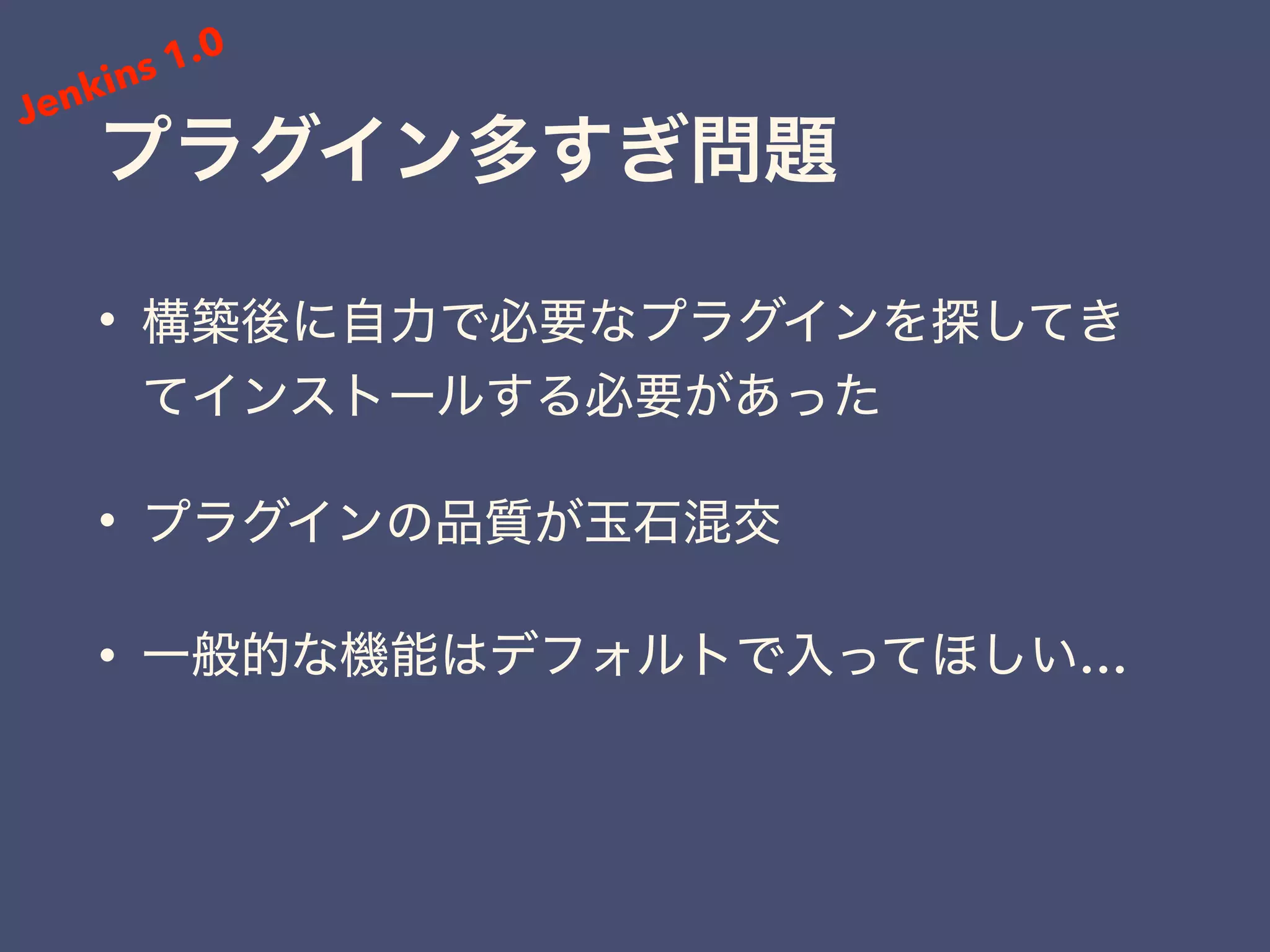
