Embed presentation
Download to read offline







The document outlines a project for implementing Snort as an intrusion prevention system on pfSense to defend against HTTP brute force attacks. It details the phases of analysis, development, testing, and documentation, along with steps for setting up the environment, configuring Snort, and testing its effectiveness. A report is to be created summarizing the findings and processes undertaken in this project.
Presenter: Huda Seyam; Date: 7/6/2020. Introduction to the project focusing on Snort IDS/IPS.
Outline of the project idea centered on implementing security measures.
Discussion on HTTP brute force attacks, highlighting security vulnerabilities.
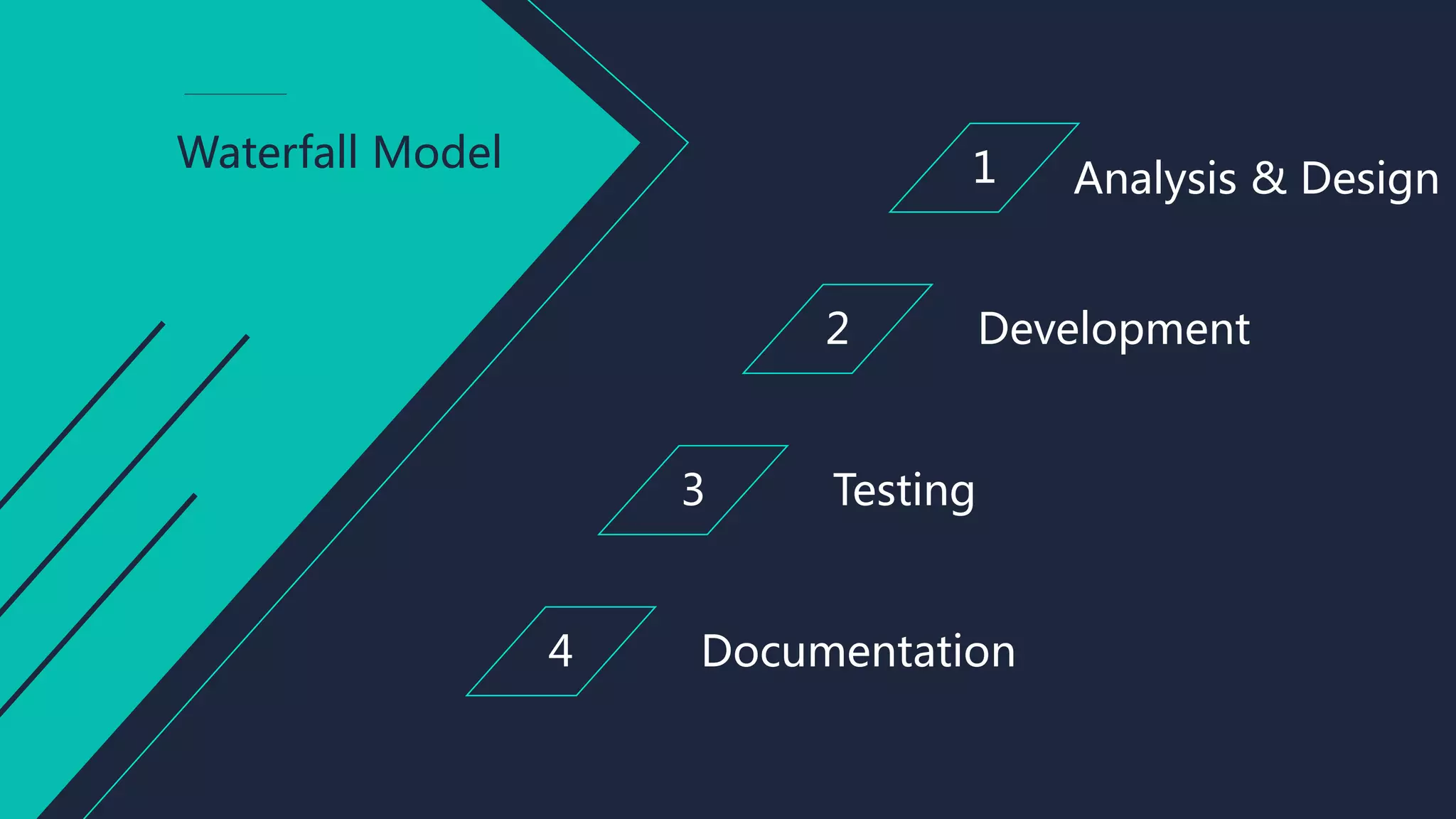
Outline of the Waterfall Model phases: Analysis & Design, Development, Testing, Documentation.
