Ch7-Computer Security
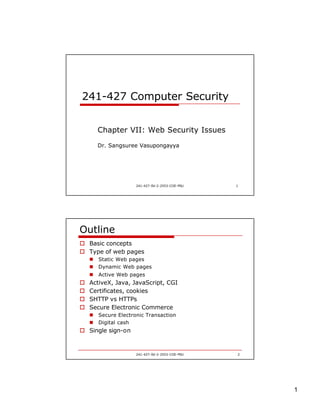
- 1. 1 241-427-SV-2-2553-COE-PSU 1 241-427 Computer Security Chapter VII: Web Security Issues Dr. Sangsuree Vasupongayya 241-427-SV-2-2553-COE-PSU 2 Outline o Basic concepts o Type of web pages n Static Web pages n Dynamic Web pages n Active Web pages o ActiveX, Java, JavaScript, CGI o Certificates, cookies o SHTTP vs HTTPs o Secure Electronic Commerce n Secure Electronic Transaction n Digital cash o Single sign-on
- 2. 2 241-427-SV-2-2553-COE-PSU 3 WWW security o Internet has grown n Availability of private or confidential information n Computer espionage n Malicious users n Gaining advantages associated with information o How can I protect my web site? 241-427-SV-2-2553-COE-PSU 4 Basic concepts o Transactions and communications between browser and Web server via HTTP protocol o Browser à HTTP request o Web server à HTTP response GET/files/new/image1 HTTP/1.1 Accept: image/gif Accept: image/jpeg HTTP /1.1 200 OK Date: Tue, 19-01-10 13:00:00 GMT Server: MyServer Content-length:3010 …….. (actual data)…. Web Browser Web Server
- 3. 3 241-427-SV-2-2553-COE-PSU 5 Types of web pages o Static web pages n Contents do not change often n Good for showing information o Dynamic web pages n Contents of a dynamic Web page can vary all day depending on a number of parameters n Involves server-side programming o Invokes a program resided on its hard disk o Access databases o Output HTML n Techniques o Microsoft’s Active Server Pages (ASP) o Sun Microsystems’s Java Servlets and Java Server Pages (JSP) 241-427-SV-2-2553-COE-PSU 6 Dynamic Web Page Web browser Web server HTTP Request Invokes an application Program in response to The HTTP request The program executes And produces HTML output HTTP Response
- 4. 4 241-427-SV-2-2553-COE-PSU 7 Active Web pages o Web server sends back an HTTP response that contains n an HTML page n A small program (script): executes on the client computer inside the Web browser o Two common types of script languages n ActiveX & Java o Web-based program is CGI (Common Gateway Interface) n Can be written in many programming languages 241-427-SV-2-2553-COE-PSU 8 ActiveX o Scripting language that makes it easier for web developers to create unique, interactive applications and web sites o Can be used with many languages n Java, VB, C++ o Developed by Microsoft initially to distributed software over the Internet o ActiveX objects (controls) n interactive graphical items on a web page n Executables n .OCX o Security concerns n No restrictions on a control’s action
- 5. 5 241-427-SV-2-2553-COE-PSU 9 ActiveX (cont.) o If the user attempts to load a control that has not been signed by a known and trusted authority o The browser will warn the user and prompt for acceptance or cancellation 241-427-SV-2-2553-COE-PSU 10 ActiveX (cont.) o Less-obvious activity w/o knowledge of the user o E.g., n Send personal or confidential information from the user’s computer over the Internet o Limited activity logging of some browsers n Difficult to identifying the dangerous control o What can we do? n Denying all ActiveX control downloads n Requiring the browser to prompt the user before download
- 6. 6 241-427-SV-2-2553-COE-PSU 11 Java o Java programs (applets) n Stored on the web server and downloaded for execution on the user’s computer when the associated web pages are loaded into a browser o Has restrictions on what it can do n Only allowed to communicate with the server that uploaded them n Limitation of back-end system access e.g., system command execution, device driver access, system library loading o However, several security holes from programming bugs have been found 241-427-SV-2-2553-COE-PSU 12 JavaScript o JacaScript n A set of extensions to increase the functionality of the browsers n An interpreted language n Not distributed as compiled programs n Often used to open, close windows, change browser settings, download and start Java programs o Privacy related security vulnerabilities n File Theft (IE 4.0, 4.01) n User file access (IE 4.0)
- 7. 7 241-427-SV-2-2553-COE-PSU 13 CGI o a program that resides on the web server as opposed to the user’s system n Form handling, advertisement switching o Server can n Redirect data to any email address, to maintain data, to adjust the content, other dynamic page creation activity o Majority of the weaknesses impact the web server n Program execute on the server o What can we do? n CGI wrappers: scripts specifically designed to perform security checks on the primary CGI script o Verifying the ownership of the CGI process o Restricting the activity of the script o Sbox, cgiwrap, suEXEC 241-427-SV-2-2553-COE-PSU 14 Applet vs ActiveX o In the past, applets have a lot of restrictions o Signed applets are allowed more access to the client computer o Applet is downloaded with an active Web page, executed inside the browser, destroyed when the user exits that Web page o ActiveX controls are free to do what they want o Once downloaded, an ActiveX control remains on the client computer until it is explicitly deleted
