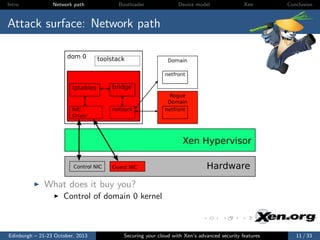
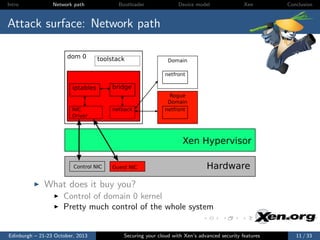
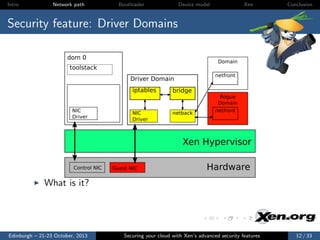
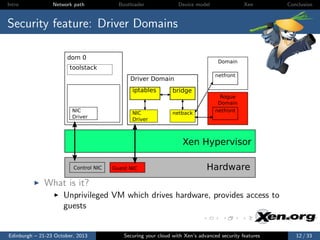
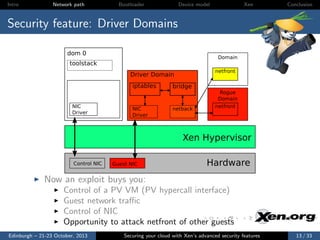
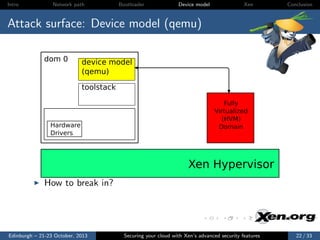
The document discusses securing cloud environments using Xen, an open-source type 1 hypervisor, emphasizing its advanced security features and architecture. It covers key concepts, security analysis principles, potential attack surfaces, and specific features like driver domains that enhance security. Finally, it provides insights on how to implement these security features effectively within a Xen environment.

![Intro
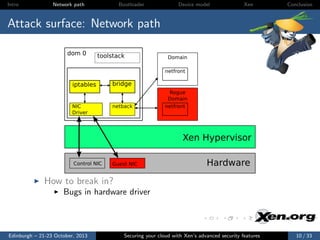
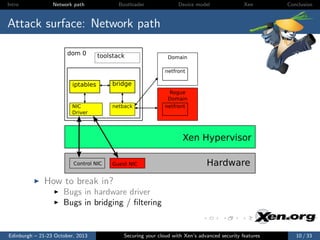
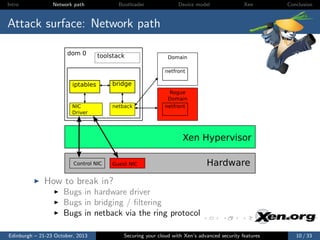
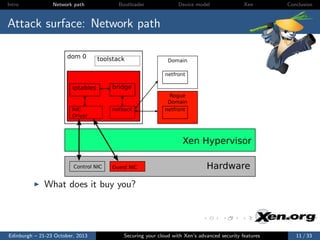
Network path
Bootloader
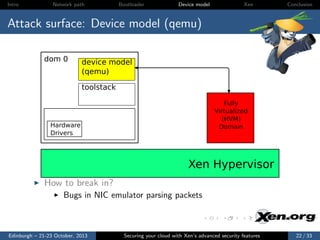
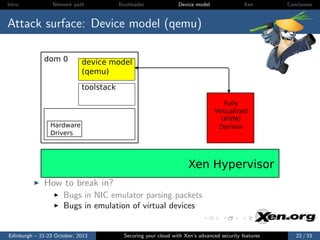
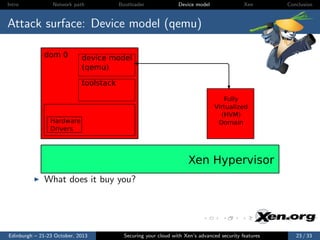
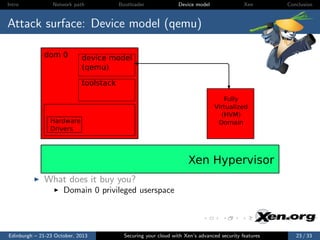
Device model
Xen
Conclusion
HowTo: Driver Domains
Create a VM with appropriate drivers
Any distro supporting dom0 should do
Install the xen-related hotplug scripts
Just installing the xen tools in the VM is usually good enough
Give the VM access to the physical NIC with PCI pass-through
Configure the network topology in the driver domain
Just like you would for dom0
Configure the guest vif to use the new domain ID
Add backend=domnet to vif declaration
vif = [ ’type=pv, bridge=xenbr0, backend=domnet’ ]
Edinburgh – 21-23 October, 2013
Securing your cloud with Xen’s advanced security features
14 / 33](https://image.slidesharecdn.com/lceu13-securingyourcloudwithxensadvancedsecurityfeatures-131107101111-phpapp01/85/LCEU13-Securing-your-cloud-with-Xen-s-advanced-security-features-George-Dunlap-Citrix-55-320.jpg)
![Intro
Network path
Bootloader
Device model
Xen
Conclusion
HowTo: Driver Domains
Create a VM with appropriate drivers
Any distro supporting dom0 should do
Install the xen-related hotplug scripts
Just installing the xen tools in the VM is usually good enough
Give the VM access to the physical NIC with PCI pass-through
Configure the network topology in the driver domain
Just like you would for dom0
Configure the guest vif to use the new domain ID
Add backend=domnet to vif declaration
vif = [ ’type=pv, bridge=xenbr0, backend=domnet’ ]
http://wiki.xen.org/wiki/Driver Domain
Edinburgh – 21-23 October, 2013
Securing your cloud with Xen’s advanced security features
