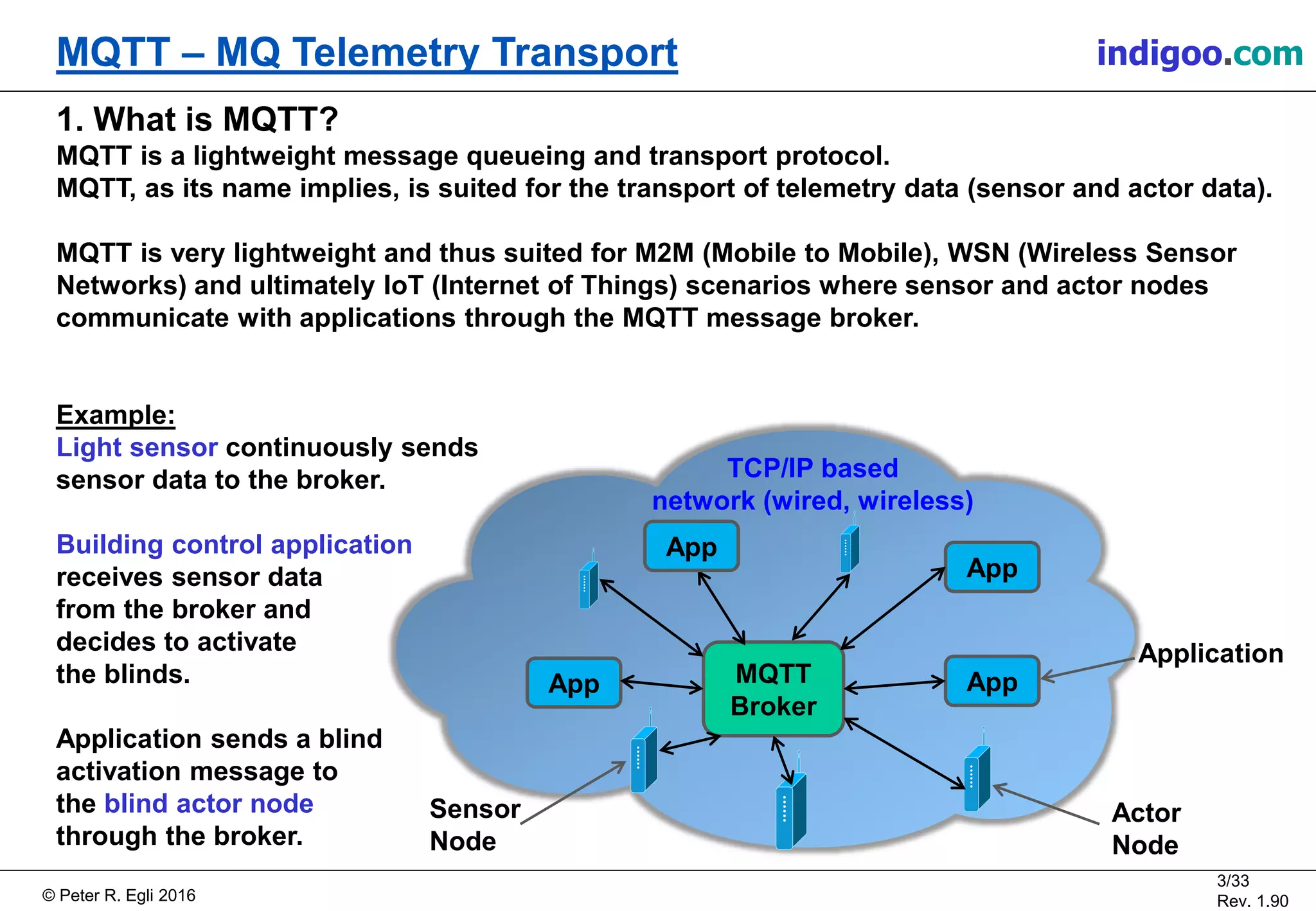
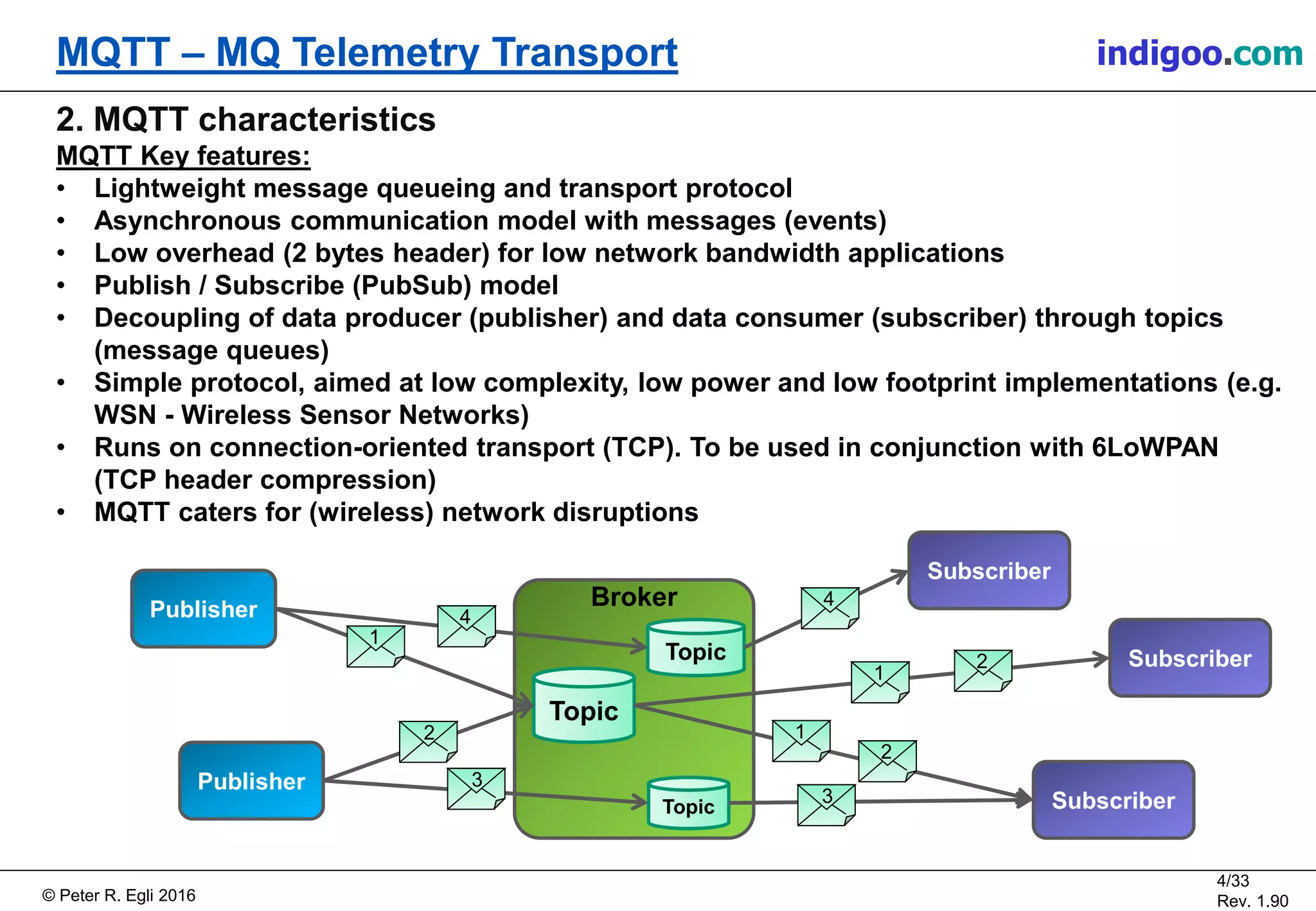
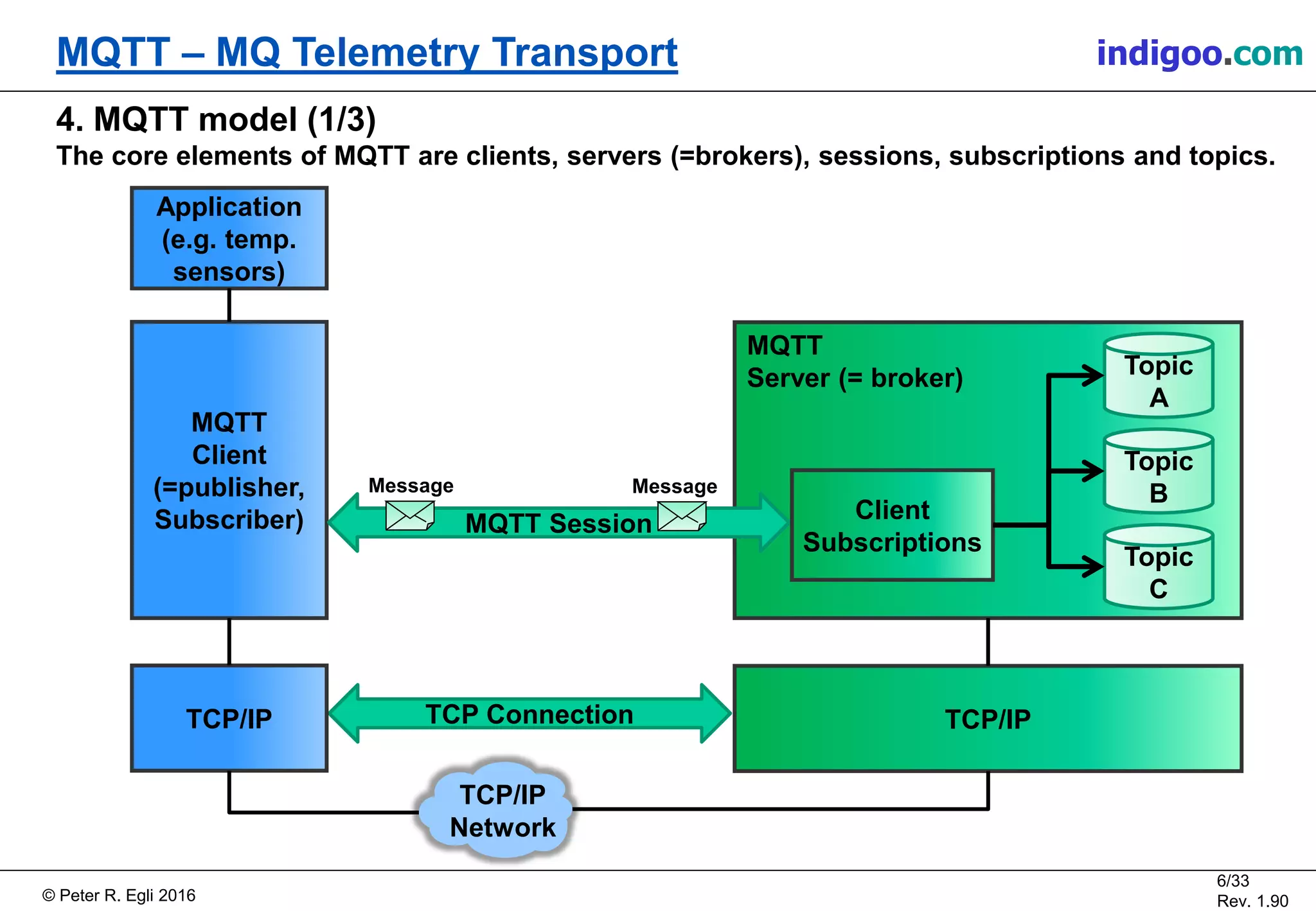
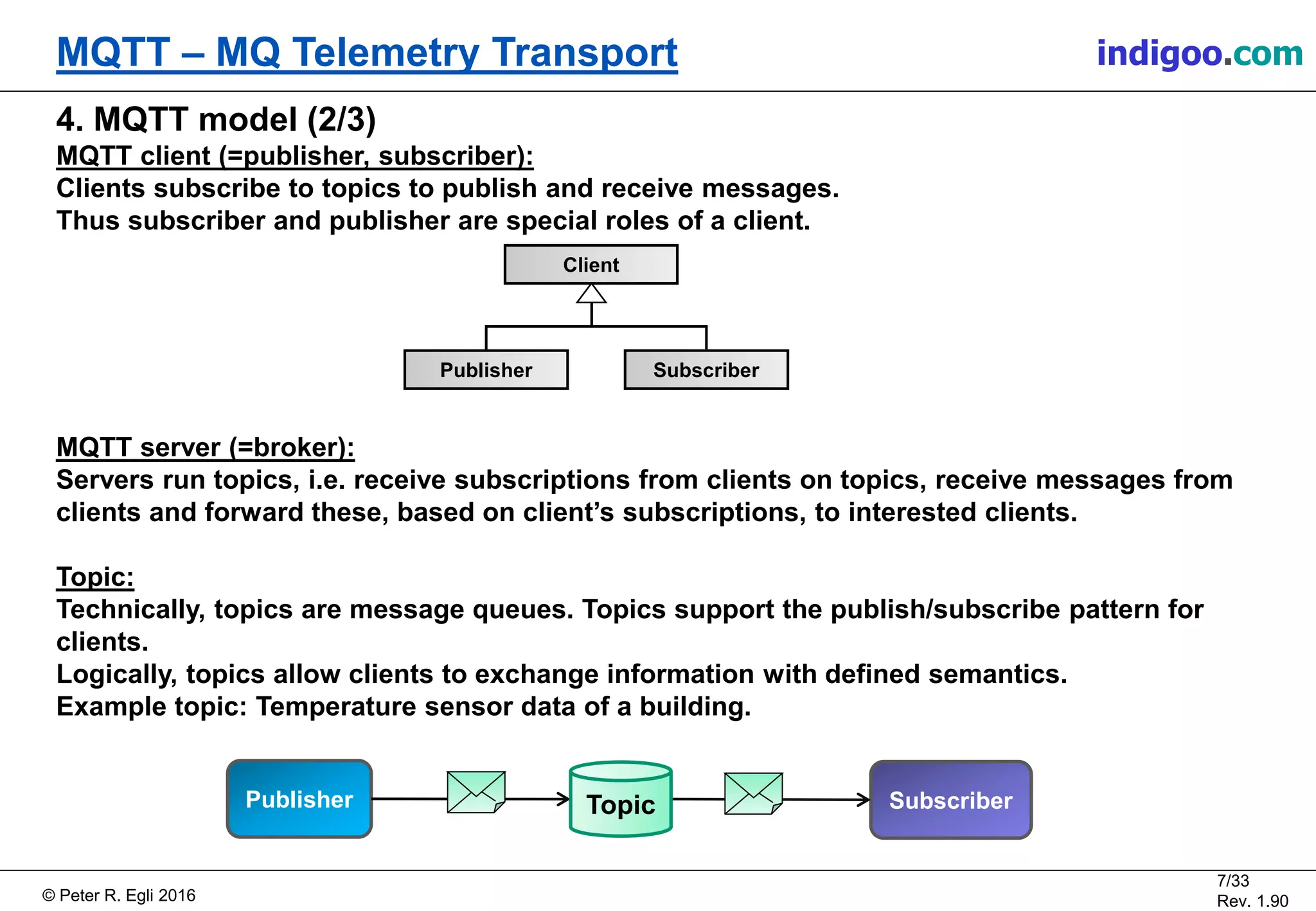
