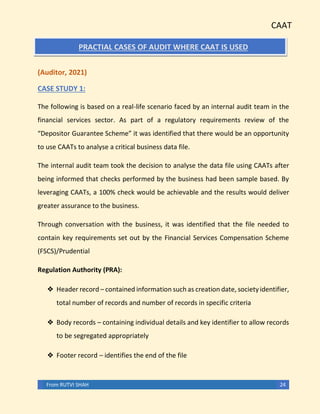
This document discusses Computer Assisted Audit Techniques (CAATs). It begins with an introduction that defines CAATs as using technology to increase the effectiveness and efficiency of auditing. It then provides three examples of how CAATs are used in auditing:
1. Creation of electronic work papers to easily navigate audits over time.
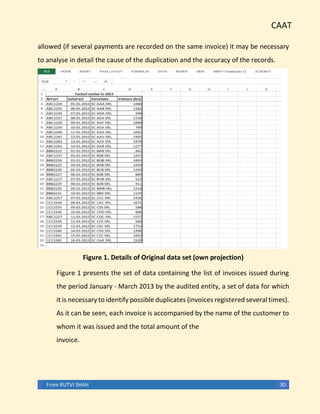
2. Fraud detection by identifying unexpected patterns in data.
3. Performing analytical tests to evaluate financial information.
The document emphasizes that as auditors encounter electronic data across clients, understanding how to use relevant information technology is critical for providing audit services. CAATs allow auditors to analyze large data volumes for anomalies and inconsistencies.