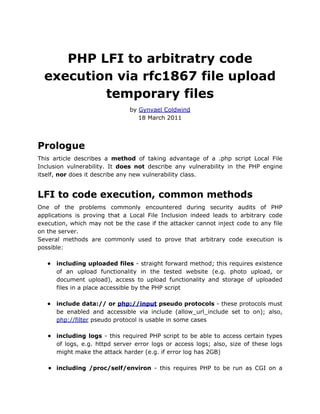
PHP LFI to Arbitrary Code Execution via rfc1867 file upload temporary files
•
0 likes•40 views
This document discusses exploiting PHP local file inclusion (LFI) vulnerabilities to achieve arbitrary code execution by including PHP's temporary upload files. On Windows, the random filenames for these temporary files can be brute forced since only the lower 16 bits of the random number are used, limiting possibilities to 65,535 files. On Linux, including these temporary files may be possible if an attacker can list files in the upload directory via a race condition or view the PHP $_FILES array.
Report
Share
Report
Share
Download to read offline
Recommended
IPSEC

VPNs and network security
En savoir plus sur www.opensourceschool.fr
Ce support est diffusé sous licence Creative Commons (CC BY-SA 3.0 FR)
Attribution - Partage dans les Mêmes Conditions 3.0 France
Php advance

The PHP date() function formats timestamps to readable dates and times. It takes a format string as the first parameter to specify how the date/time should be formatted. Common format characters include d for day, m for month, and Y for year. The date() function can also take an optional second parameter, which is a timestamp. If no timestamp is provided, it will use the current date and time. Cookies are often used to identify users across multiple pages. The setcookie() function creates a cookie, while $_COOKIE retrieves cookie values. Sessions in PHP allow information to be stored and retrieved across multiple pages for a single user.
How PHP works 

PHP may seem to be a very easy language but many of don't know how PHP works. We will discuss the less known facts about PHP and we will also cover some common type of software design patterns used with PHP
paradise city

Docx4j is a Java library for working with docx, pptx, and xlsx files. It can open these files programmatically by unzipping the package and parsing the XML. This allows the file contents to be manipulated and modified in Java. The document provides an overview of docx4j's capabilities, dependencies, usage examples, and getting started information for developers.
Varnish : Advanced and high-performance HTTP caching

En savoir plus sur www.opensourceschool.fr
Ce support est diffusé sous licence Creative Commons (CC BY-SA 3.0 FR) Attribution - Partage dans les Mêmes Conditions 3.0 France
Plan :
1. Reverse proxies
2. Varnish overview
3. VCL
4. CLI tools
Fluentd meetup dive into fluent plugin (outdated)

Fluentd meetup in Japan. I talked about "Dive into Fluent plugin".
Some contents are outdated. See this slide: http://www.slideshare.net/repeatedly/dive-into-fluentd-plugin-v012
Interoperable PHP

Interoperability with the focus on PHP. Some pure PHP details, internal details are making it interesting for regular PHP developers as well as for extension developers.
Monitoring : The art of knowing when and why things go wrong

En savoir plus sur www.opensourceschool.fr
Ce support est diffusé sous licence Creative Commons (CC BY-SA 3.0 FR) Attribution - Partage dans les Mêmes Conditions 3.0 France
Plan :
1 Principles
2 Monitoring tools
3 Reading graphs
4 Real-life examples
Recommended
IPSEC

VPNs and network security
En savoir plus sur www.opensourceschool.fr
Ce support est diffusé sous licence Creative Commons (CC BY-SA 3.0 FR)
Attribution - Partage dans les Mêmes Conditions 3.0 France
Php advance

The PHP date() function formats timestamps to readable dates and times. It takes a format string as the first parameter to specify how the date/time should be formatted. Common format characters include d for day, m for month, and Y for year. The date() function can also take an optional second parameter, which is a timestamp. If no timestamp is provided, it will use the current date and time. Cookies are often used to identify users across multiple pages. The setcookie() function creates a cookie, while $_COOKIE retrieves cookie values. Sessions in PHP allow information to be stored and retrieved across multiple pages for a single user.
How PHP works 

PHP may seem to be a very easy language but many of don't know how PHP works. We will discuss the less known facts about PHP and we will also cover some common type of software design patterns used with PHP
paradise city

Docx4j is a Java library for working with docx, pptx, and xlsx files. It can open these files programmatically by unzipping the package and parsing the XML. This allows the file contents to be manipulated and modified in Java. The document provides an overview of docx4j's capabilities, dependencies, usage examples, and getting started information for developers.
Varnish : Advanced and high-performance HTTP caching

En savoir plus sur www.opensourceschool.fr
Ce support est diffusé sous licence Creative Commons (CC BY-SA 3.0 FR) Attribution - Partage dans les Mêmes Conditions 3.0 France
Plan :
1. Reverse proxies
2. Varnish overview
3. VCL
4. CLI tools
Fluentd meetup dive into fluent plugin (outdated)

Fluentd meetup in Japan. I talked about "Dive into Fluent plugin".
Some contents are outdated. See this slide: http://www.slideshare.net/repeatedly/dive-into-fluentd-plugin-v012
Interoperable PHP

Interoperability with the focus on PHP. Some pure PHP details, internal details are making it interesting for regular PHP developers as well as for extension developers.
Monitoring : The art of knowing when and why things go wrong

En savoir plus sur www.opensourceschool.fr
Ce support est diffusé sous licence Creative Commons (CC BY-SA 3.0 FR) Attribution - Partage dans les Mêmes Conditions 3.0 France
Plan :
1 Principles
2 Monitoring tools
3 Reading graphs
4 Real-life examples
Unix Basics 04sp

Unix is a multi-user networked operating system that handles files, runs programs, and handles input/output. It is designed for server use and networking is intrinsic. Each user has their own settings and permissions, and multiple users can be logged in simultaneously. The document then provides information about accessing Unix servers from Windows and using basic commands like ls, cd, mkdir and rm to navigate directories and manage files.
Python - basics

