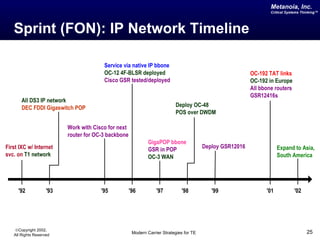
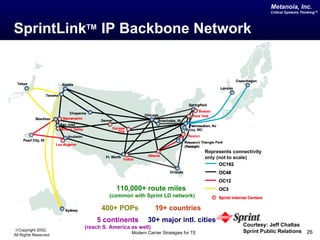
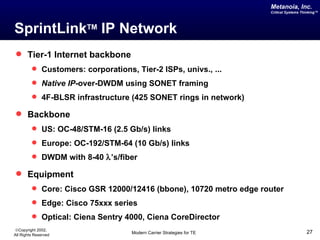
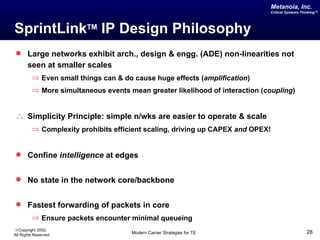
The document discusses critical system thinking in traffic engineering for service providers, emphasizing the importance of deploying an appropriate physical topology and mapping customer traffic flows. It traces the evolution of network strategies from the 1990s, highlighting the transition from ad-hoc traffic management to structured approaches with ATM and MPLS technologies. It also outlines the operational strategies of major carriers like Global Crossing and Sprint, focusing on scalability, network efficiency, and effective traffic engineering principles.
![Metanoia, Inc.
Critical Systems Thinking™
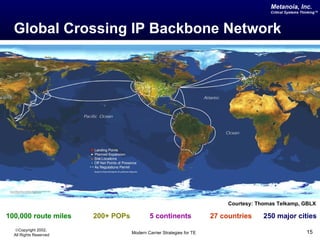
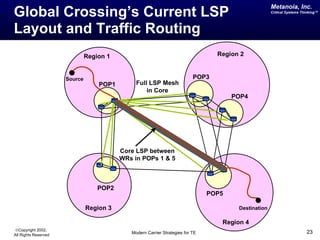
Global Crossing IP Network
OC-48c/STM-16c (2.5Gbps) IP backbone
Selected 10Gbps links operational (e.g. Atlantic)
Edge Equipment
Cisco 7500/7200 ESR, OSR
Juniper M10/20/40
Core Equipment
Cisco GSR 12000/12400
[12.0(17) SI]
Services offered
Internet access & Transit services
IP VPNs -- Layer 3 and Layer 2
MPLS and DiffServ deployed globally
©Copyright 2002,
All Rights Reserved Modern Carrier Strategies for TE 17](https://image.slidesharecdn.com/modern-carrier-strategies-for-tedrvishalsharma2002-11-28-120508074253-phpapp01/85/Modern-Carrier-Strategies-for-Traffic-Engineering-17-320.jpg)
![Metanoia, Inc.
TE in the US IP Network: Critical Systems Thinking™
Deployment Strategy
Decision to adopt MPLS for traffic engineering & VPNs
Y2000: 50+ POPs, 300 routers; Y2002: 200+ POPs
Initially, hierarchical MPLS system 2 levels of LSPs
Later, a flat MPLS LSP full mesh only between core routers
Started w/ 9 regions -- 10-50 LSRs/region ⇒ 100-2500 LSPs/region
Within regions: Routers fully-meshed
Across regions: Core routers fully-meshed
Intra-region traffic ~Mb/s to Gb/s, Inter-region traffic ~ Gb/s
Source [Xiao00]
©Copyright 2002,
All Rights Reserved Modern Carrier Strategies for TE 20](https://image.slidesharecdn.com/modern-carrier-strategies-for-tedrvishalsharma2002-11-28-120508074253-phpapp01/85/Modern-Carrier-Strategies-for-Traffic-Engineering-20-320.jpg)
![Metanoia, Inc.
Critical Systems Thinking™
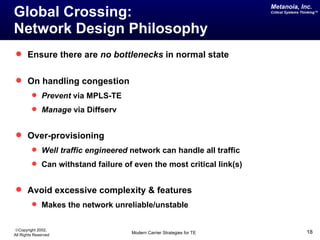
Sprint’s Approach to Monitoring
Backbone
Links
Backbone
Peering Links
Router
Probe
Access Access Access
Router Router Router
Analysis platform located at
Sprint ATL, Burlingame, CA Customers Customers Customers
Adapted from [Diot99]
©Copyright 2002,
All Rights Reserved Modern Carrier Strategies for TE 31](https://image.slidesharecdn.com/modern-carrier-strategies-for-tedrvishalsharma2002-11-28-120508074253-phpapp01/85/Modern-Carrier-Strategies-for-Traffic-Engineering-31-320.jpg)
![Metanoia, Inc.
Critical Systems Thinking™
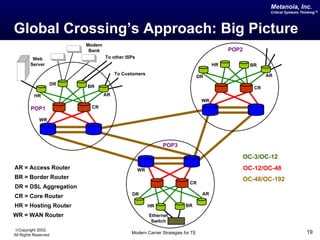
A Peek at a Row of a Traffic Matrix
To Backbone
Peer 2
Peer 1
ISP
Web 2
Web 1
Sprint POP under study
Distribution of aggregate access
traffic across other POPs in the Sprint
backbone
Adapted from [Bhattacharya02]
Summary of Data Collected
©Copyright 2002,
All Rights Reserved Modern Carrier Strategies for TE 34](https://image.slidesharecdn.com/modern-carrier-strategies-for-tedrvishalsharma2002-11-28-120508074253-phpapp01/85/Modern-Carrier-Strategies-for-Traffic-Engineering-34-320.jpg)