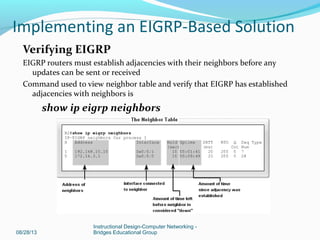
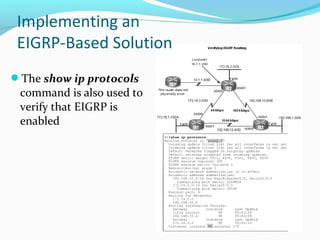
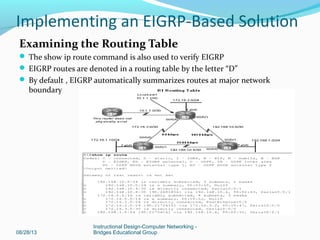
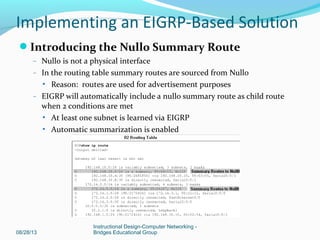
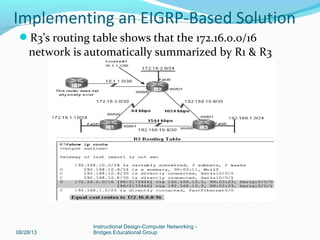
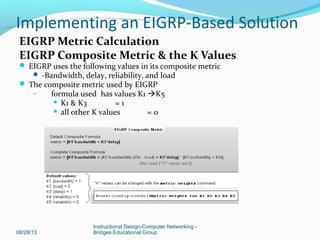
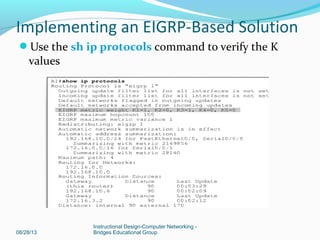
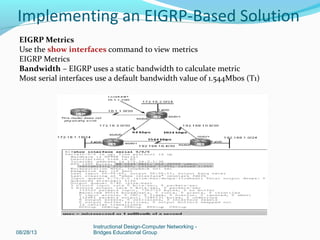
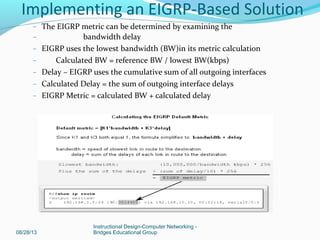
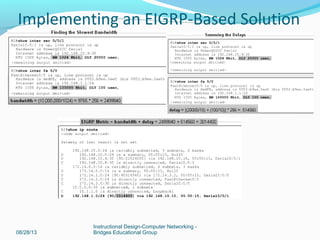
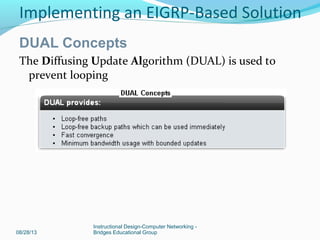
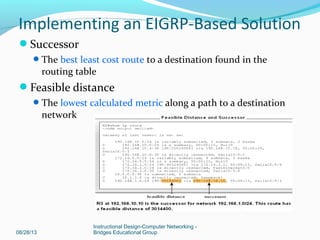
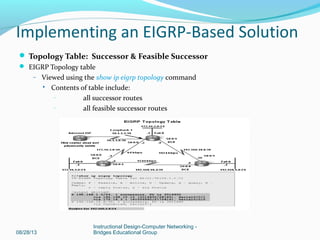
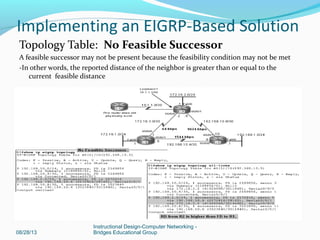
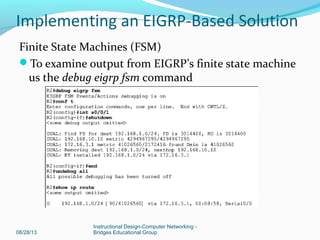
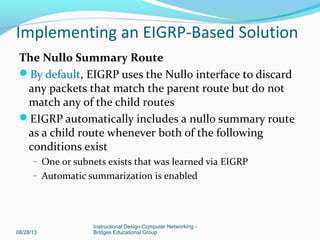
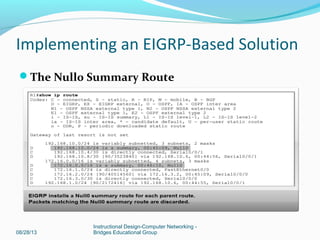
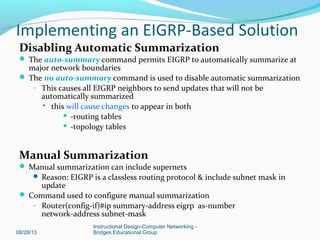
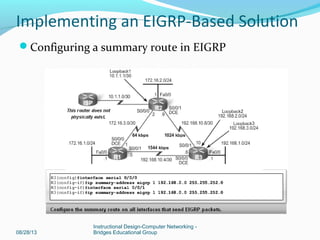
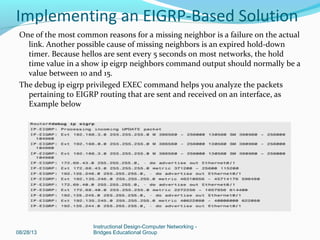
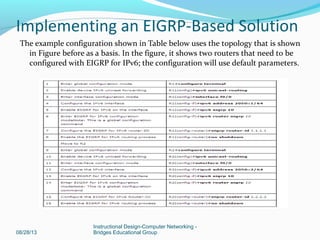
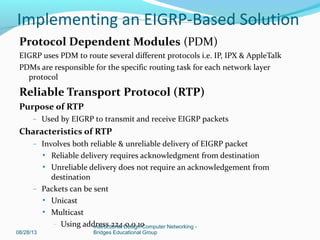
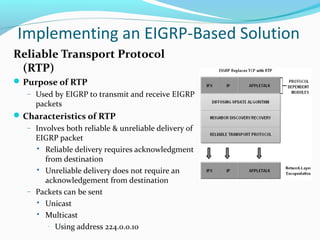
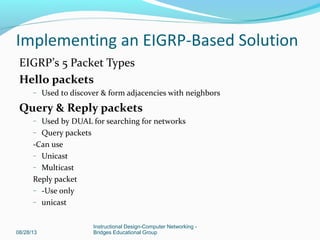
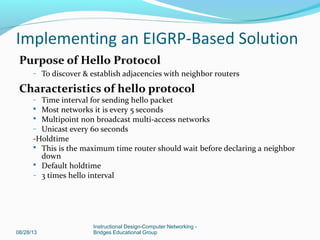
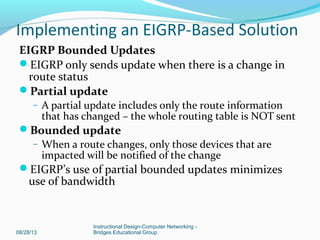
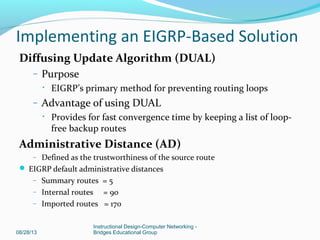