Python was created in 1980 by Guido Van Rossum. There are differences between Python versions 2.x and 3.x related to compatibility, understandability, maturity, and robustness. Some frameworks like Twisted and gevent have not yet migrated to Python 3.x, while others like NumPy, Django, Flask, CherryPy, Pyramid, PIL, cx_Freeze, and Py2exe have migrated. The document also includes code examples and information about a Python developer.
WEB PROGRAMMING UNIT VI BY BHAVSINGH MALOTH

This document discusses advanced Perl concepts including finer points of looping, using pack and unpack, working with files and directories, eval, data structures, packages, modules, objects, and interfacing with the operating system. It provides examples and explanations of continue blocks, multiple loop variables, subroutine prototypes, determining calling context, packing and unpacking data, opening, reading and writing files, getting file information, working with directories, using eval, defining arrays of arrays, packages, modules, BEGIN and END blocks, and the basics of defining objects and classes in Perl.
Unit 7

The document discusses various types of files in UNIX/Linux systems such as regular files, directory files, device files, FIFO files, and symbolic links. It describes how each file type is created and used. It also covers UNIX file attributes, inodes, and how the kernel manages file access through system calls like open, read, write, and close.
Development and deployment with composer and kite

A short introduction into development and deployment with kite, another PHP build and deployment tool
Delphi L05 Files and Dialogs

The document provides an introduction to event-driven programming and forms using Delphi. It discusses files and dialogs, including file processing routines for input and output, common file types, and examples of using files. It also covers media players, open and save dialogs, and the TFileRun component for executing files. Key points include how to assign, read from, write to, and close files, as well as how open and save dialogs can be used to select files without directly opening or saving them.
Threat Modeling: Applied on a Publish-Subscribe Architectural Style

1. Introduction to threat modeling.
2. Applying threat modeling to identify security vulnerabilities and security threats on a simplified real-world system.
IPC mechanisms in windows

A presentation that briefly describes different techniques of inter-process communication mechanisms in Windows operating system
parenscript-tutorial

This document provides a tutorial on using ParenScript, a tool for embedding Lisp code into JavaScript and HTML documents. It demonstrates several examples of using ParenScript, including embedding a simple onclick handler, generating a JavaScript file from ParenScript code, and rewriting an existing slideshow script in ParenScript. The slideshow example shows how to integrate data from Common Lisp into the generated JavaScript code to customize the behavior. Overall, the tutorial provides a good introduction to basic ParenScript usage and concepts through examples.
Kerberos : The network authentification protocol

En savoir plus sur : www.opensourceschool.fr
Plan :
1. The Kerberos Protocol
2. Kerberos implementations
3. Kerberos for web applications
4. Lab
Introduction To Embedding The PH7 PHP Engine in a C/C++ Host Application.

PH7 is an embeddable PHP engine written in C that allows hosting applications to compile and execute PHP scripts directly without the overhead of CGI or other process-based approaches. It implements most of PHP 5.3 and introduces extensions. PH7 is highly portable, runs as a library, and has a small footprint, making it suitable for embedded systems. This document provides an overview of PH7 and instructions for getting started with a simple example C program that uses PH7 to execute a PHP script directly within the parent process.
PASTE: A Network Programming Interface for Non-Volatile Main Memory

The document describes PASTE, a network programming interface for non-volatile main memory. PASTE aims to enable durable zero-copy networking to NVMM and help applications organize persistent data structures on NVMM. It allows applications to use TCP/IP while protecting data. PASTE offers high performance even without native NVMM support by leveraging techniques from modern network stacks. Evaluation shows PASTE outperforms existing write-ahead logging and B+tree implementations for NVMM storage and is applicable to systems like Redis, packet logging middleboxes, and scalable NFV backends.
Nguyễn Vũ Hưng: Basic Linux Power Tools 

The document provides an overview of the contents of a training on the Unix and GNU/Linux command line. It covers topics such as shells and filesystem structure, file handling commands, standard input/output redirection, task control, text editing and system administration basics. The training aims to teach users full control of tasks and how to get help and find resources on the command line.
Unit VI 

This document provides an overview of advanced Perl concepts including:
1. Finer points of looping, including the continue block and multiple loop variables. Subroutine prototypes allow specifying the number and types of arguments.
2. Working with files using filehandles for reading, writing, and appending. Functions like open, close, rename, unlink for file operations.
3. Working with directories using opendir, readdir, rewinddir and related functions.
4. EVAL for evaluating strings and blocks of code. Packages for namespacing and modules. BEGIN and END blocks act as constructors and destructors.
3 sentences or less.
Tribal Nova Docker feedback

A document about what we learnt while introducing Docker at the Tribal Nova company, and the migration of our backend projects as containers.
The layout is really not my strength...
Tips and Tricks for Increased Development Efficiency

Short presentation targetted at university students showing some tools and software that are usually not talked about in courses which helps development productivity.
Volatile memory analysis

The document discusses the Volatility Framework, which is an open-source tool for extracting digital artifacts from volatile memory (RAM) samples on Windows, Linux, and Mac OS X systems. It provides commands to analyze processes, modules, memory, and other kernel objects in memory images. The summary includes high-level information on the supported operating systems, file formats, and some example commands like pslist, modules, and dlldump.
Remote file path traversal attacks for fun and profit

An end-to-end demo of how to exploit file path construction issues as well as how to mitigate this attack is given.
PHP {in}security

Short presentation on techniques for protecting against vulnerabilities in commonly available PHP packages using a combination of Apache + FastCGI + suEXEC + chroot + mod_security2
John's Top PECL Picks

A presentation I gave at PHP Quebec, 2006 on some of the less known and very powerful PECL extensions available for PHP
php

This document provides instructions for installing PHP4 on an Andrew Linux system, including modifying configuration files to load the PHP module and Apache web server, testing with a sample PHP file, and additional resources for more information on the Andrew package and Apache configuration systems. Key steps include editing /etc/package.proto and running /etc/mpp-package to update the system, modifying /etc/httpd.conf to handle PHP files, and creating a test PHP file to validate the installation.
php

