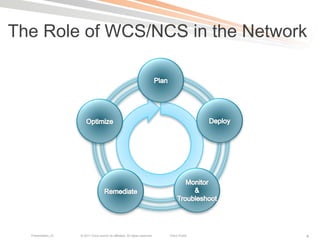
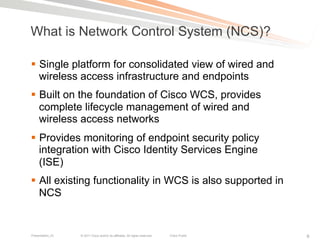
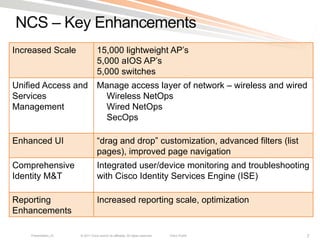
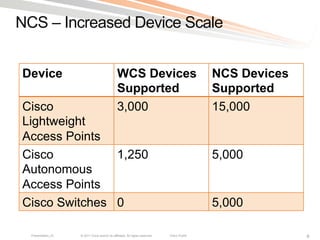
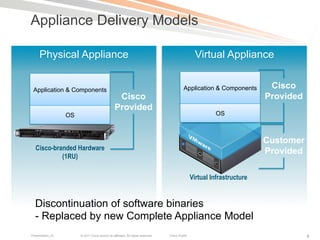
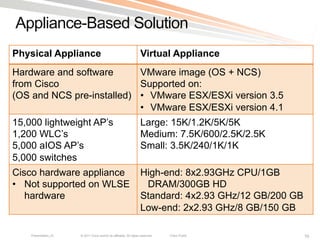
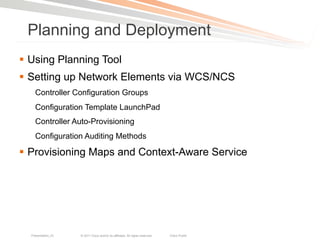
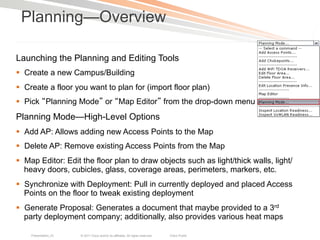
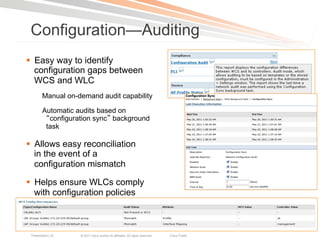
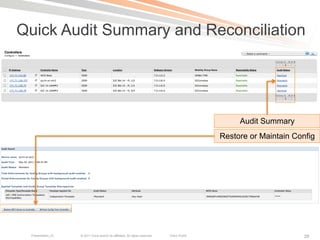
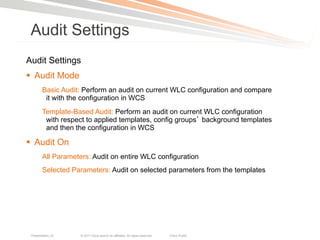
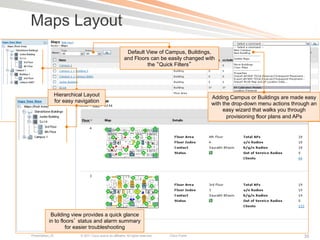
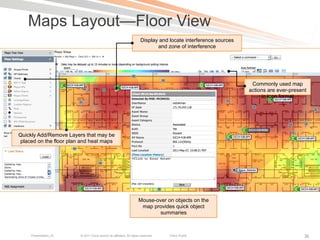
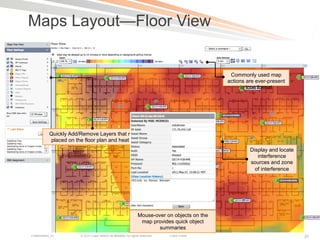
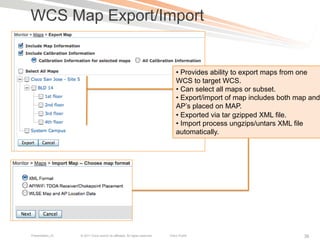
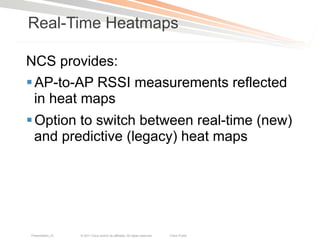
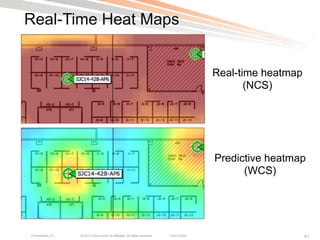
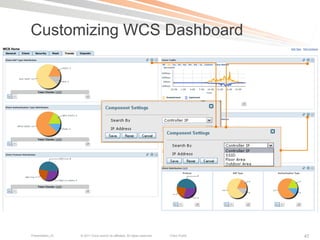