- 8. 8 241-427-SV-2-2553-COE-PSU 15 User Certification o Unique digital identification n Presented to other users or web sites n Relies on public key cryptography o Purpose n encrypting and decrypting e-mail n digitally sign e-mail n uniquely identify one’s self o Legally binding electronic signatures 241-427-SV-2-2553-COE-PSU 16 CA in Thailand o Thailand KPI association n http://thpki.org/about_us.php o G-CA http://www.gca.thaigov.net/ o Thai Digital ID http://www.thaidigitalid.com/ o CAT CA http://www.thaipki.com/ o TOT CA http://www.ca.tot.co.th/about.php
- 9. 9 241-427-SV-2-2553-COE-PSU 17 Certificate error 241-427-SV-2-2553-COE-PSU 18 Type of certificate error o Security certificate has been revoked o Address does not match the address in the security certificate o Security certificate is out of date o Security certificate is not from a trusted source : issued by a certification authority that is not recognized by the browser o Other problems
- 10. 10 241-427-SV-2-2553-COE-PSU 19 Cookies o A mechanism to proved a sort of memory to the browser process o Since, HTTP is stateless (no information) n How can you remember information from page to page e.g., shopping carts, travel itineraries, user names & passwords o Cookies act as a notepad by recording information that can be accessed by multiple pages o Cookie n Small piece of information (at most 4K bytes) n Containing site-specific information 241-427-SV-2-2553-COE-PSU 20 Web cookies o Many sites provide the user with a Web cookie n A numerical value that is stored and managed by the user’s browser on the user machine n The website users the cookie value as an index into a database where it retains information about the user n Once the user returns to a website for which he/she has a cookies, the cookie is automatically passed by the user’s browser to the website n Thus, the website can act as a single sign-on that is the user is authenticated based on the possession of the user’s web cookie
- 11. 11 241-427-SV-2-2553-COE-PSU 21 Security issues of cookies o Significant amount of information about the user n User’s IP address, the brand & version of the user’s browser, the brand & version of the user’s OS, the web site the user last accessed n Can be used to create a personal profile, interests, habits n Can be done w/o violating the security rules n Privacy issues o Cookies keep username & password n Compromise of the access controls o What can we do? n Limit the lifetime of each cookie n Notify when a cookie is required 241-427-SV-2-2553-COE-PSU 22 Privacy setting
- 12. 12 241-427-SV-2-2553-COE-PSU 23 SHTTP o Secure Hyper Text Transfer Protocol n A set of security mechanisms defined for protecting the Internet traffic o Data entry forms & Internet-based transactions n Works at the application layers n Supports both authentication and encryption of HTTP traffic between client and server o HTTPS is an HTTP request sent by using SSL o Not very successful 241-427-SV-2-2553-COE-PSU 24 Secure electronic commerce o Electronic commerce n Business between two parties electronically n Both partitas not see face-to-face o Security issues n Destruction of data: o protecting data against accidental or malicious loss n Modification of data n Unauthorized disclosure of information n Non-repudiation n Interference of operation o Data must not be sent to unintended recipients n Misrepresentation n Inappropriate use of date
- 13. 13 241-427-SV-2-2553-COE-PSU 25 Interesting applications o Banking (relies heavily on encryption) o Stock brokerages o Gambling n Authentication & encryption o Shopping mall n Shipping cart n A single transaction on various items from several locations 241-427-SV-2-2553-COE-PSU 26 Secure Electronic Transaction o SET: an open encryption and security specification designed to protect credit card transactions on the Internet o Not a payment system o A set of security protocols and formats that enable users to employ the existing credit card payment infrastructure on an open network in a secure fashion o Provides 3 services n A secure communications channel among all parties involved in a transaction n Trust by the use of X509 digital certificates n Privacy: information is only available to parties in a transaction when and where necessary
- 14. 14 241-427-SV-2-2553-COE-PSU 27 SET Requirements o Provide confidentiality of payment and ordering information (via encryption) o Ensure the integrity of all transmitted data (via digital signatures) o Provide authentication that a cardholder is a legitimate user of a credit card account (via digital signatures & certificates) n Card holder and account number o Provide authentication that a merchant can accept credit card transactions through its relationship with a financial institution (via digital signatures & certificates) o Ensure the use of the best security practices and system design techniques not interfere with the user of other security mechanisms e.g., IPSec or SSL/TLS o Independent of hardware platform, OS and Web software 241-427-SV-2-2553-COE-PSU 28 Key Features of SET o Confidentiality of information n DES encrypts credit card number o Integrity of data n RSA digital signature, n SHA-1 hash codes, HMAC using SHA-1 o Cardholder account authentication n X509v3 digital certificates with RSA signatures o Merchant authentication n X509v3 digital certificates with RSA signatures
