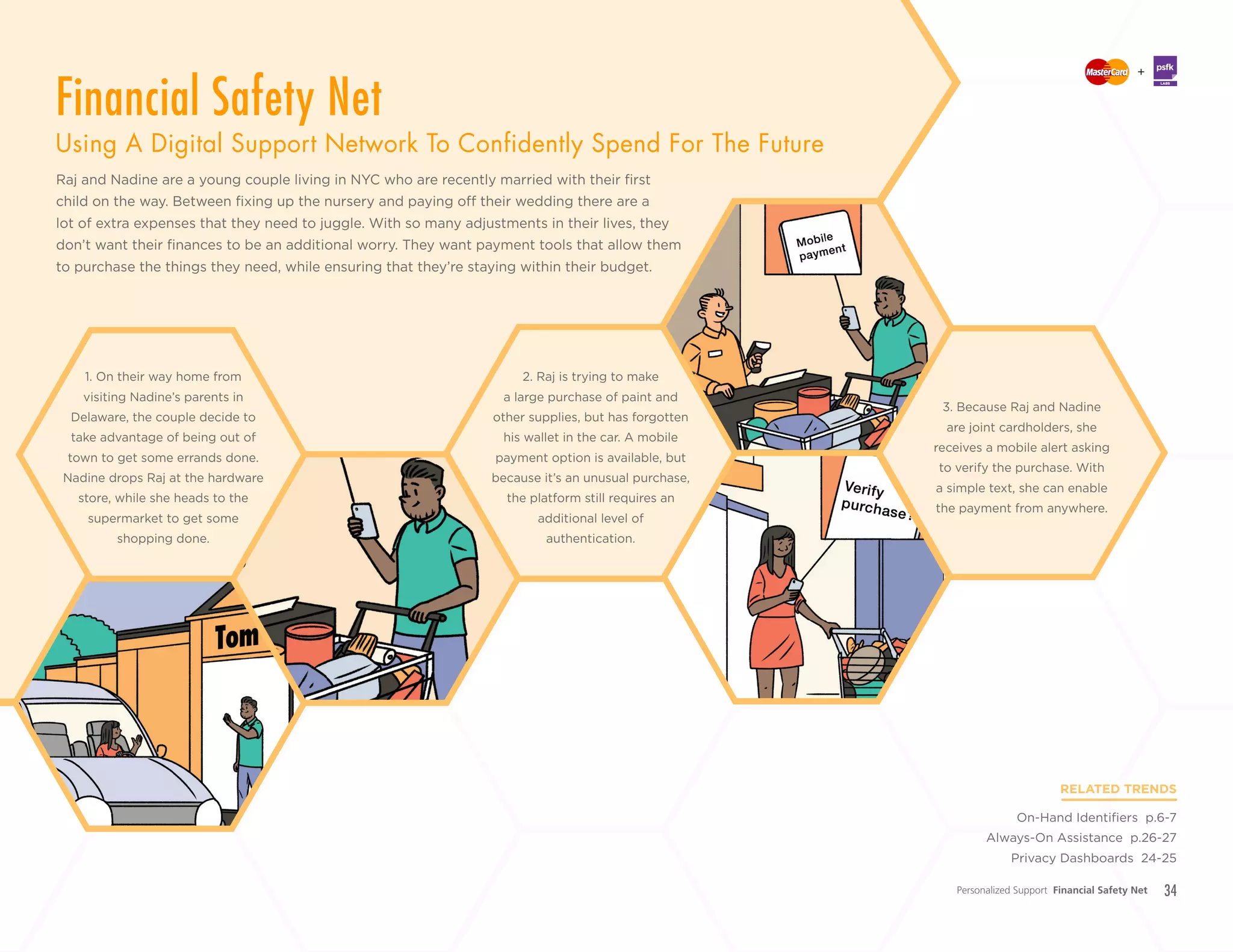
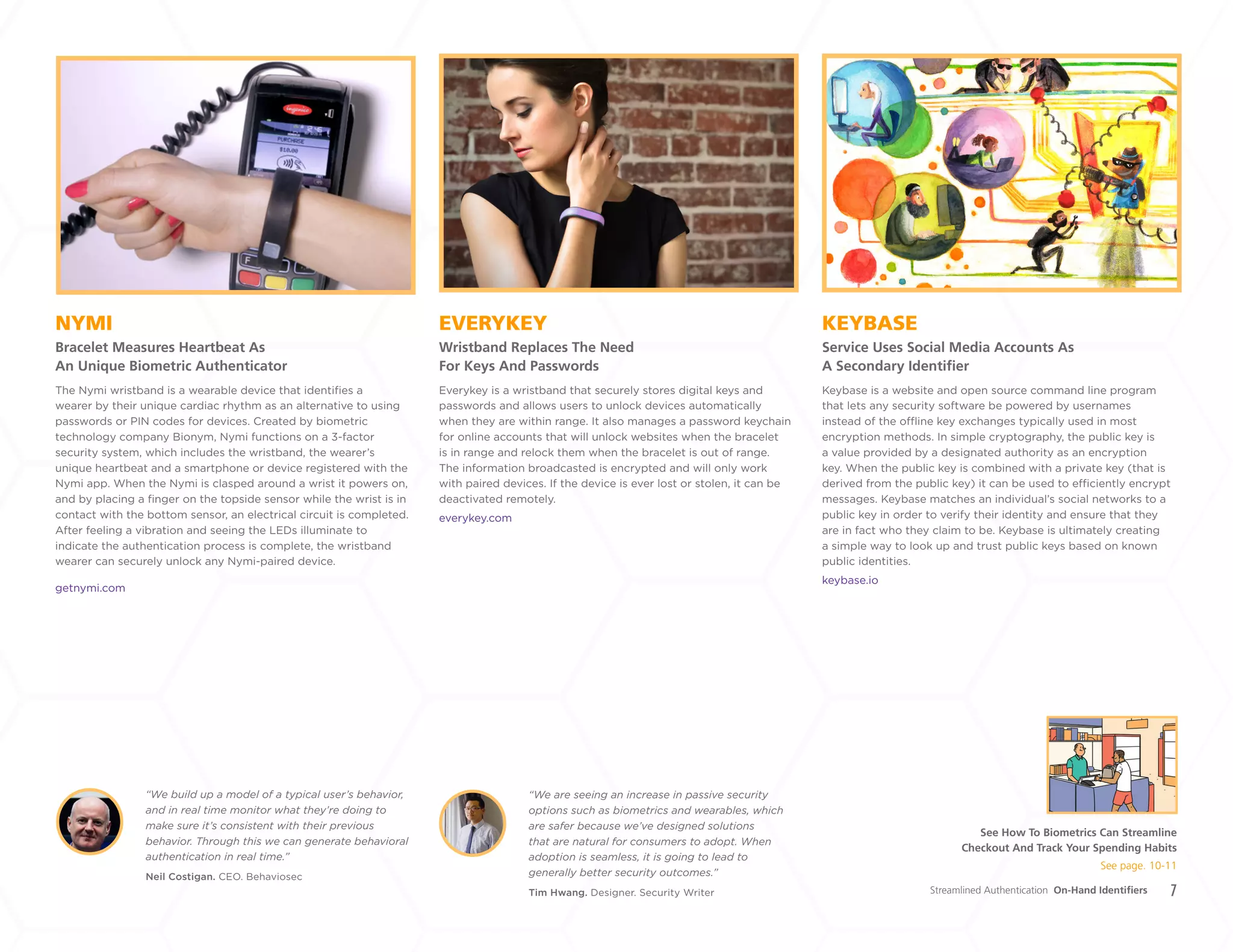
To Verify User IdentityIndia’s ICICI Bank has introduced a new initiative to make banking
as simple as possible for its customers by enabling them to
use voice recognition technology to verify their identity. ICICI
customers can access their accounts and make transactions
using only their voice, which is registered and recognized as a
password. Customers register a ‘voice print’ which is stored on
the bank’s database. Each sample has over 100 characteristics,
including voice modulation, accent, pronunciation and speed,
making it impossible to imitate. When the customer telephones
the bank from their registered number, the bank uses voice
recognition to determine if the voice is a match. The customer’s
unique voice therefore functions as their new password, replacing
other authentication methods such as card numbers, personal
addresses or security questions.