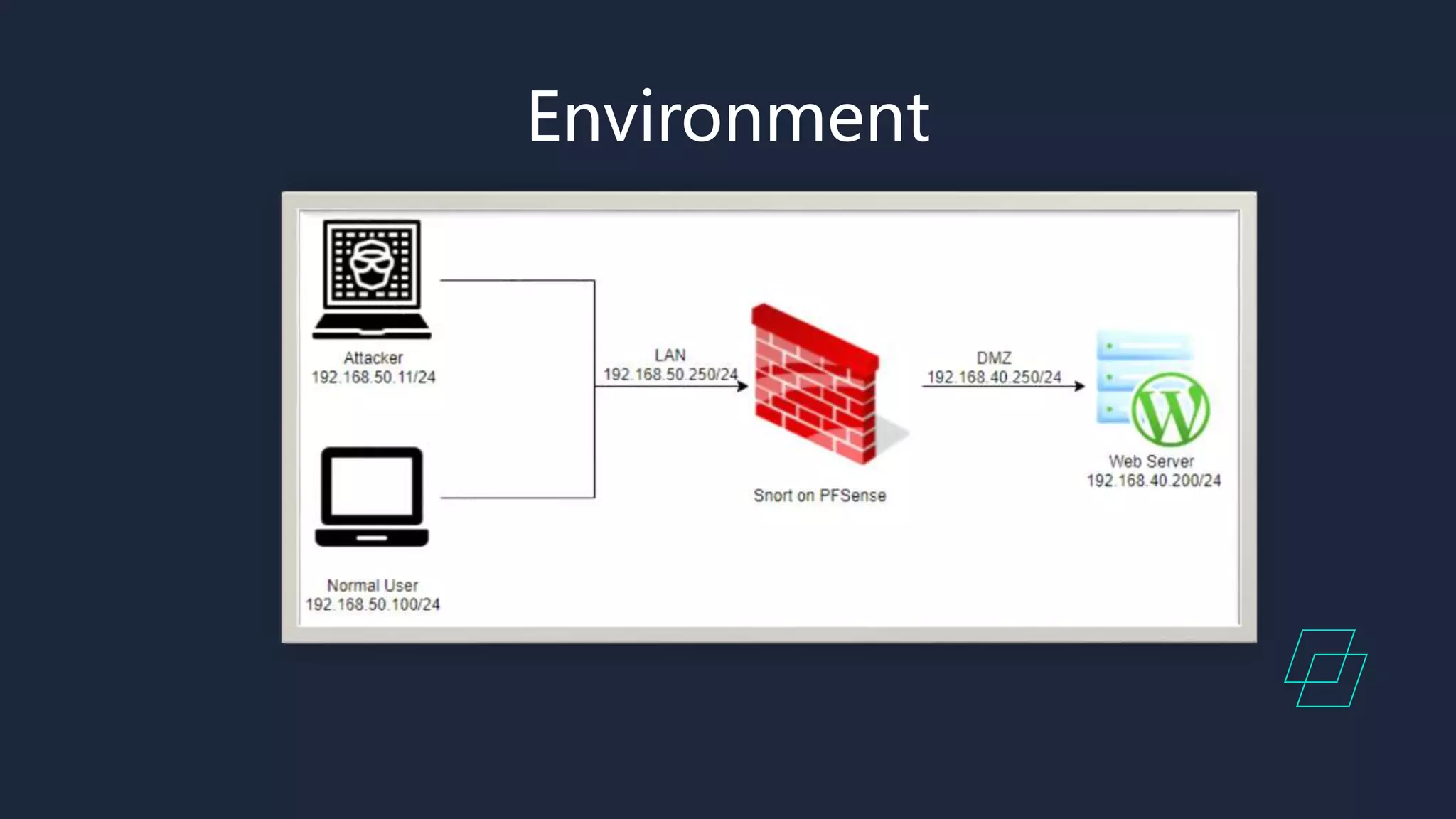
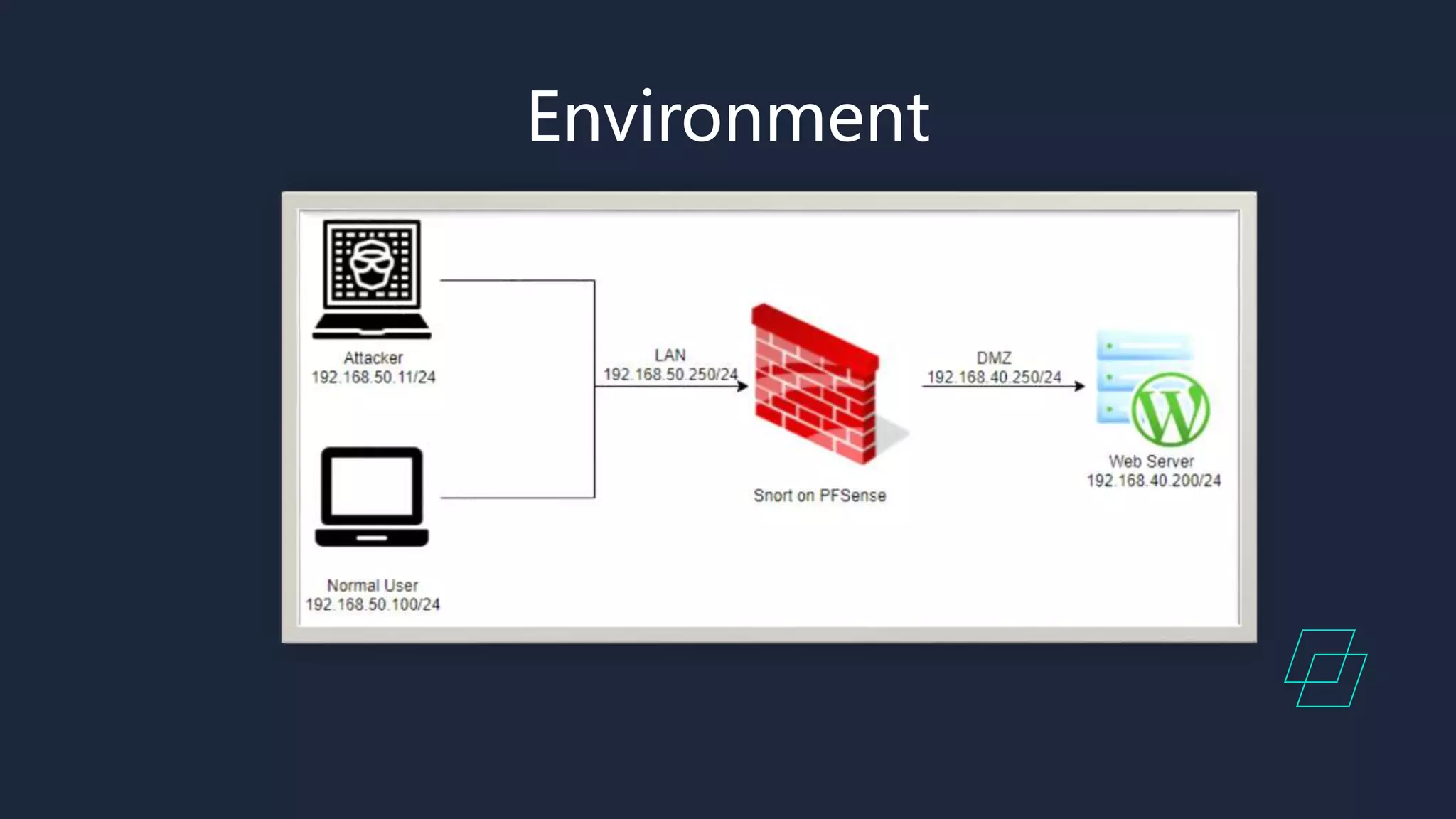
Steps for analysis and environmental setup including drafting and required installations.
