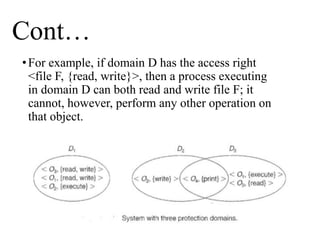
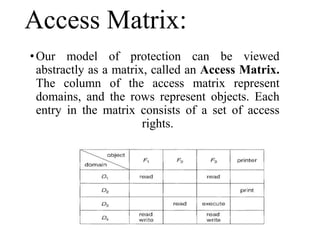
The document discusses the protection and security mechanisms of operating systems, emphasizing the importance of controlling access to resources to prevent unauthorized use. It explains concepts such as the principle of least privilege, access control models like role-based and capability-based systems, and various security measures to protect against threats. Additionally, it categorizes security violations and highlights the role of the security kernel and user authentication in maintaining system integrity.