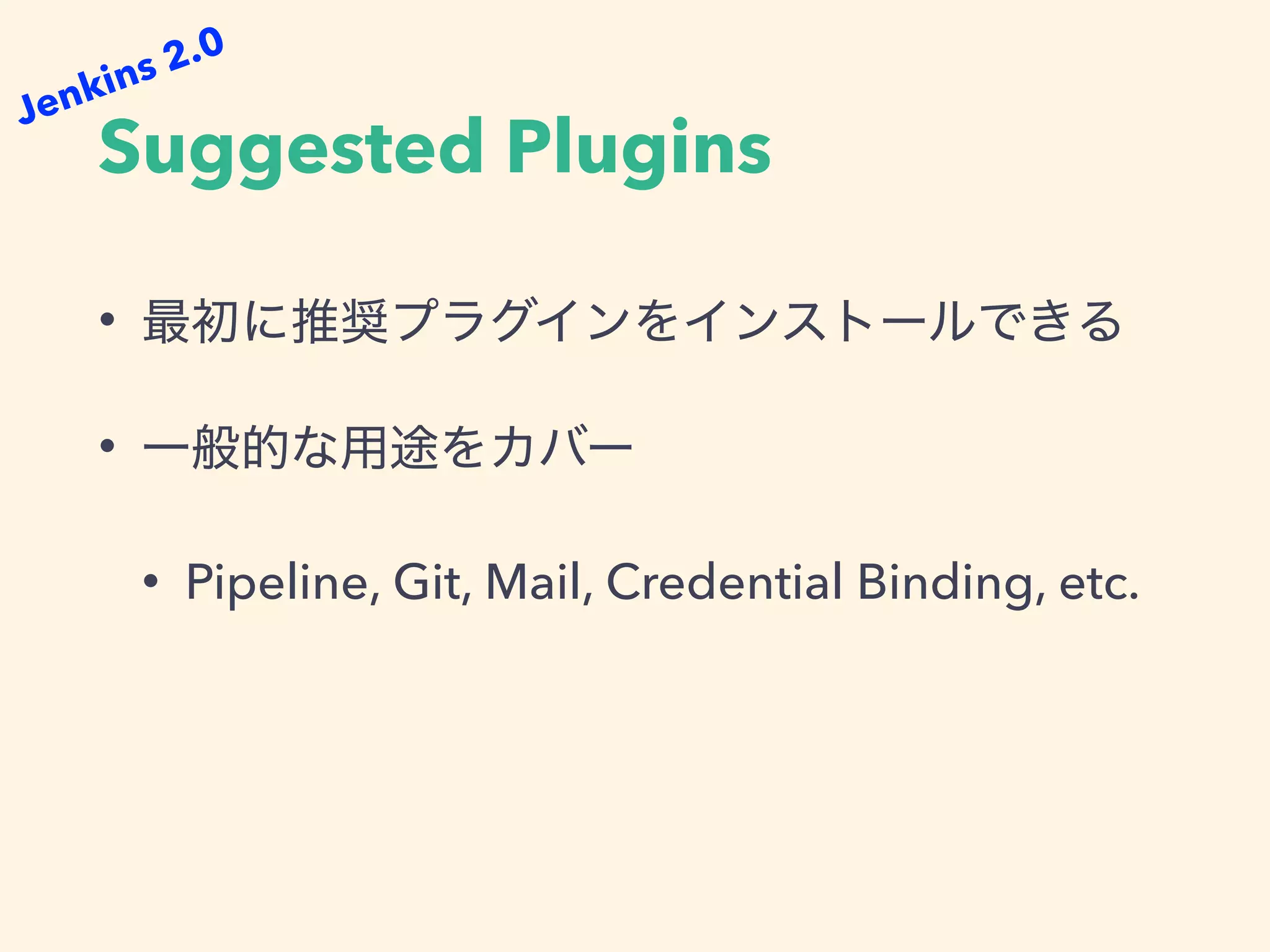
