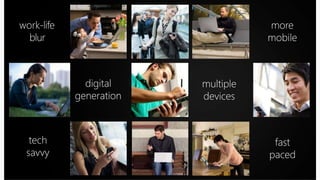
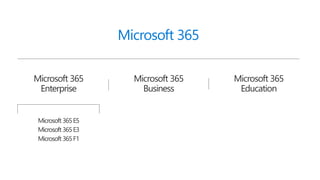
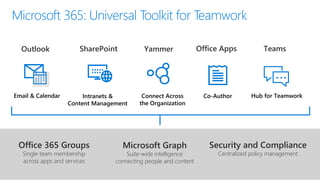
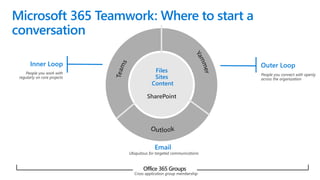
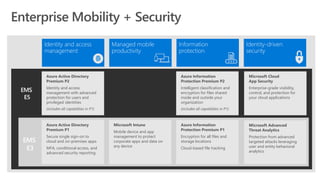
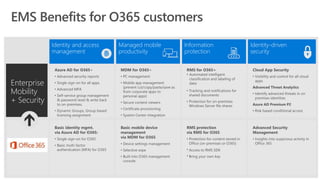
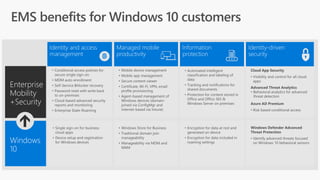
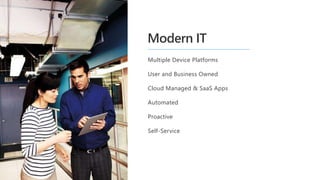
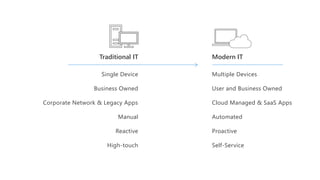
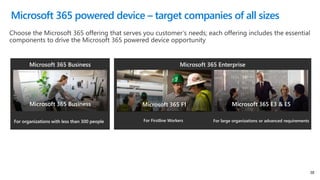
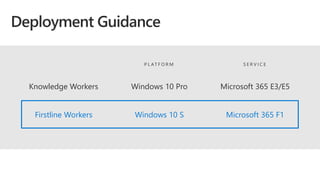
The document provides an overview of the modern workplace through Microsoft 365, emphasizing digital transformation, intelligent security, and collaboration tools, such as Microsoft Teams. It outlines the benefits of integrating Office 365, Windows 10, and enterprise mobility for enhanced productivity and security, while also detailing the various Microsoft 365 plans available for different business needs. Additionally, it highlights the importance of effective deployment and user adoption strategies to maximize the potential of Microsoft 365 services.