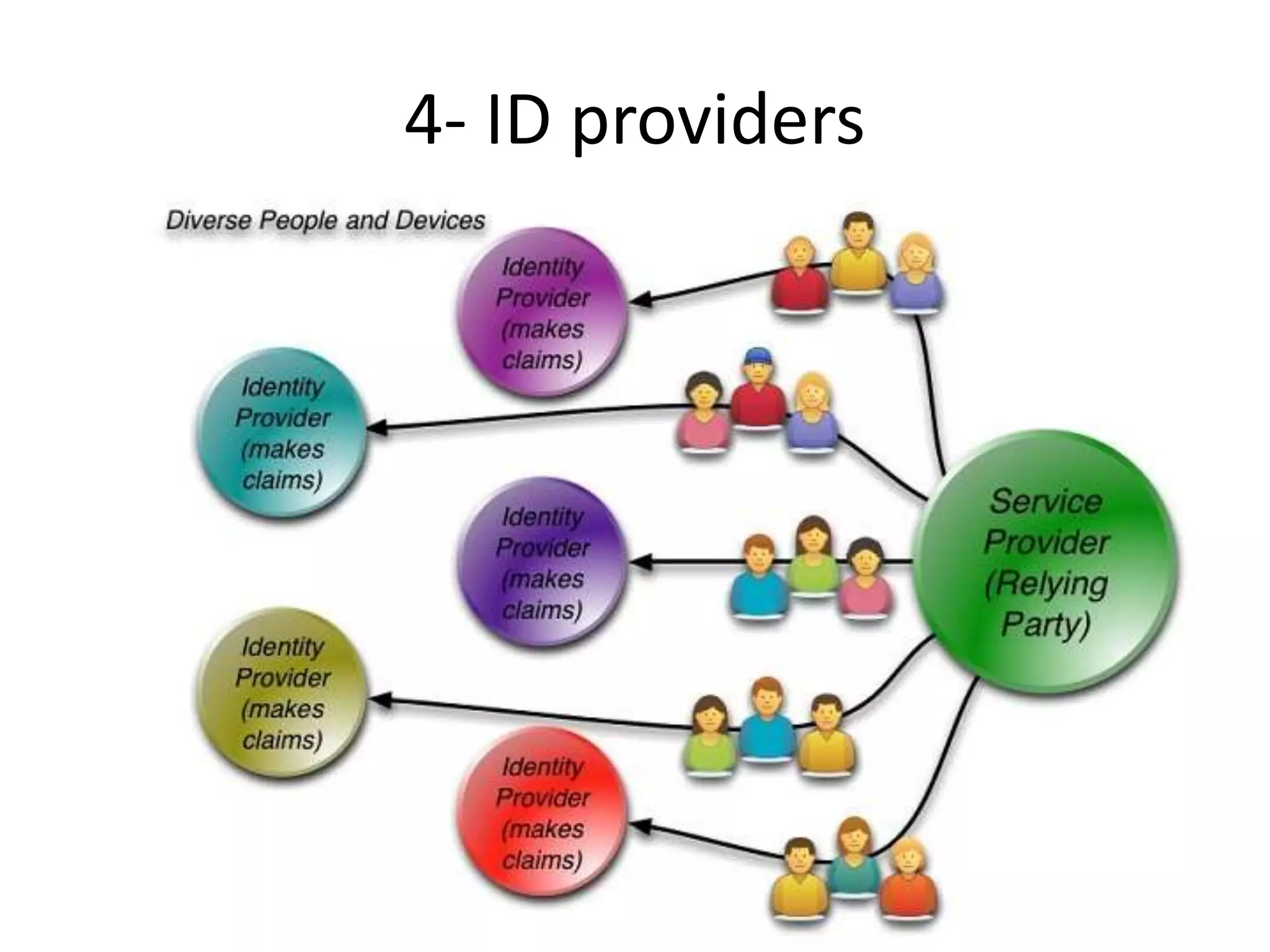
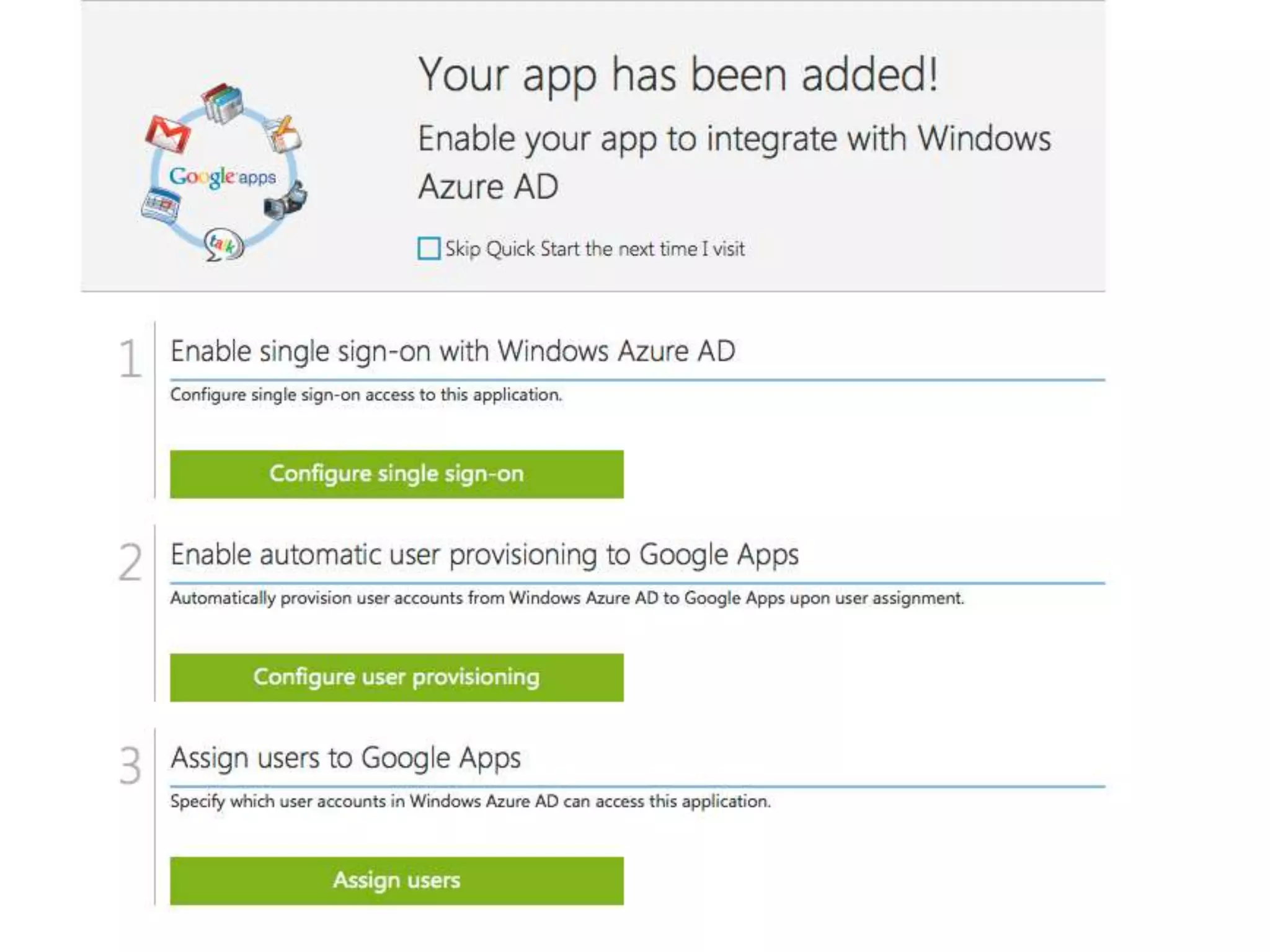
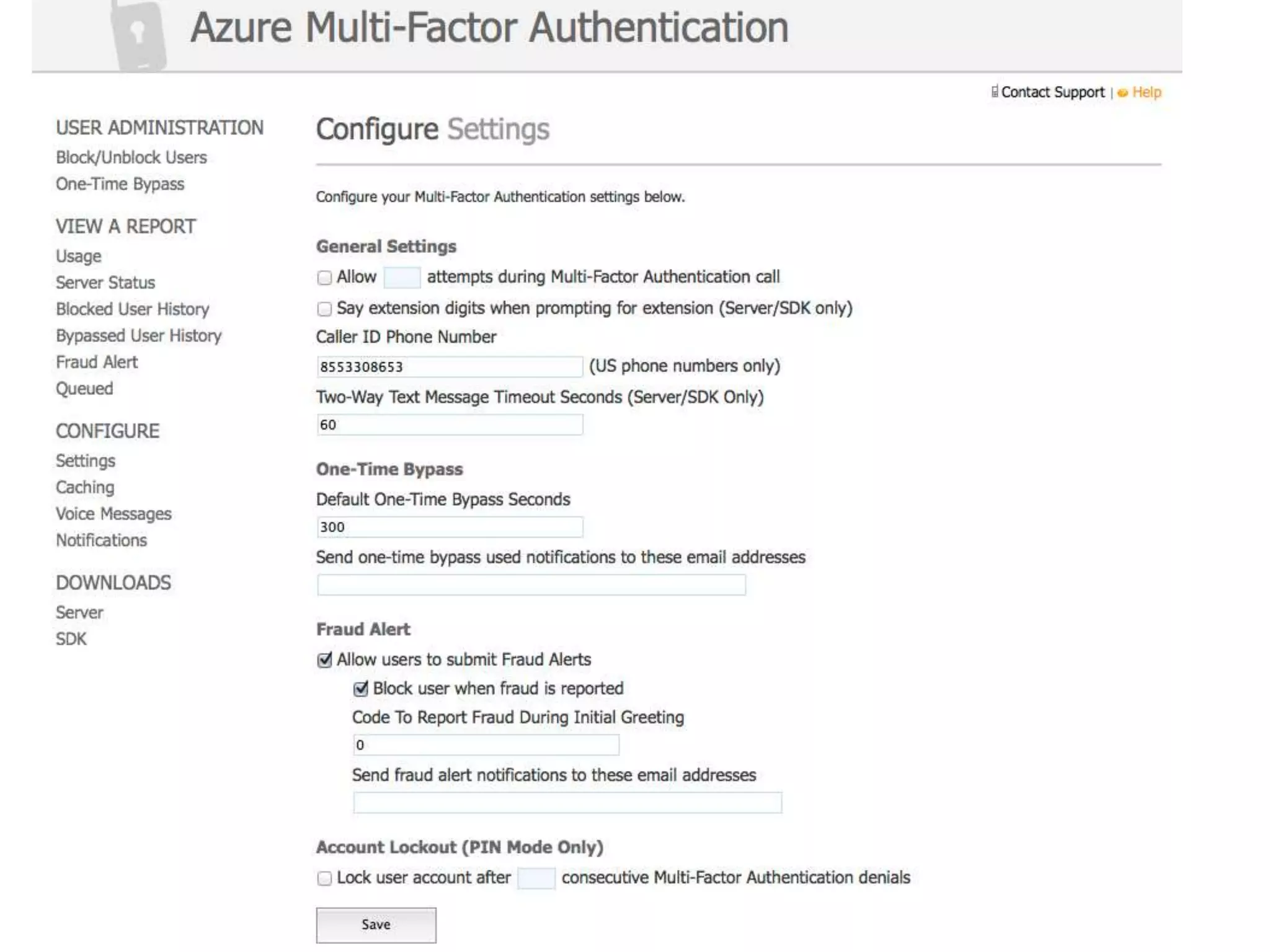
