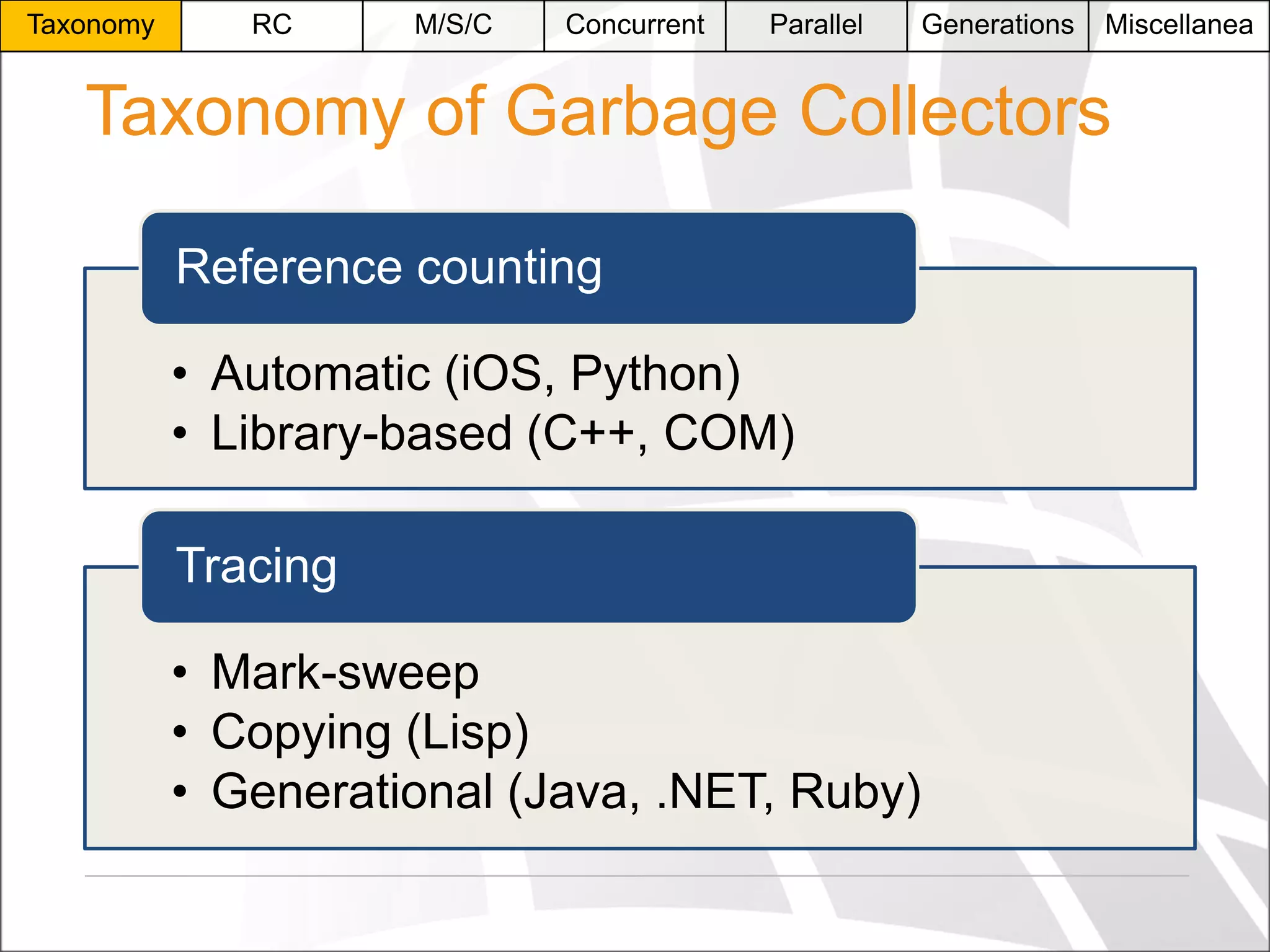
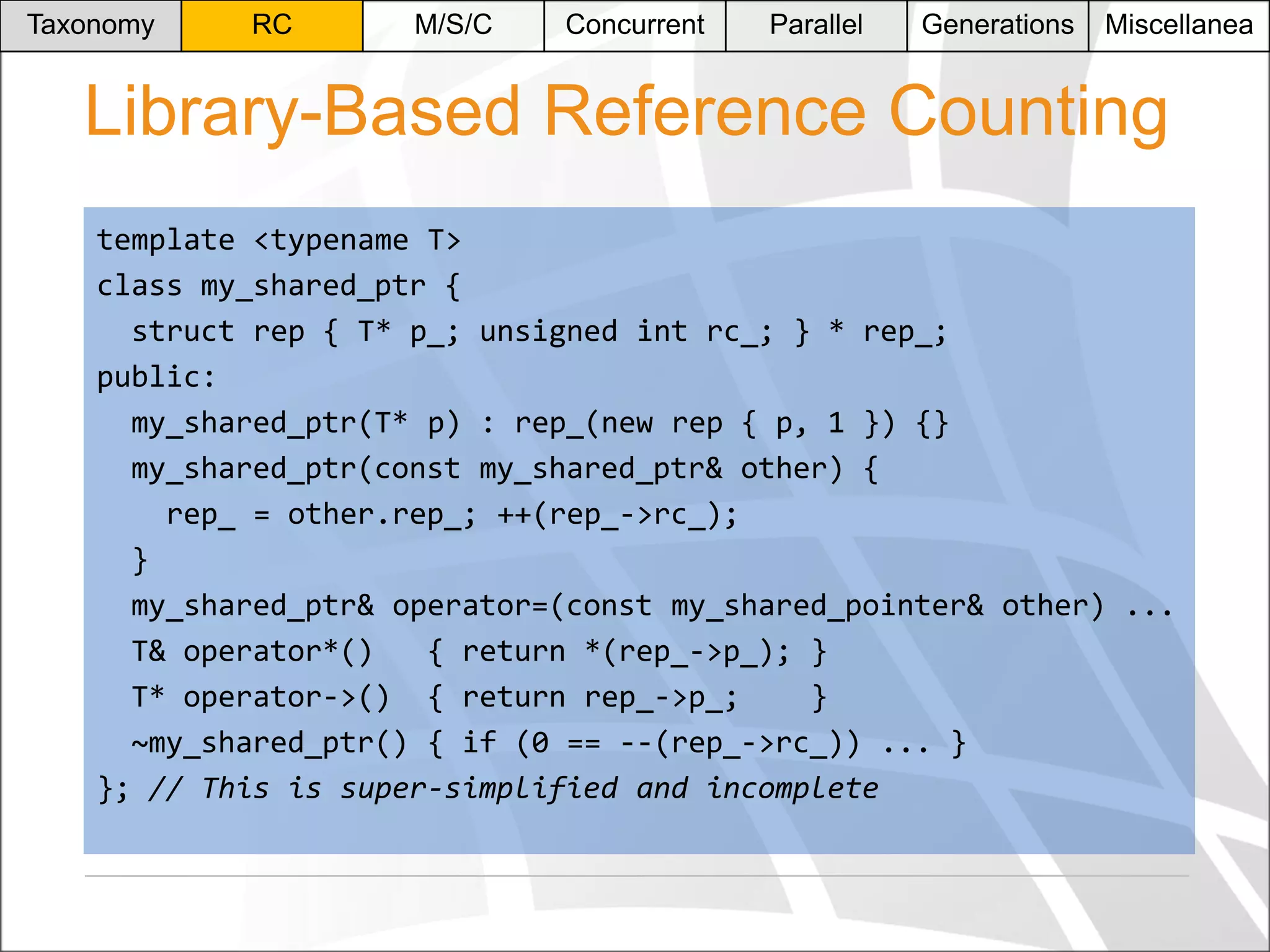
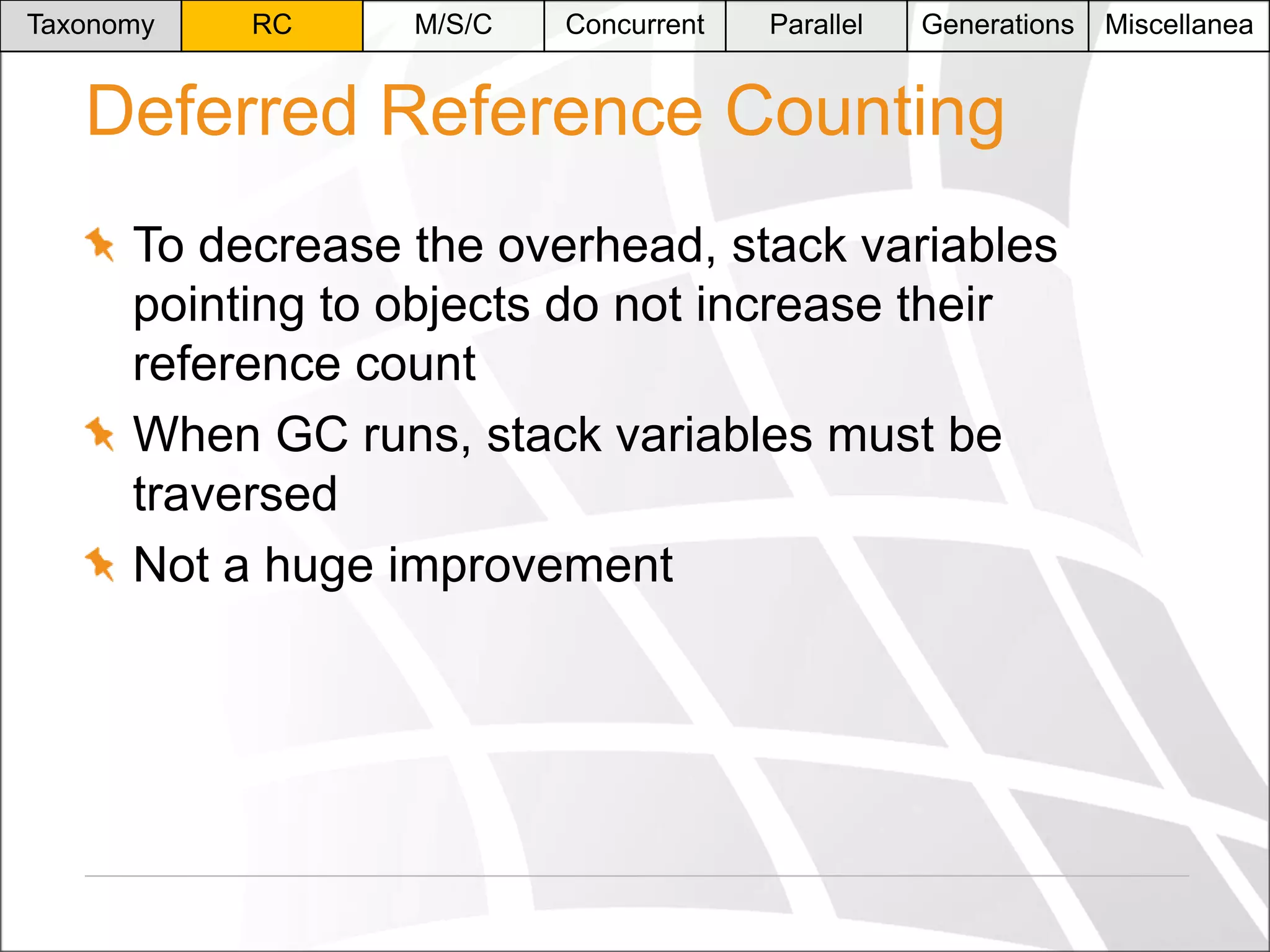
