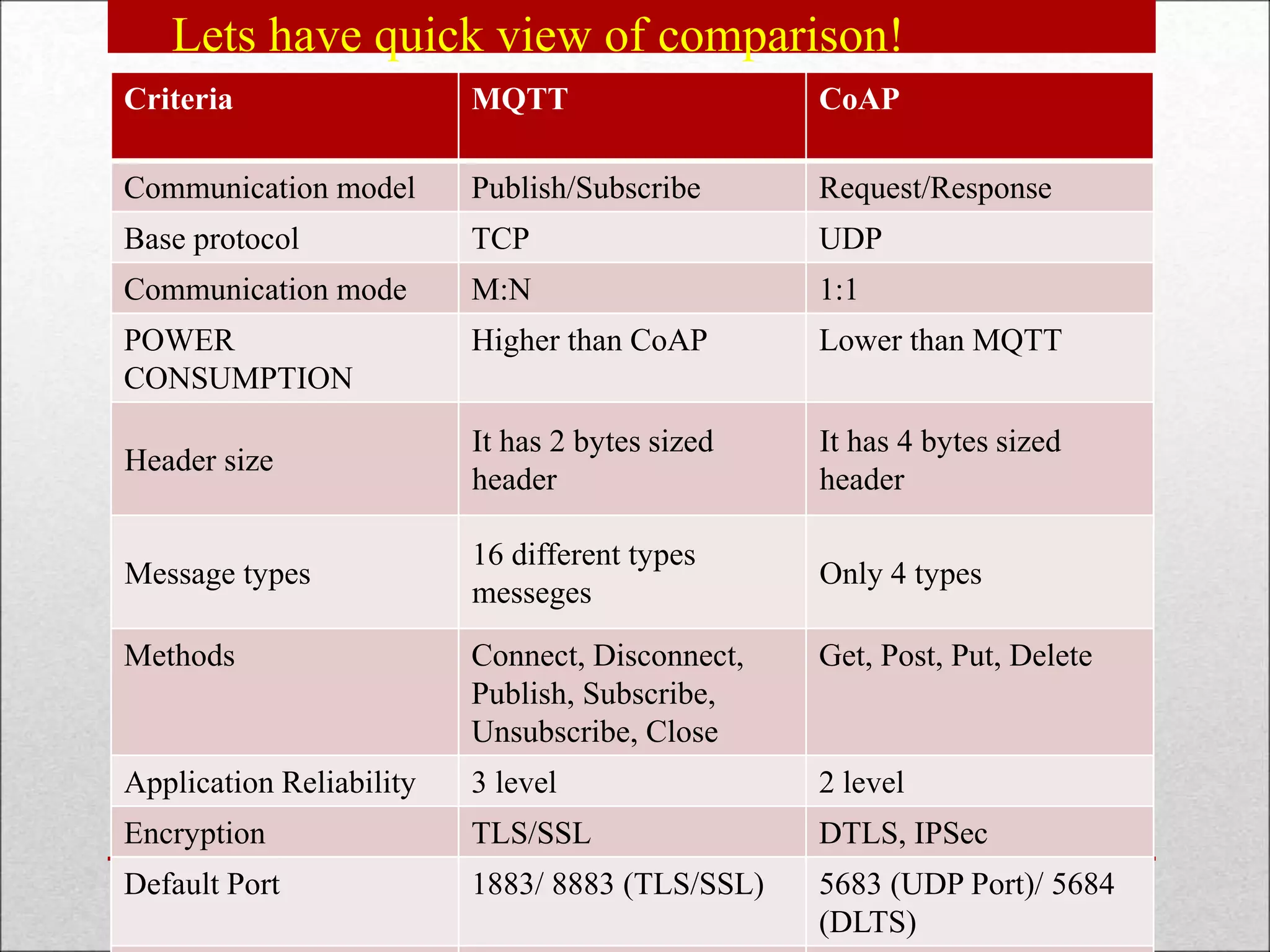
The document presents a comparison of MQTT (Message Queuing Telemetry Transport) and CoAP (Constrained Application Protocol), two lightweight messaging protocols for the Internet of Things (IoT). It outlines their working principles, communication models, message types, and suitability for various IoT applications, highlighting key differences such as MQTT's publish/subscribe model versus CoAP's request/response model. The conclusion emphasizes both protocols' unique benefits and challenges in the context of IoT implementations.
