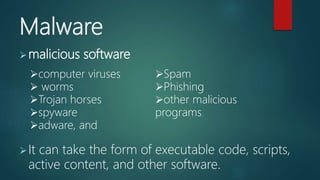
This document provides a lesson on internet safety and netiquette. It outlines 5 objectives for students, which are to consider safety and reputation when sharing information online, avoid internet dangers, be responsible on social media, and browse efficiently. It then defines internet threats like malware, viruses, worms, Trojans, adware, spyware, spam, phishing and provides tips to stay safe such as being mindful of what you share, reading terms and conditions, knowing social media security features, and avoiding suspicious emails or downloads.