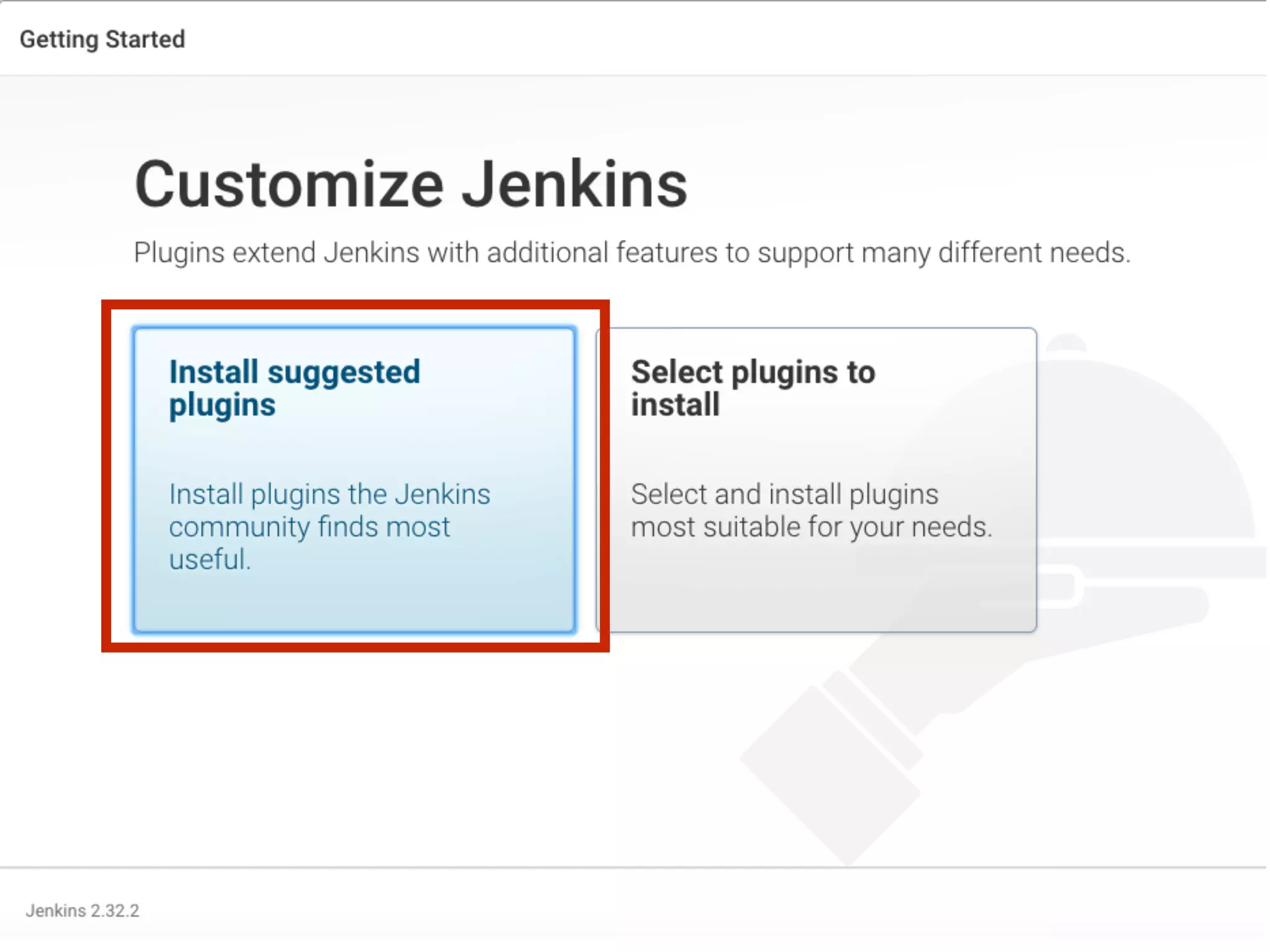