- 15. 15 241-427-SV-2-2553-COE-PSU 29 SET participants 241-427-SV-2-2553-COE-PSU 30 SET participants o Cardholder: buyer o Merchant: seller o Issuer: financial institution n provides the cardholder with payment care o Acquirer: financial institution n Establishes an account with a merchant n Processes payment card authorizations & payments o Payment gateway n Operated by the acquirer or a trusted third party o Certification authority n Issue X.509v3 public -key certificates for cardholders, merchants and payment gateways
- 16. 16 241-427-SV-2-2553-COE-PSU 31 A simplified SET model 241-427-SV-2-2553-COE-PSU 32 SSL versus SET o Exchange of data in an encrypted form o Two parties exchange certificates o Not very strong authentication o Possible risk of merchant fraud, since customer gives financial data to merchant o Merchant is liable for customer fraud o High practical usage o E-commerce related payment mechanism o All parties must be certified by a trusted third party o Strong authentication mechanism o Unlikely risk of merchant fraud, since customer gives financial data to payment gateway o Payment gateway is liable for customer fraud o Low practical use
- 17. 17 241-427-SV-2-2553-COE-PSU 33 How is electronic money (e-money) possible? o Because of public-key cryptography & digital signatures o Banks and customers use their keys n to encrypt (for security) n sign (for identification) blocks of digital data that represent money orders o A bank "signs" money orders using its private key and customers and merchants verify the signed money orders using the bank's widely published public key o Customers sign deposits and withdraws using their private key and the bank uses the customer's public key to verify the signed withdraws and deposits 241-427-SV-2-2553-COE-PSU 34 Digital cash o One way of making payments on the Internet o Money represented by computer files o Type n Identified electronic money n Anonymous electronic money Bank Customer Merchant (a) Obtaining electronic money from a bank (b) Makin purchase using electronic money (c) The merchant getting paid from the bank
- 18. 18 241-427-SV-2-2553-COE-PSU 35 Identified electronic money o Similar to credit card n The electronic money is issued by the bank with a serial number n The bank knows who was the customer and how he uses it o Problems n Privacy issues 241-427-SV-2-2553-COE-PSU 36 Anonymous electronic money o Also called as blinded money o Similar to real hard cash (no trace, no trail) o Instead of the bank created the serial number, the customer is the one who creates the serial number 1. Customer generates a random number, then generate a blinded number 2. Customer sends the blinded number to the bank 3. The bank sends the e-money with the blinded number back 4. The customer use the original number 5. The bank and the merchant cannot trace the money o Problem: double spending
- 19. 19 241-427-SV-2-2553-COE-PSU 37 Online v.s. Offline e-money o Classified based on involvement of the bank o Online electronic money n The bank is actively participated in the transaction between the customer and the merchant n The bank can confirm in real time whether the e-money is valid (the money is not already spent) o Offline electronic money n The bank is not actively participated in the transaction n The customer purchases something from the merchant using his/her e-money n The merchant accepts the e-money without validating it online n The merchant process the e-money later at a fixed time everyday 241-427-SV-2-2553-COE-PSU 38 Double Spending Problem o For online electronic money n Double spending problem is not possible because the bank is a part of the transaction o For identified offline e-money n Double spending problem can happen n However the customer can be tracked from the serial numbers (generated by the bank) o For anonymous offline electronic money n Double spending problem can happen n Cannot be tracked n Not practical
- 20. 20 241-427-SV-2-2553-COE-PSU 39 Single sign-on o Many web sites require users to enter their authentication information (usually a password) o Problem : n Many users do not like to enter passwords repeatedly n Users have trouble to remember many passwords o Solution: n Users only authenticate once and their “credentials” stay with them wherever they go on the internet n Subsequent authentication would be transparent to the user n No further authentication is needed for authorized applications n Microsoft passport or Security Assertion Markup Language (SAML) 241-427-SV-2-2553-COE-PSU 40 Trusting the Web o Web-based business transaction guidelines n Ethical business practices o Reputation of the company o Standard business practices n Transaction integrity o Information should be safe from interception, modification, deletion by unauthorized individual or errors n Protection of privacy o Information must be kept confidential o Safe from unauthorized or accidental disclosure