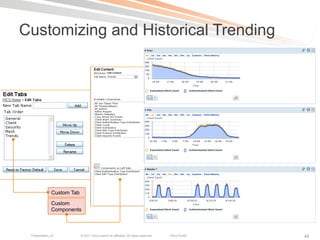
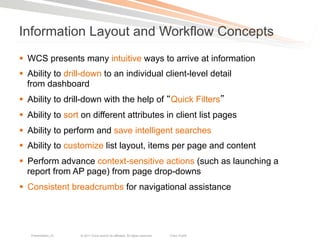
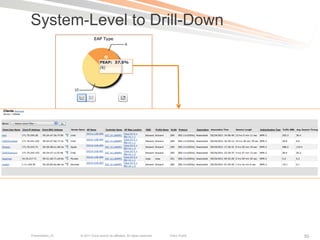
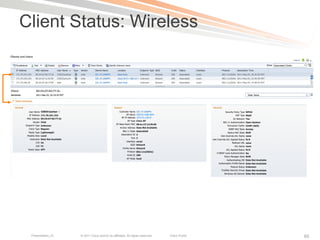
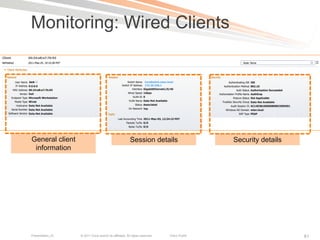
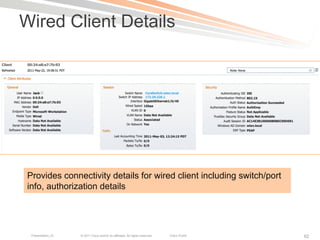
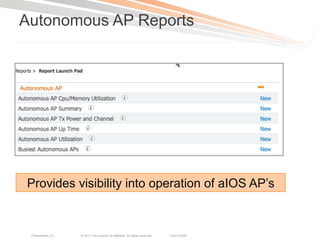
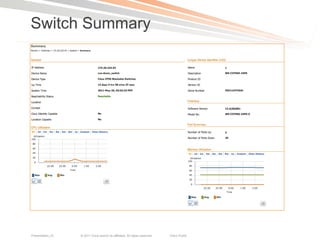
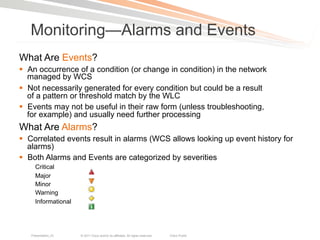
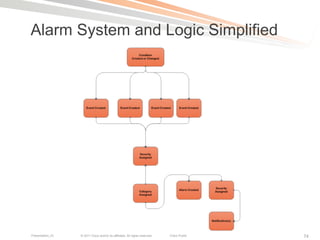
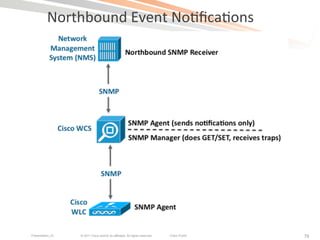
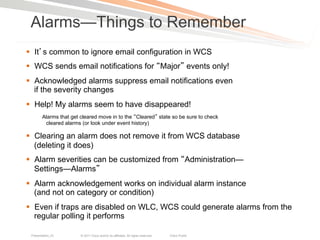
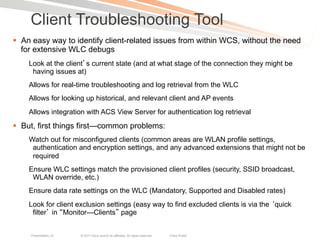
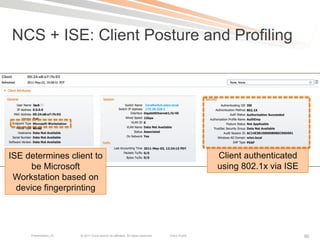
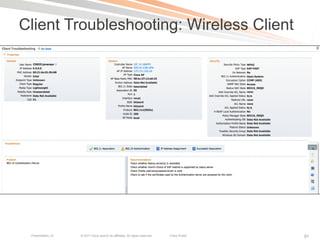
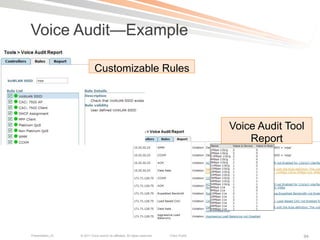
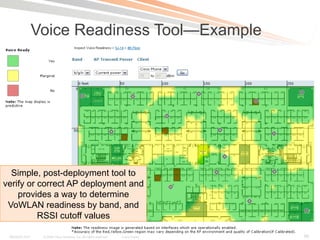
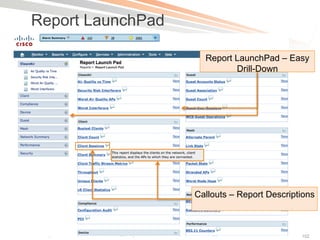