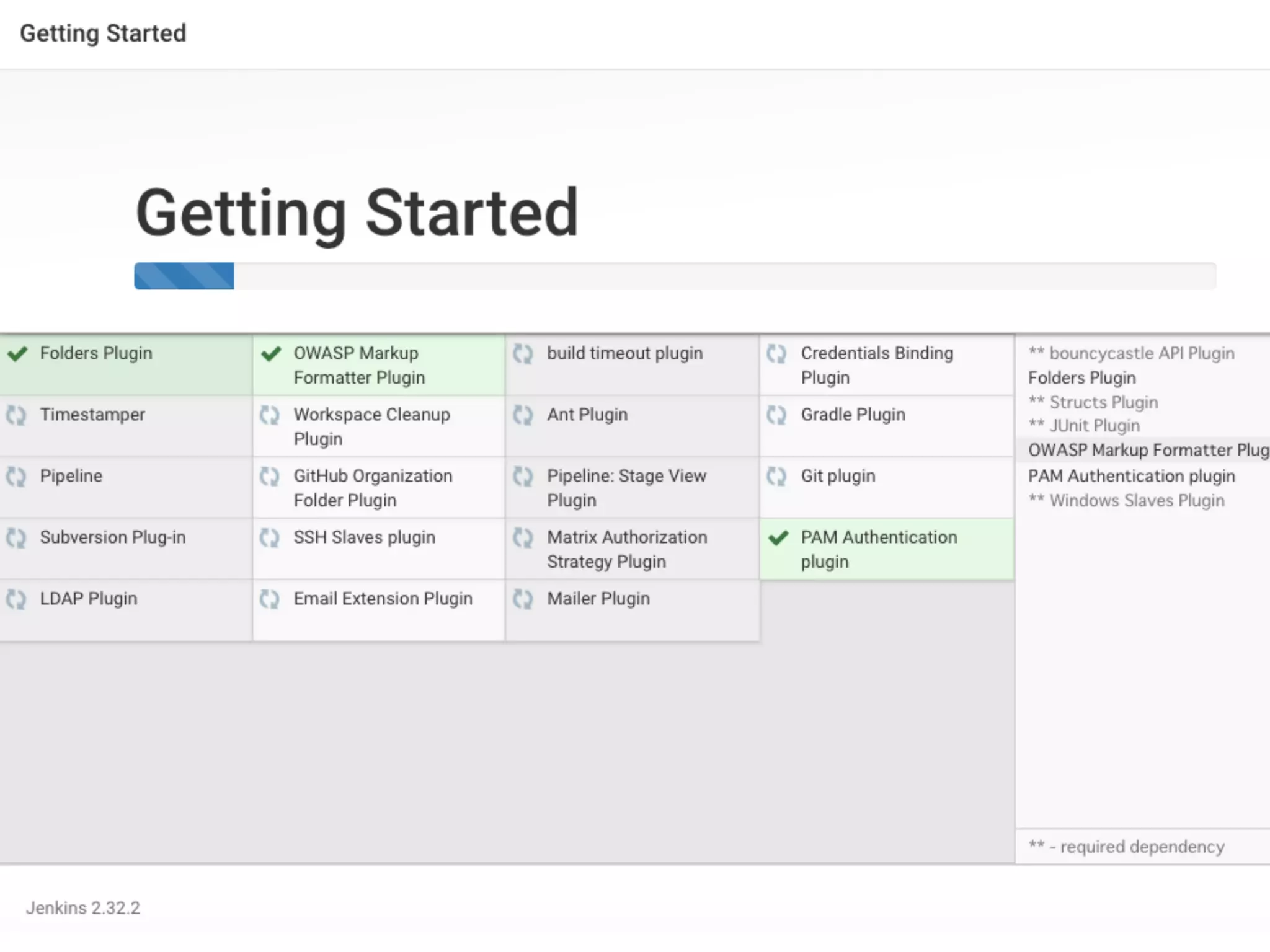