This document provides instructions for installing PHP4 on an Andrew Linux system, including modifying configuration files to load the PHP module and Apache web server, testing with a sample PHP file, and additional resources for more information on the Andrew package and Apache configuration systems. Key steps include editing /etc/package.proto and running /etc/mpp-package to update the system, modifying /etc/httpd.conf to handle PHP files, and creating a test PHP file to validate the installation.
More Related Content
What's hot
Unix Basics 04sp

Unix is a multi-user networked operating system that handles files, runs programs, and handles input/output. It is designed for server use and networking is intrinsic. Each user has their own settings and permissions, and multiple users can be logged in simultaneously. The document then provides information about accessing Unix servers from Windows and using basic commands like ls, cd, mkdir and rm to navigate directories and manage files.
Python - basics

Python was created in 1980 by Guido Van Rossum. There are differences between Python versions 2.x and 3.x related to compatibility, understandability, maturity, and robustness. Some frameworks like Twisted and gevent have not yet migrated to Python 3.x, while others like NumPy, Django, Flask, CherryPy, Pyramid, PIL, cx_Freeze, and Py2exe have migrated. The document also includes code examples and information about a Python developer.
WEB PROGRAMMING UNIT VI BY BHAVSINGH MALOTH

This document discusses advanced Perl concepts including finer points of looping, using pack and unpack, working with files and directories, eval, data structures, packages, modules, objects, and interfacing with the operating system. It provides examples and explanations of continue blocks, multiple loop variables, subroutine prototypes, determining calling context, packing and unpacking data, opening, reading and writing files, getting file information, working with directories, using eval, defining arrays of arrays, packages, modules, BEGIN and END blocks, and the basics of defining objects and classes in Perl.
Unit 7

The document discusses various types of files in UNIX/Linux systems such as regular files, directory files, device files, FIFO files, and symbolic links. It describes how each file type is created and used. It also covers UNIX file attributes, inodes, and how the kernel manages file access through system calls like open, read, write, and close.
Development and deployment with composer and kite

A short introduction into development and deployment with kite, another PHP build and deployment tool
Delphi L05 Files and Dialogs

The document provides an introduction to event-driven programming and forms using Delphi. It discusses files and dialogs, including file processing routines for input and output, common file types, and examples of using files. It also covers media players, open and save dialogs, and the TFileRun component for executing files. Key points include how to assign, read from, write to, and close files, as well as how open and save dialogs can be used to select files without directly opening or saving them.
Threat Modeling: Applied on a Publish-Subscribe Architectural Style

1. Introduction to threat modeling.
2. Applying threat modeling to identify security vulnerabilities and security threats on a simplified real-world system.
IPC mechanisms in windows

A presentation that briefly describes different techniques of inter-process communication mechanisms in Windows operating system
parenscript-tutorial

This document provides a tutorial on using ParenScript, a tool for embedding Lisp code into JavaScript and HTML documents. It demonstrates several examples of using ParenScript, including embedding a simple onclick handler, generating a JavaScript file from ParenScript code, and rewriting an existing slideshow script in ParenScript. The slideshow example shows how to integrate data from Common Lisp into the generated JavaScript code to customize the behavior. Overall, the tutorial provides a good introduction to basic ParenScript usage and concepts through examples.
Kerberos : The network authentification protocol

En savoir plus sur : www.opensourceschool.fr
Plan :
1. The Kerberos Protocol
2. Kerberos implementations
3. Kerberos for web applications
4. Lab
Introduction To Embedding The PH7 PHP Engine in a C/C++ Host Application.

PH7 is an embeddable PHP engine written in C that allows hosting applications to compile and execute PHP scripts directly without the overhead of CGI or other process-based approaches. It implements most of PHP 5.3 and introduces extensions. PH7 is highly portable, runs as a library, and has a small footprint, making it suitable for embedded systems. This document provides an overview of PH7 and instructions for getting started with a simple example C program that uses PH7 to execute a PHP script directly within the parent process.
PASTE: A Network Programming Interface for Non-Volatile Main Memory

The document describes PASTE, a network programming interface for non-volatile main memory. PASTE aims to enable durable zero-copy networking to NVMM and help applications organize persistent data structures on NVMM. It allows applications to use TCP/IP while protecting data. PASTE offers high performance even without native NVMM support by leveraging techniques from modern network stacks. Evaluation shows PASTE outperforms existing write-ahead logging and B+tree implementations for NVMM storage and is applicable to systems like Redis, packet logging middleboxes, and scalable NFV backends.
Nguyễn Vũ Hưng: Basic Linux Power Tools 

The document provides an overview of the contents of a training on the Unix and GNU/Linux command line. It covers topics such as shells and filesystem structure, file handling commands, standard input/output redirection, task control, text editing and system administration basics. The training aims to teach users full control of tasks and how to get help and find resources on the command line.
Unit VI 

This document provides an overview of advanced Perl concepts including:
1. Finer points of looping, including the continue block and multiple loop variables. Subroutine prototypes allow specifying the number and types of arguments.
2. Working with files using filehandles for reading, writing, and appending. Functions like open, close, rename, unlink for file operations.
3. Working with directories using opendir, readdir, rewinddir and related functions.
4. EVAL for evaluating strings and blocks of code. Packages for namespacing and modules. BEGIN and END blocks act as constructors and destructors.
3 sentences or less.
Tribal Nova Docker feedback

A document about what we learnt while introducing Docker at the Tribal Nova company, and the migration of our backend projects as containers.
The layout is really not my strength...
Tips and Tricks for Increased Development Efficiency

Short presentation targetted at university students showing some tools and software that are usually not talked about in courses which helps development productivity.
Volatile memory analysis

The document discusses the Volatility Framework, which is an open-source tool for extracting digital artifacts from volatile memory (RAM) samples on Windows, Linux, and Mac OS X systems. It provides commands to analyze processes, modules, memory, and other kernel objects in memory images. The summary includes high-level information on the supported operating systems, file formats, and some example commands like pslist, modules, and dlldump.
Remote file path traversal attacks for fun and profit

An end-to-end demo of how to exploit file path construction issues as well as how to mitigate this attack is given.
What's hot (18)
Threat Modeling: Applied on a Publish-Subscribe Architectural Style

Threat Modeling: Applied on a Publish-Subscribe Architectural Style
Introduction To Embedding The PH7 PHP Engine in a C/C++ Host Application.