![CoAP – Message layer – Messages Types
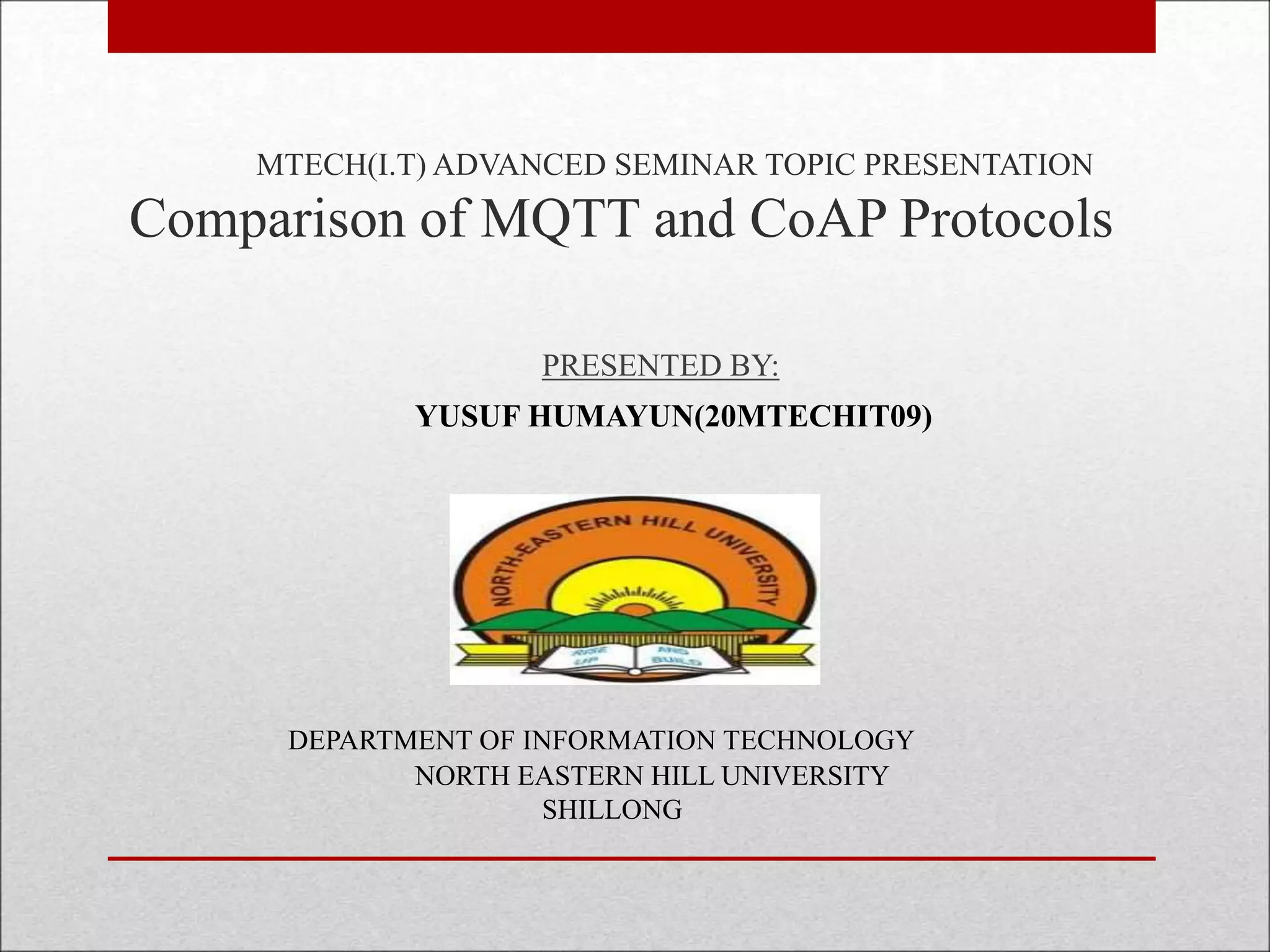
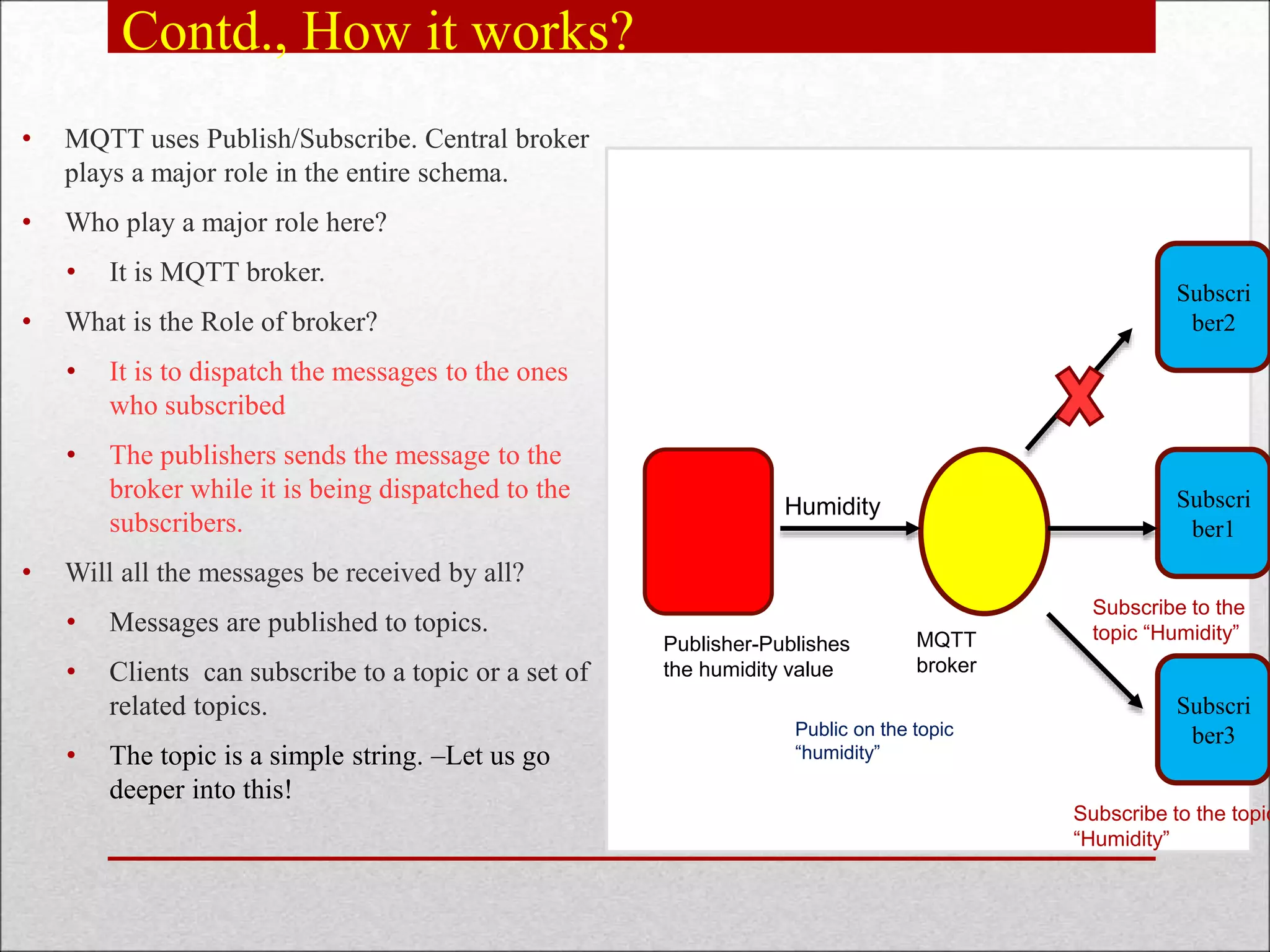
• Supports 4 types of messages.