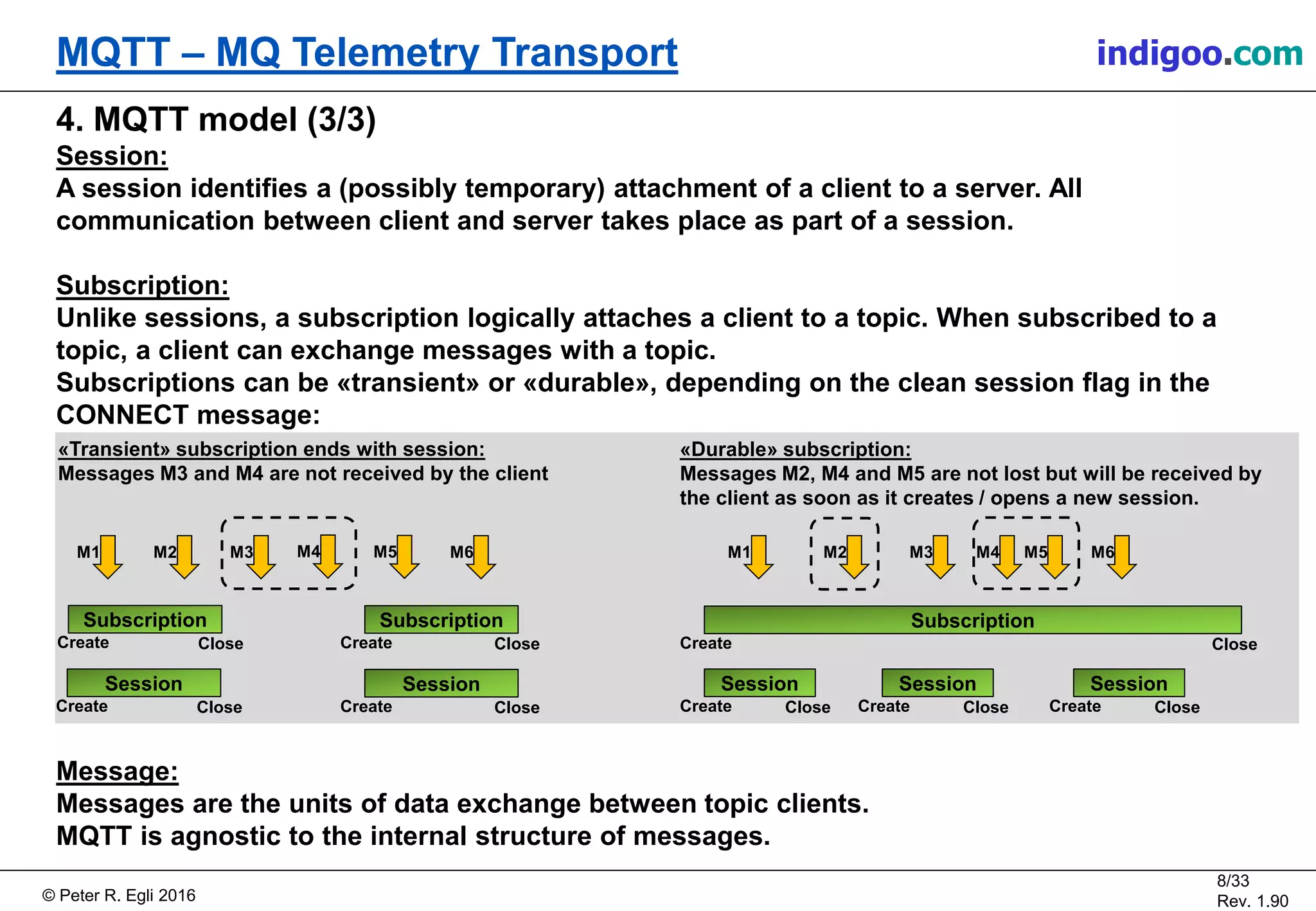
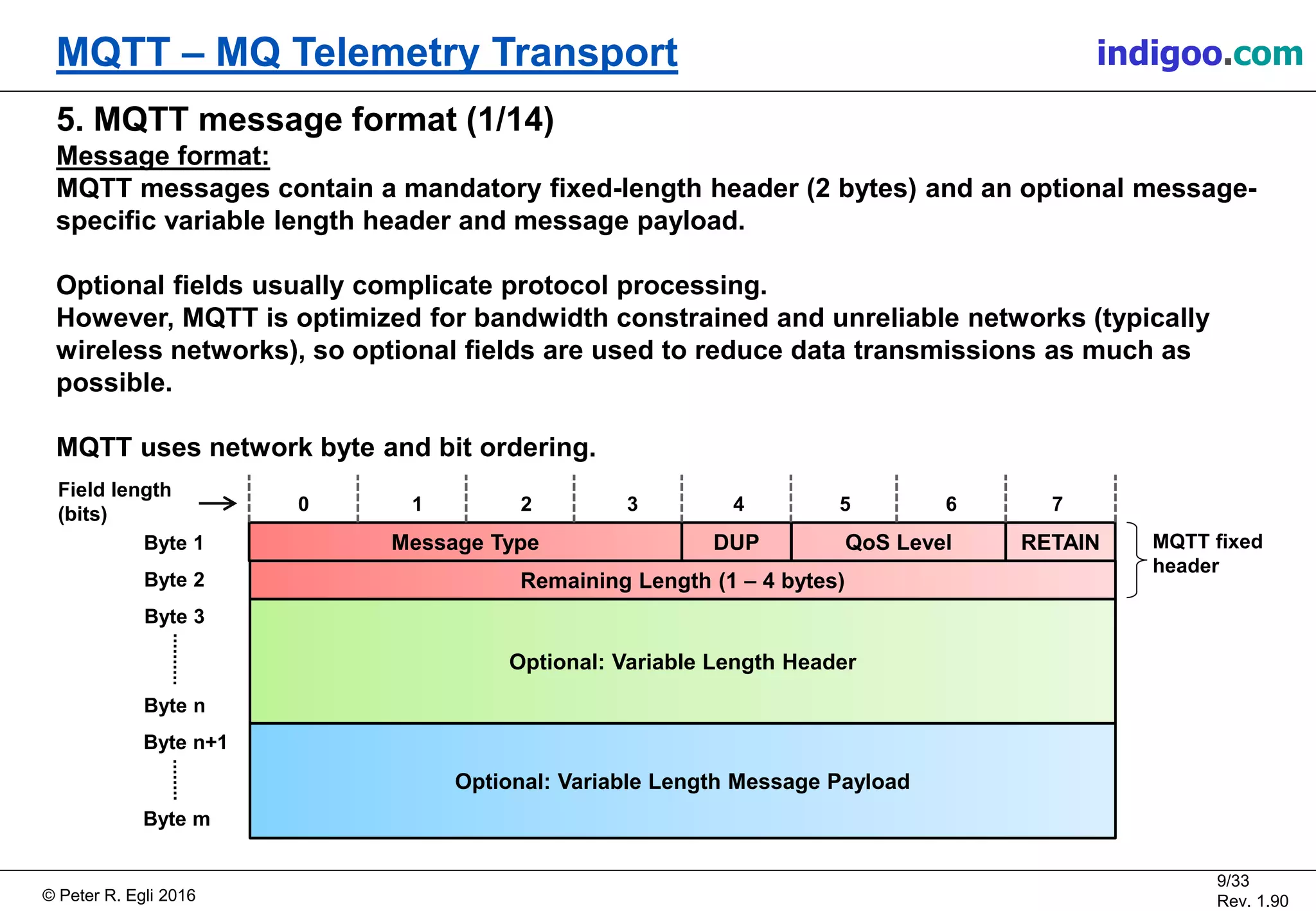
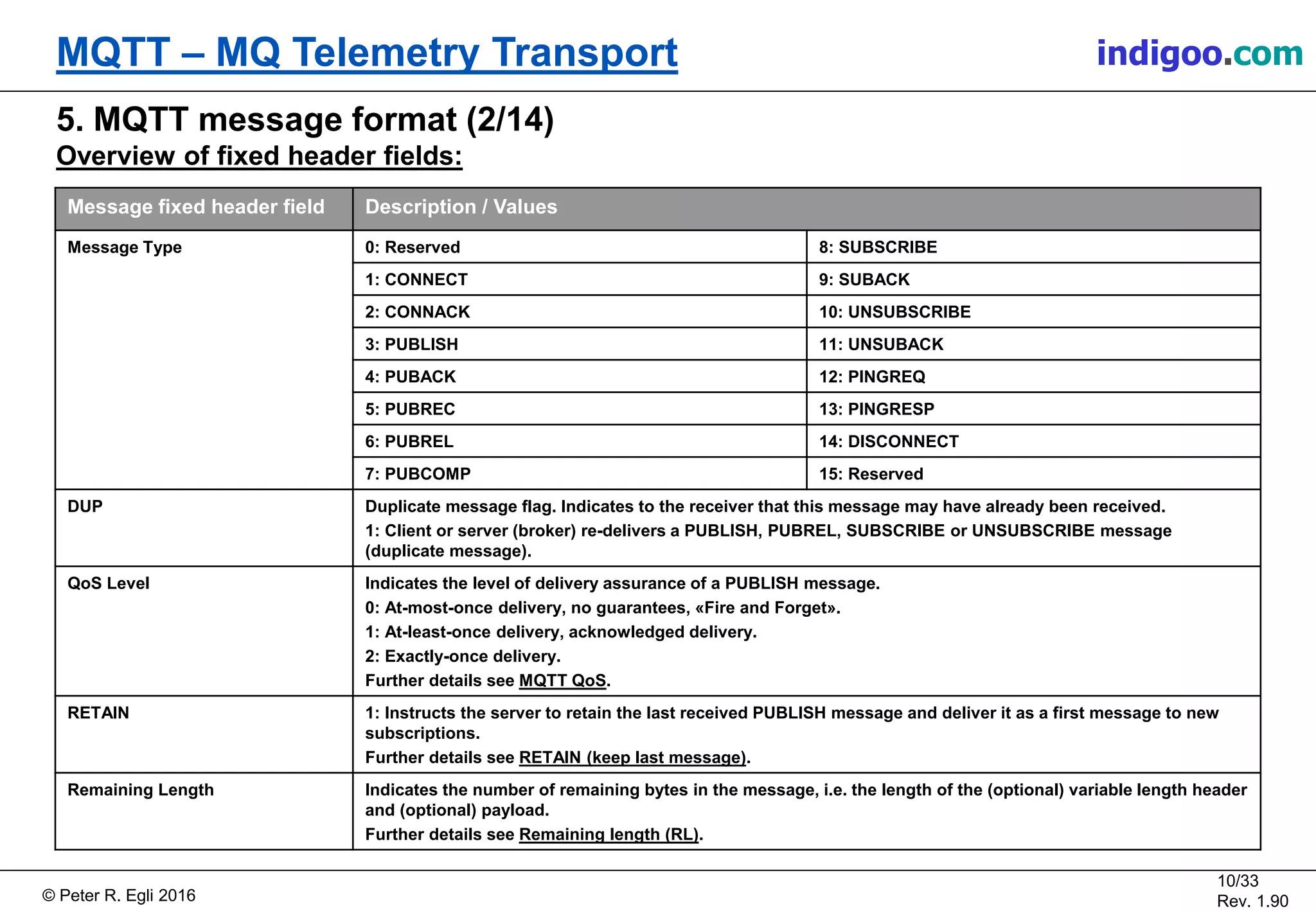
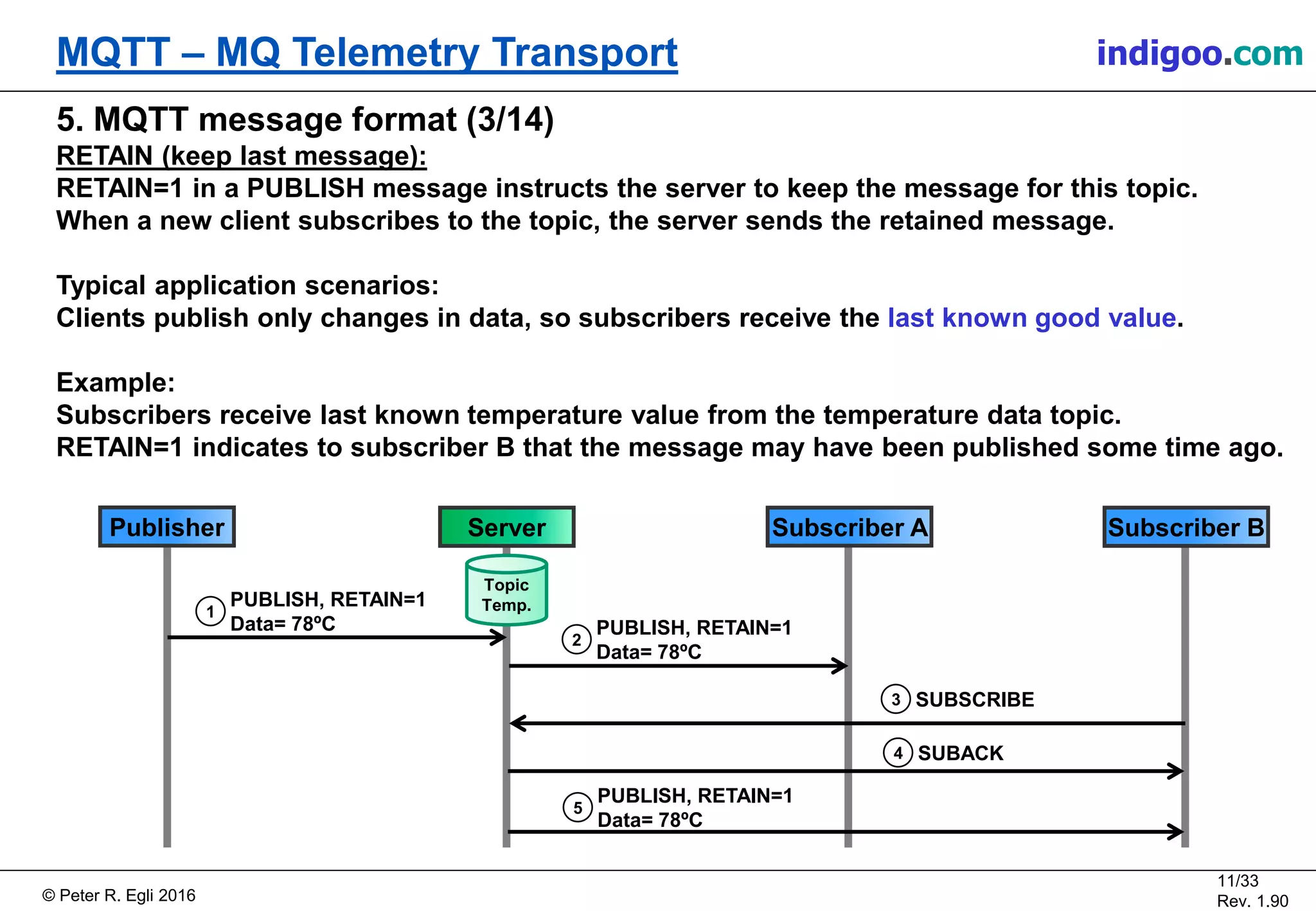