Introduction To Embedding The PH7 PHP Engine in a C/C++ Host Application.
PASTE: A Network Programming Interface for Non-Volatile Main Memory

PASTE: A Network Programming Interface for Non-Volatile Main Memory
Tips and Tricks for Increased Development Efficiency

Tips and Tricks for Increased Development Efficiency
Remote file path traversal attacks for fun and profit

Remote file path traversal attacks for fun and profit
Similar to PHP LFI to Arbitrary Code Execution via rfc1867 file upload temporary files
PHP {in}security

Short presentation on techniques for protecting against vulnerabilities in commonly available PHP packages using a combination of Apache + FastCGI + suEXEC + chroot + mod_security2
John's Top PECL Picks

A presentation I gave at PHP Quebec, 2006 on some of the less known and very powerful PECL extensions available for PHP
php

This document provides instructions for installing PHP4 on an Andrew Linux system, including modifying configuration files to load the PHP module and Apache web server, testing with a sample PHP file, and additional resources for more information on the Andrew package and Apache configuration systems. Key steps include editing /etc/package.proto and running /etc/mpp-package to update the system, modifying /etc/httpd.conf to handle PHP files, and creating a test PHP file to validate the installation.
php

This document provides instructions for installing PHP4 on an Andrew Linux system, including modifying configuration files to load the PHP module and Apache web server, testing with a sample PHP file, and additional resources for more information on the Andrew package and Apache configuration systems. Key steps include editing /etc/package.proto and running /etc/mpp-package to update the system, modifying /etc/httpd.conf to handle PHP files, and creating a test PHP file to validate the installation.
File upload php

The PHP script uses the HTTP_Upload class to handle multiple file uploads from an HTML form. It creates 5 instances of the HTTP_Upload class, one for each file upload field. It checks that the files were uploaded successfully and moves them to the destination folder. Any errors are displayed to the user.
<?php
// Destination folder for uploaded files
$destination_folder = '/homework_submissions';
// Loop through each file upload field
for($i=1; $i<=5; $i++) {
// Create HTTP_Upload instance
$
Php.ppt

PHP is a widely-used scripting language for web development that is embedded into HTML. It runs on web servers and takes PHP code as input to create web pages as output. To use PHP for websites, you need PHP itself installed on a web server along with having a web browser. This document provides instructions on installing PHP and configuring it to work with an Apache web server on Linux. It describes downloading and extracting the PHP files, editing the configuration file php.ini, and restarting the web server for the changes to take effect.
15955 state-of-the-art-post-exploitation-in-hardened-php-environments

This document discusses protections against executing arbitrary PHP code on hardened PHP environments after code execution is achieved. It introduces new techniques to overcome many protections by combining local PHP exploits that leak information and cause memory corruption. Specifically, it shows how important memory structures can be leaked and manipulated to deactivate protections within PHP, Suhosin, the C library, filesystems, compilers, and the operating system kernel.
Download It

This document discusses securing Apache and PHP configurations. It begins by noting that LAMP stacks are commonly used but often insecurely configured. It then provides background on Apache and PHP, explaining how PHP can run as an Apache module or CGI binary. Running as a module provides performance benefits but less security, while CGI binaries allow running as separate users via suEXEC/suPHP. Alternative solutions like ModSecurity, Suhosin, and PHP hardening patches are also discussed. The document concludes that the optimal configuration depends on needs and that awareness of platform configurations is important.
Php basics

PHP is a server-side scripting language commonly used for web development. It allows variables, functions, and other elements to be run on the server rather than in the user's browser. Key elements of PHP include variables, operators, echo and print functions to output text, and the ability to open, read, and write files. Sessions and cookies can also be used to store and retrieve information from the user's browser across multiple page views.
Lfi

Local File Inclusion (LFI) vulnerabilities allow an attacker to include files from a web server by manipulating input that is used to include files. For example, a script that includes files based on a page parameter, like script.php?page=index.html, could be exploited by changing the page parameter to try and include files like ../../../../etc/passwd. Successful exploitation can reveal sensitive information like the server's password file. LFI vulnerabilities are common and can often be exploited through PHP wrappers like php://input or php://filter to include files or execute system commands on the server.
Php

The document summarizes PHP, an open-source scripting language commonly used for web development. PHP can be embedded into HTML and is interpreted by web servers to create dynamic web pages. Key points covered include PHP's origins, popularity, uses, and how to install and configure it by placing PHP files on a web server and ensuring the server can parse the files. The document also provides links to tutorials on installing PHP and its dependencies.
Phalcon 2 - PHP Brazil Conference

This document provides an overview of the Phalcon PHP framework. It discusses why frameworks are important for PHP development and how traditional frameworks work. It then explains how Phalcon is different as it is implemented as a PHP extension written in C, making it faster than traditional frameworks. The document demonstrates how to install Phalcon, create a basic project structure, define controllers and models, and connect to a database.
Php Conference Brazil - Phalcon Giant Killer

This document provides information about the Phalcon PHP framework. It begins with an overview of how PHP works and how traditional PHP frameworks work in comparison. It then discusses how PHP extensions and the Phalcon framework specifically work. Phalcon is introduced as a full stack PHP framework written as a C extension for high performance. Details are provided about how Phalcon works, compares to other frameworks in terms of performance, and how to install, configure, and create projects with Phalcon.
"15 Technique to Exploit File Upload Pages", Ebrahim Hegazy

During the session we will go through different methods of exploiting file upload pages in order to trigger Remote Code Execution, SQL Injection, Directory Traversal, DOS, Cross Site Scripting and else of web application vulnerabilities with demo codes. Also, we will see things from both Developers and Attackers side. What are the protections done by Developers to mitigate file upload issues by validating File Name, File Content-Type, actual File Content and how to bypass it All using 15 Technique!
Information on PHP Handlers