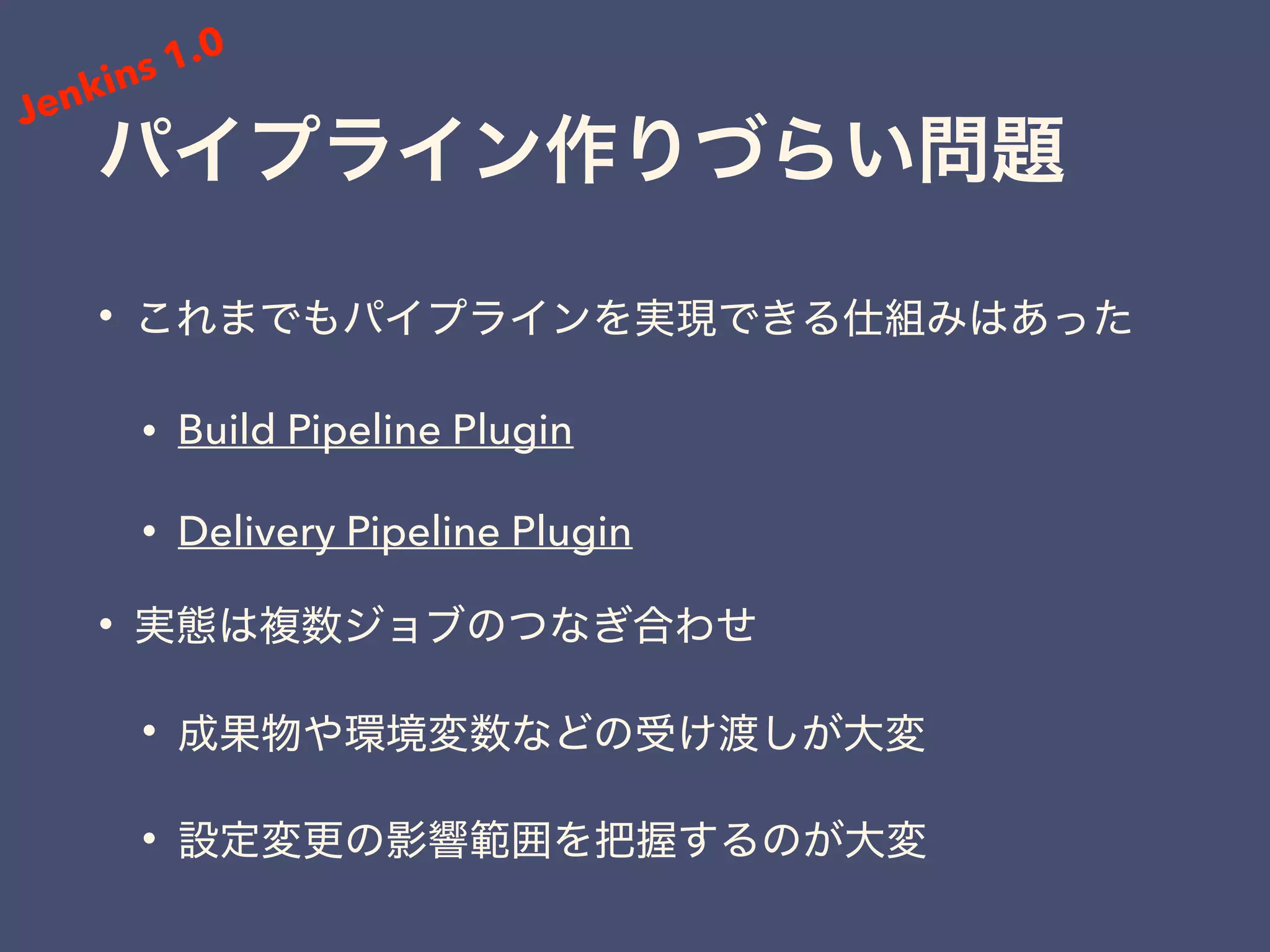