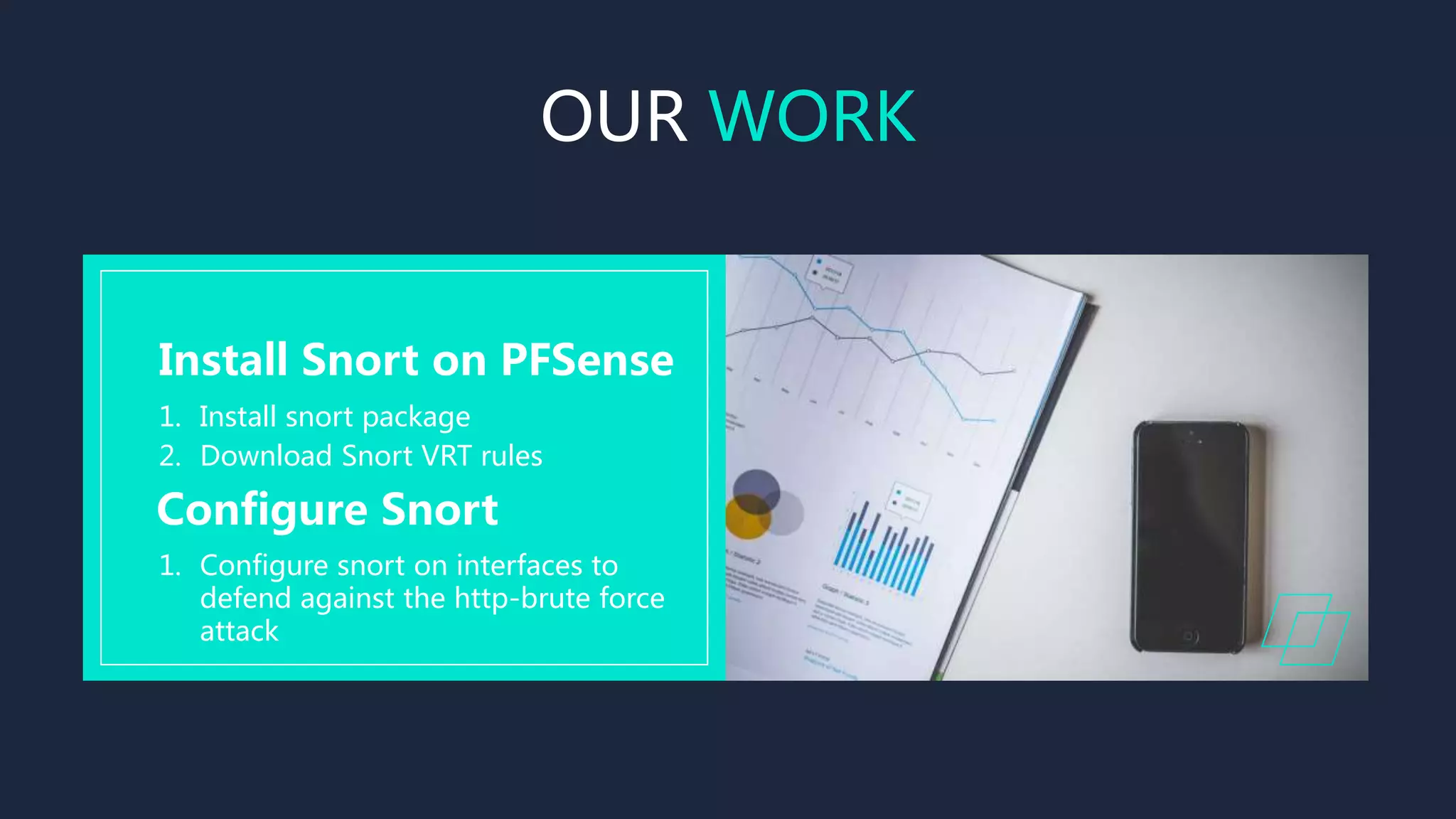
Setup and configuration of Snort on PFSense as an intrusion prevention system.
Testing procedures including performing a HTTP brute force attack and checking alerts.
Report writing documenting the processes undertaken and findings.
List of references including links for setting up intrusion detection with Snort and PFSense.
Thank you note concluding the presentation.