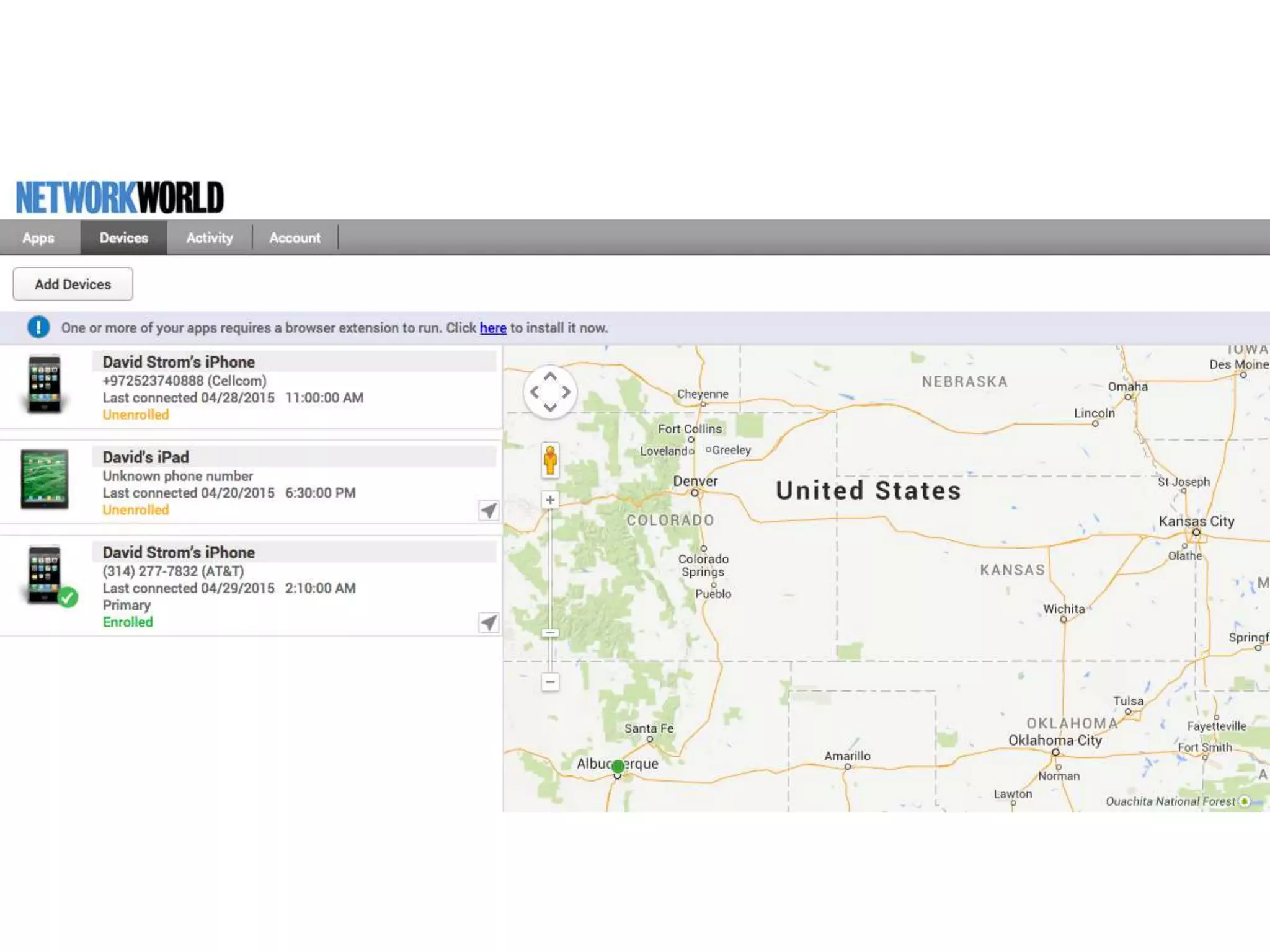
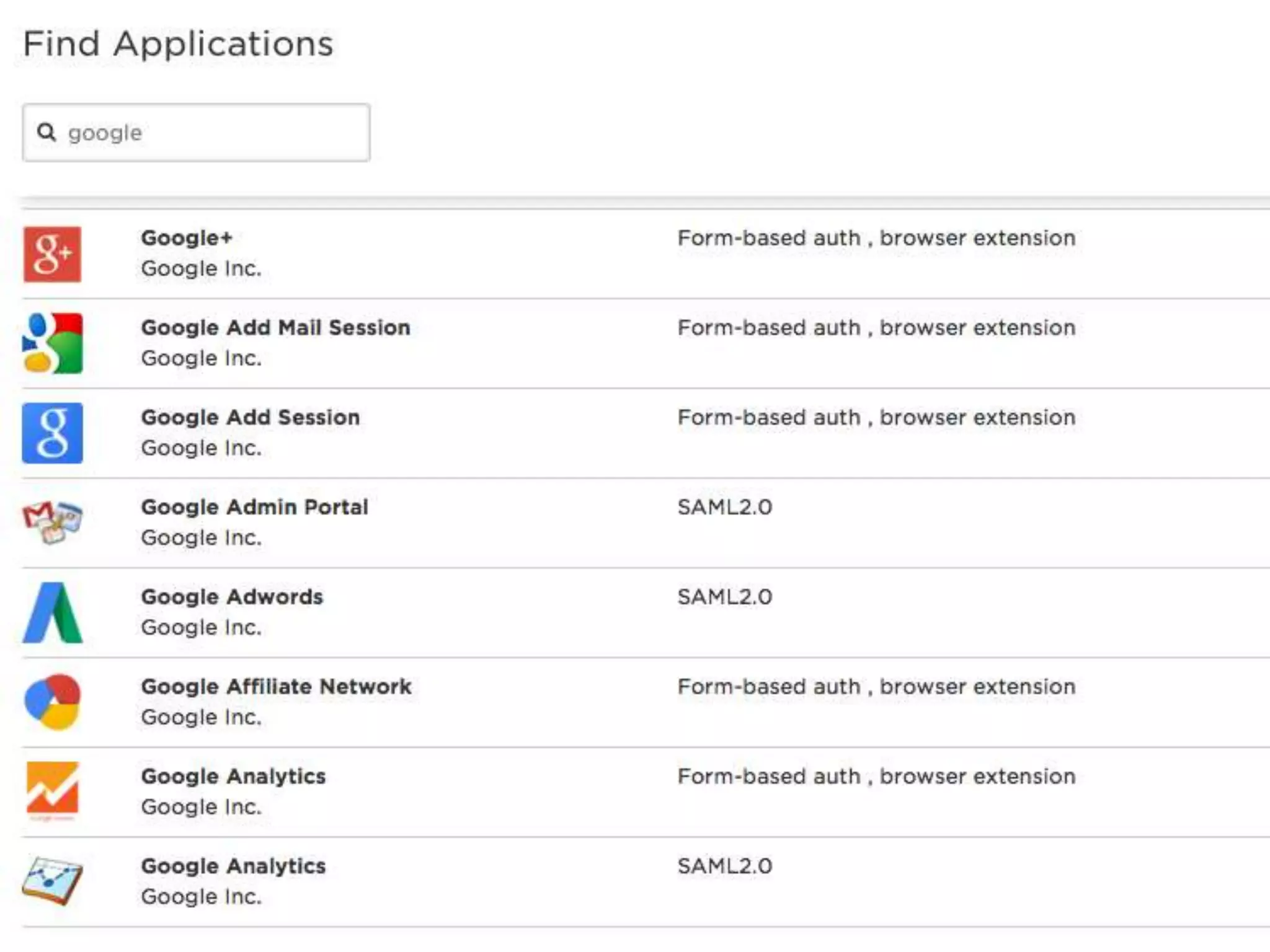
