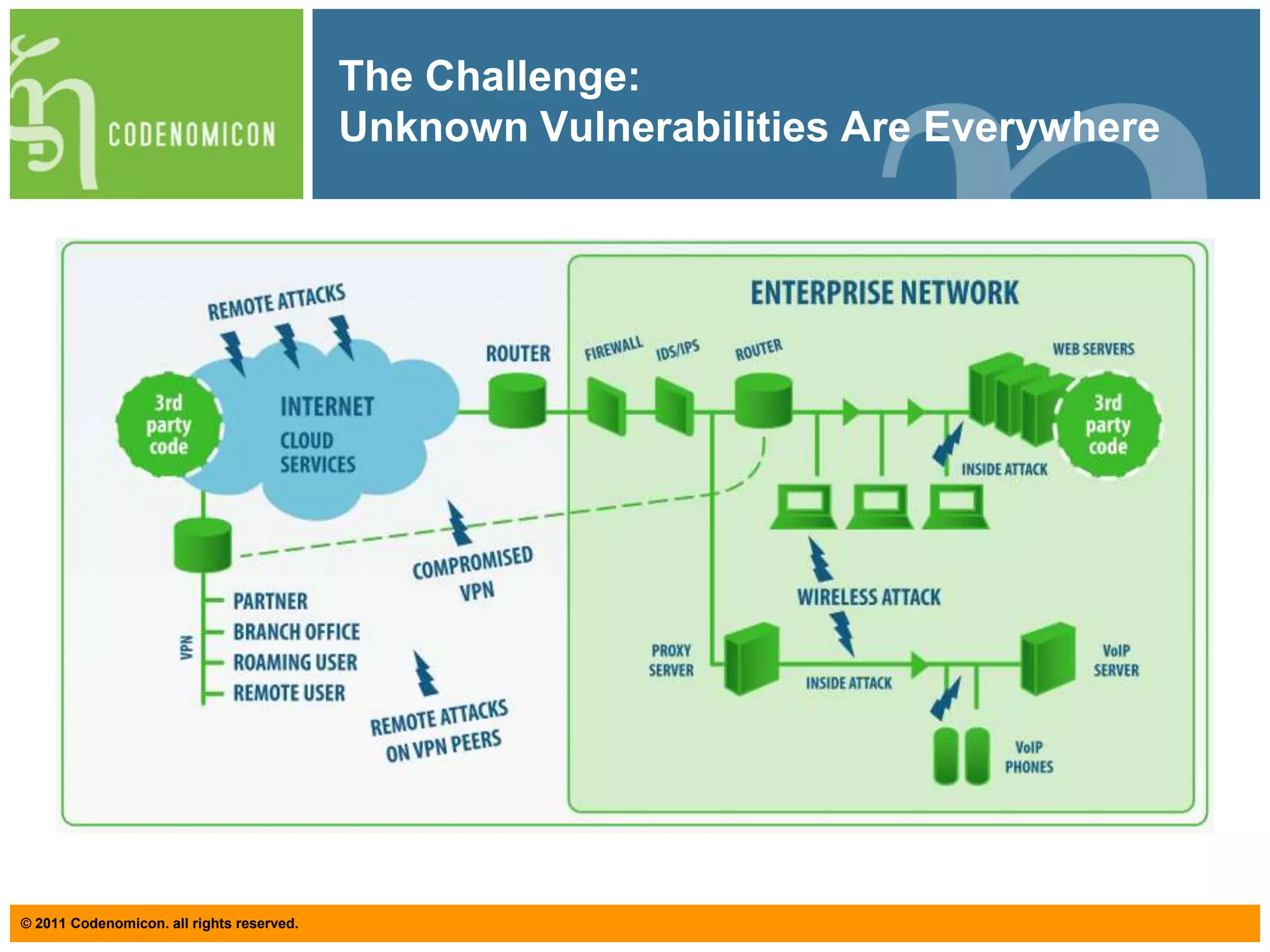
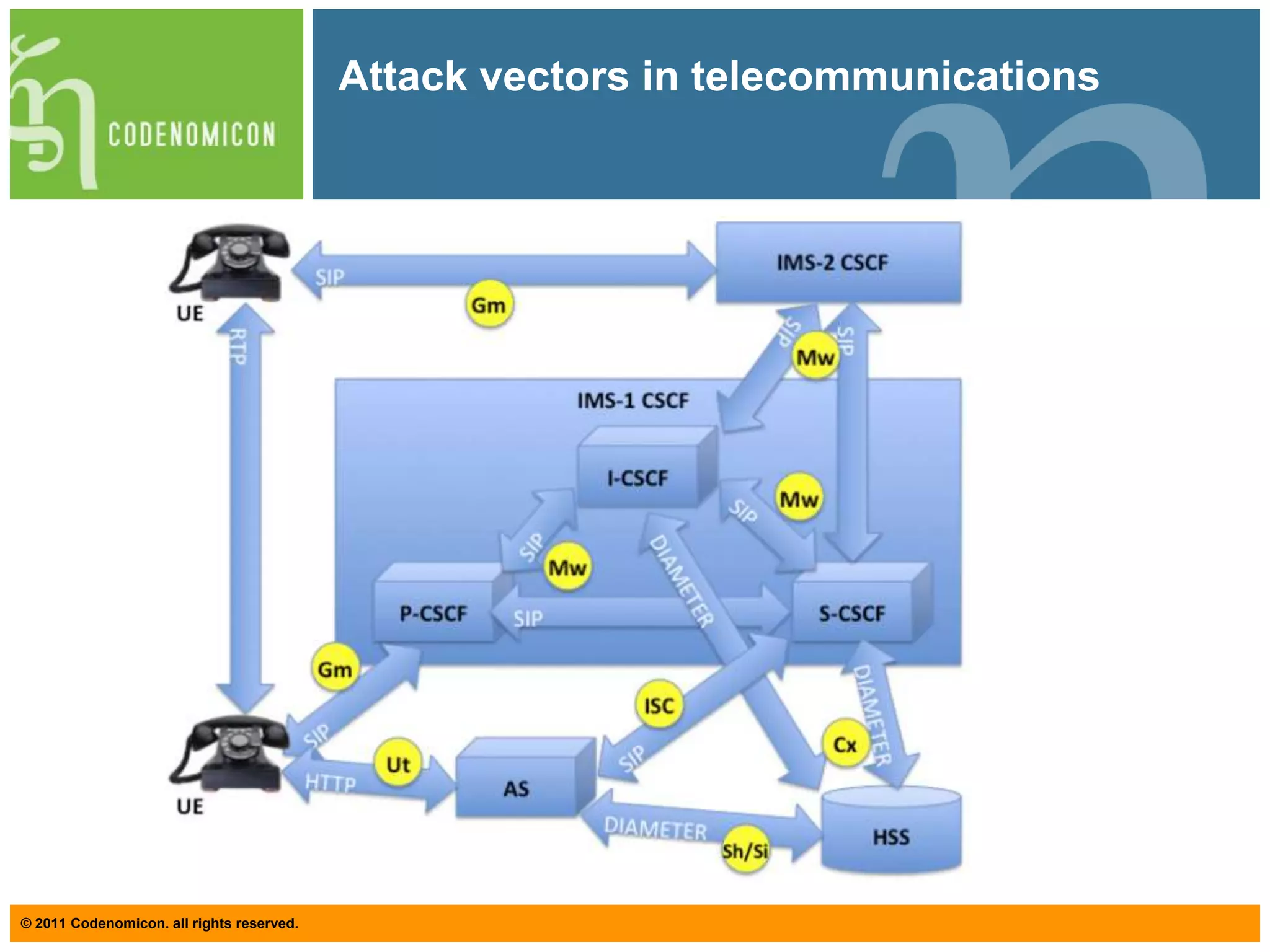
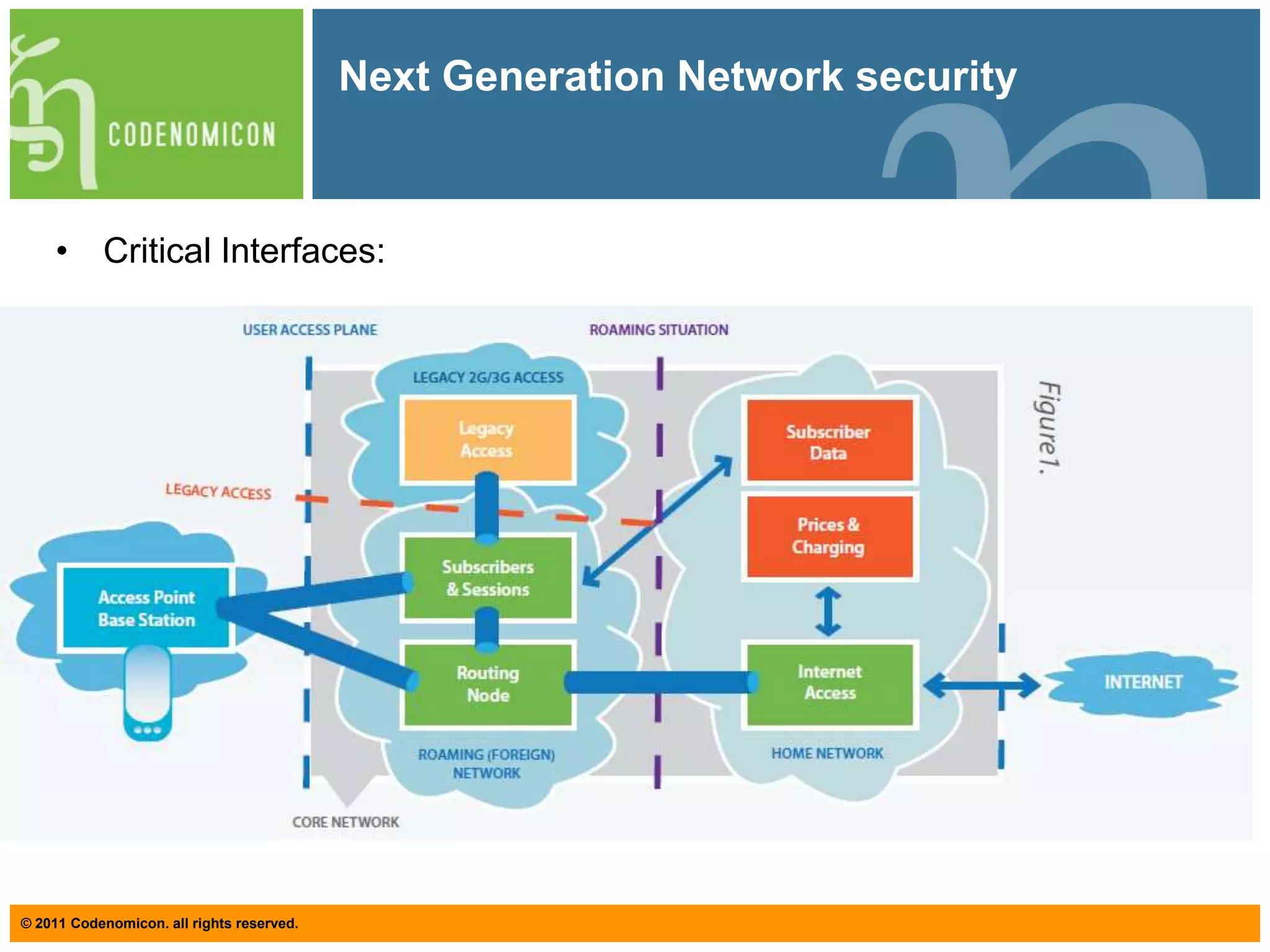
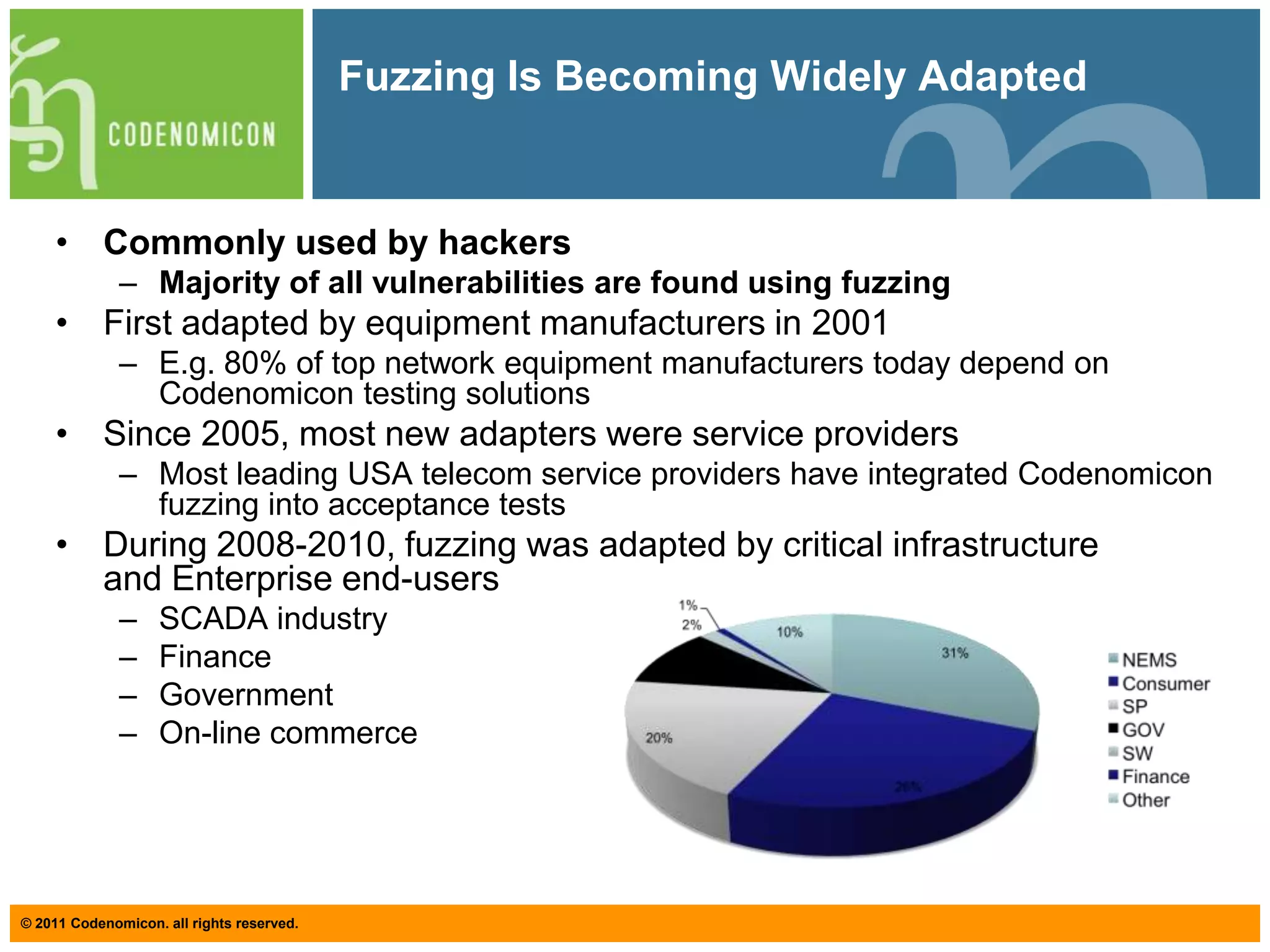
This document summarizes a webinar about fuzzing and unknown vulnerability management for telecommunications. The webinar was presented by Juha-Matti Tirilä and Tero Rontti from Codenomicon and covered topics like the growing complexity and attack vectors in telecommunications, definitions of fuzzing and different fuzzing techniques, challenges with vulnerability management, and a case study on fuzzing MPEG2-TS files. The goal of unknown vulnerability management is to have a framework for applying proper security testing procedures to identify vulnerabilities before they are discovered and exploited.