1. Confirmable(CON)
2. Non Confirmable(NON)
3. Acknowledgement (ACK)
4. Reset(RST)
o Confirmable(CON)- Reliable
messaging
o Retransmit –Untill acknowledgement
arrives with the some message ID.
o Time out/ Recipient fails to process
message – will send RST with
response
c
Client Server
ACK [ADDR]
CON[ADDR]](https://image.slidesharecdn.com/comparisonofmqttandcoapprotocol-210805081122/75/Comparison-of-mqtt-and-coap-protocol-14-2048.jpg)
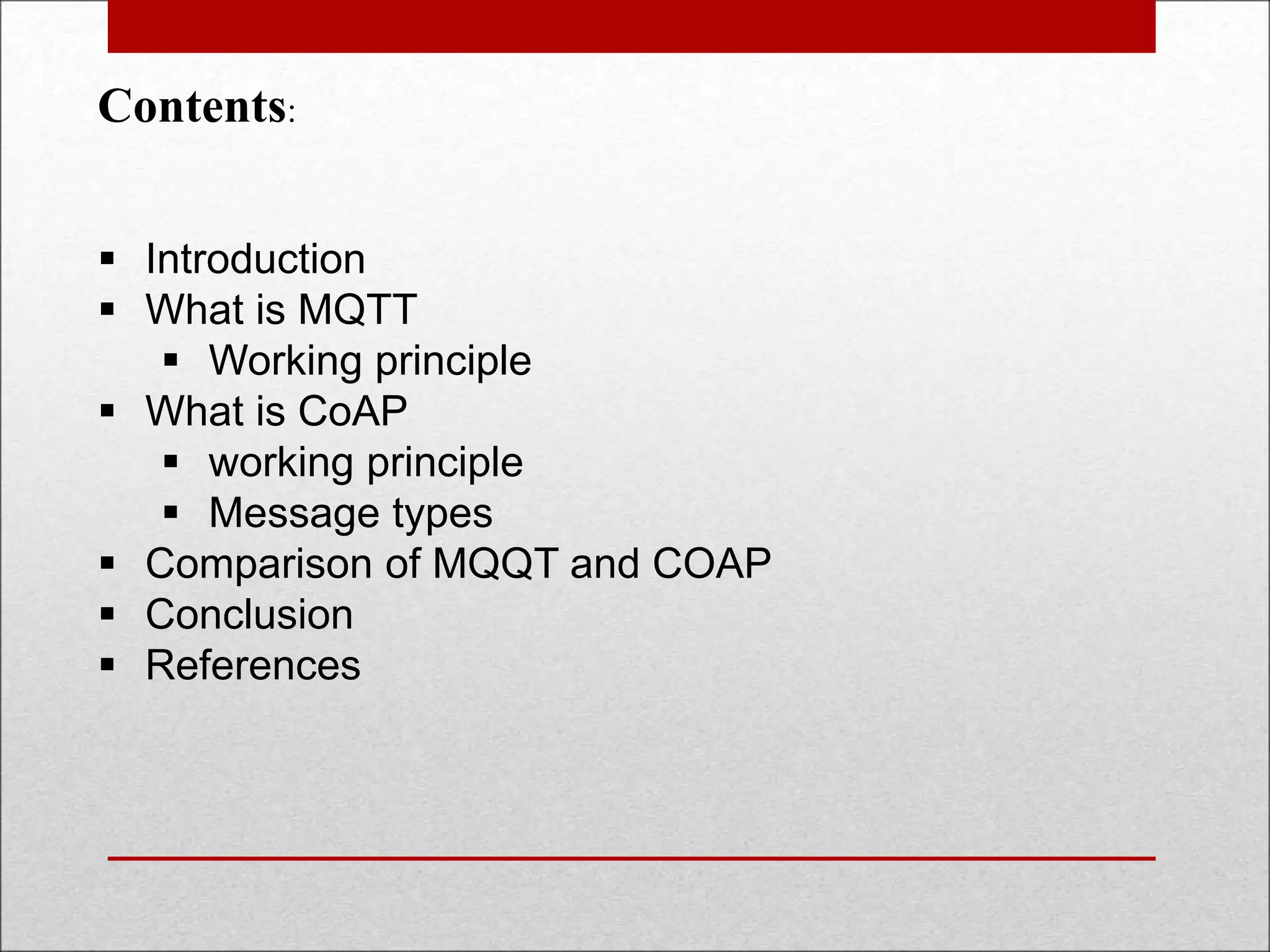
![CoAP –Request/ Response layer-messages
Piggy-backed: Client shall send request with a CON/ NON.