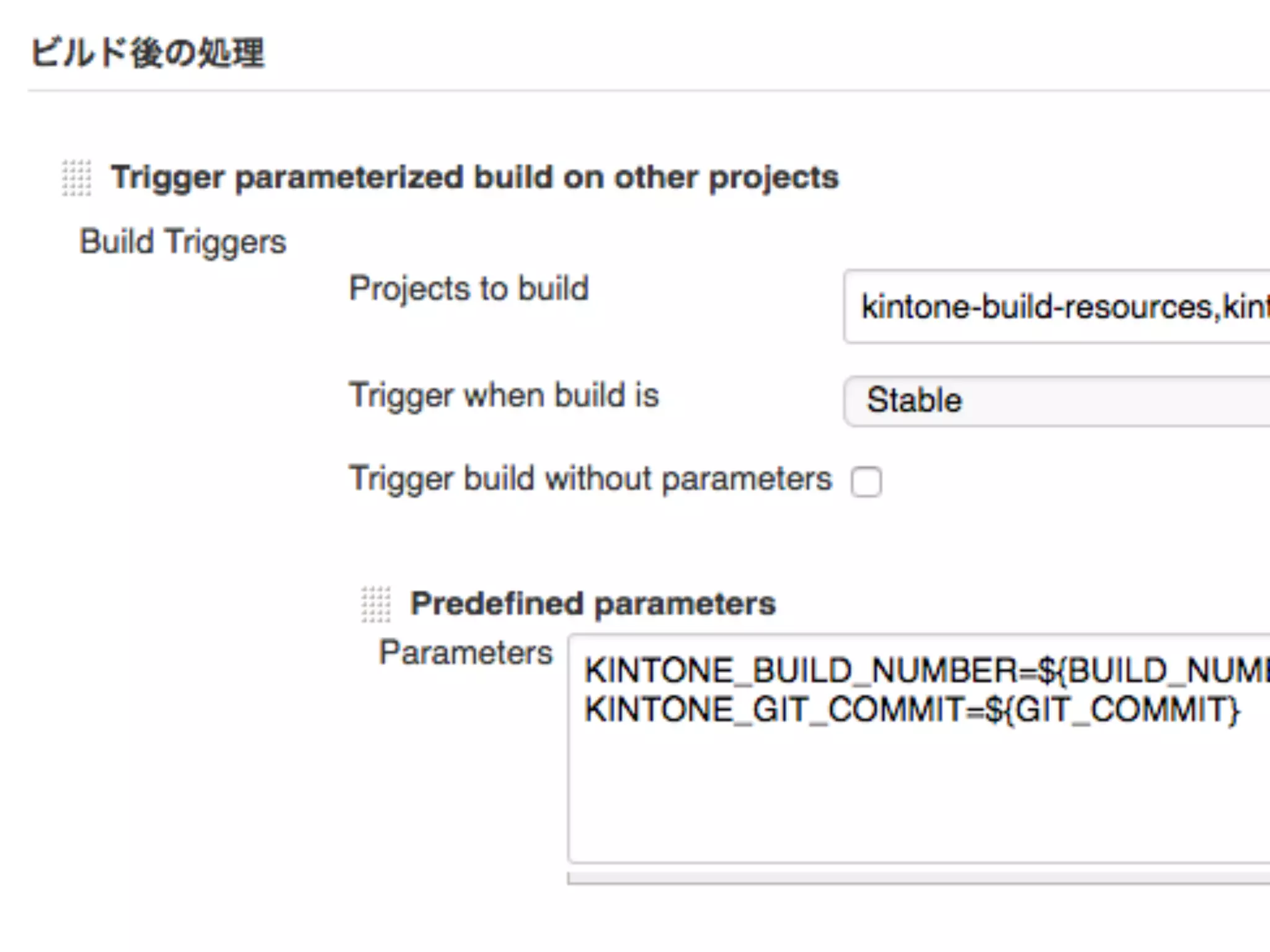
