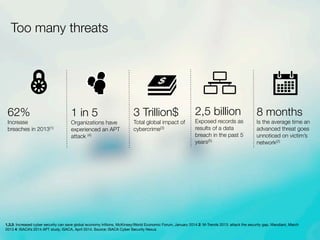
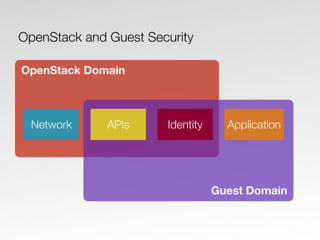
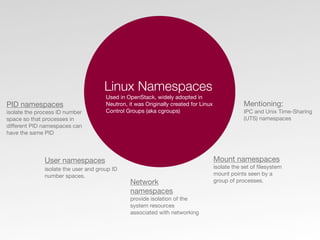
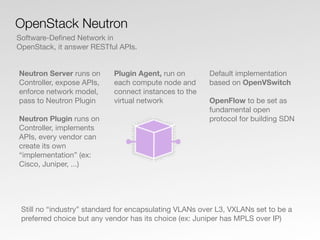
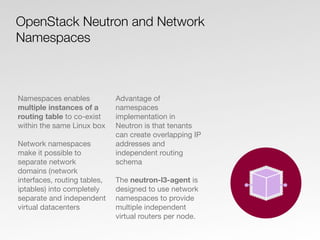
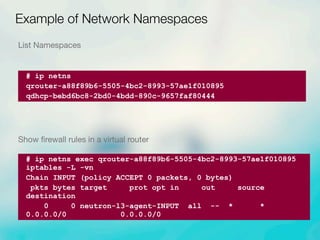
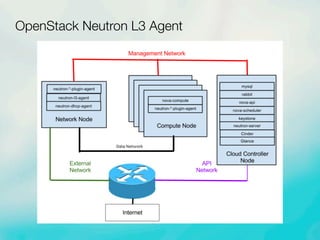
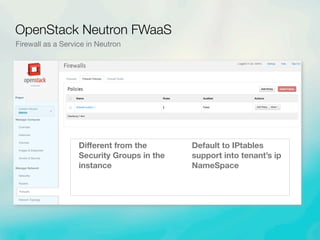
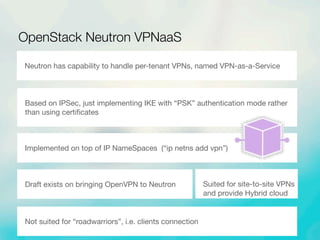
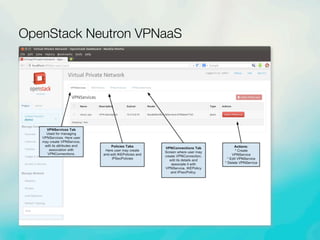
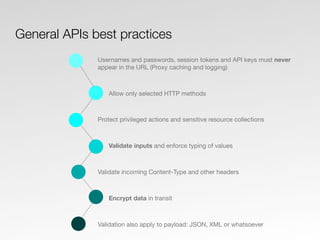
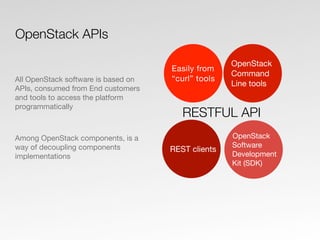
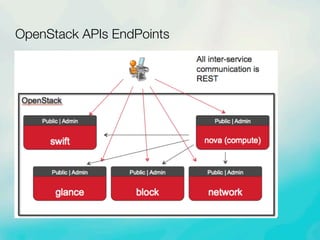
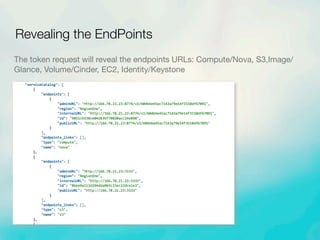
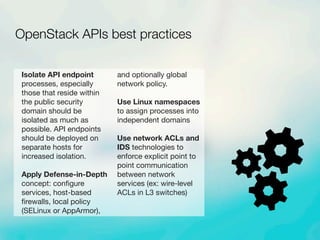
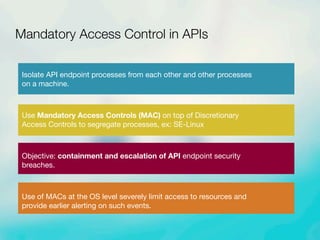
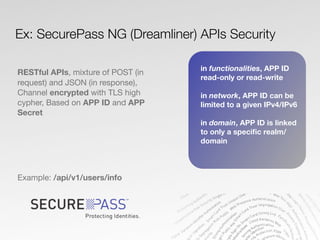
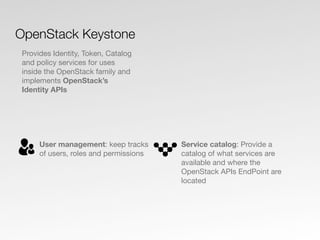
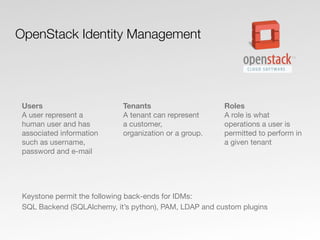
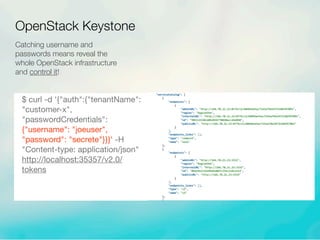
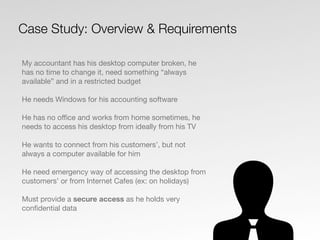
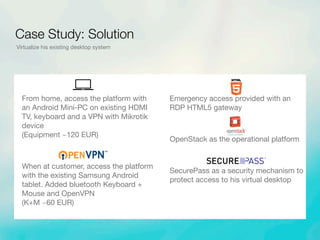
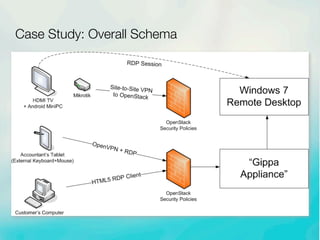
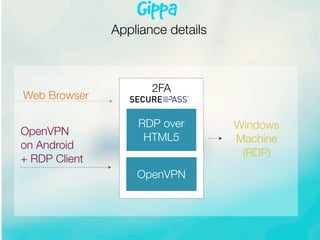
The document discusses strategies for enhancing security in OpenStack environments, focusing on user identity protection in a distributed cloud model. It highlights the need for robust API security practices, the implementation of network namespaces for isolate services, and the necessity of strong authentication methods to guard against identity theft and cybercrime. A case study illustrates a practical application of these security measures for a user needing secure access to their virtual desktop from various locations.