Ack shall be received immediately the corresponding token number and message
(Here, humidity).If not available, the failure code shall be embedded as a part of the
ACK
c
Client Server
CON/NON [MESSAGE_ID]
GET/Humidity
(Token number)
c
Client Server
ACK [MESSAGE-ID]
(Token Number)
60%
CON/NON [MESSAGE_ID]
GET/Humidity
(Token number)
ACK [MESSAGE-ID]
(Token Number)
NOT FOUND](https://image.slidesharecdn.com/comparisonofmqttandcoapprotocol-210805081122/75/Comparison-of-mqtt-and-coap-protocol-16-2048.jpg)
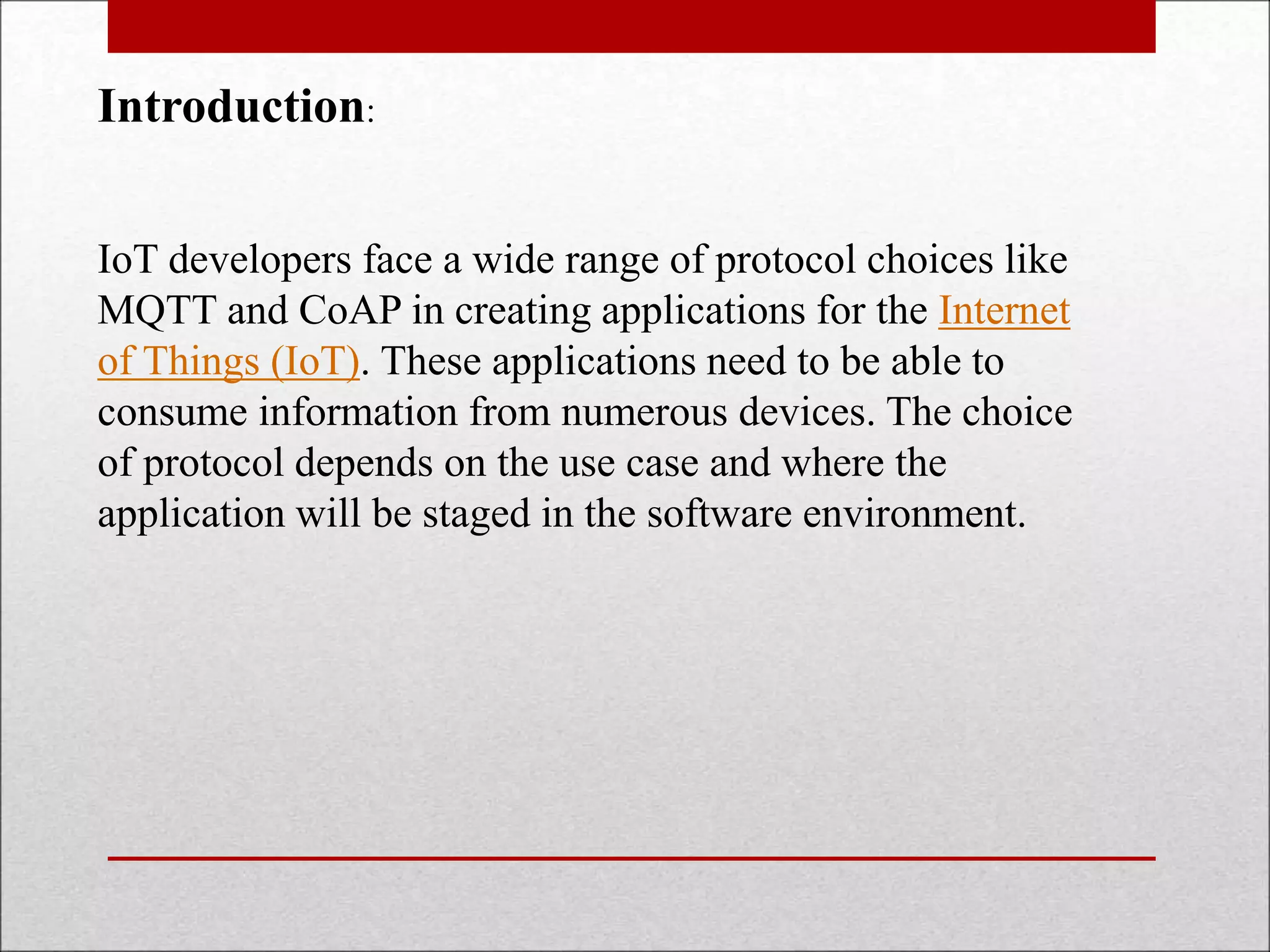