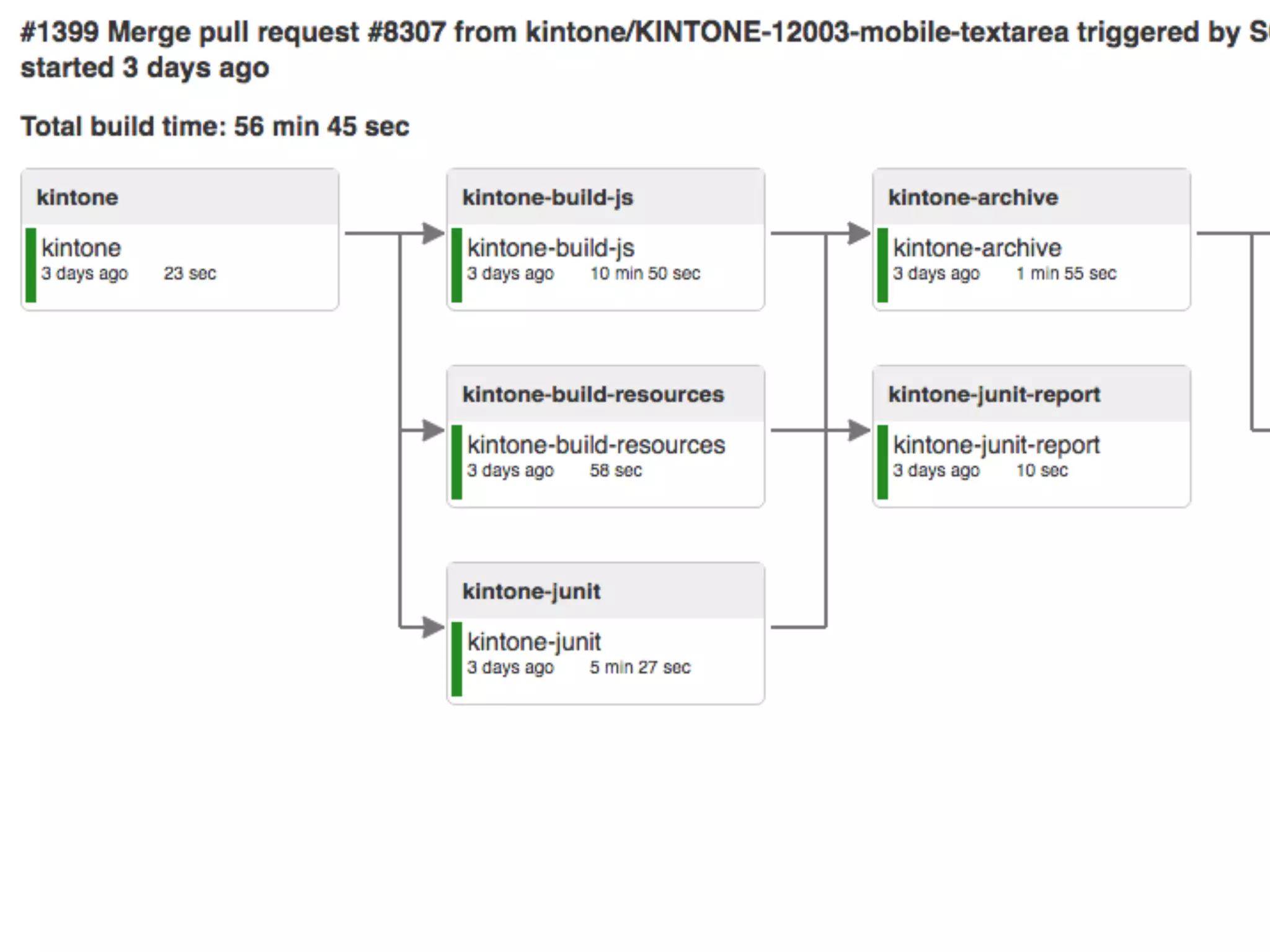