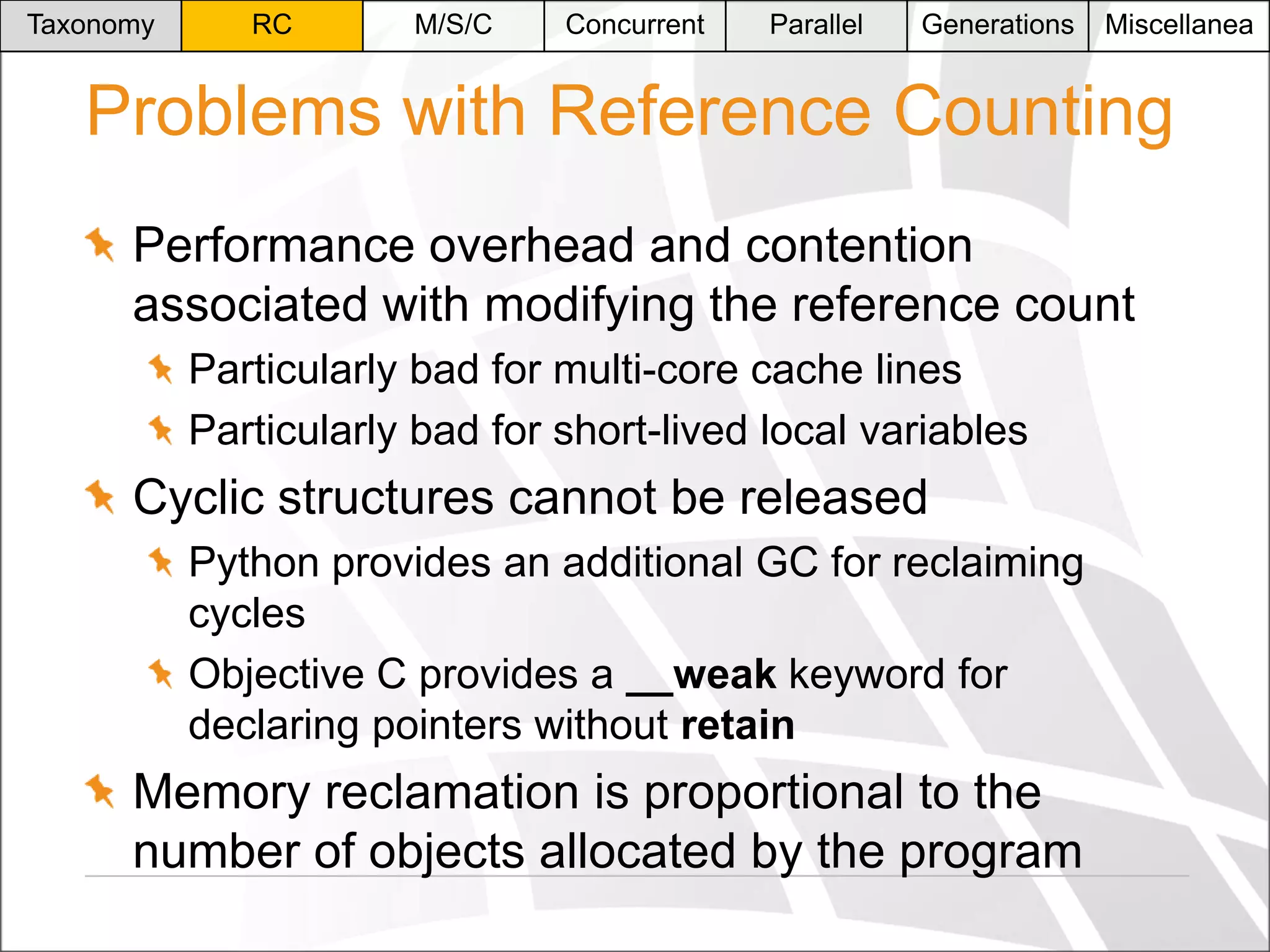
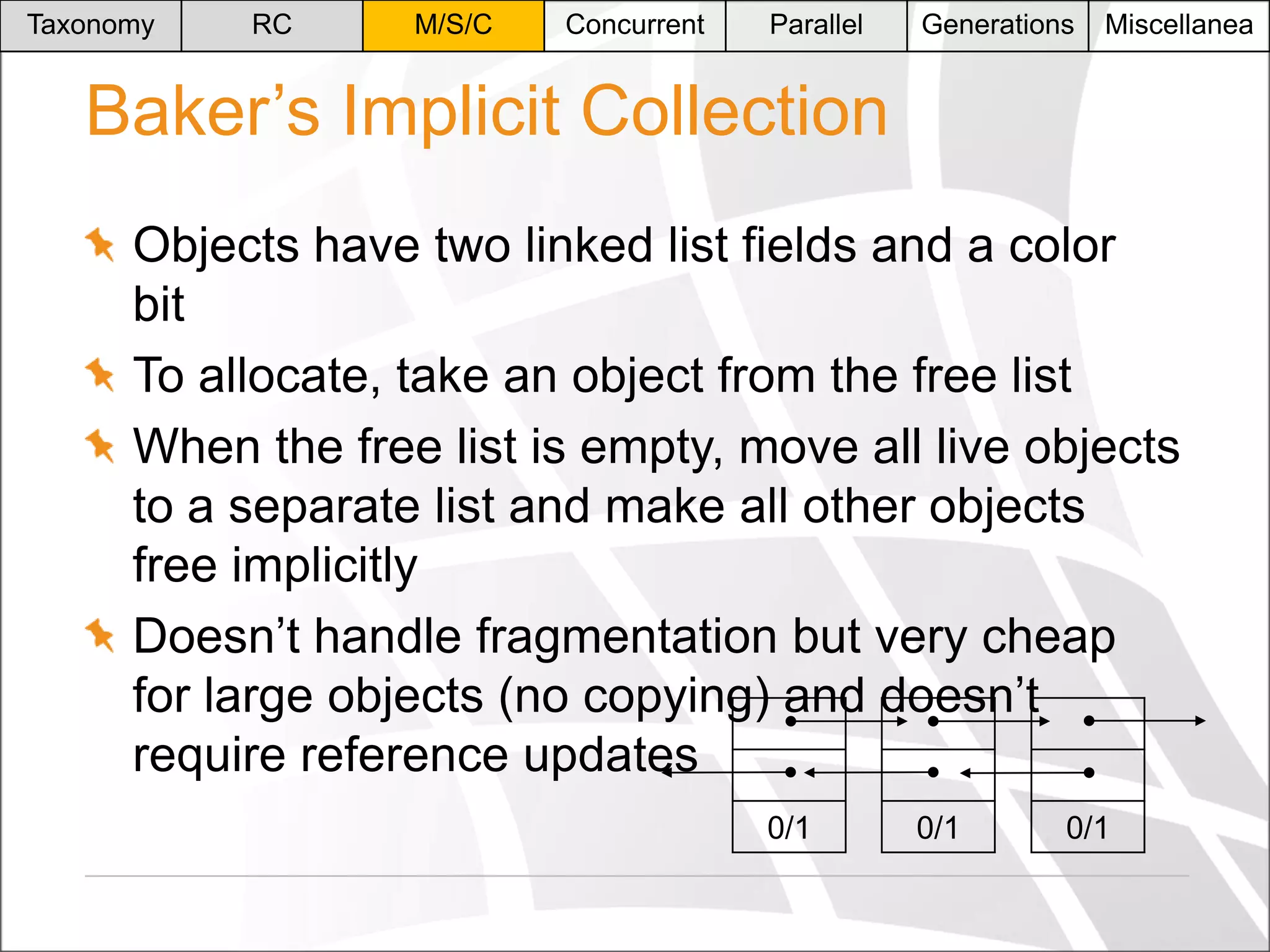
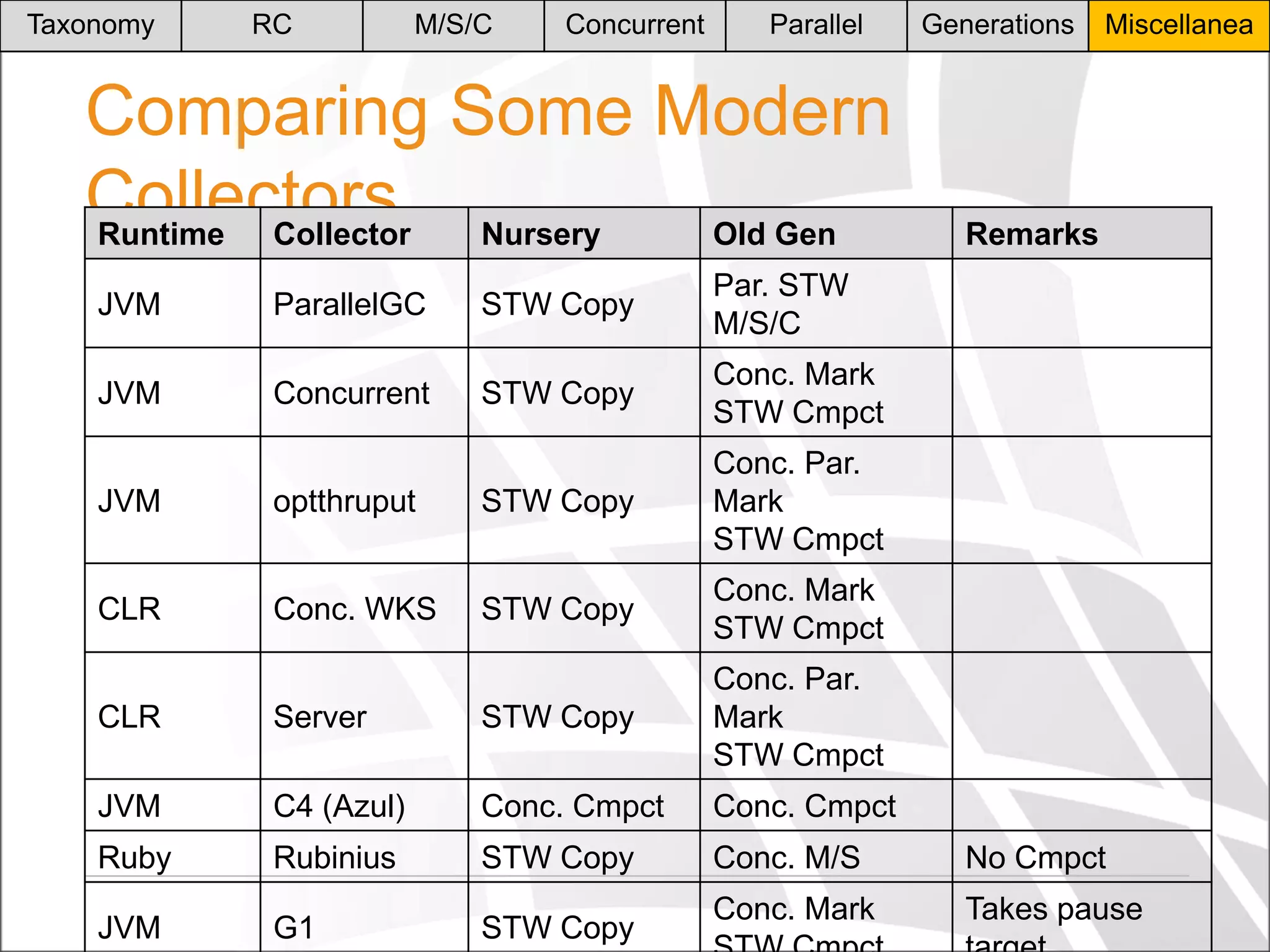
The document discusses advancements in garbage collection techniques, including automatic reference counting and various tracing methods such as mark-sweep, copying, and generational approaches. It highlights the complexities of modern memory management, particularly in concurrent environments, and details systems like Azul's fully concurrent collectors designed for high-performance applications. The content also reviews practical implementations and performance implications of different garbage collection strategies in languages such as Java and Objective-C.
