Embed presentation
Downloaded 485 times
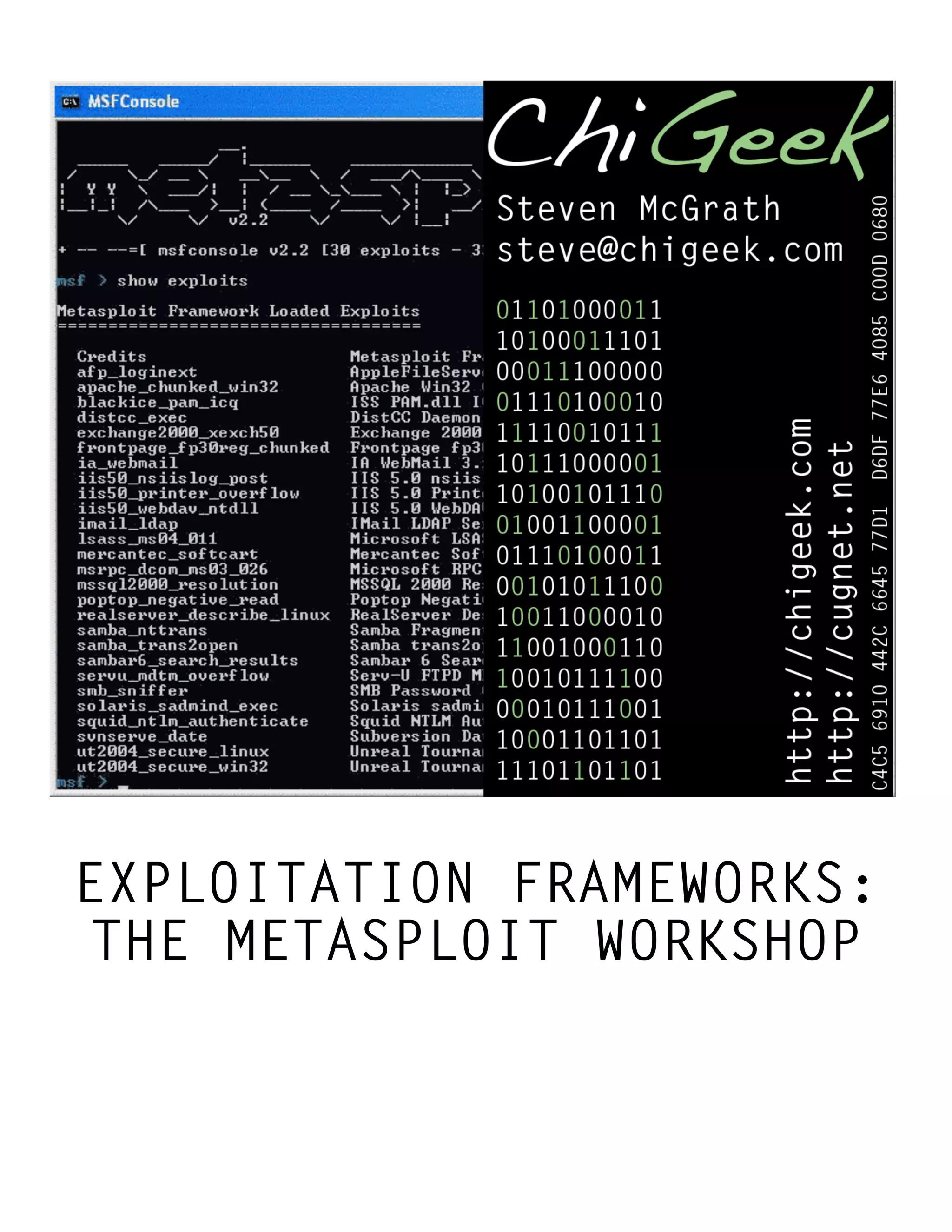



































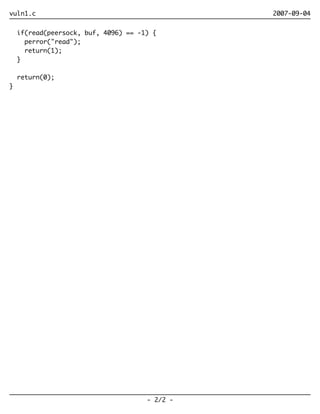
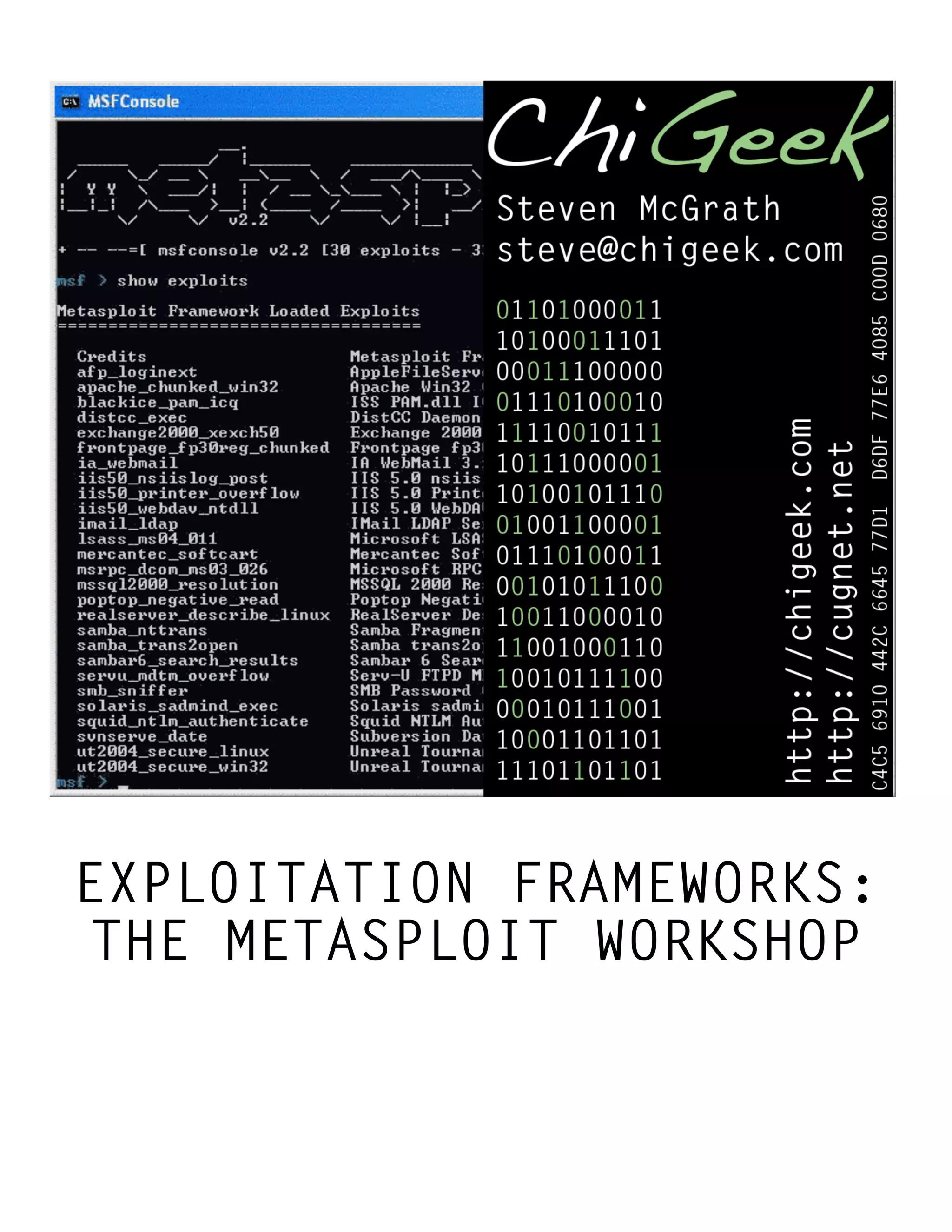
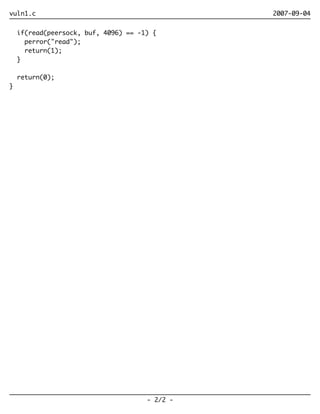
This document provides an overview of the Metasploit exploitation framework. It discusses Metasploit's structure and components, including modules, plugins, Rex library, and Framework Core classes. It describes the main interfaces for using Metasploit, including msfconsole, msfcli, msfweb, and msfgui. It also covers using Metasploit as a user, developer, and expert, including automation, Metasploitable, and the powerful Metasploit payload known as Metapreter.