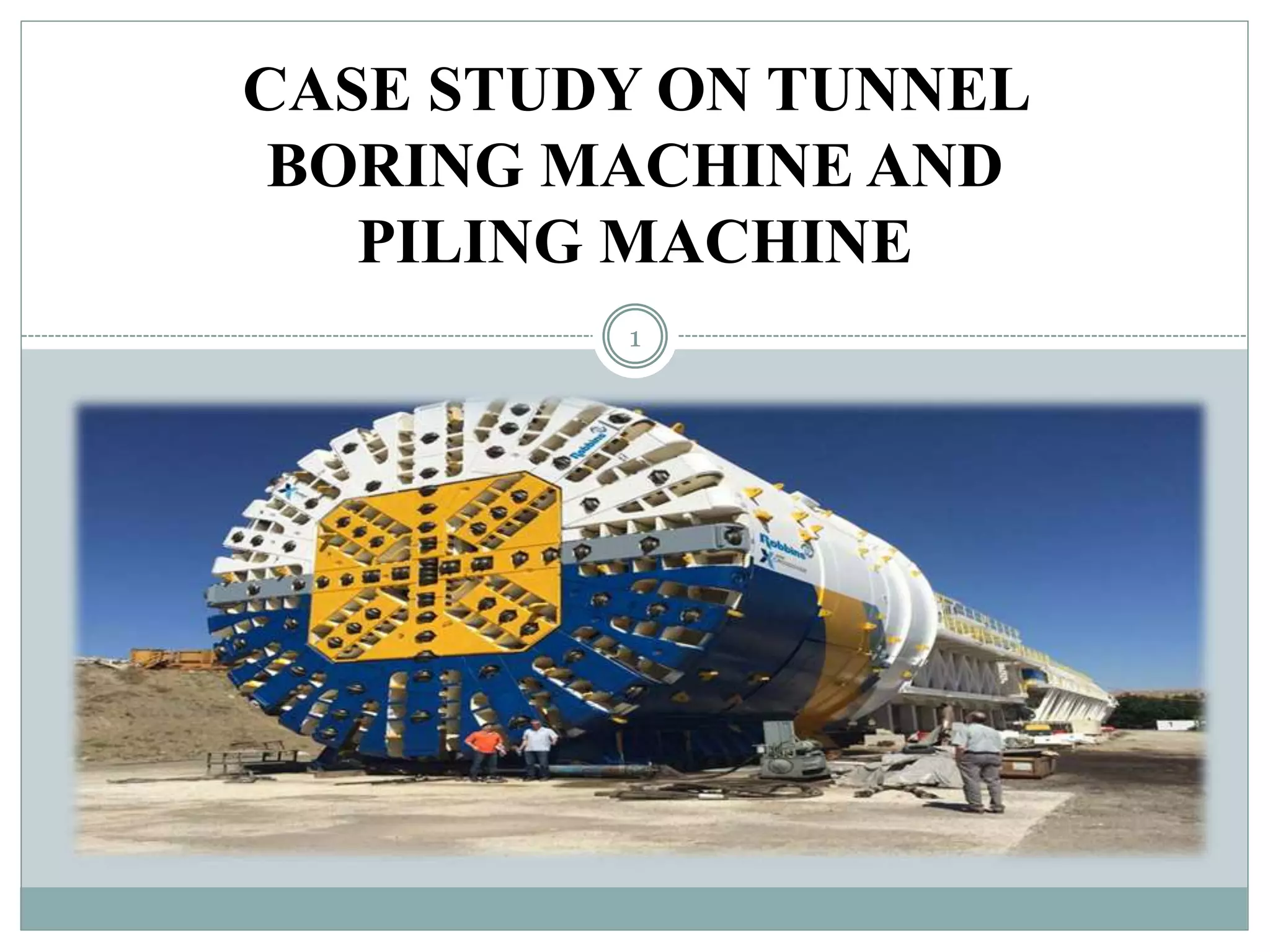
This document presents a detailed case study on Tunnel Boring Machines (TBMs) and piling machines, explaining their technologies, types, and applications in construction and excavation. It discusses various TBMs like slurry shield and single shield machines, as well as piling methods like diesel impact and vibratory hammers, including case studies illustrating their performance. The conclusion emphasizes the significant impact of boring machines on urban infrastructure and the importance of selecting the appropriate machinery based on specific project requirements.
![INTRODUCTION
Tunnel Boring Machine (TBM) also known as
‘MOLE’.
It is used to excavate tunnels with a circular
cross section
It can bore through anything from hard rock to
sand.
Different types of TBMs are used for different
geo technology.
Used as an alternative to drilling and blasting
methods and conventional 'hand mining' in soil
Limits the disturbance to the surrounding
ground and produces a smooth tunnel wall.
Suitable to use in heavily urbanized areas.
Tunnel Boring Machine [1]
3](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-3-320.jpg)
![• Piling is a type of Foundation which
is defined as a column supported
type of foundation.
• It may be made of Timber, Concrete,
Steel, or combination of any of them.
• Pile foundation is adopted when the
loose soil extends to a great depth.
• The load is transmitted by the piles
to the hard below or it is resisted by
the friction developed on the sides of
piles.
• Piling process involves lifting and
holding the pile into position and
driving until it stops due to hard or
reaches to a specified depth.