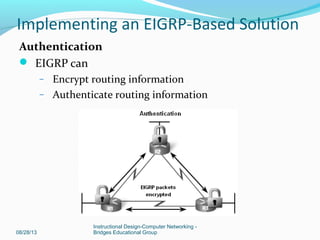
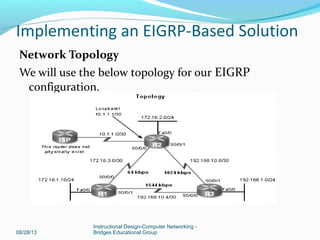
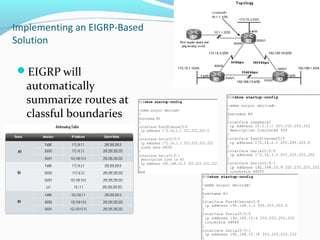
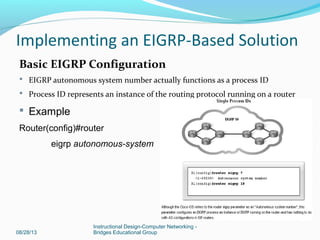
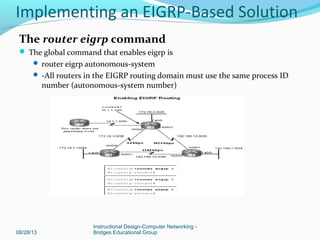
The document discusses implementing an EIGRP-based solution for computer networking. It covers topics such as EIGRP configuration, metrics, neighbor discovery, route summarization, and troubleshooting. Specific configuration commands are provided for enabling EIGRP routing, verifying neighbor relationships, and modifying interface metrics. The routing protocol's use of DUAL, finite state machines, and automatic summarization are also explained.

![08/28/13
Instructional Design-Computer Networking -
Bridges Educational Group
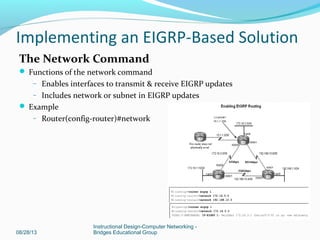
The network Command with a Wildcard Mask
-This option is used when you want to configure EIGRP
to advertise specific subnets
-Example
Router(config-router)#network network-address
[wildcard-mask]
Implementing an EIGRP-Based Solution](https://image.slidesharecdn.com/implementinganeigrpbasedsolution-130828081151-phpapp01/85/Implementing-an-EGIRP-Based-Solution-20-320.jpg)