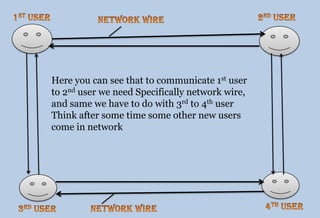
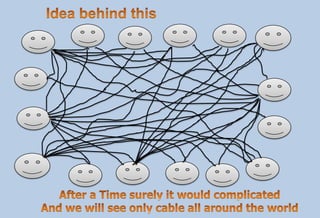
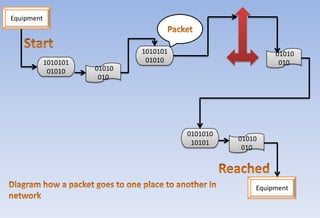
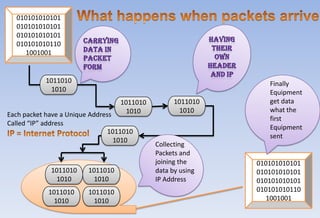
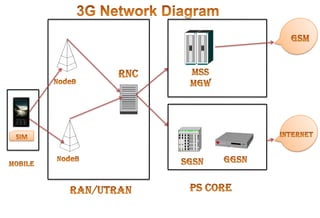
Narendra Singh Negi, a senior recruitment consultant at Net Consulting International, shares insights on telecom networks, specifically circuit switching and packet switching. He explains how data is transmitted efficiently through unique IP addresses, enabling robust communication across networks like GPRS. Additionally, he discusses the roles of key components such as the Radio Network Controller (RNC), Gateway GPRS Support Node (GGSN), and Serving GPRS Support Node (SGSN) in managing mobile communications.