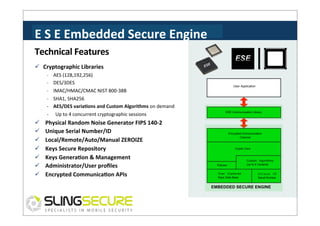
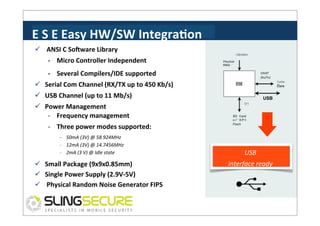
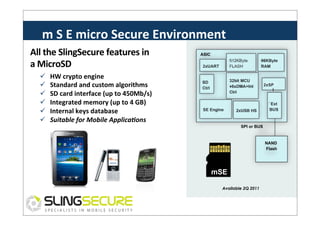
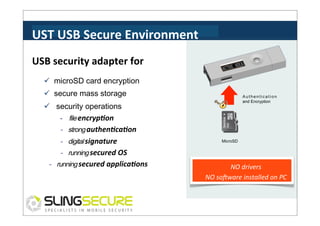
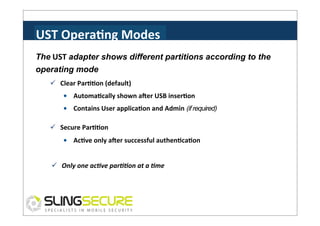
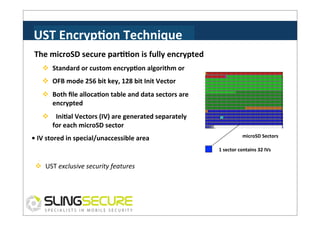
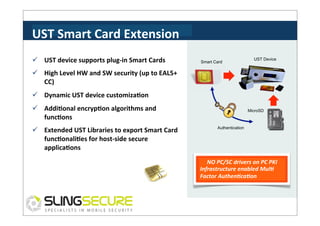
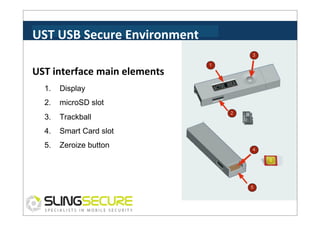
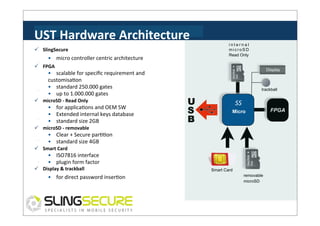
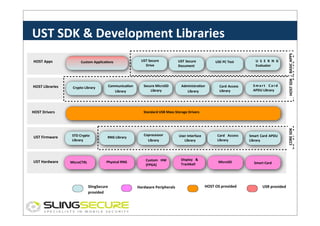
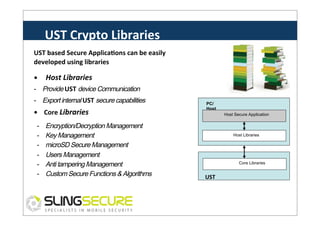
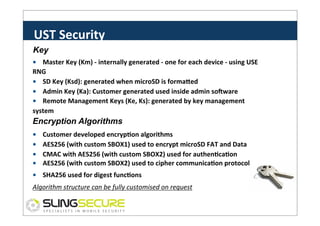
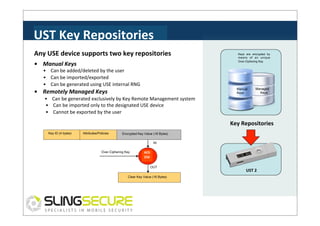
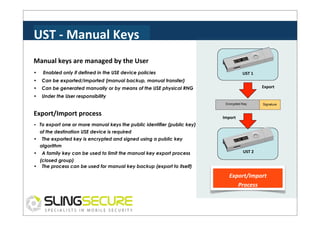
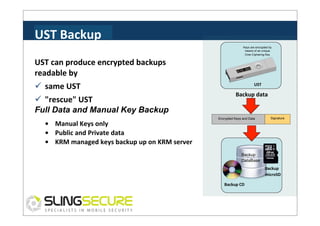
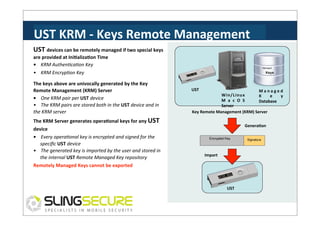
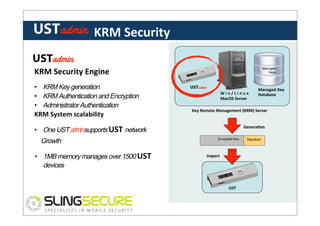
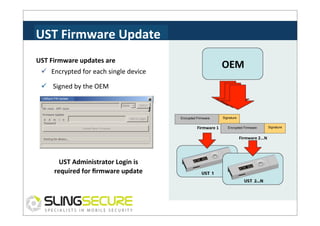
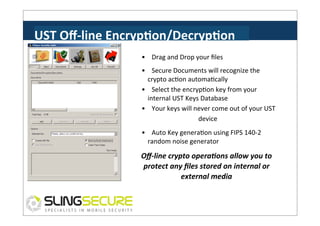
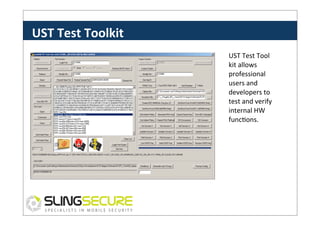
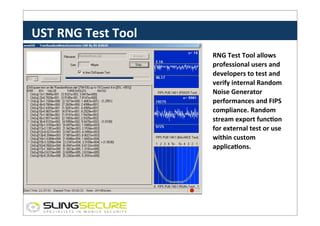
Slingsecure S.R.L. develops hardware and software solutions for mobile and fixed network security, featuring products like the USB Security Token and Micro Secure Environment. Their technology employs advanced encryption methods, secure key management, and diverse application functionalities, supporting integration with various systems. The UST USB device offers features such as secure data storage, encryption, and remote management capabilities, aiming to provide robust security for sensitive information.