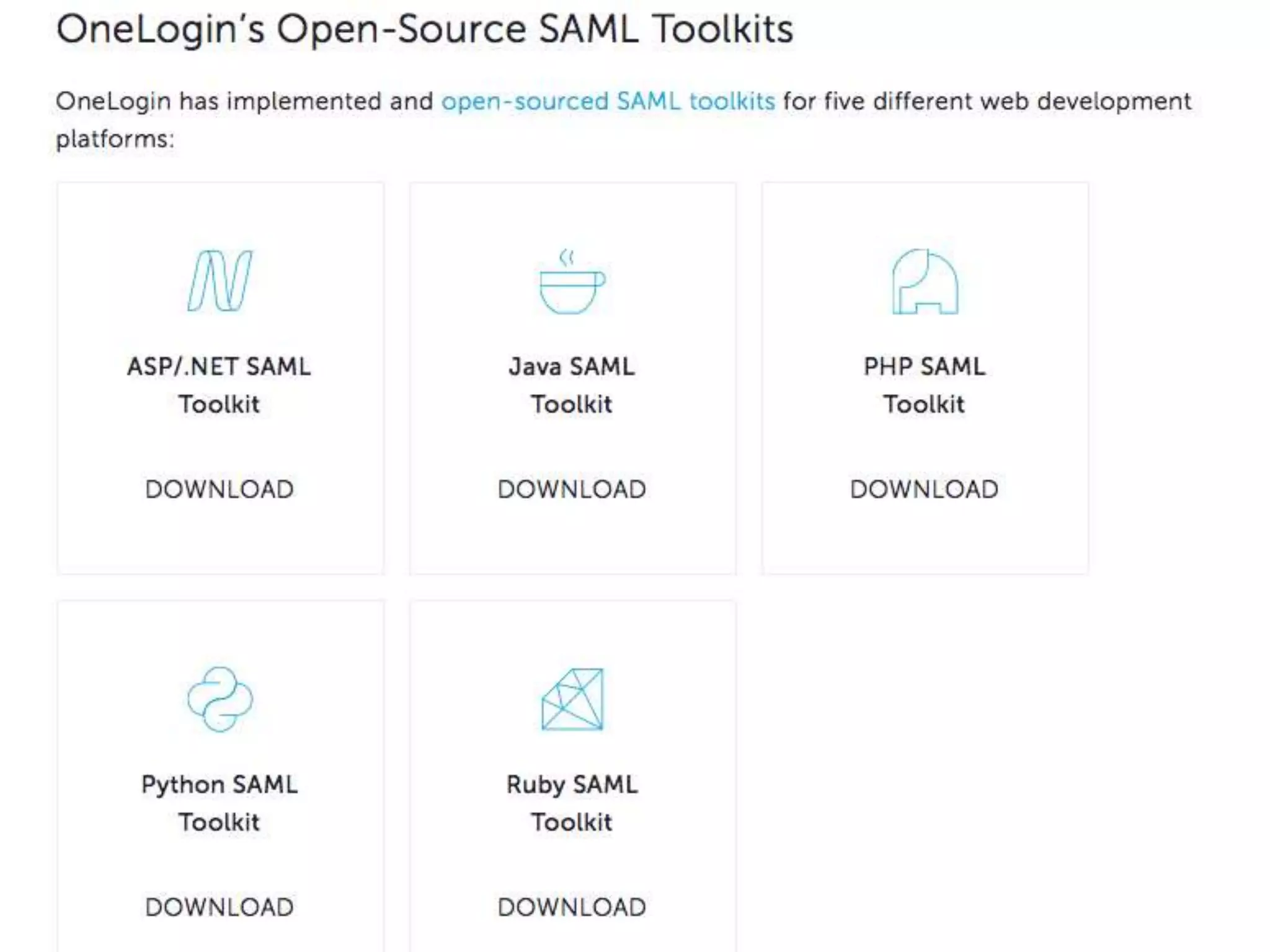
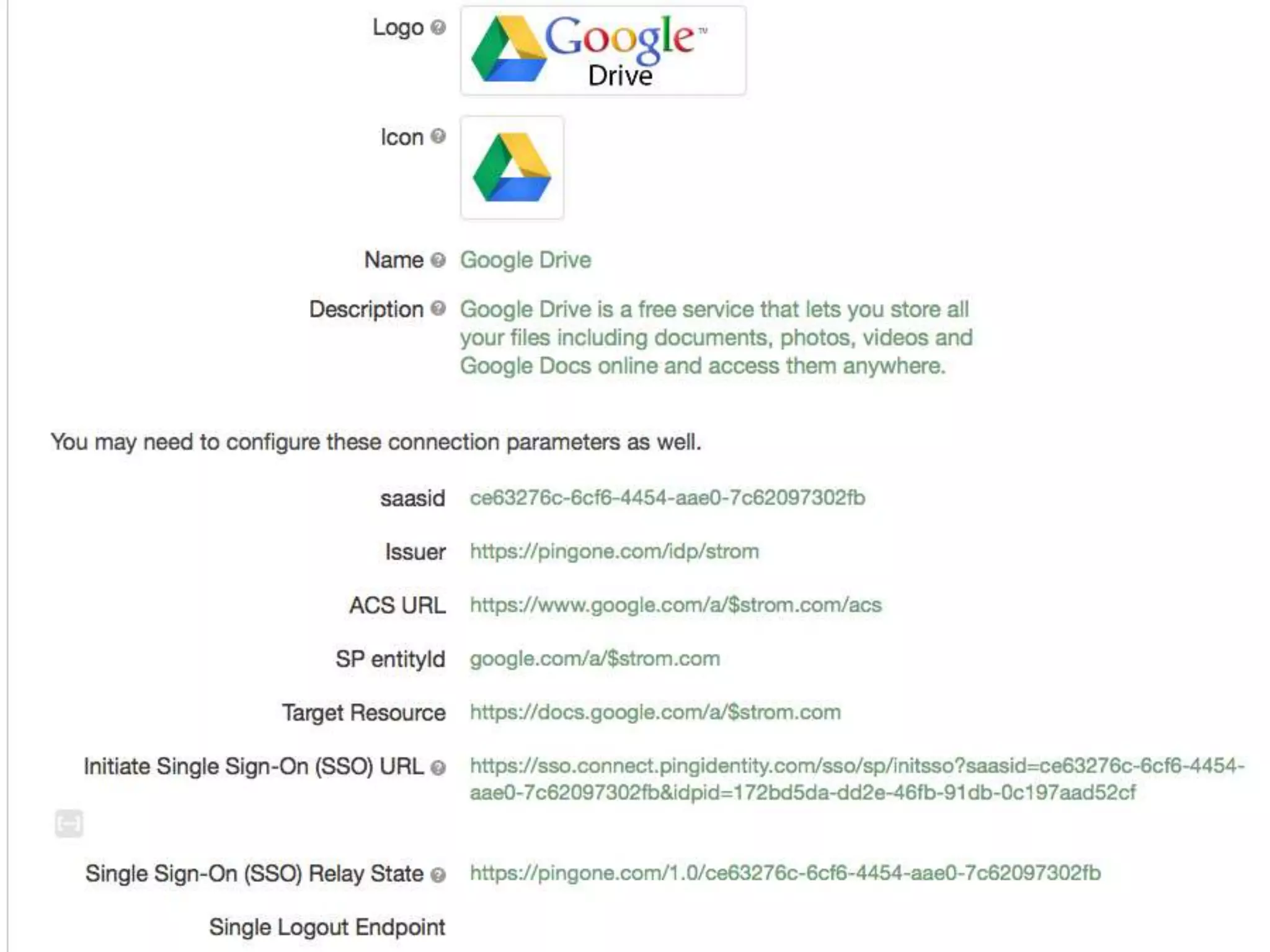
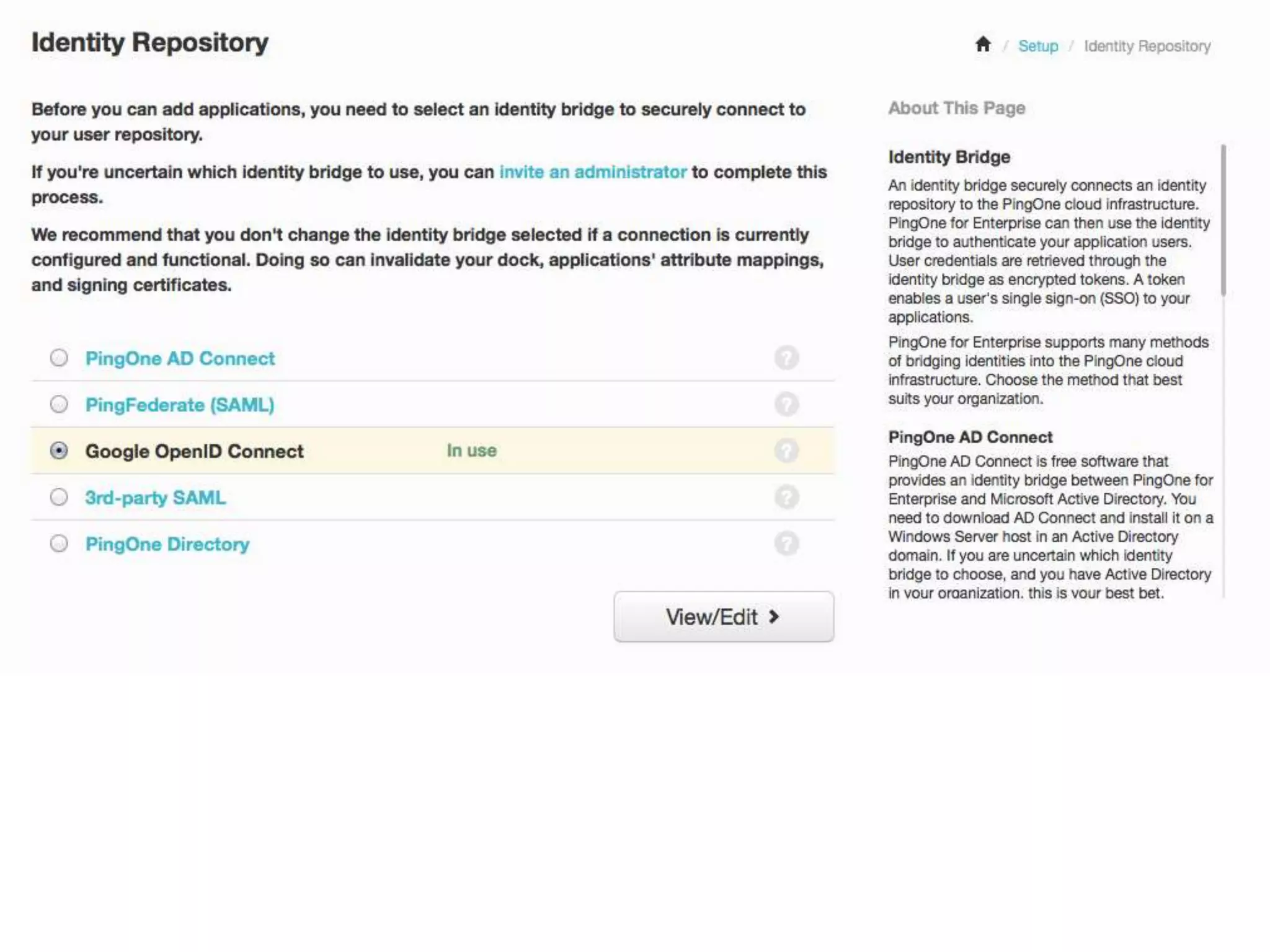