The term “PHP handlers” refers to a certain type of Apache module and these contain those libraries that are used by the Apache web server for running and interpreting PHP code.
Secure PHP environment

This document summarizes Stefan Neufeind's presentation on securing PHP environments. The presentation covers basic security steps like physical, network, and application security. It discusses approaches for separating users like suPHP and FastCGI. It also describes hardening PHP using a patch that adds checks, limitations, and filters to enhance security. The goal is to help attendees understand how to configure a secure PHP server environment and harden the PHP application itself against common attacks.
Composer namespacing

Welcome to the wonderful world of composer,
We will see what is composer, how we can use it.
Namespacing (What, How & Why)
& Autoloading your own code using composer
File handling C program

Wherever there is a need to handle large volumes of data, it is advantageous to store data on the disks and read whenever necessary. This method employs the concept of files to store data. A file is a place on disk where a group of related data is stored.file handling c programming tutorial
Piattaforma Web Linux completa dai sorgenti

Come creare una piattaforma Web basata su Linux partendo dai sorgenti, con PHP, Java, .NET (Mono) su Apache. Sperimentata in produzione.
Php ppt

PHP is a widely used scripting language originally designed for web development. It code is embedded into HTML and interpreted by a web server to produce dynamic web pages. PHP can also be run from the command line or used for desktop applications. It is available on most operating systems and works with many databases. The PHP source code is free to use and customize.
Similar to PHP LFI to Arbitrary Code Execution via rfc1867 file upload temporary files (20)
15955 state-of-the-art-post-exploitation-in-hardened-php-environments

15955 state-of-the-art-post-exploitation-in-hardened-php-environments
"15 Technique to Exploit File Upload Pages", Ebrahim Hegazy

"15 Technique to Exploit File Upload Pages", Ebrahim Hegazy
More from Attaporn Ninsuwan
J query fundamentals

This document is a table of contents and introduction for a book titled "jQuery Fundamentals" by Rebecca Murphey. The book covers jQuery basics, core concepts, events, effects, Ajax, plugins, and advanced topics. It includes over 50 code examples to demonstrate jQuery syntax and techniques. The book is available under a Creative Commons license and the source code is hosted on GitHub.
Jquery enlightenment

This document provides a preface and table of contents for a book on jQuery concepts. The preface explains that the book is intended to teach intermediate and advanced jQuery concepts through code examples. It highlights some stylistic approaches used in the book, such as emphasizing code over text explanations and using color coding. It also defines some key terms that will be used, and recommends reviewing the jQuery documentation and understanding how the text() method works before reading the book. The table of contents then outlines the book's 12 chapters and their respective sections, which cover topics like selecting, traversing, manipulating, events, plugins and more.
Br ainfocom94

This document proposes techniques for embedding unique codewords in electronic documents to discourage illicit copying and distribution. It describes three coding methods - line-shift coding, word-shift coding, and feature coding - that alter document formatting or text elements in subtle, hard-to-detect ways. Experimental results show the line-shift coding method can reliably decode documents even after photocopying, enabling identification of the intended recipient. The techniques aim to make unauthorized distribution at least as difficult as obtaining documents legitimately from the publisher.
Chapter 12 - Computer Forensics

This document discusses the field of computer forensics. It defines computer forensics as the collection, preservation, and analysis of computer-related evidence. The goal is to provide solid legal evidence that can be admitted in court and understood by laypeople. Computer forensics is used to investigate various incidents including human behavior like fraud, physical events like hardware failures, and organizational issues like staff changes. It aims to determine the root cause of system disruptions and failures.
Techniques for data hiding p

This document discusses techniques for data hiding, which involves embedding additional data into digital media files like images, audio, or text. It describes several constraints on data hiding, such as the amount of data to hide, ensuring the data remains intact if the file is modified, and preventing unauthorized access to the hidden data. The document outlines traditional and novel data hiding techniques and evaluates them for applications like copyright protection, tamper-proofing, and adding supplemental data to files. It also discusses tradeoffs between hiding more data versus making the data more robust against modifications to the file.
Stop badware infected_sites_report_062408

This document summarizes an analysis of over 200,000 websites engaged in badware behavior according to Google's Safe Browsing initiative. The analysis found that over half of infected sites were located in China, with the top three Chinese network blocks accounting for 68% of infections in that country. In contrast, infected sites in the US were more distributed. Compared to the previous year, the total number of infected sites increased, likely due to expanded scanning and increased malware distribution through websites.
Steganography past-present-future 552

Steganography has been used for over 2500 years to hide secret messages. The paper explores steganography's history from ancient times through modern digital applications. It discusses early examples like Johannes Trithemius' steganographic treatise in the 15th century. Modern uses include microdots, digital images, audio, and digital watermarks for copyright protection. Terrorist groups may use steganography but there is no public evidence yet. Steganography continues to evolve with technology while attackers work to defeat new techniques.
Ch03-Computer Security

The document discusses various cryptographic techniques including symmetric and asymmetric encryption. Symmetric encryption uses the same key for encryption and decryption, while asymmetric encryption uses two different keys. The document then describes the Data Encryption Standard (DES) algorithm and its variants, including Triple DES. It also covers the Advanced Encryption Standard (AES) algorithm, its design principles, and modes of operation for block ciphers like ECB, CBC, CFB and OFB.
Ch02-Computer Security

This document discusses the topic of steganography, which is hiding secret messages within other harmless messages. It outlines different techniques for hiding messages in text, images, and audio files. For text, it describes line shift coding, word shift coding, and feature coding methods. For images, it explains least significant bit insertion and exploiting the limitations of the human visual system. For audio, it mentions low-bit encoding and other techniques like phase coding and spread spectrum. It also discusses steganalysis, which aims to detect and destroy hidden messages within files.
Ch01-Computer Security

This document discusses the need for computer security and provides an introduction to key concepts. It explains that security is necessary to protect vital information, provide authentication and access control, and ensure availability of resources. The document then outlines common security threats like firewall exploits, software bugs, and denial of service attacks. It also discusses basic security components of confidentiality, integrity, and availability as well as goals of preventing attacks, detecting violations, and enabling recovery.
Ch8-Computer Security