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Automatic Reference Counting
Used by Apple since iOS 4 with the LLVM
Objective-C compiler
-(NSString *)foo:(NSString *)str {
NSString *temp = [str lowercaseString];
_field = temp;
return temp;
}
[obj foo:str];
Miscellanea](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-7-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Miscellanea
Automatic Reference Counting
The compiler inserts release/retain messages
to maintain the reference count
-(NSString *)foo:(NSString *)str {
NSString *temp = [str lowercaseString];
_field = [temp retain];
[str release];
return temp;
}
[obj foo:[str retain]];](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-8-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Miscellanea
How To Suspend Threads Safely?
(1)
The compiler occasionally inserts suspension
request checks, known as safe points
for (int k = 0; k < 100000; ++k)
{
LengthyCalculation(k);
mov byte ptr [pGuardPage], 0
}](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-19-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Miscellanea
How To Suspend Threads Safely?
(2) GlobalExceptionHandler(PEXCEPTION_POINTERS exc)
LONG
{
if (exc->ExceptionRecord->ExceptionCode ==
EXCEPTION_ACCESS_VIOLATION &&
exc->ExceptionRecord->Parameters[0] == pGuardPage)
{
SetEvent(hThreadEvents[nThisThread]);
WaitForSingleObject(hResumeEvent, ...);
return EXCEPTION_CONTINUE_EXECUTION;
}
return EXCEPTION_CONTINUE_SEARCH;
}](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-20-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Miscellanea
Inter-Generational Relations
This design breaks if objects from gen 1/2
reference objects from gen 0
Write barrier to perform a.f = b:
// assume that a is in ECX, b is in EBX
cmp
ecx, dword ptr [gEndOfGeneration0]
jg
SKIP
mov
edx, ecx
shr
edx, 10
xor
eax, eax
cmpxchg
1, byte ptr [pCardTable + edx]
SKIP:
mov
dword ptr [ecx + OFFSET(f)], ebx
Range
Has ref to
gen 0?
0 – 1023
No
1024 – 2047
Yes
…
No
…
Yes
…
No](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-44-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Miscellanea
Modern Performance Problems
Excessive paging when doing full GC
