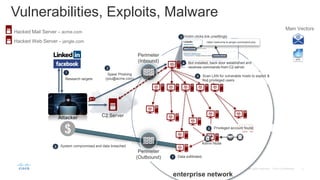
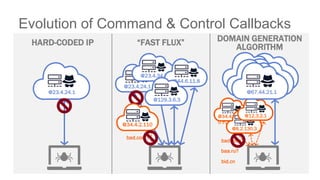
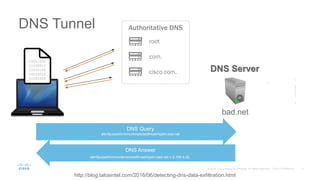
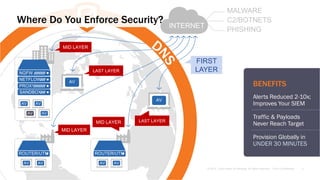
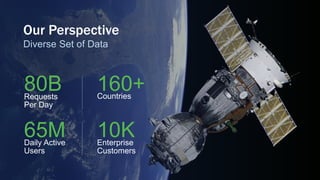
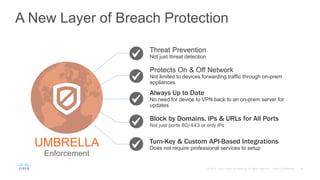
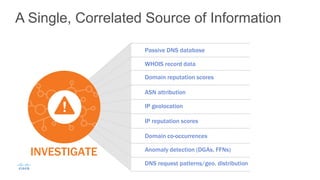
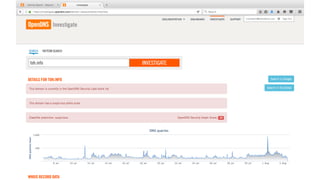
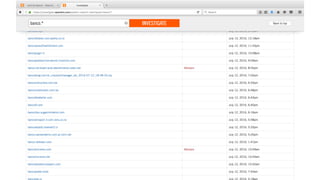
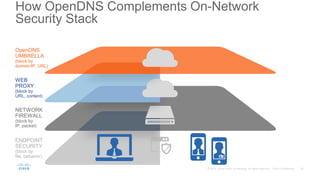
This document discusses how DNS can be used as an attack vector and the importance of DNS security. It provides examples of how attackers can use DNS for command and control of botnets, data exfiltration, and domain generation algorithms. The document also describes Cisco's Umbrella security solution, which uses DNS enforcement and threat intelligence to protect networks and devices from internet malware, C2 botnets, phishing, and other threats.