14 / 33](https://image.slidesharecdn.com/lceu13-securingyourcloudwithxensadvancedsecurityfeatures-131107101111-phpapp01/85/LCEU13-Securing-your-cloud-with-Xen-s-advanced-security-features-George-Dunlap-Citrix-56-320.jpg)


![Intro
Network path
Bootloader
Device model
Xen
Conclusion
HowTo: Use the example FLASK policy
Build Xen with XSM enabled
Build the example policy
Add the appropriate label to guest config files
seclabel=[foo]
Edinburgh – 21-23 October, 2013
Securing your cloud with Xen’s advanced security features
30 / 33](https://image.slidesharecdn.com/lceu13-securingyourcloudwithxensadvancedsecurityfeatures-131107101111-phpapp01/85/LCEU13-Securing-your-cloud-with-Xen-s-advanced-security-features-George-Dunlap-Citrix-134-320.jpg)
![Intro
Network path
Bootloader
Device model
Xen
Conclusion
HowTo: Use the example FLASK policy
Build Xen with XSM enabled
Build the example policy
Add the appropriate label to guest config files
seclabel=[foo]
stubdom label=[foo]
Edinburgh – 21-23 October, 2013
Securing your cloud with Xen’s advanced security features
30 / 33](https://image.slidesharecdn.com/lceu13-securingyourcloudwithxensadvancedsecurityfeatures-131107101111-phpapp01/85/LCEU13-Securing-your-cloud-with-Xen-s-advanced-security-features-George-Dunlap-Citrix-135-320.jpg)
![Intro
Network path
Bootloader
Device model
Xen
Conclusion
HowTo: Use the example FLASK policy
Build Xen with XSM enabled
Build the example policy
Add the appropriate label to guest config files
seclabel=[foo]
stubdom label=[foo]
http://wiki.xen.org/wiki/Xen Security Modules : XSMFLASK
Edinburgh – 21-23 October, 2013
Securing your cloud with Xen’s advanced security features
30 / 33](https://image.slidesharecdn.com/lceu13-securingyourcloudwithxensadvancedsecurityfeatures-131107101111-phpapp01/85/LCEU13-Securing-your-cloud-with-Xen-s-advanced-security-features-George-Dunlap-Citrix-136-320.jpg)
![Intro
Network path
Bootloader
Device model
Xen
Conclusion
HowTo: Use the example FLASK policy
Build Xen with XSM enabled
Build the example policy
Add the appropriate label to guest config files
seclabel=[foo]
stubdom label=[foo]
http://wiki.xen.org/wiki/Xen Security Modules : XSMFLASK
WARNING: In 4.3, the example policy not extensively tested.
Use with care!
Edinburgh – 21-23 October, 2013
Securing your cloud with Xen’s advanced security features
30 / 33](https://image.slidesharecdn.com/lceu13-securingyourcloudwithxensadvancedsecurityfeatures-131107101111-phpapp01/85/LCEU13-Securing-your-cloud-with-Xen-s-advanced-security-features-George-Dunlap-Citrix-137-320.jpg)