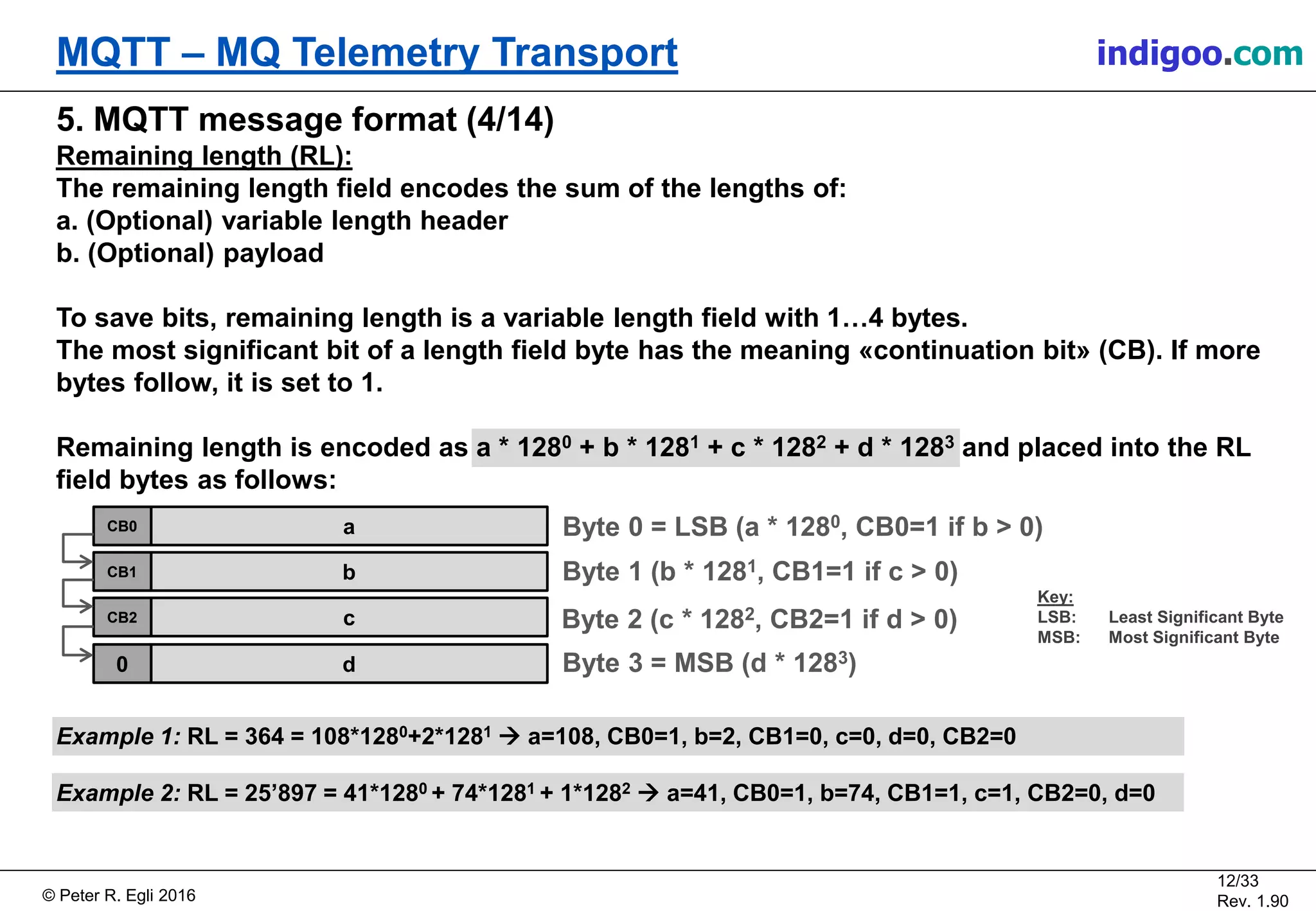
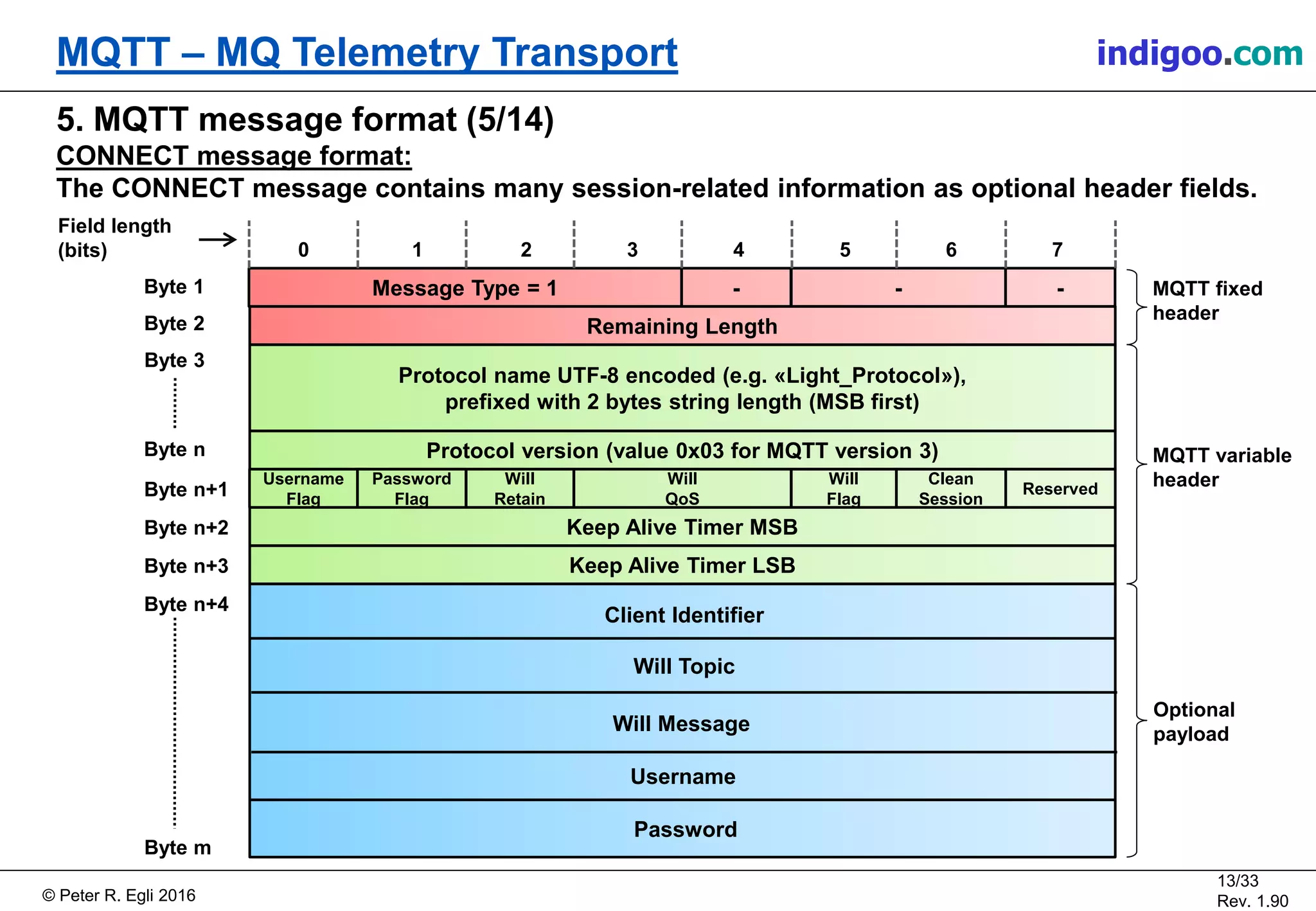
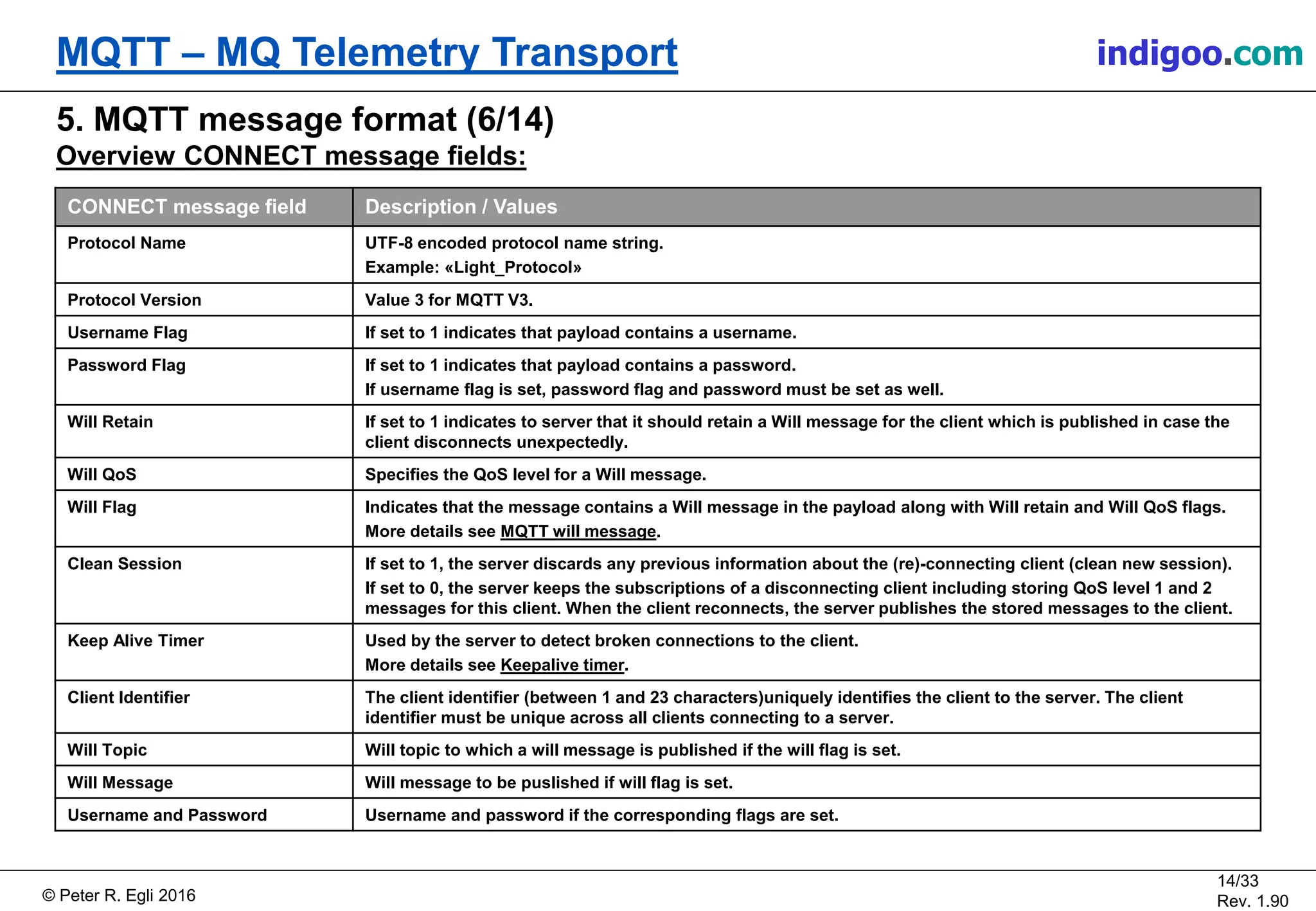
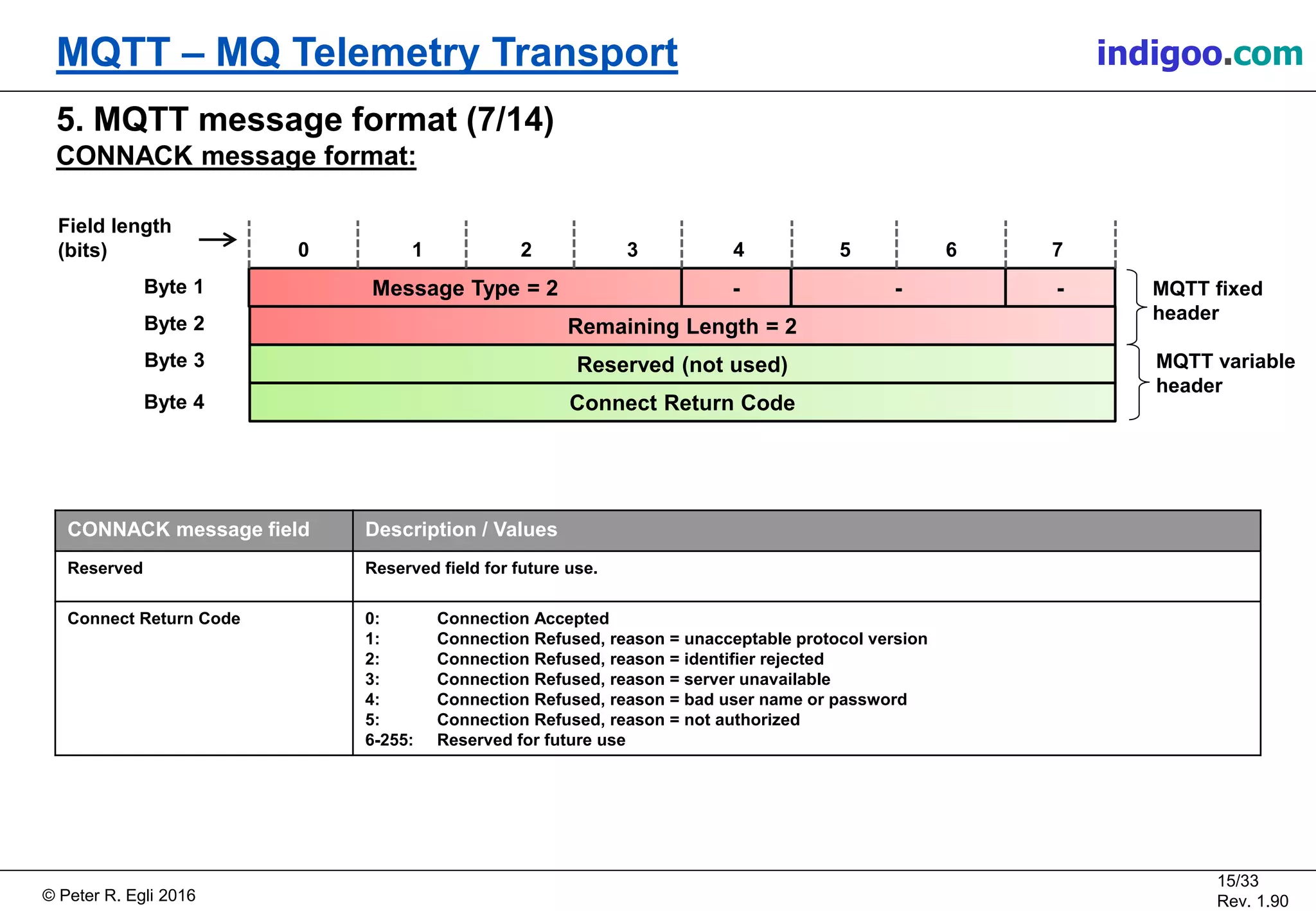