Occasional long and unpredictable pauses
In a game, you usually have 16-33ms/frame
Steep performance decline when most of the
available memory is live
“We feel so strongly about ARC being the right
approach to memory management that we have
decided to deprecate Garbage Collection in OS
X.”
[Apple, WWDC 2012]](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-46-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Miscellanea
Apple Said WHAT?
“…as long as their applications will be running on
systems equipped with more than three times as
much RAM as required, the garbage collection is
a reasonable choice.”
[Hertz et al.]](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-47-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
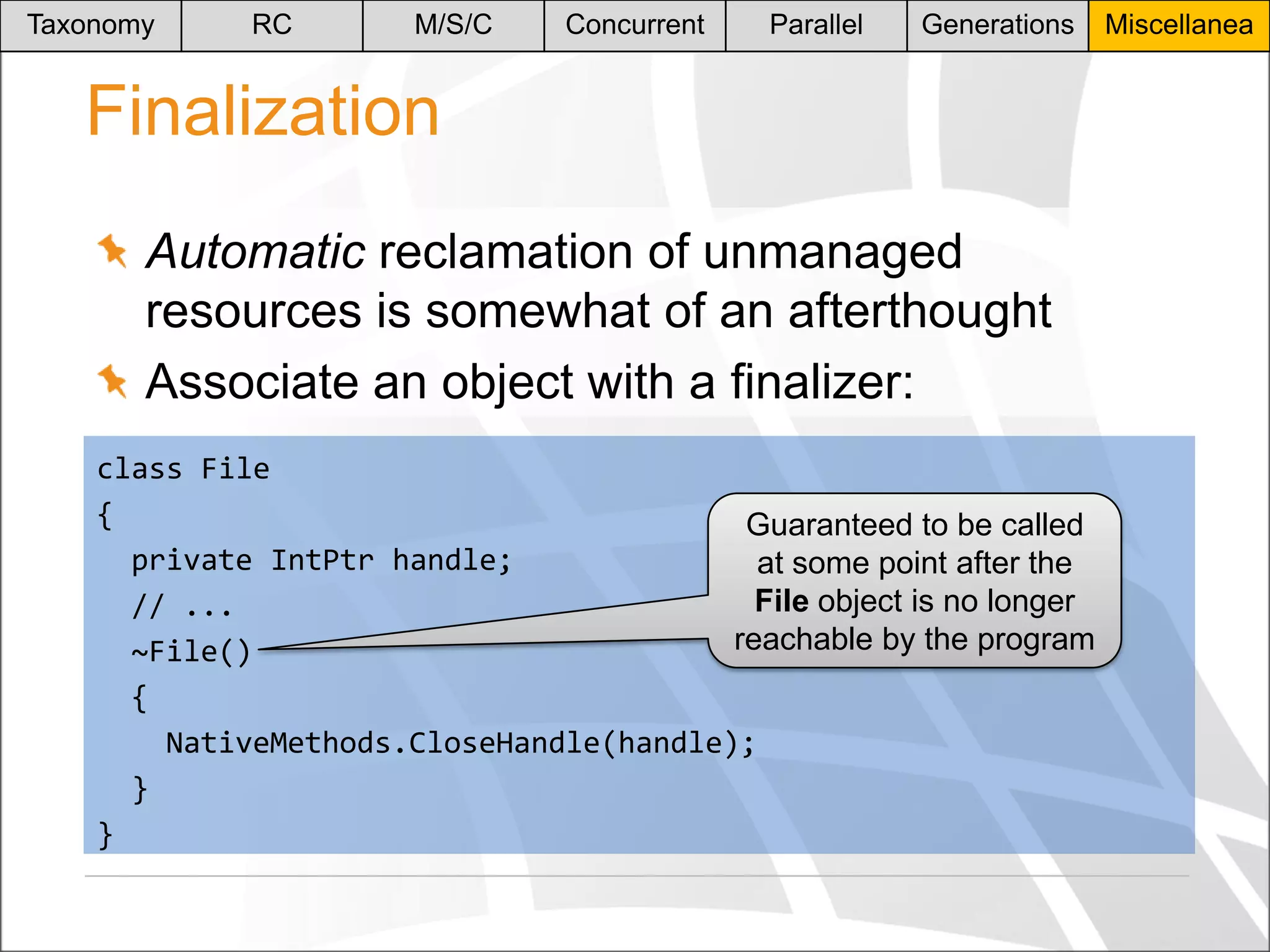
Finalization Performance
Performance issues with Java finalizers
[Weimer]
What happens here, assuming that the
Statement class has registered a finalizer?
for (int i = 0; i < 10000000; ++i) {
Statement st = db.prepare("SELECT 1");
st.close();
}
Miscellanea](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-54-2048.jpg)
![Taxonomy
RC
M/S/C
Concurrent
Parallel
Generations
Miscellanea
Summary
Is garbage collection a good idea?
Should we all switch to Java?
Should we all switch to static char mem[10000000];?
There is no clear cut answer
There is progress
There are tradeoffs](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-56-2048.jpg)

![References
Uniprocessor Garbage Collection Techniques [Wilson]
Mostly Concurrent Compaction for Mark-Sweep GC [Ossia et al.]
Concurrent Garbage Collection in Rubinius [Bussink]
Parallel Garbage Collection for Shared Memory Multiprocessors
[Flood et al.]
Qualifying the Performance of Garbage Collection vs. Explicit
Memory Management [Hertz et al.]
Why mobile web apps are slow [Crawford]
STOPLESS: A Real-Time Garbage Collector for Multiprocessors
[Pizlo et al.]
A real-time garbage collector with low overhead and consistent
utilization [Bacon et al.]
C4: The Continuously Concurrent Compacting Collector [Tene et
al.]
The Pauseless GC Algorithm [Click et al.]](https://image.slidesharecdn.com/moderngc-131104223548-phpapp02/75/A-History-of-Modern-Garbage-Collection-Techniques-58-2048.jpg)