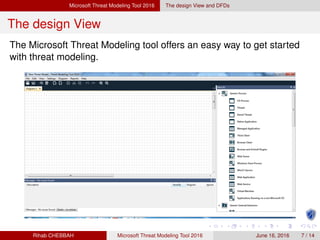
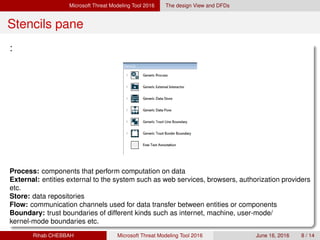
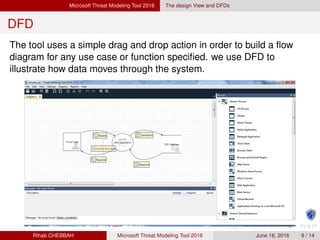
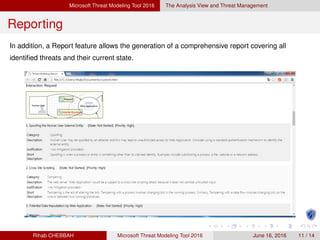
The document discusses the Microsoft Threat Modeling Tool 2016. It provides an introduction to threat modeling and the Microsoft Security Development Lifecycle approach. It then describes the tool, which uses data flow diagrams and the STRIDE threat classification model to graphically identify processes, data flows, and potential threats in an application. Developers can use the tool to communicate security designs, analyze them for issues, and manage mitigations.