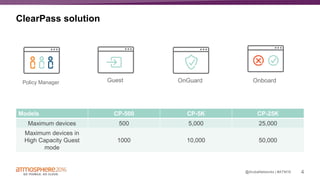
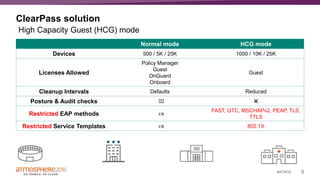
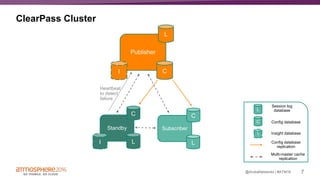
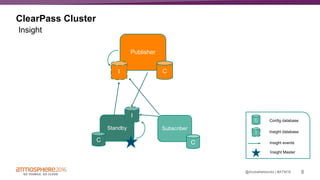
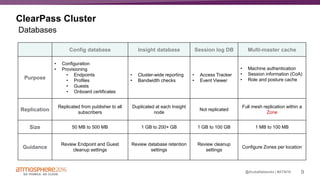
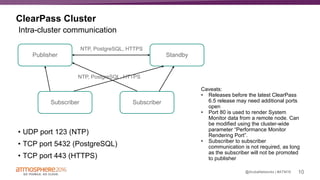
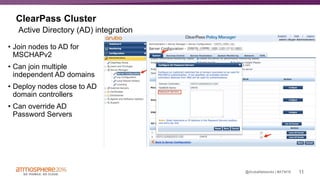
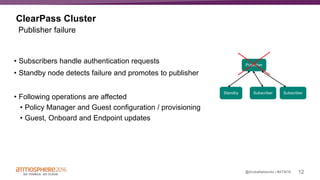
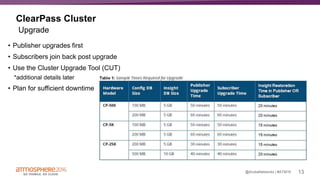
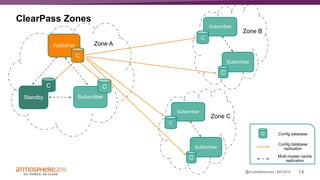
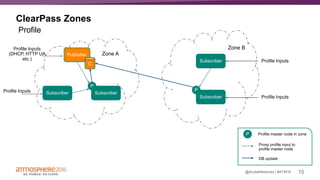
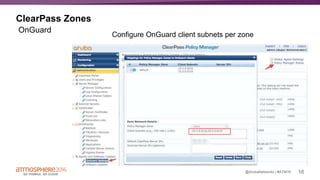
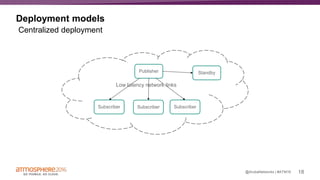
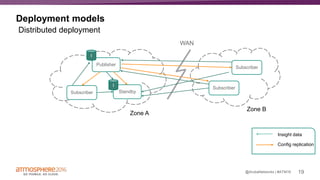
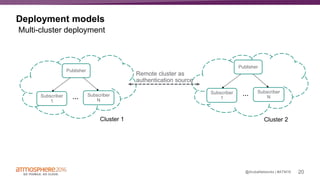
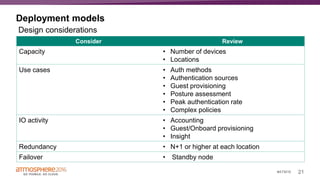
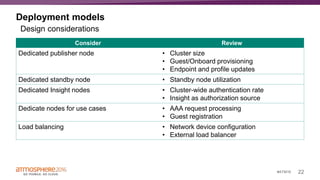
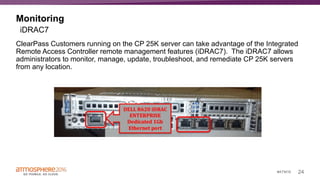
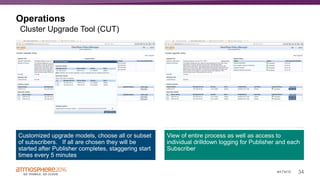
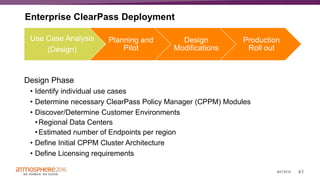
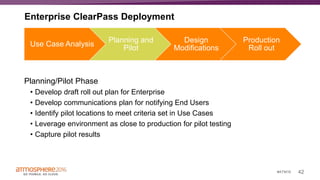
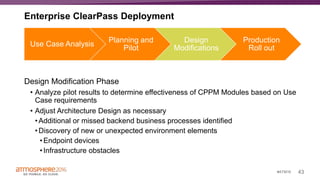
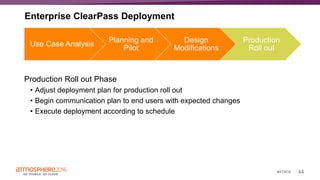
The document outlines a comprehensive approach to deploying large-scale, distributed access management using Aruba ClearPass, discussing its solutions, cluster configurations, deployment models, and operational details. It emphasizes the importance of planning, monitoring, and tuning in order to manage authentication and authorization processes effectively. Key components addressed include infrastructure setup, integration with Active Directory, and the use of advanced monitoring tools like ClearPass Insight.