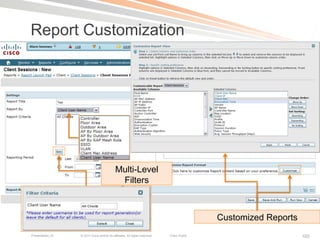
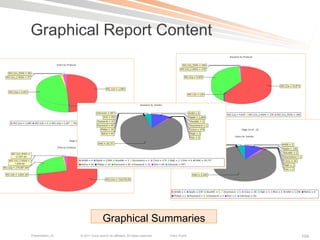
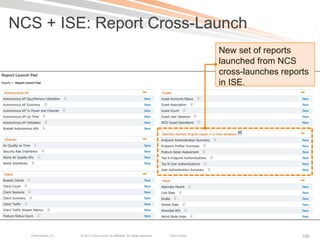
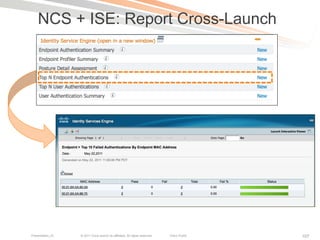
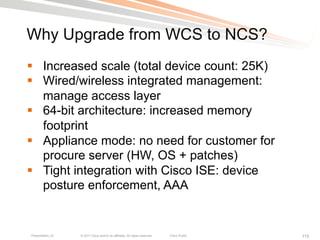
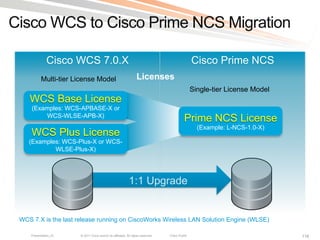
The document outlines the management of enterprise WLAN using Cisco's Wireless Control System (WCS) and its successor, the Cisco Prime Network Control System (NCS), highlighting their roles, planning, deployment, monitoring, and troubleshooting features. It details enhancements in NCS, such as increased device support and improved user interface, while providing guidance on configuration and reporting tools. The session aims to demonstrate practical tasks and best practices related to these systems.