4
Piling Machine [2]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-4-320.jpg)
![ Cutting rolls are used to tear of
the soil and rock from tunnel face.
They are mounted on the cutting
heads.
Different types of materials are
used for different ground
condition.
They are placed radically, so as to
have maximum efficiency.
They can revolve themselves in
full 360 degree.
They can be replaced periodically.
CUTTING ROLLS
5
Cutting Rolls[3]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-5-320.jpg)
![CUTTERHEADS
Cutter heads is the part of the
TBM which faces the ground to
be tunneled.
It will revolve in speed of 1 to 10
rpm
Cutting rolls and cutting blades
are mounted here.
Cutter head can revolve 360
degree.
6
Cutter head of a TBM [4]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-6-320.jpg)
![GRIPPER
Grippers are also called
supporting arms of TBMs.
All TBMs have at least a pair of
grippers.
Grippers provide a radial thrust to
the tunnel walls with the help of
hydraulic press.
Grippers are used only when
cutter head moves forward
against the tunnel face.
7
Gripper [5]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-7-320.jpg)
![SLURRYSHIELD
• Slurry shields are TBM fitted with a
full face cutter head which provides
face support by pressurizing boring
fluid inside the cutter head chamber.
• These machines are most suited for
tunnels through unstable material
subjected to high groundwater pressure.
• Slurry shields are mainly suitable for
excavation in sand and gravels with
silts.
• Soils are mixed with betonies slurry,
which must be removed from the
tunnel through a system of slurry tubes
that exit the tunnel.
• Large slurry separation plants are
needed on the surface for this process,
which separate the dirt from the slurry
so it can be recycled back into the
tunnel.[8]
9
Slurry Shield TBM [6]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-9-320.jpg)
![MIXSHIELD
The Mix Shield technology developed
by Herrenknecht is an advance on
conventional slurry technology.
The support pressure in the excavation
chamber is precisely managed using
an automatically controlled air
cushion.
This means that heterogeneous
geologies and high water pressures of
more than 15 bar can be controlled
safely even with very large excavation
diameters.
Mix Shields often use a jaw crusher
for tunneling purpose, which is
positioned in front of the intake
screen.
10
Mix Shield TBM [7]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-10-320.jpg)
![SINGLE SHIELD TBM
Single shield have no shield as
that of in soft ground type.
Excavation is done by cutter rolls
transferred through openings in
the cutter head to a belt conveyor,
and then to muck cars or conveyor
belt.
There is no excavation chambers
as chips are of solid and not as
slurry.
More smoother tunnel walls can
be created using this machine .
11
Single Shield TBM [8]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-11-320.jpg)
![DOUBLESHIELDTBM
These are the most technically sophisticated tunnel boring machines in
use.
This type of machine is ideally suited for drilling long tunnels in hard
rock where geological fault zones occur.
Flexible use in all kinds of rock.
12
Double
Shield
TBM
[9]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-12-320.jpg)
![CASE STUDY ON TBM PERFORMANCE
To improve the water supply to Vakola, a 12.24 km long passage
between Maroshi and Ruparel College was uncovered by a Tunnel
exhausting machine.
The tunnel is separated into three segments, i.e.Maroshi–Vakola(5.834
km long), Vakola–Mahim(4.549 km), and Mahim–Ruparel
College(1.859 km).
13
Tunnel
Between
Maroshi to
Ruparel
[10]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-13-320.jpg)
![DIESEL IMPACT HAMMER
Rapid controlled explosions can be
produced by the diesel hammer.
The explosions raise a ram which is
used to drive the pile into the ground.
Although the ram is smaller than the
weight used in the drop hammer the
increased frequency of the blows can
make up for this inefficiency.
This type of hammer is most suitable
for driving piles through non-
cohesive granular soils where the
majority of the resistance is from end
bearing.
16
Diesel Impact Hammer [11]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-16-320.jpg)
![STEAM IMPACT HAMMER
The Steam Impact Hammer is the
most commonly used method of
insertion of displacement piles
A weight approximately half that of
the pile is raised a suitable distance in
a guide and released to strike the pile
head .
When driving a hollow pile tube the
weight usually acts on a plug at the
top of the pile tube, thus reducing any
excess stress along the length of the
tube during insertion.
These are mechanically driven by
steam, by compressed air or
hydraulically.
17
Steam Impact Hammer [12]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-17-320.jpg)
![VIBRATORY HAMMER
Vibratory Hammer can prove to be
very effective in driving piles through
non cohesive granular soils.
The vibration of the pile excites the soil
grains adjacent to the pile making the
soil almost free flowing thus
significantly reducing friction along the
pile shaft.
The vibration can be produced by
electrically powered contra-rotating
eccentric masses attached to the pile
head usually acting at a frequency of
about 20-40 Hz.
If this frequency is increased to around
100 Hz it can set up a longitudinal
resonance in the pile and penetration
rates can approach up to 20 m/min in
moderately dense granular soils.
18
Vibratory Hammer [13]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-18-320.jpg)
![20
Fig. Pareto analysis of drilling machines’ subsystems in Sarcheshmeh Copper Mine[14]](https://image.slidesharecdn.com/presentationonpilingmachinetmb-210719040751/85/Presentation-on-Piling-Machine-TMB-20-320.jpg)