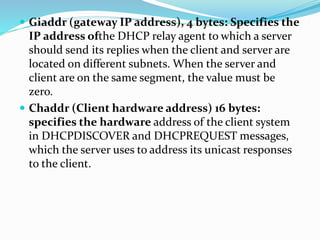
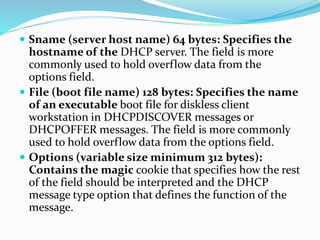
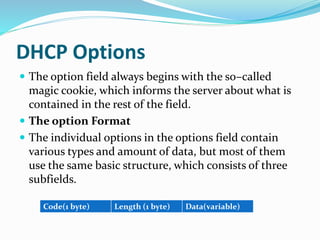
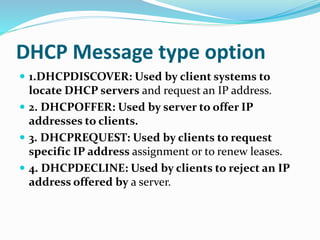
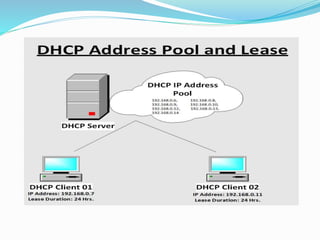
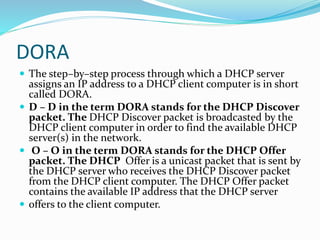
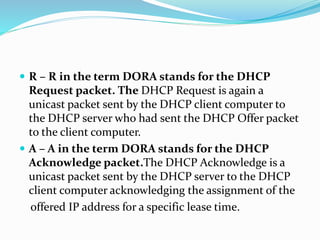
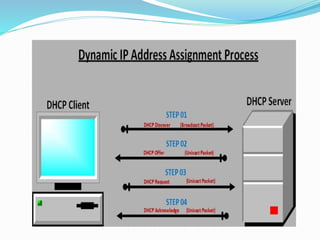
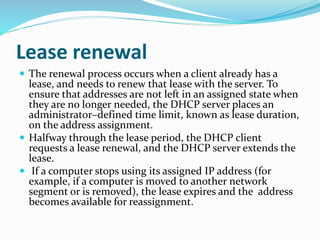
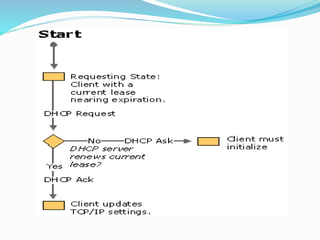
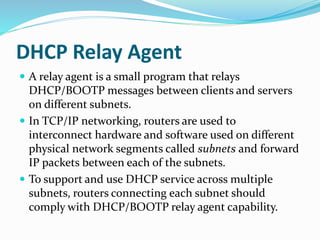
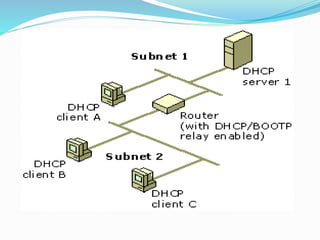
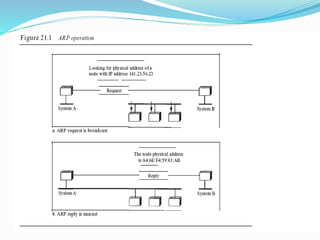
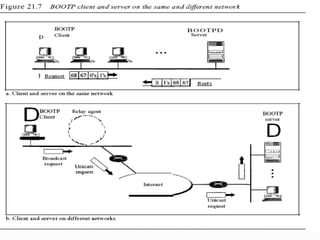
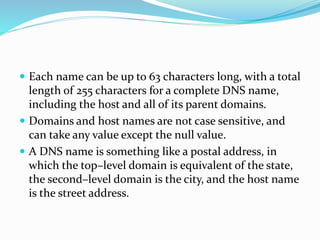
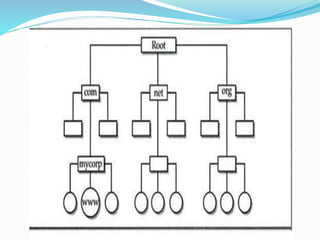
The document provides a comprehensive overview of the Dynamic Host Configuration Protocol (DHCP), detailing its architecture, operation, and its role in dynamically assigning IP addresses. It discusses the differences between static, automatic, and dynamic IP address allocation, explains the DORA process for IP address assignment, and outlines the objectives and functions of DHCP and its interaction with other protocols like ARP and DNS. Additionally, it covers DHCP relay agents and includes details on message formats, options, and lease renewal processes.