The document discusses various types of malicious programs including buffer overflows, viruses, worms, Trojan horses, backdoors, and logic bombs. It describes how buffer overflows can corrupt the program stack and be exploited by attackers. It explains that viruses attach themselves to other programs and replicate, worms replicate across networks, and Trojan horses masquerade as legitimate programs. It also outlines different approaches for antivirus software including signature-based, heuristic, activity monitoring, and full-featured protection.
Ch7-Computer Security

This document discusses various topics relating to web security, including:
1) Different types of web pages like static, dynamic, and active pages and the technologies used to create them like JavaScript, Java, and CGI.
2) Security issues associated with technologies like ActiveX, Java applets, JavaScript, and cookies.
3) Protocols for secure communication like HTTPS, digital certificates, and single sign-on systems.
4) Methods for secure electronic commerce including SET and digital cash technologies.
Ch6-Computer Security

This document provides an overview of network security topics including attacks like diffing, sniffing, session hijacking and spoofing. It discusses protocols for secure communication including SSL, TLS and IPSec. SSL and TLS provide security at the transport layer by encrypting data between a client and server. IPSec provides security at the network layer for both transport and tunnel modes. Authentication Header and Encapsulating Security Payload are the two security protocols used in IPSec.
Ch06b-Computer Security

This document provides an overview of network security topics including diffing, sniffing, session hijacking, spoofing, SSL, TLS, IPSec, and VPNs. It discusses how these attacks work and methods to protect against them, such as encryption. Network layer security protocols like IPSec are described, which uses authentication headers or encapsulating security payloads to provide security services to packets. Transport layer security protocols SSL and TLS are also summarized, including how they establish encrypted sessions between clients and servers.
Ch5-Computer Security

This document discusses various topics related to computer security authorization, including multilevel security models like Bell-LaPadula and Biba's model, covert channels, inference control, CAPTCHAs, firewalls, and intrusion detection systems. It also provides an overview of network layers like the network layer, transport layer, TCP, and UDP. The key models discussed are Bell-LaPadula for confidentiality and Biba's model for integrity. Covert channels, inference control, and intrusion detection systems are described as techniques for authorization and access control.
Ch04-Computer Security

This document discusses various methods of authentication, including message authentication, entity authentication, and digital signatures. It describes techniques such as hashing, message authentication codes (MACs), digital signatures using RSA, and challenge-response authentication. It also covers other authentication methods such as passwords, biometrics, and zero-knowledge proofs. The goal of authentication is to verify the identity of entities and ensure the integrity and authenticity of messages.
Chapter5 - The Discrete-Time Fourier Transform

This document discusses the discrete-time Fourier transform (DTFT). It begins by introducing the DTFT and how it can be used to represent aperiodic signals as the sum of complex exponentials. Several properties of the DTFT are then discussed, including linearity, time/frequency shifting, periodicity, and conjugate symmetry. Examples are provided to illustrate how to compute the DTFT of simple signals. The document also discusses how the DTFT can be used to represent periodic signals and impulse trains.
Chapter4 - The Continuous-Time Fourier Transform

This document discusses the continuous-time Fourier transform. It begins by developing the Fourier transform representation of aperiodic signals as the limit of Fourier series coefficients as the period increases. It then defines the Fourier transform pairs and discusses properties like convergence. Several examples of calculating the Fourier transform of common signals like exponentials, pulses and periodic signals are provided. Key concepts like the sinc function are also introduced.
Chapter3 - Fourier Series Representation of Periodic Signals

This document discusses Fourier series representation of periodic signals. It introduces continuous-time periodic signals and their representation as a linear combination of harmonically related complex exponentials. The coefficients in the Fourier series representation can be determined by multiplying both sides of the representation by complex exponentials and integrating over one period. The key steps are: 1) multiplying both sides by e-jω0t, 2) integrating both sides from 0 to T=2π/ω0, and 3) using the fact that the integral equals T when k=n and 0 otherwise to obtain an expression for the coefficients an. Examples are provided to illustrate these concepts.
More from Attaporn Ninsuwan (20)
Chapter3 - Fourier Series Representation of Periodic Signals

Chapter3 - Fourier Series Representation of Periodic Signals
Recently uploaded
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/building-and-scaling-ai-applications-with-the-nx-ai-manager-a-presentation-from-network-optix/
Robin van Emden, Senior Director of Data Science at Network Optix, presents the “Building and Scaling AI Applications with the Nx AI Manager,” tutorial at the May 2024 Embedded Vision Summit.
In this presentation, van Emden covers the basics of scaling edge AI solutions using the Nx tool kit. He emphasizes the process of developing AI models and deploying them globally. He also showcases the conversion of AI models and the creation of effective edge AI pipelines, with a focus on pre-processing, model conversion, selecting the appropriate inference engine for the target hardware and post-processing.
van Emden shows how Nx can simplify the developer’s life and facilitate a rapid transition from concept to production-ready applications.He provides valuable insights into developing scalable and efficient edge AI solutions, with a strong focus on practical implementation.Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
Mind map of terminologies used in context of Generative AI

Mind map of common terms used in context of Generative AI.
UiPath Test Automation using UiPath Test Suite series, part 5

Welcome to UiPath Test Automation using UiPath Test Suite series part 5. In this session, we will cover CI/CD with devops.
Topics covered:
CI/CD with in UiPath
End-to-end overview of CI/CD pipeline with Azure devops
Speaker:
Lyndsey Byblow, Test Suite Sales Engineer @ UiPath, Inc.
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
GraphSummit Singapore | Neo4j Product Vision & Roadmap - Q2 2024

Maruthi Prithivirajan, Head of ASEAN & IN Solution Architecture, Neo4j
Get an inside look at the latest Neo4j innovations that enable relationship-driven intelligence at scale. Learn more about the newest cloud integrations and product enhancements that make Neo4j an essential choice for developers building apps with interconnected data and generative AI.
Microsoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

