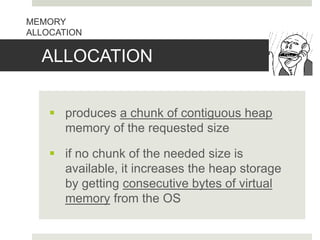
The document discusses heap memory management. It describes the heap as the portion of memory used for indefinitely stored data. A memory manager subsystem allocates and deallocates space in the heap. It keeps track of free space and serves as the interface between programs and the operating system. When allocating memory, the manager either uses available contiguous space or increases heap size from the OS. Deallocated space is returned to the free pool but memory is not returned to the OS when heap usage drops.

















![ Memory-leak Error
- failing to EVER delete data that cannot be
referenced
Dangling-pointer-dereference
[note: dangling pointers - pointers to storage that
has
been deallocated]
- referencing deleted data
MANUAL DEALLOCATION
REQUESTS](https://image.slidesharecdn.com/heap-161015052136/85/Heap-Management-24-320.jpg)


