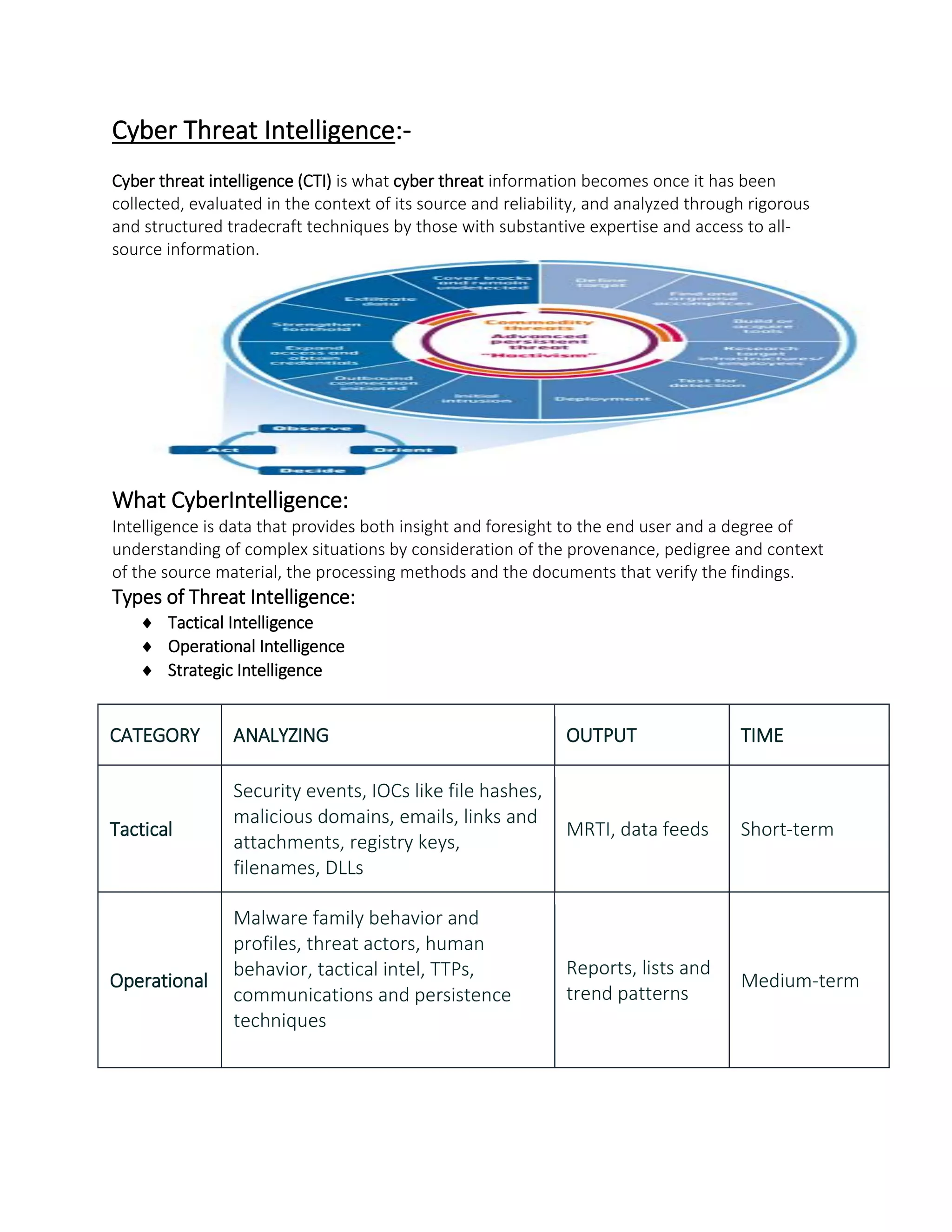
Cyber threat intelligence (CTI) involves collecting, evaluating, and analyzing cyber threat information using expertise and all-source information to provide insight and understanding of complex cyber situations. CTI can include tactical, operational, and strategic intelligence about security events, indicators of compromise, malware behavior, threat actors, and mapping online threats to geopolitical events over short, medium, and long timeframes. Implementing CTI enables organizations to prepare for and respond to existing and unknown threats through evidence-based knowledge and actionable advice beyond just reactive defense measures.