The choice of an operating system plays a pivotal role in shaping our computing experience. For decades, Microsoft's Windows has dominated the market, offering a familiar and widely adopted platform for personal and professional use. However, as technological advancements continue to push the boundaries of innovation, alternative operating systems have emerged, challenging the status quo and offering users a fresh perspective on computing.
One such alternative that has garnered significant attention and acclaim is Nitrux Linux 3.5.0, a sleek, powerful, and user-friendly Linux distribution that promises to redefine the way we interact with our devices. With its focus on performance, security, and customization, Nitrux Linux presents a compelling case for those seeking to break free from the constraints of proprietary software and embrace the freedom and flexibility of open-source computing.
UiPath Test Automation using UiPath Test Suite series, part 6

Welcome to UiPath Test Automation using UiPath Test Suite series part 6. In this session, we will cover Test Automation with generative AI and Open AI.
UiPath Test Automation with generative AI and Open AI webinar offers an in-depth exploration of leveraging cutting-edge technologies for test automation within the UiPath platform. Attendees will delve into the integration of generative AI, a test automation solution, with Open AI advanced natural language processing capabilities.
Throughout the session, participants will discover how this synergy empowers testers to automate repetitive tasks, enhance testing accuracy, and expedite the software testing life cycle. Topics covered include the seamless integration process, practical use cases, and the benefits of harnessing AI-driven automation for UiPath testing initiatives. By attending this webinar, testers, and automation professionals can gain valuable insights into harnessing the power of AI to optimize their test automation workflows within the UiPath ecosystem, ultimately driving efficiency and quality in software development processes.
What will you get from this session?
1. Insights into integrating generative AI.
2. Understanding how this integration enhances test automation within the UiPath platform
3. Practical demonstrations
4. Exploration of real-world use cases illustrating the benefits of AI-driven test automation for UiPath
Topics covered:
What is generative AI
Test Automation with generative AI and Open AI.
UiPath integration with generative AI
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

Sudheer Mechineni, Head of Application Frameworks, Standard Chartered Bank
Discover how Standard Chartered Bank harnessed the power of Neo4j to transform complex data access challenges into a dynamic, scalable graph database solution. This keynote will cover their journey from initial adoption to deploying a fully automated, enterprise-grade causal cluster, highlighting key strategies for modelling organisational changes and ensuring robust disaster recovery. Learn how these innovations have not only enhanced Standard Chartered Bank’s data infrastructure but also positioned them as pioneers in the banking sector’s adoption of graph technology.
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Full-RAG: A modern architecture for hyper-personalization

Mike Del Balso, CEO & Co-Founder at Tecton, presents "Full RAG," a novel approach to AI recommendation systems, aiming to push beyond the limitations of traditional models through a deep integration of contextual insights and real-time data, leveraging the Retrieval-Augmented Generation architecture. This talk will outline Full RAG's potential to significantly enhance personalization, address engineering challenges such as data management and model training, and introduce data enrichment with reranking as a key solution. Attendees will gain crucial insights into the importance of hyperpersonalization in AI, the capabilities of Full RAG for advanced personalization, and strategies for managing complex data integrations for deploying cutting-edge AI solutions.
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
Recently uploaded (20)
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
Mind map of terminologies used in context of Generative AI

Mind map of terminologies used in context of Generative AI
UiPath Test Automation using UiPath Test Suite series, part 5

UiPath Test Automation using UiPath Test Suite series, part 5
GraphSummit Singapore | Neo4j Product Vision & Roadmap - Q2 2024

GraphSummit Singapore | Neo4j Product Vision & Roadmap - Q2 2024
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...
UiPath Test Automation using UiPath Test Suite series, part 6

UiPath Test Automation using UiPath Test Suite series, part 6
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Full-RAG: A modern architecture for hyper-personalization

