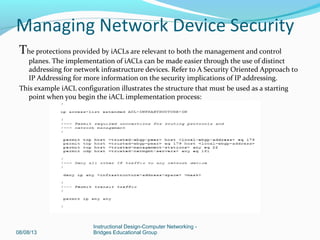
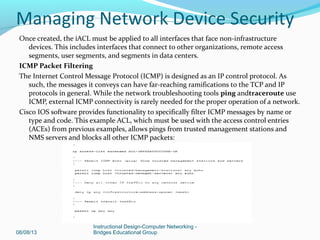
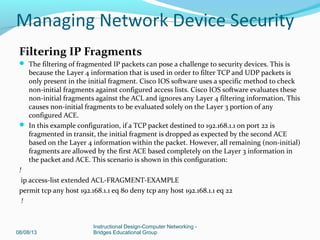
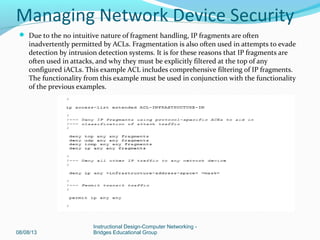
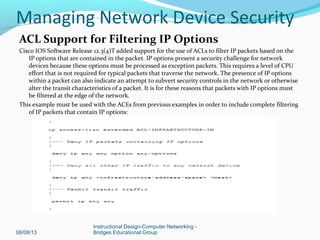
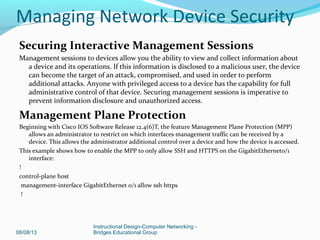
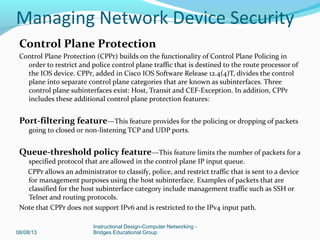
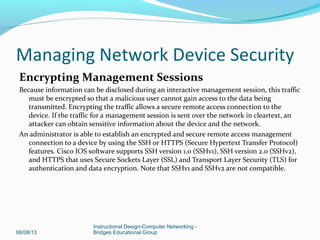
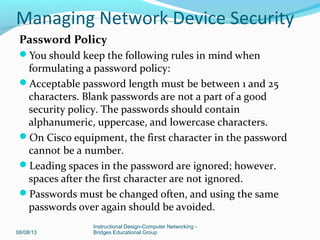
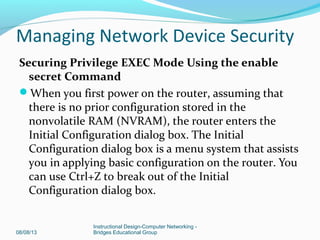
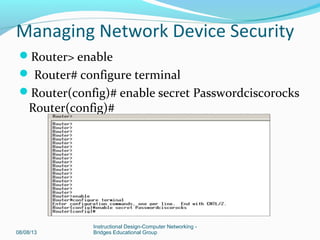
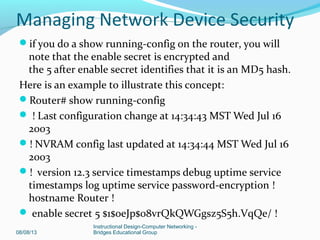
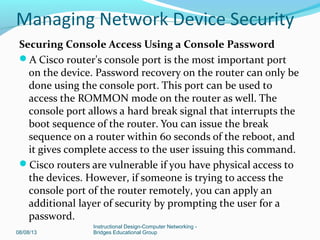
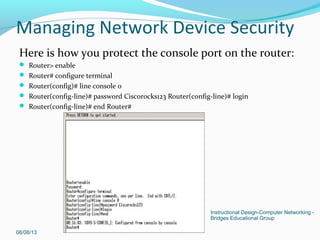
This document provides instructions for securing network devices, including securing administrative access, implementing device hardening, and implementing traffic filtering. It discusses securing access to the device through the console port, VTY lines, and auxiliary port by configuring login passwords. It also recommends encrypting all passwords, configuring session timeouts, implementing access levels for administrators, and configuring warning banners. For the management plane, it suggests securing protocols like SNMP, SSH, and disabling unneeded services. Device hardening includes securing the management, control, and data planes through password policies and encryption. Traffic filtering can be implemented through access control lists.


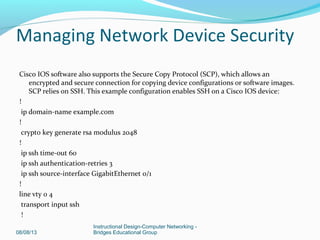
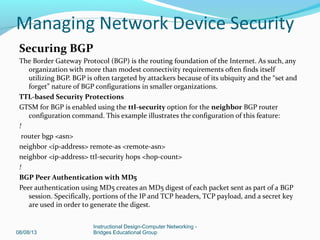
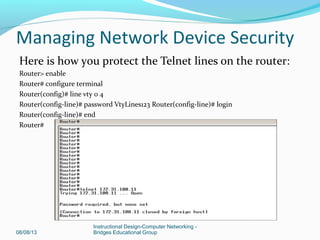
![Securing VTY Access Using a Telnet Password
By default, all Cisco routers support up to five
simultaneous Telnet sessions, and by default, no passwords
are assigned to these Telnet or VTY lines. There is built-in
security on the VTY lines that mandates the use of
passwords to access the router via a Telnet session. If a
Telnet session is initiated to a router that does not have a
password assigned to the VTY lines, the following message
appears on the screen:
telnet 172.31.100.11 Trying... Connected to 172.31.100.11
Escape character is '^]'. Password required, but not set
Connection closed by remote host
08/08/13
Instructional Design-Computer Networking -
Bridges Educational Group
Managing Network Device Security](https://image.slidesharecdn.com/lesson5slide1-130807201124-phpapp01/85/Managing-Network-Device-Security-13-320.jpg)
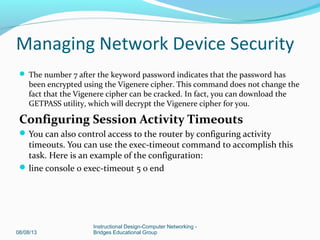
![EXEC Timeout
In order to set the interval that the EXEC command interpreter waits for user input before
it terminates a session, issue the exec-timeout line configuration command. The exec-
timeout command must be used in order to logout sessions on vty or tty lines that are
left idle. By default, sessions are disconnected after 10 minutes of inactivity.
!
line con 0
exec-timeout <minutes> [seconds]
line vty 0 4
exec-timeout <minutes> [seconds]
!
Keepalives for TCP Sessions
The service tcp-keepalive-in and service tcp-keepalive-out global configuration
commands enable a device to send TCP keepalives for TCP sessions. This configuration
must be used in order to enable TCP keepalives on inbound connections to the device
and outbound connections from the device. This ensures that the device on the remote
end of the connection is still accessible and that half-open or orphaned connections are
removed from the local Cisco IOS device.
!
service tcp-keepalive-in service tcp-keepalive-out
!
08/08/13
Instructional Design-Computer Networking -
Bridges Educational Group
Managing Network Device Security](https://image.slidesharecdn.com/lesson5slide1-130807201124-phpapp01/85/Managing-Network-Device-Security-32-320.jpg)