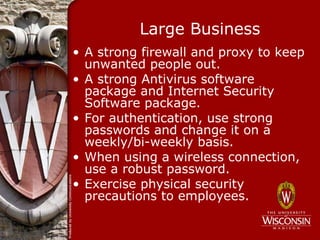
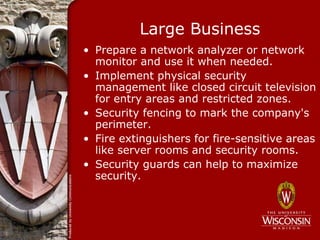
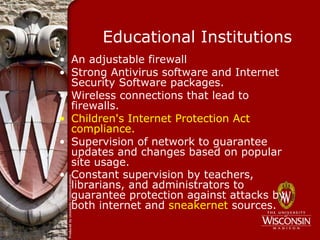
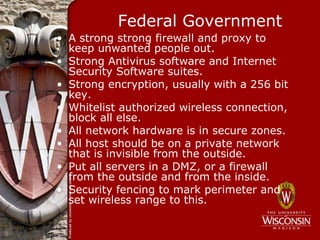
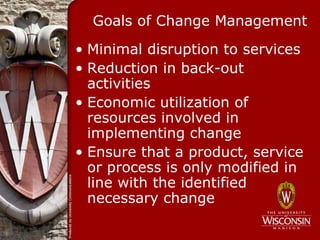
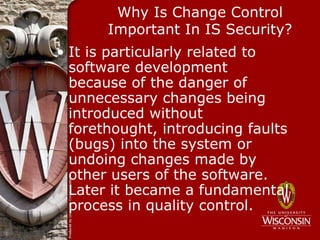
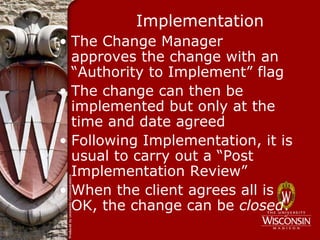
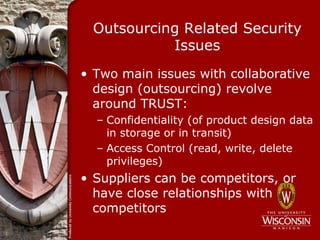
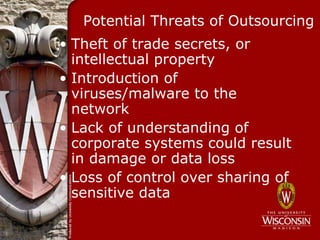
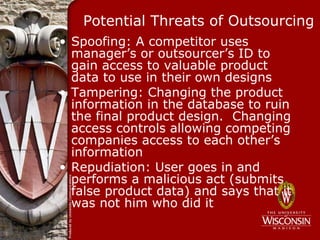
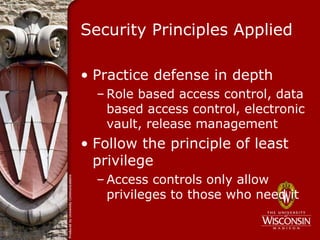
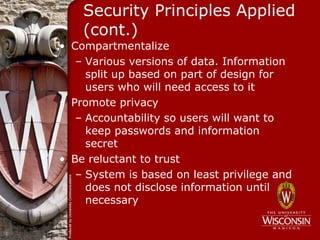
This document discusses several topics related to network security, including change control and outsourcing. It begins with an overview of network security and how it differs from computer security by protecting entry points and shared resources from attacks. Key aspects of network security are then defined, such as authentication, authorization, firewalls, intrusion prevention systems, antivirus software, honeypots, and security management approaches for small, medium, and large businesses as well as educational institutions and government. Change control processes and their importance for information security are also outlined. Finally, outsourcing related security issues and potential threats are identified along with some countermeasures for addressing them.