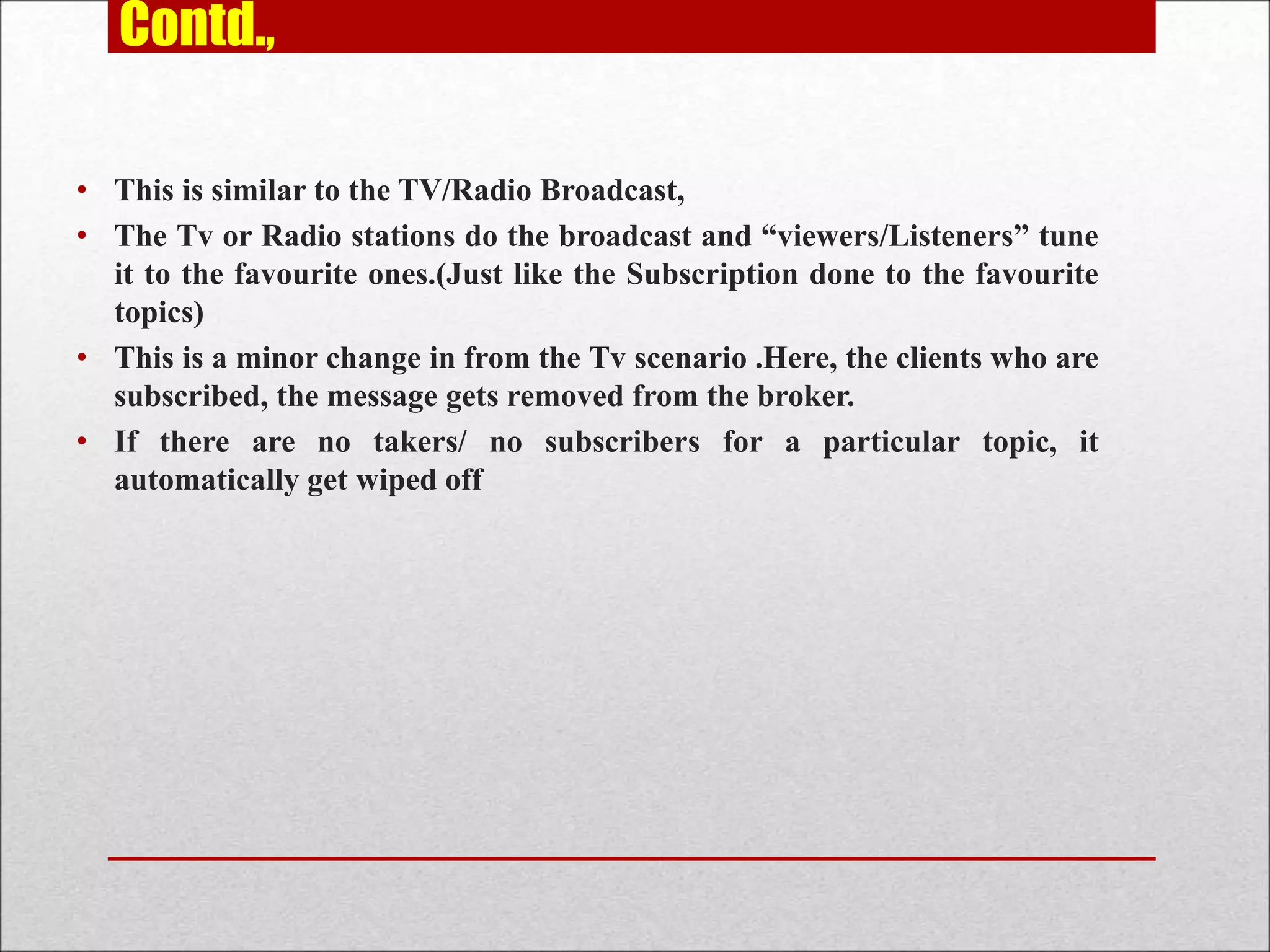
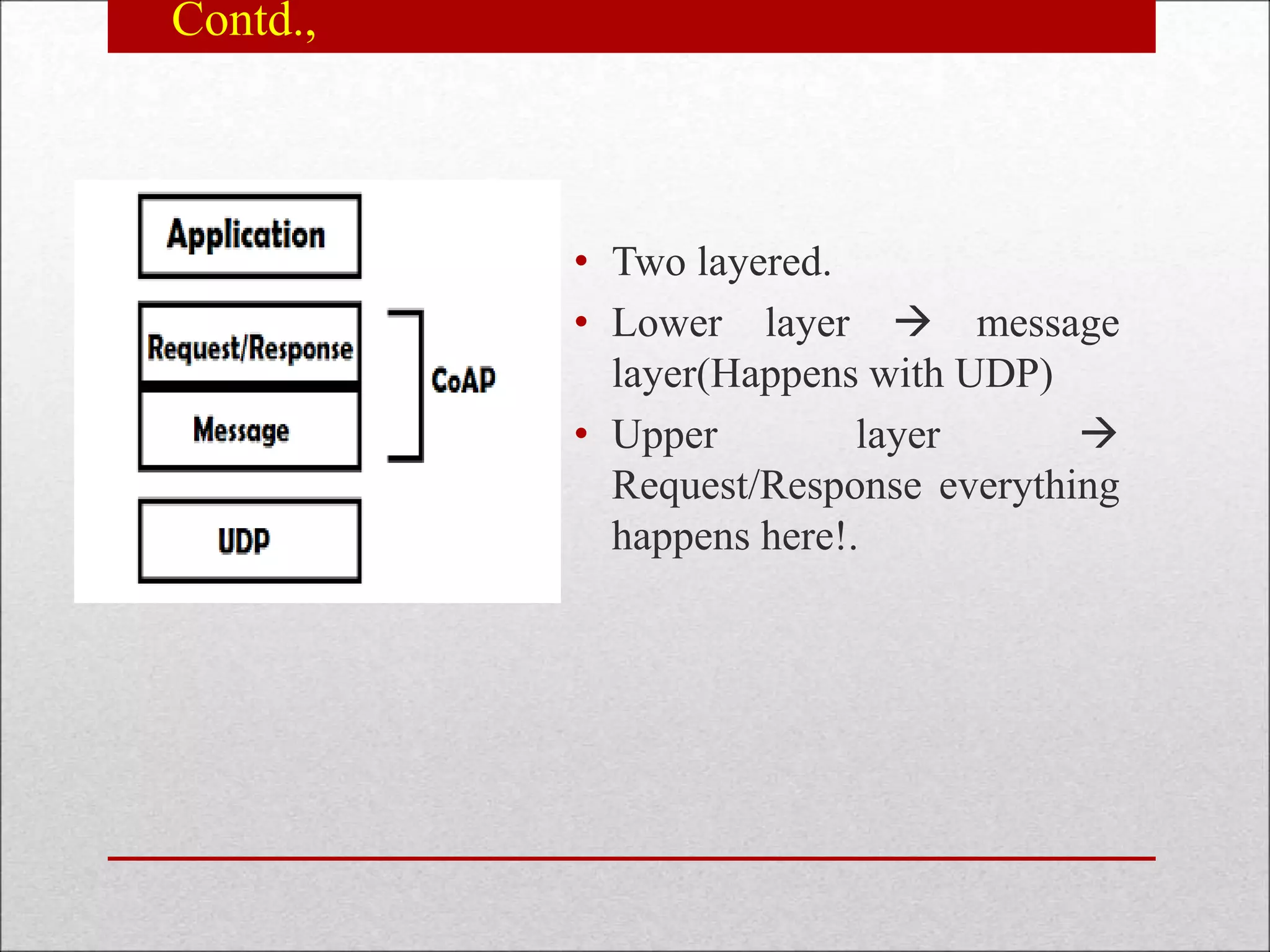
![Contd.,
• Separate response: when a
CON type message is sent to
the server from the client
and in case, the server is
unable to respond
immediately, An Empty ACK
shall be reverted.
• After some time(not sure
how much),when the server
can send the response ,it shall
send a CON message with
data, ACK shall be back from
the client
c
Client Server
CON/NON [MESSAGE_ID]
GET/Humidity
(Token number)
CON/NON [MESSAGE_ID]
GET/Humidity
60%
ACK