bit.ly/1LhiTaW
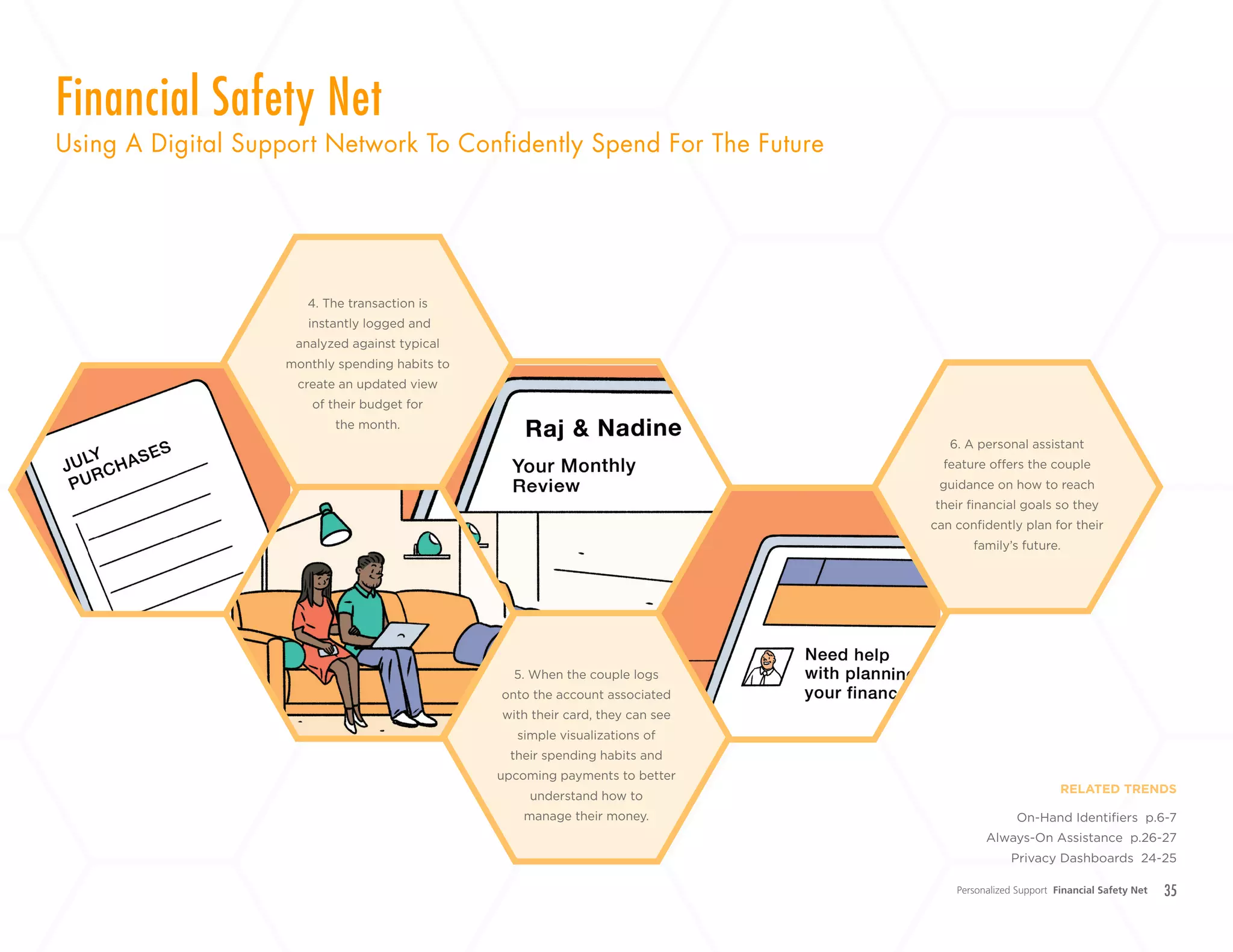
MasterCard is taking mobile payment security one step further
by launching a feature that can verify a user’s identity through a
picture of their face. Instead of merely using your fingerprint to
authorize a transaction like Apple Pay, MasterCard is letting users
take a selfie. Buy a drink using a MasterCard, and the app will
send a notification to snap a picture of your face to confirm your
identity. As an added security measure, users have to blink when
taking the selfie so that someone wouldn’t be able to just hold
up a photo to trick the app. MasterCard’s app will also support
fingerprint scanning for authorizing purchases. The goal is to
target younger users who already use their phones multiple times
a day with apps like Snapchat, who will be most likely to adopt
the service.
newsroom.mastercard.com/videos/replacing-passwords-with-
selfies/
Chris McWilton. President of North American Markets.
MasterCard
Greg Mitchell. President. Chief Executive Officer.
First Tech Federal Credit Union
“While progress is being made with the move
to EMV and mobile payments...we are [making
investments] to protect the payments system for
cardholders, merchants and issuers. That’s at the
heart of what our cardholders expect when they
see our brand mark.”
“The MasterCard cybersecurity concept
is innovative, and a big step towards this
commitment. We look forward to helping
MasterCard bring this new technology to our
member cardholders throughout America,”
Swedish startup Behaviosec has invented a new type of
personalized authentication that serves as an alternative to
passwords. Instead, the service works to identify users by their
unique biometric fingerprint, which includes a combination
of ways in which users interact with their device, such as the
force with which they hit a key, the angle they use to swipe a
touchscreen, or their typing speed. This type of identification
frees users from the burden of memorizing complex passwords,
and simply allows them to interact with their device as they
normally would to confirm their identity.
behaviosec.com
Streamlined Authentication Person As Password
See How To Biometrics Can Streamline
Checkout And Track Your Spending Habits
See page. 10-11
+
LABS](https://image.slidesharecdn.com/psfkpresentsthefutureofdigitalsafetysecurity-151013210956-lva1-app6891/75/PSFK-Presents-the-Future-of-Digital-Safety-Security-10-2048.jpg)