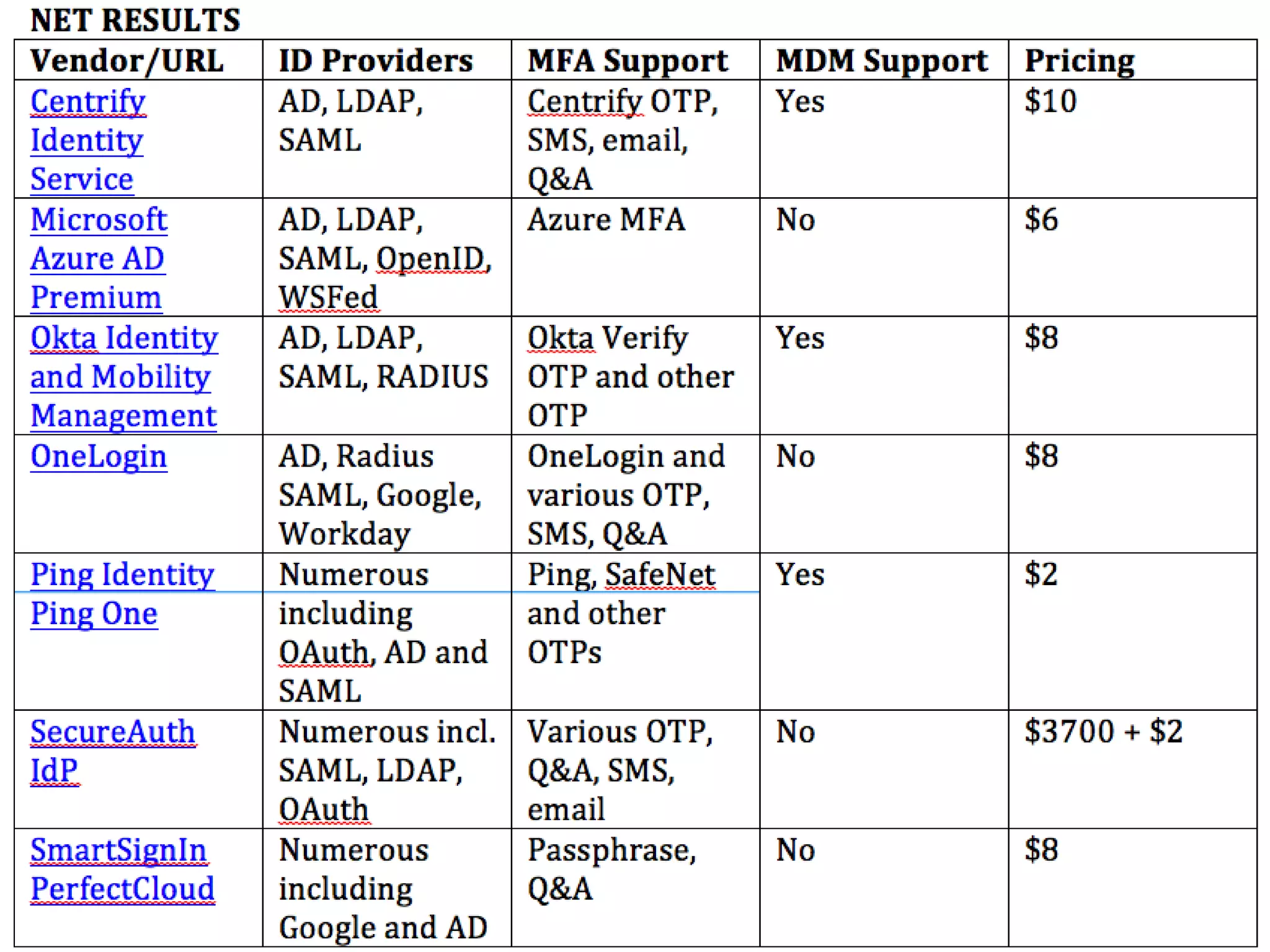
The document summarizes new developments in single sign-on (SSO) tools, including acquisitions and product launches. It reviews several SSO products and notes other vendors who declined participation. Five trends are highlighted: 1) growing use of multi-factor authentication, 2) increased integration with mobile device management, 3) cloud services dominance, 4) identity providers, and 5) proliferation of applications. The author provides contact information and links for additional information.