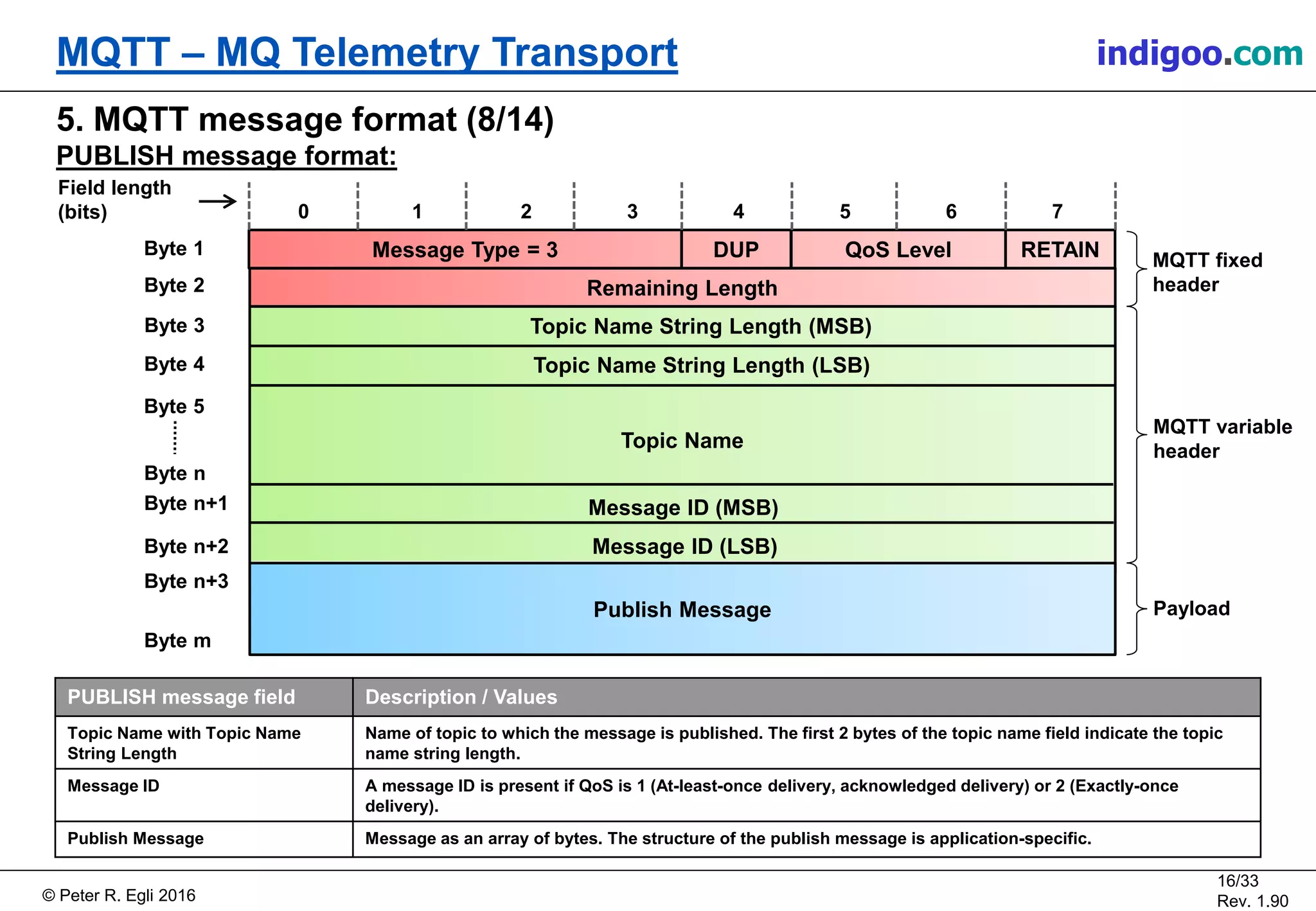
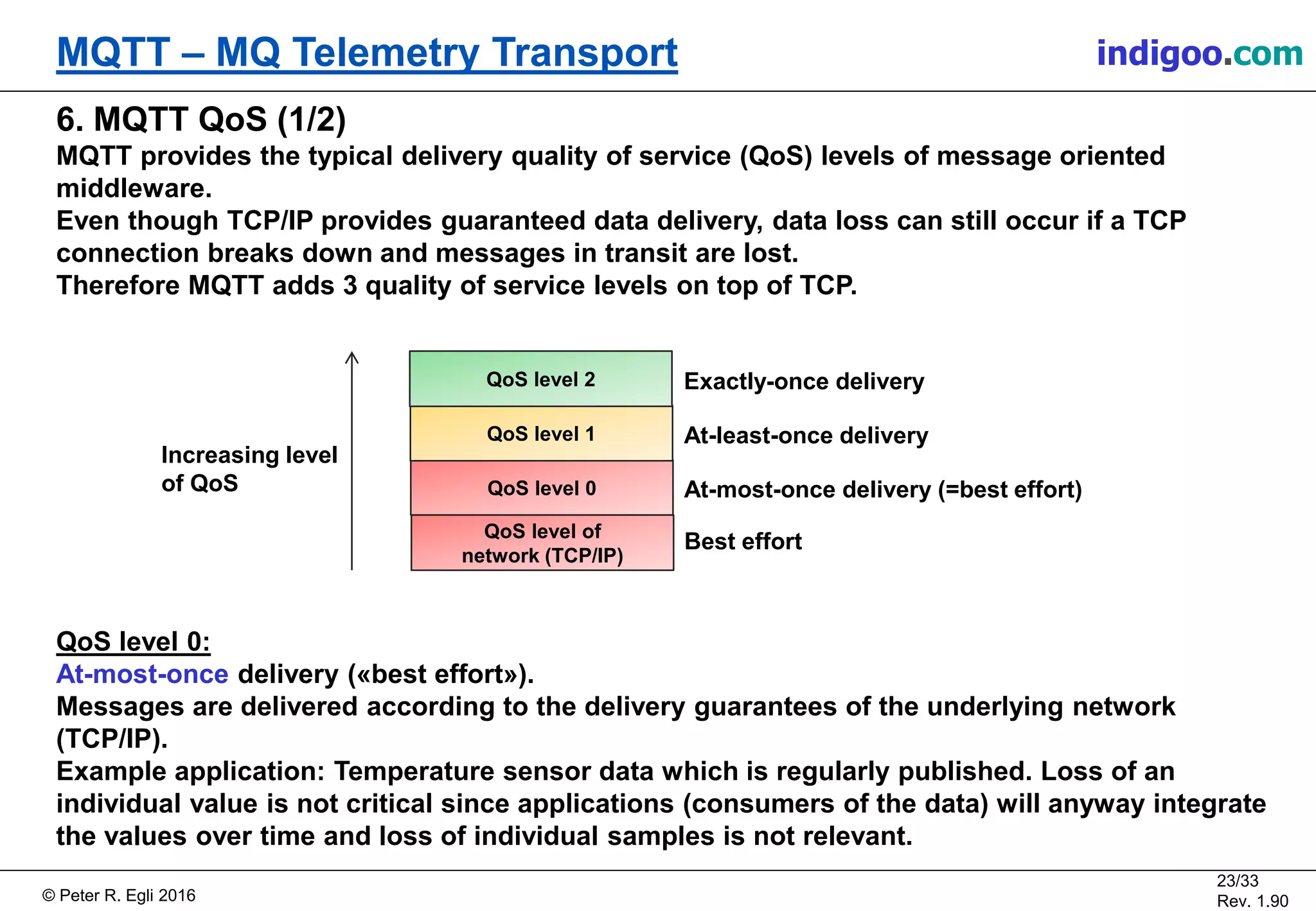
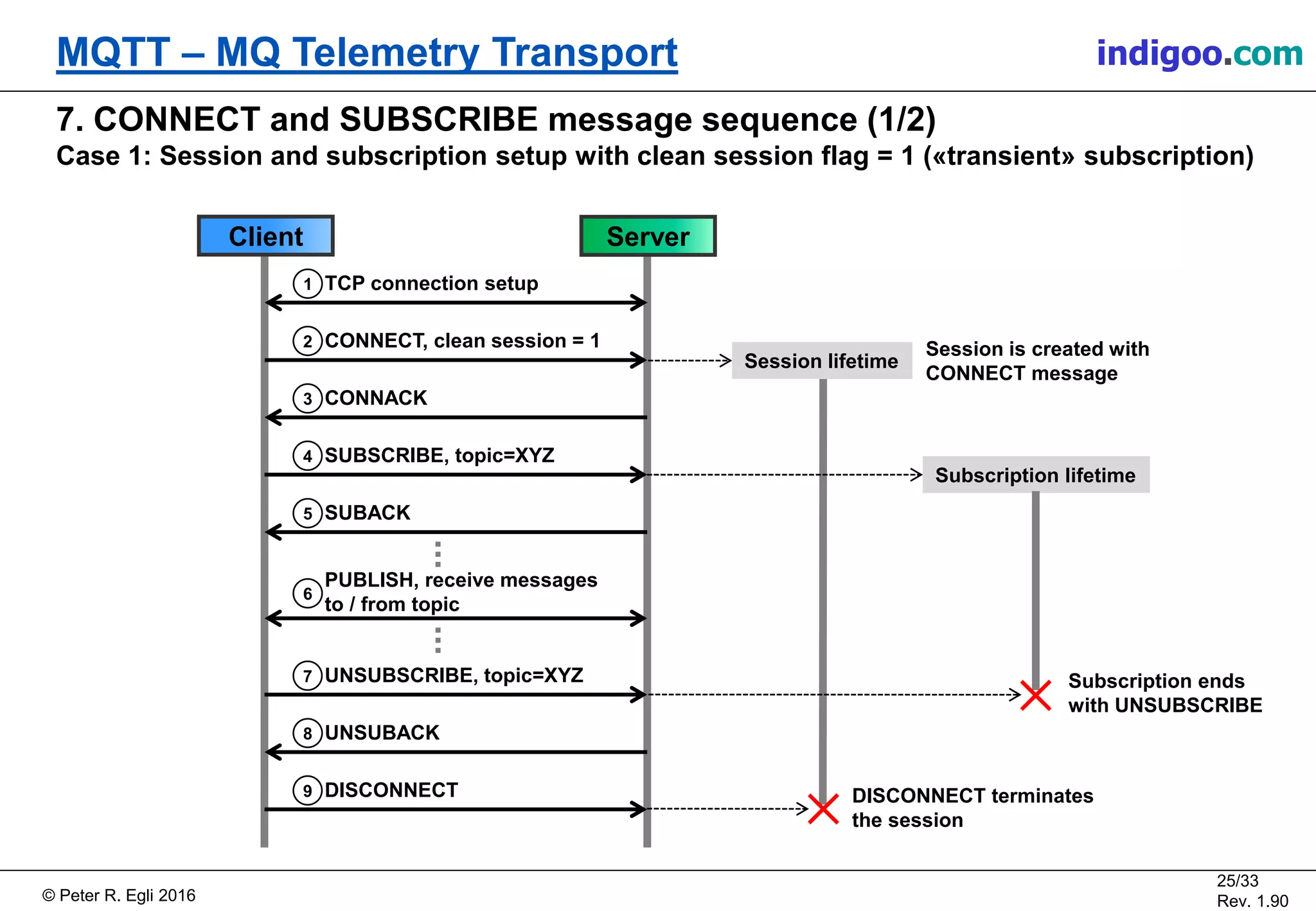
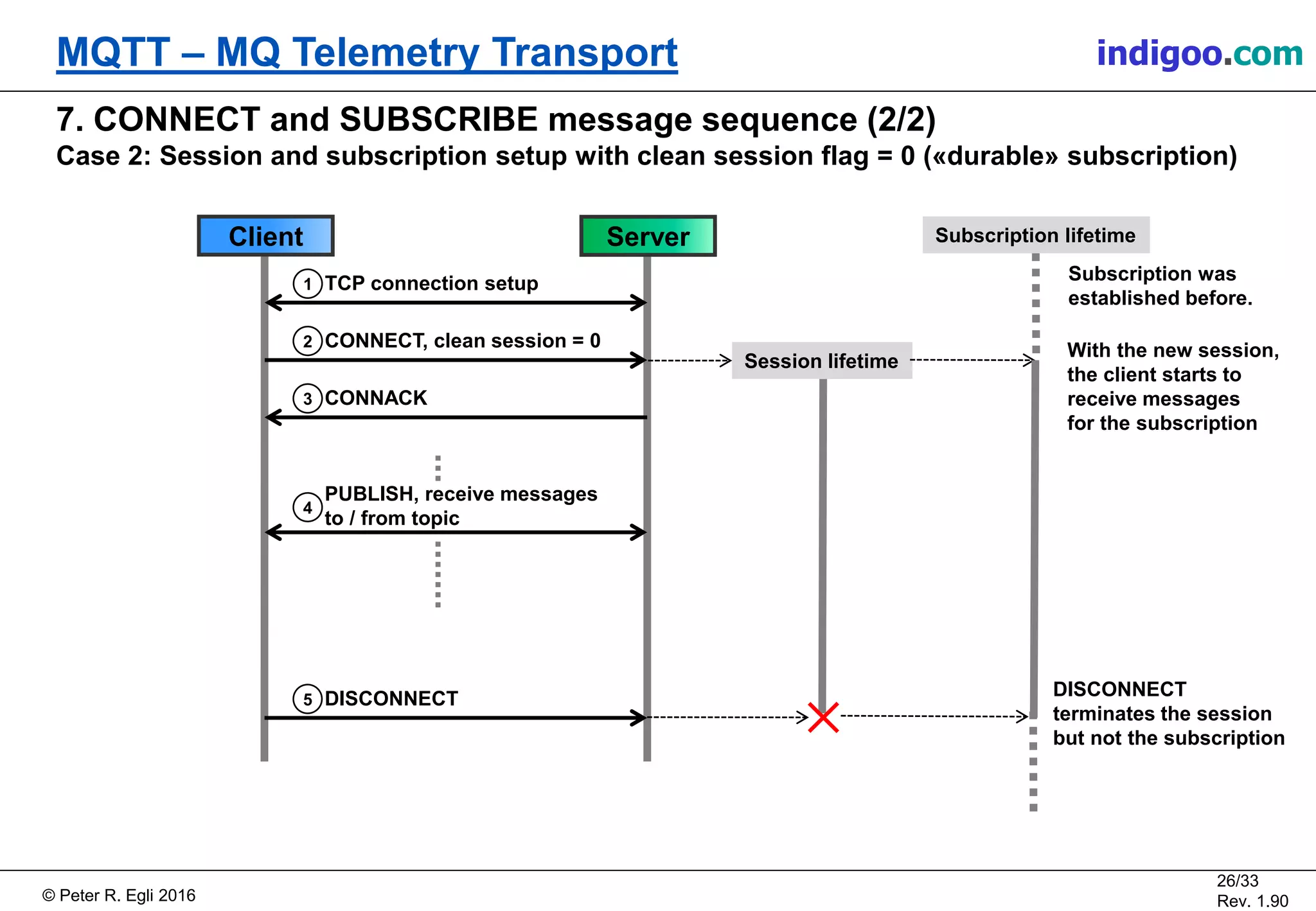