Full-RAG: A modern architecture for hyper-personalization
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
PHP LFI to Arbitrary Code Execution via rfc1867 file upload temporary files
- 1. PHP LFI to arbitratry code execution via rfc1867 file upload temporary files by Gynvael Coldwind 18 March 2011 Prologue This article describes a method of taking advantage of a .php script Local File Inclusion vulnerability. It does not describe any vulnerability in the PHP engine itself, nor does it describe any new vulnerability class. LFI to code execution, common methods One of the problems commonly encountered during security audits of PHP applications is proving that a Local File Inclusion indeed leads to arbitrary code execution, which may not be the case if the attacker cannot inject code to any file on the server. Several methods are commonly used to prove that arbitrary code execution is possible: ● including uploaded files - straight forward method; this requires existence of an upload functionality in the tested website (e.g. photo upload, or document upload), access to upload functionality and storage of uploaded files in a place accessible by the PHP script ● include data:// or php://input pseudo protocols - these protocols must be enabled and accessible via include (allow_url_include set to on); also, php://filter pseudo protocol is usable in some cases ● including logs - this required PHP script to be able to access certain types of logs, e.g. httpd server error logs or access logs; also, size of these logs might make the attack harder (e.g. if error log has 2GB) ● including /proc/self/environ - this requires PHP to be run as CGI on a
- 2. system that has the /proc pseudo-filesystem and PHP script is required to have access to the aforementioned pseudo-file ● include session files - this requires the attacker to be able to influence the value of any string in a session (to inject code, e.g. <?php phpinfo(); ? >), the sessions must be stored in a serialized session file (as e.g. x| s:19:"<?php phpinfo(); ?>"; - this is the default setting for PHP) and the PHP script must be able to access the session file (usually names /tmp/ sess_SESSIONID) ● include other files created by PHP application - this is very application and system specific, but it basically describes any other file that is created the websites functionality and the way it works, e.g. database files, cache files, application-level logs, etc Additional tools included both the poison nul byte (addressed in PHP 5.3.4[1] released 2010-12-09) and excessive slash (/) suffix into path truncation bug[2] (patched in 2009). Temporary upload file inclusion One other option is to take advantage of the way PHP handles file uploads via HTTP. This method is far less known and not really usable on platforms other than Windows (see Exploiting on Linux for details). Actually when I started writing this paper I believed that this method is not known at all, but after few days of searching and asking around I found a person (hi phunk ;>) that stumbled on this method before. Nevertheless I couldn't find any other proof of this being common knowledge, hence I decided to publish this article. PHP engine, upon receiving a POST packet with RFC 1867 coded file(s), creates one or more temporary files which are used to store the uploaded files data. A PHP script handling file uploads is required to use the move_uploaded_file function to move the uploaded temporary file to a place of it's desire (if the script requires the file to exists after it terminates that is). When the script ends PHP engine removes all temporary files for files that were uploaded (if any are left after the script ends that is). The image below shows the timeline of this behaviour:
- 3. The important fact here is that PHP engine creates the temporary files even if the PHP script does not expect them (i.e. is not an upload handling script). Hence, it is possible to send a file with arbitrary code to any PHP script, and include the temporary file that the PHP engine has created. Pros and cons Good news is that it's common for a PHP script to have access to the directory (see upload_tmp_dir in php.ini) where the temporary files are created (i.e. can include files from this directory). On the default PHP installation the upload_tmp_dir is not set - in this case either /tmp on Linux-based systems or C:WindowsTemp on Windows are used. The bad news is that the name of the temporary file is random, which renders this method unusable in most cases - it is fully exploitable on Windows and exploitable in some cases on other systems. Exploitation on Windows To generate the random name on Windows PHP uses the GetTempFileName function. Looking into documentation we can find the following explanation: The GetTempFileName function creates a temporary file name of the following form: <path><pre><uuuu>.TMP In case of PHP <path> is upload_tmp_dir (normally it's just C:WindowsTemp) and <pre> is "php" (without the quotes). The last part is described as:
- 4. <uuuu> Hexadecimal value of uUnique uUnique is one the arguments of GetTempFileName and in case of PHP, it's set to 0, which is a special value telling the function to use the current system time. The important part here can be found in the remarks section: Only the lower 16 bits of the uUnique parameter are used. This limits GetTempFileName to a maximum of 65,535 unique file names if the lpPathName and lpPrefixStringparameters remain the same. Only 65k unique names makes a brute force possible, and using current system time (number of milliseconds) makes things even simpler. However, brute force is not needed here, thanks to a certain FindFirstFile quirk [3] which allows using masks (<< as * and > as ?) in LFI paths on Windows. Thanks to this, one can form an include path like this: http://site/vuln.php?inc=c:windowstempphp<< Commonly there are other files with "php" prefix in this directory, so narrowing the mask might be required. In this case it's best to choose the widest possible mask that does not include any file (e.g. php1<< or phpA<<, in worse case php11<<, etc) and send upload-packets until the PHP engine will create a temporary file that will match the mask. Exploitation on GNU/Linux For temporary name generation PHP engine on GNU/Linux uses mkstemp from GNU libc. This function, depending on the way glibc is compiled, uses either (in pseudocode; variables are uint64_t): 1. random_value = (seed += time() ^ PID) 2. random_value = (seed += (gettimeofday().sec << 32 | gettimeofday().usec) ^ PID) 3. random_value = (seed += rdtsc ^ PID) The random_value is later written as 6 digits of k=62 (A-Za-z0-9 charset) numeric system, and appended to the "/tmp/php" prefix (unless another directory is set), e.g. /tmp/phpUs7MxA.
- 5. From the aforementioned random_value generation methods, the 3rd is most commonly used nowadays. According to initial tests I made, the random value is unpredictable enough to be considered safe against remote attacker. This leads to the assumption that using this exploitation path is possible only in these specific cases: ● When the tester is able to list the files in the upload (/tmp) directory (presumably by another PHP script) - this would require a race condition method where the tester uploads one file to a slow script (i.e. a script that runs for a relatively long time) and lists the files in the upload directory in another script, acquires the file temporary file name, and fires the LFI exploit. ● When the tester is able to list the $_FILES array in a script - this requires an even more tight race condition and is not always possible, since the attacker must obtain the $_FILES array content during upload and send another packet before the previous script ends and the temporary file is removed. This is not possible in case of buffering of PHP output (e.g. if mod_gzip is enabled in Apache). Hence, this method is usable only in some specific cases and should not be considered a generic method. See also: part 2 of "A note on research done" section. A note on research done One of the ideas I had to widen the exploitation window (i.e. the time window during which the temporary file exist) was to create an HTTP packet with e.g. 20 files (this is the default file-per-HTTP-packet limit in PHP) and send the first 19 files normally, but the last file in a slow manner (byte, sleep, byte, sleep, repeat). In theory, the previous uploaded files from the same packet should still exist until the upload will finish and the time window closes. However, it turns out that the PHP engine's upload parsing function is not executed until the whole HTTP packet arrives, thus, these files won't be yet created. Also, in some cases, when httpd has access to /proc/self/fd (commonly httpd works with privileges dropped to www-data, while /proc/self/fd has root as it's owner, hence requires root privileges to access), this method is easier to exploit by trying
- 6. to upload files (in one thread) and include /proc/self/fd/XYZ in the other (e.g. start with XYZ=10). However, the temporary file fd handle exists only between opening the temp file and closing it, so it's a very narrow time window. Uploading large files might widen this window a little though. Future work There is some room for improvements and additional research related to this method: ● test mktemp and mkstemp on other systems (*BSD, Solaris, etc) / in other libc implementations ● do proper research on mkstemp on GNU/Linux and it's predictability for both a local and a remote attacker, that has both no knowledge and knowledge of previous generated temporary names ● the FindFirstFile << quirk works now, but it may be removed later, hence doing proper research on remotly predicting the temporary file name on Windows might also be worth doing References [1] PHP 5.3 Changelog. http://php.net/ChangeLog-5.php [2] Francesco "ascii" Ongaro, Giovanni "evilaliv3" Pellerano. PHP filesystem attack vectors. http://www.evilaliv3.org/articles/php-filesystem-attack-vectors/ [3] Vladimir Vorontsov, Arthur Gerkis. Oddities of PHP file access in Windows®. Cheat-sheet, 2011. http://onsec.ru/onsec.whitepaper-02.eng.pdf Thanks to Felix Gröbert for the interesting discussion that led to this article :) Disclaimer The views expressed here are mine alone and not those of my employer.