ACK](https://image.slidesharecdn.com/comparisonofmqttandcoapprotocol-210805081122/75/Comparison-of-mqtt-and-coap-protocol-17-2048.jpg)
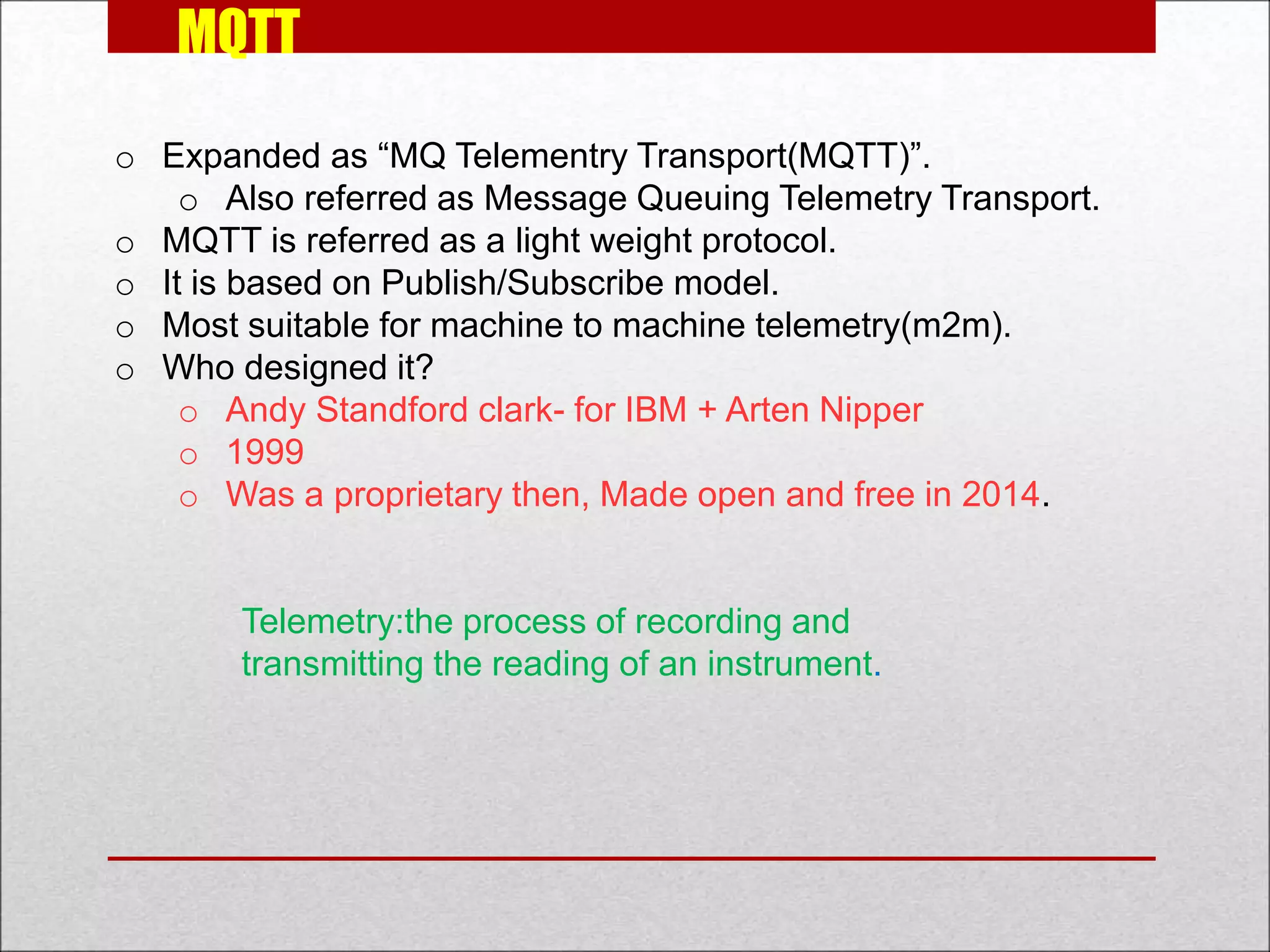
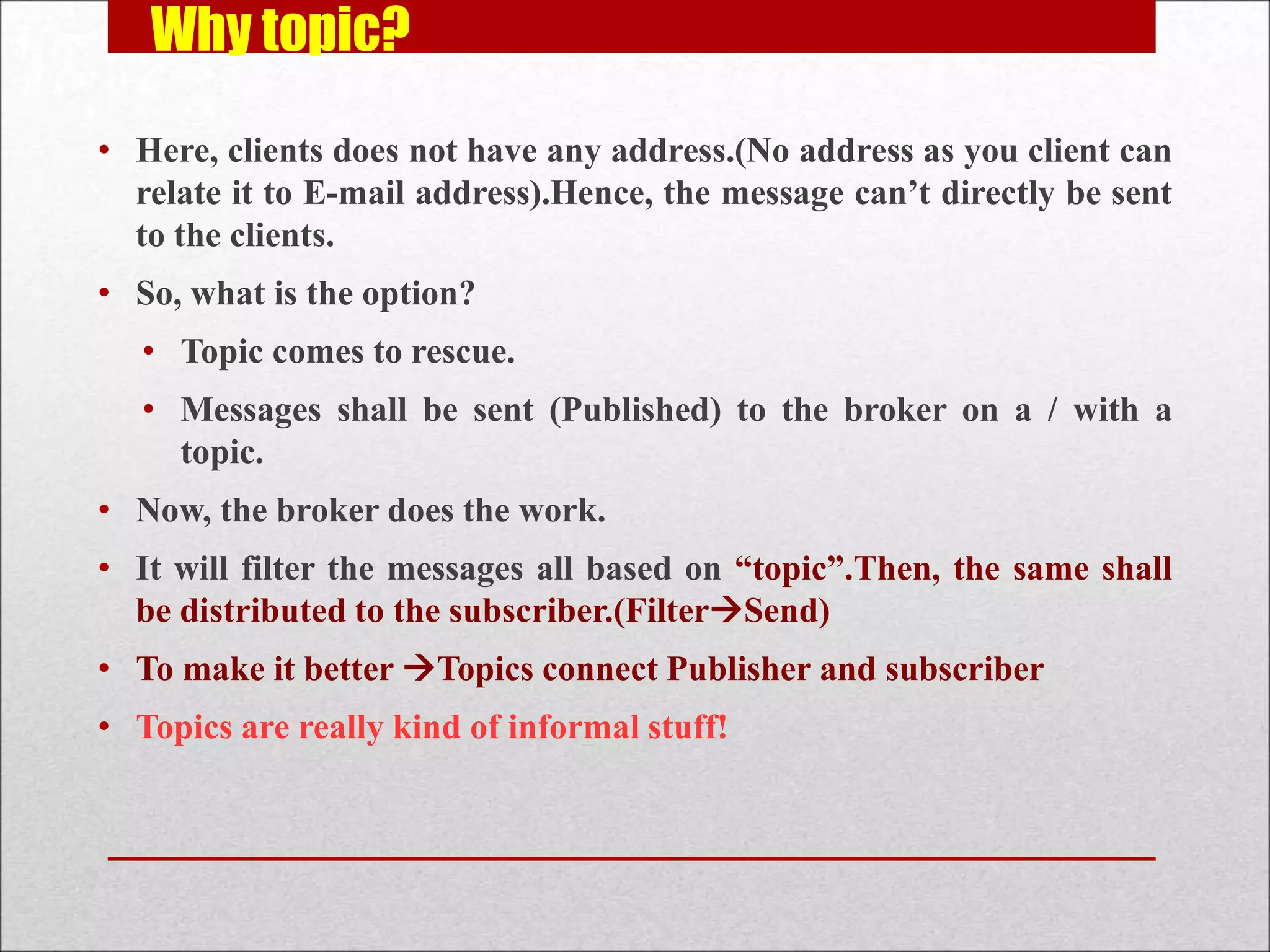
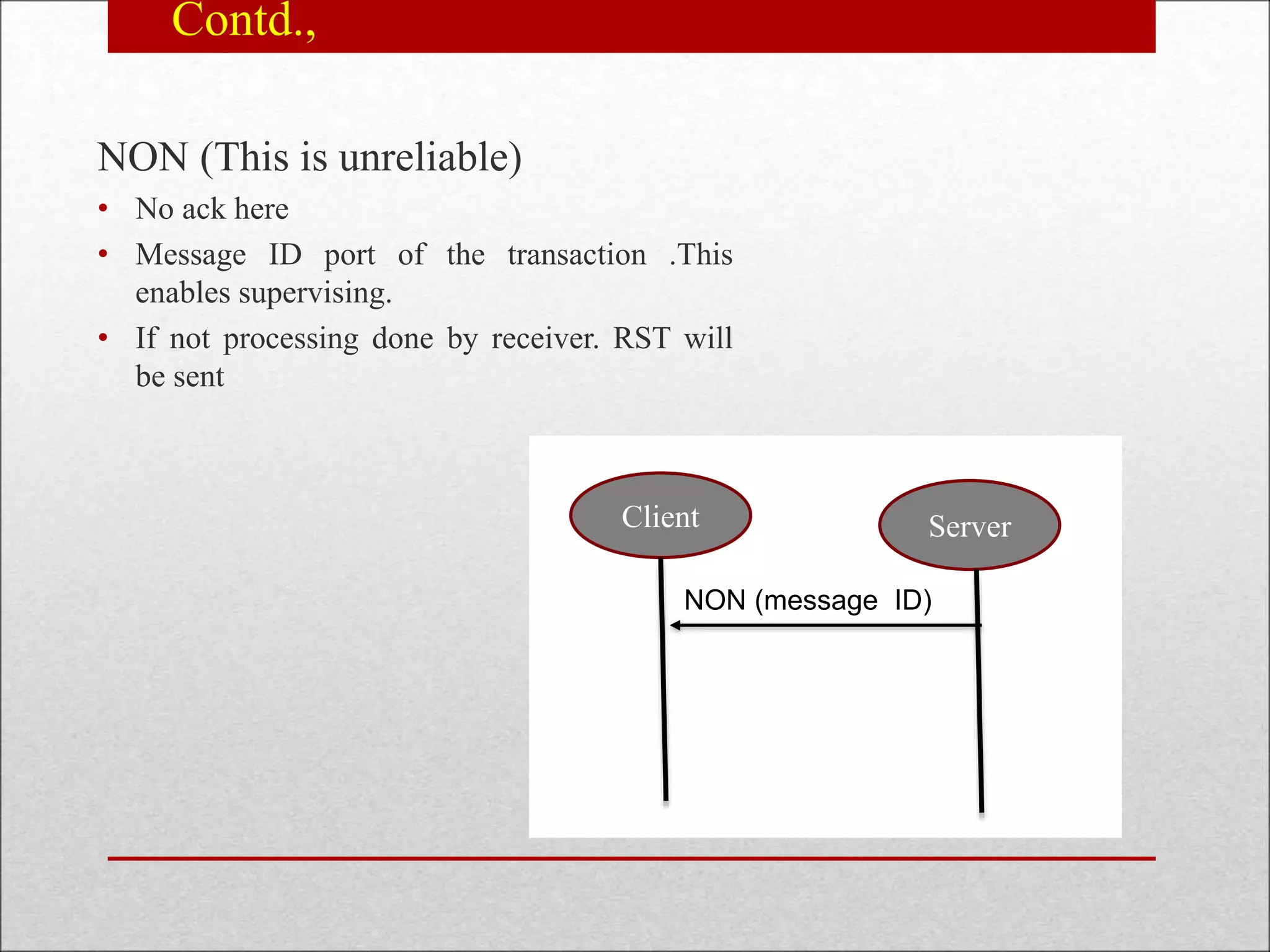
![Contd.,
o Non confirmable request and response:
o Here, NON type message shall be sent from the
client to server .Server need not give ACK. Server
can send a NON type response in turn
c
Client Server
CON/NON [MESSAGE_ID]
GET/Humidity
(Token number)
CON/NON
[MESSAGE_ID]
GET/Humidity
60%](https://image.slidesharecdn.com/comparisonofmqttandcoapprotocol-210805081122/75/Comparison-of-mqtt-and-coap-protocol-18-2048.jpg)


![References:
[1] Gazis, Vangelis, et al. A survey of technologies for the internet of things.,2015
International Wireless Communications and Mobile Computing Conference
(IWCMC). IEEE, 2015.
[2] Karagiannis, Vasileios, et al. A survey on application layer protocols for the
internet of things,Transaction on IoT and Cloud computing 3.1 (2015): 11-17.
[3] Grigorik, Ilya. Native web communication protocols and their effects on the
performance of web services and systems.,Transaction on IoT and Cloud
computing 3.1 (2015): 11-17.
[4] Karagiannis, Vasileios, et al. Making the web faster with HTTP
2.0.,Communications of the ACM 56.12 (2013): 42-49.
[5] Stansberry, J. ”MQTT and CoAP: Underlying protocols for the IoT.”,Electronic
Design (2015).
[6] Colitti, Walter, Kris Steenhaut, and Niccolo De Caro. ` ”Integrating wireless
sensor networks with the web.”,Extending the Internet to Low power and Lossy
Networks (IP+ SN 2011) (2011).](https://image.slidesharecdn.com/comparisonofmqttandcoapprotocol-210805081122/75/Comparison-of-mqtt-and-coap-protocol-22-2048.jpg)