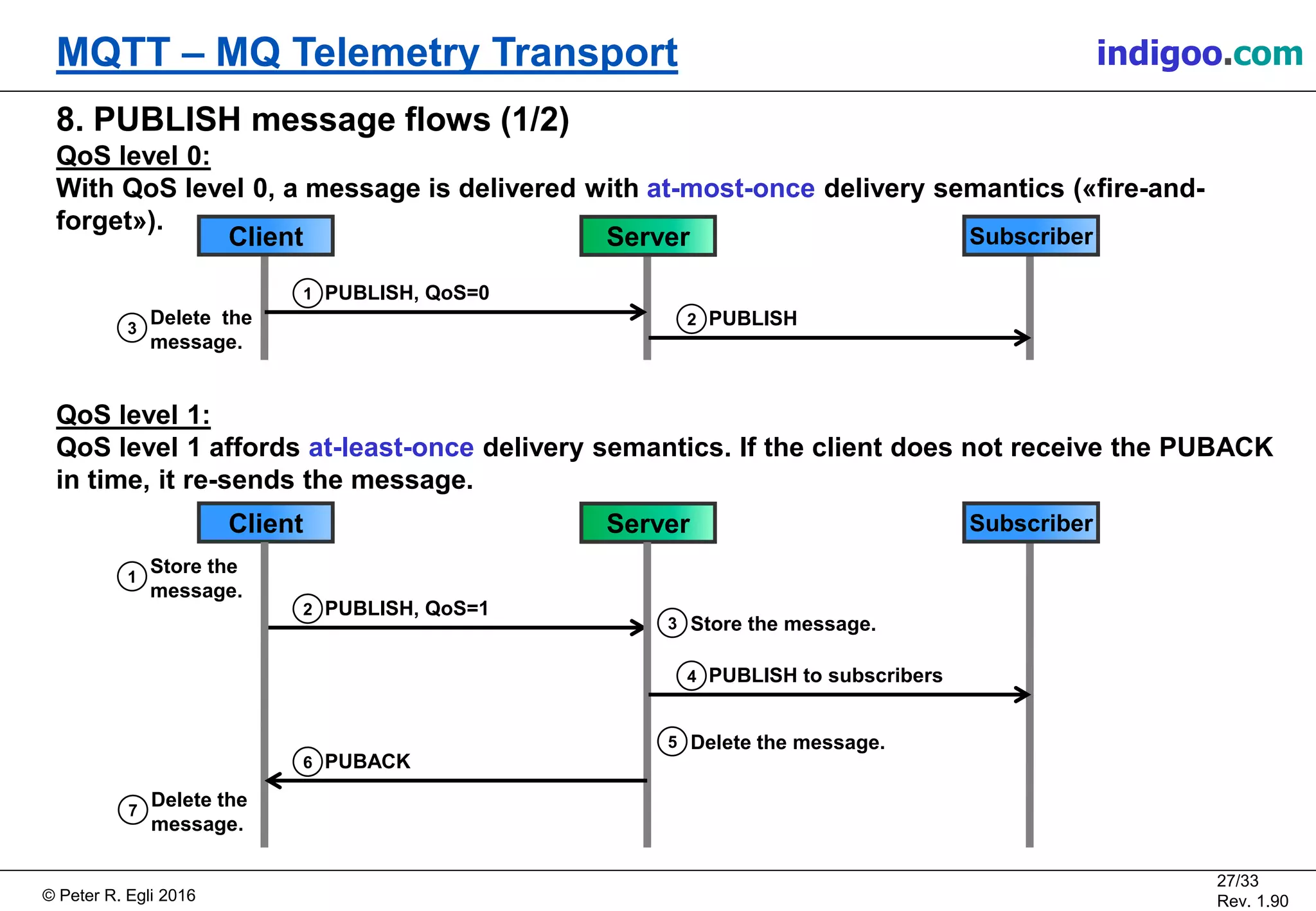
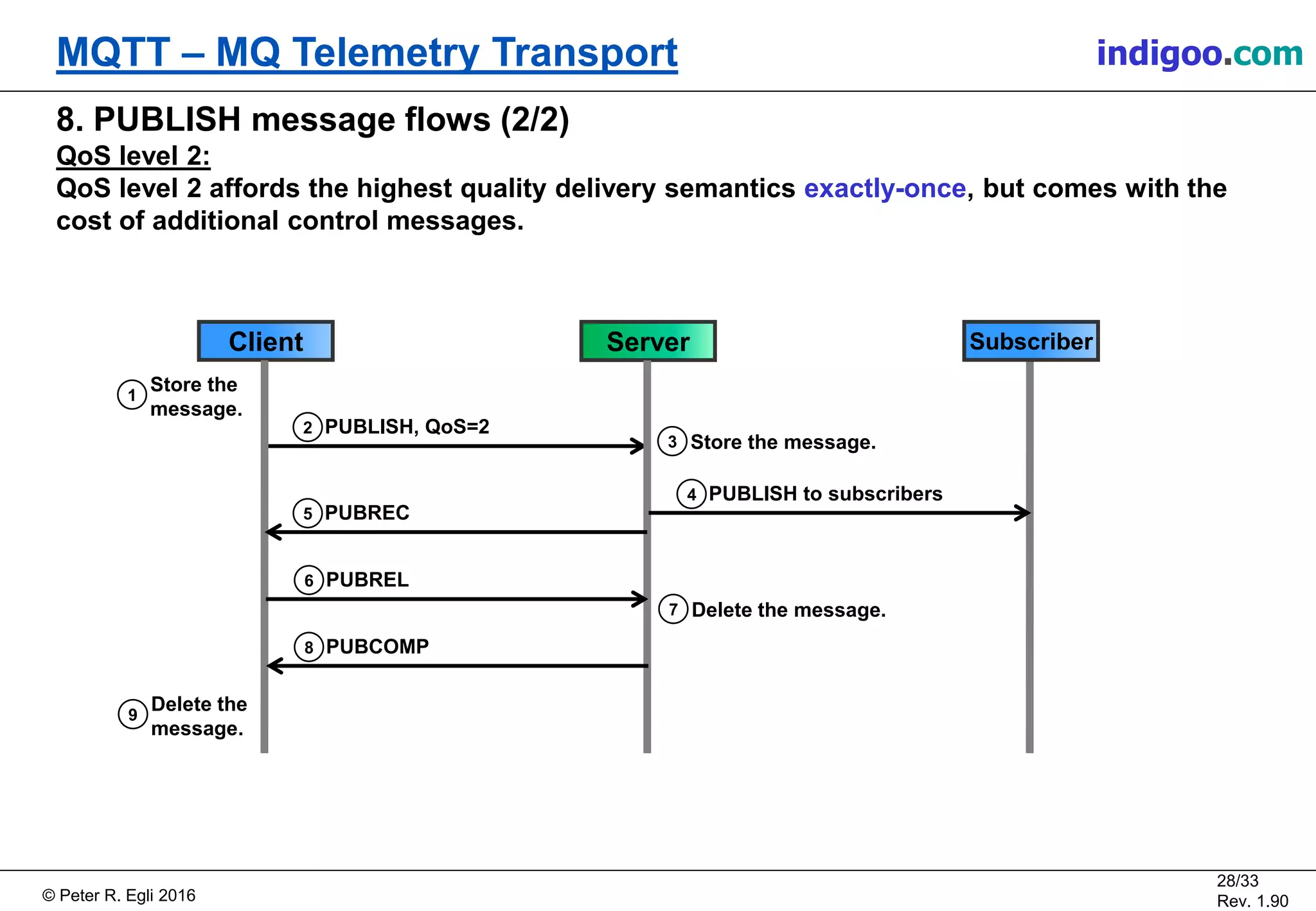
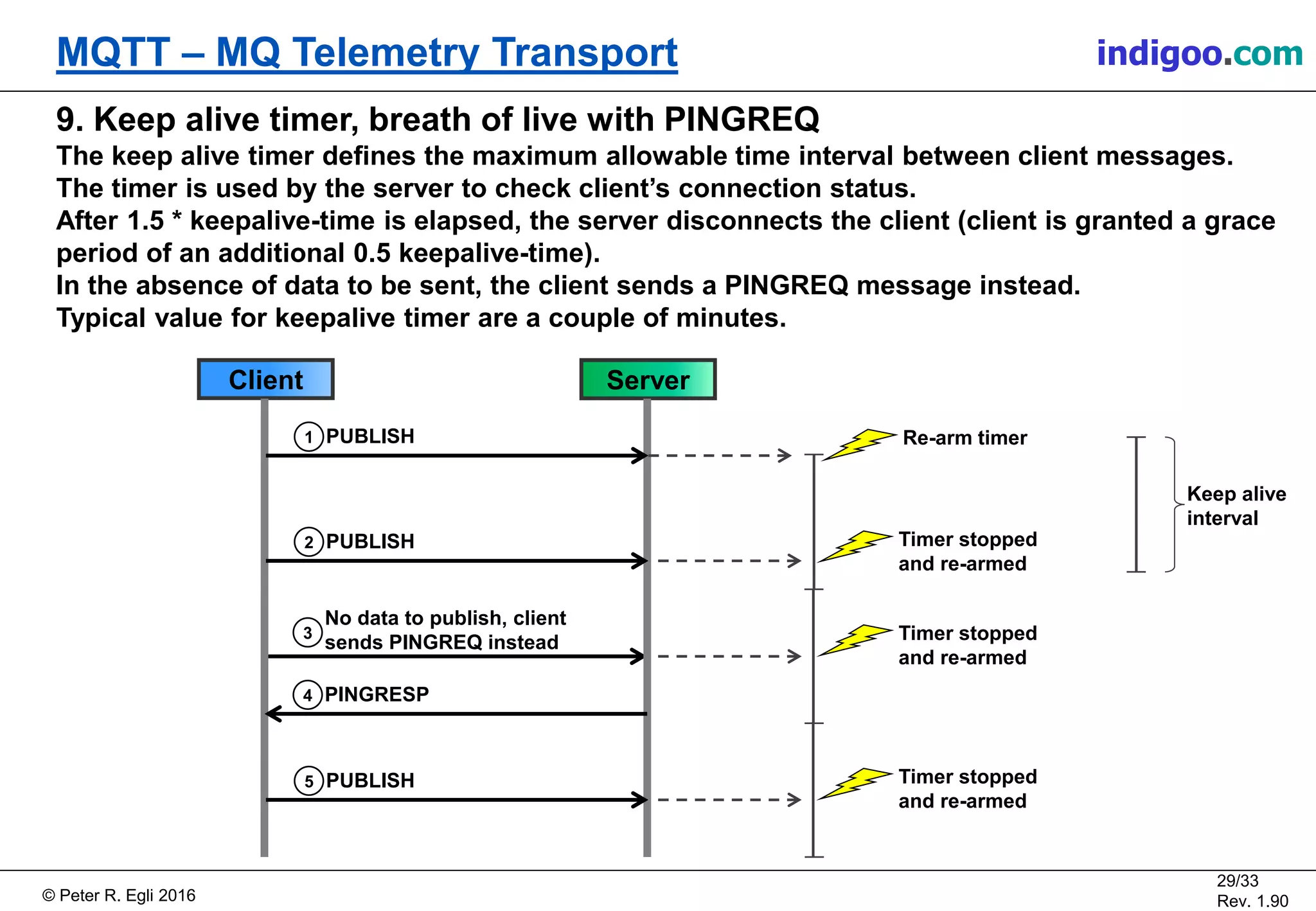
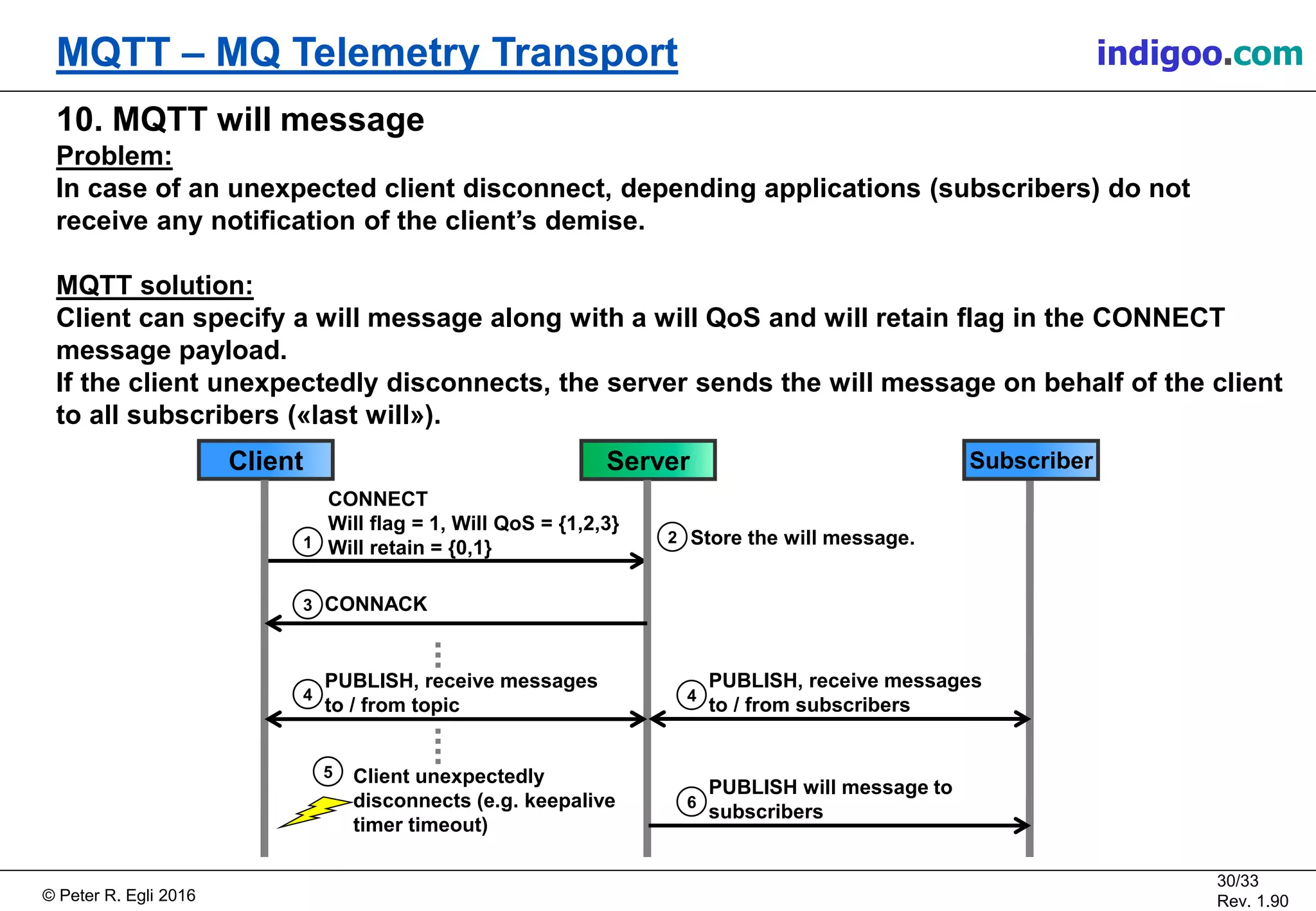
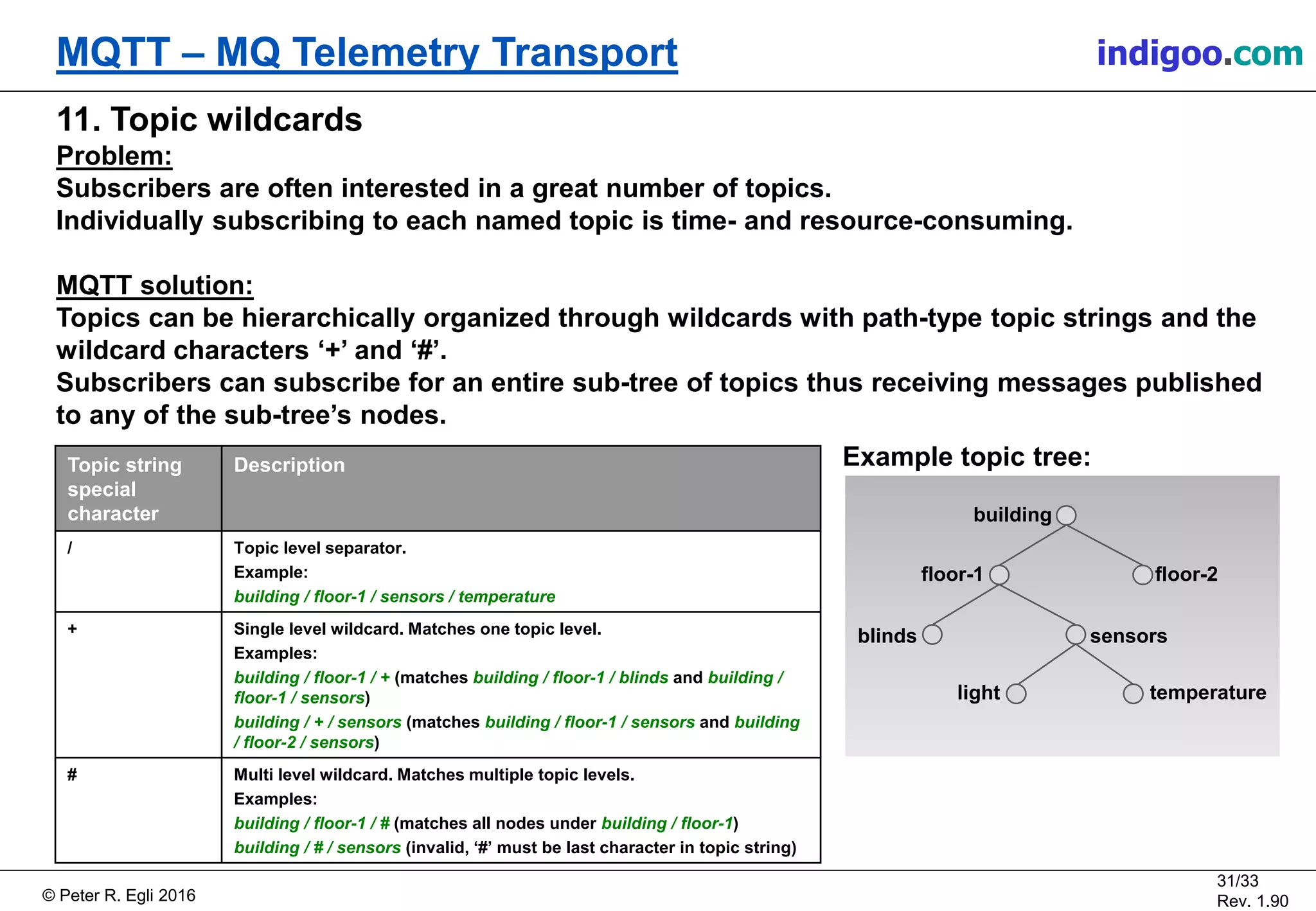
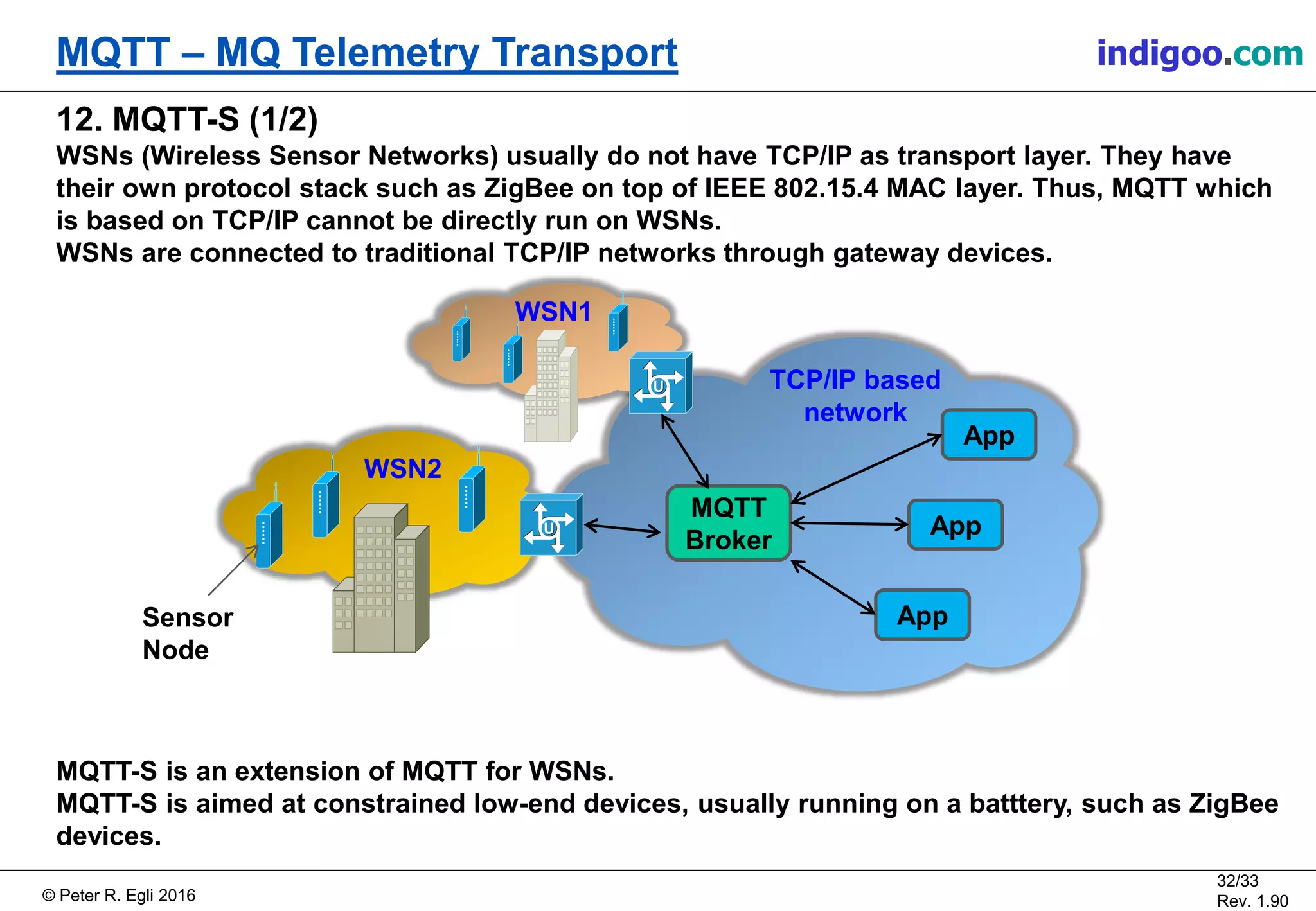
The document provides an introduction to MQTT, a lightweight messaging protocol designed for machine-to-machine (M2M) and Internet of Things (IoT) applications. It covers various aspects of MQTT, including its characteristics, message format, and operational model involving clients, servers, and topics. Additionally, it discusses the origins of MQTT and its evolution into a standardized protocol managed by the OASIS technical committee.