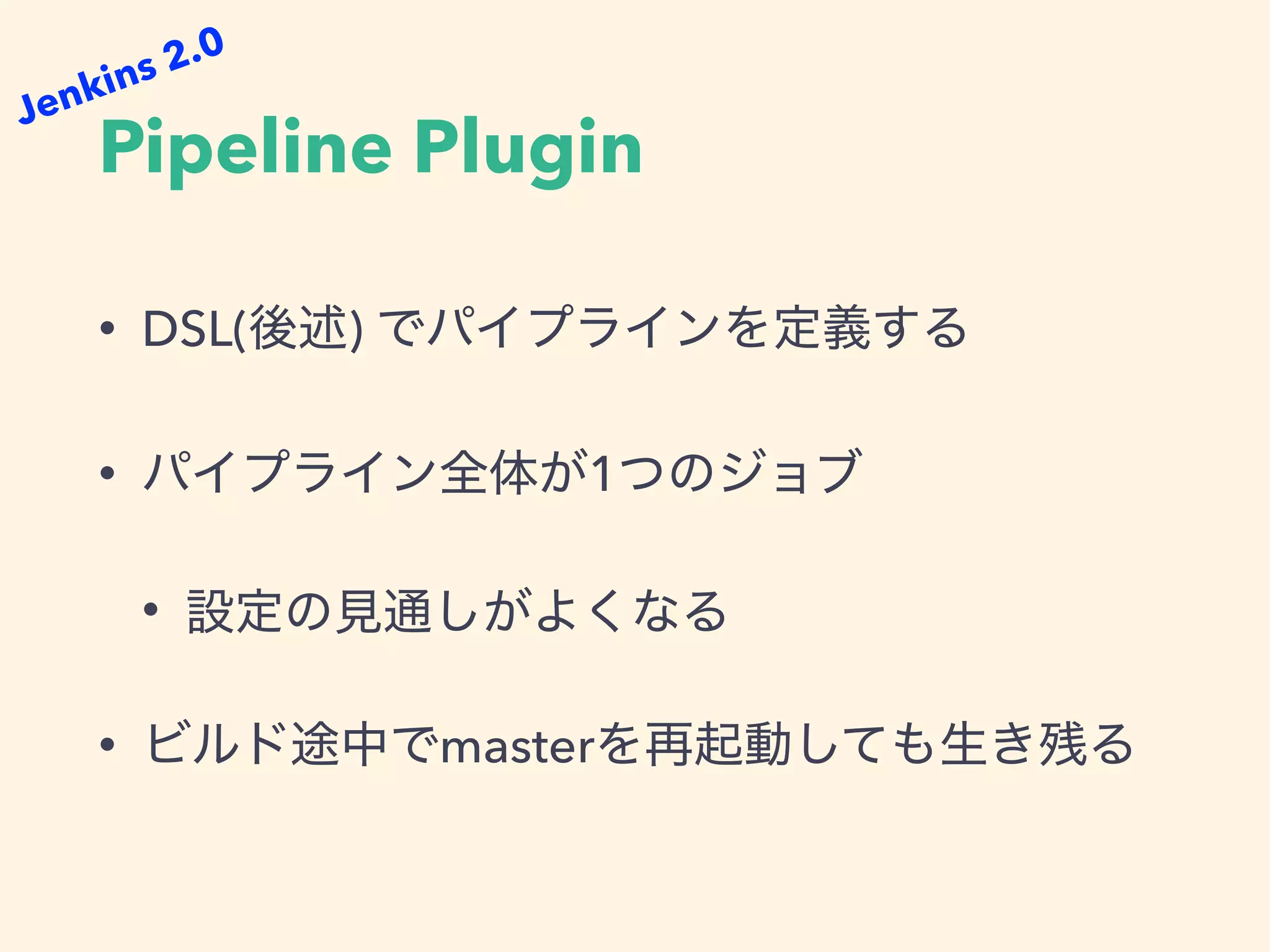
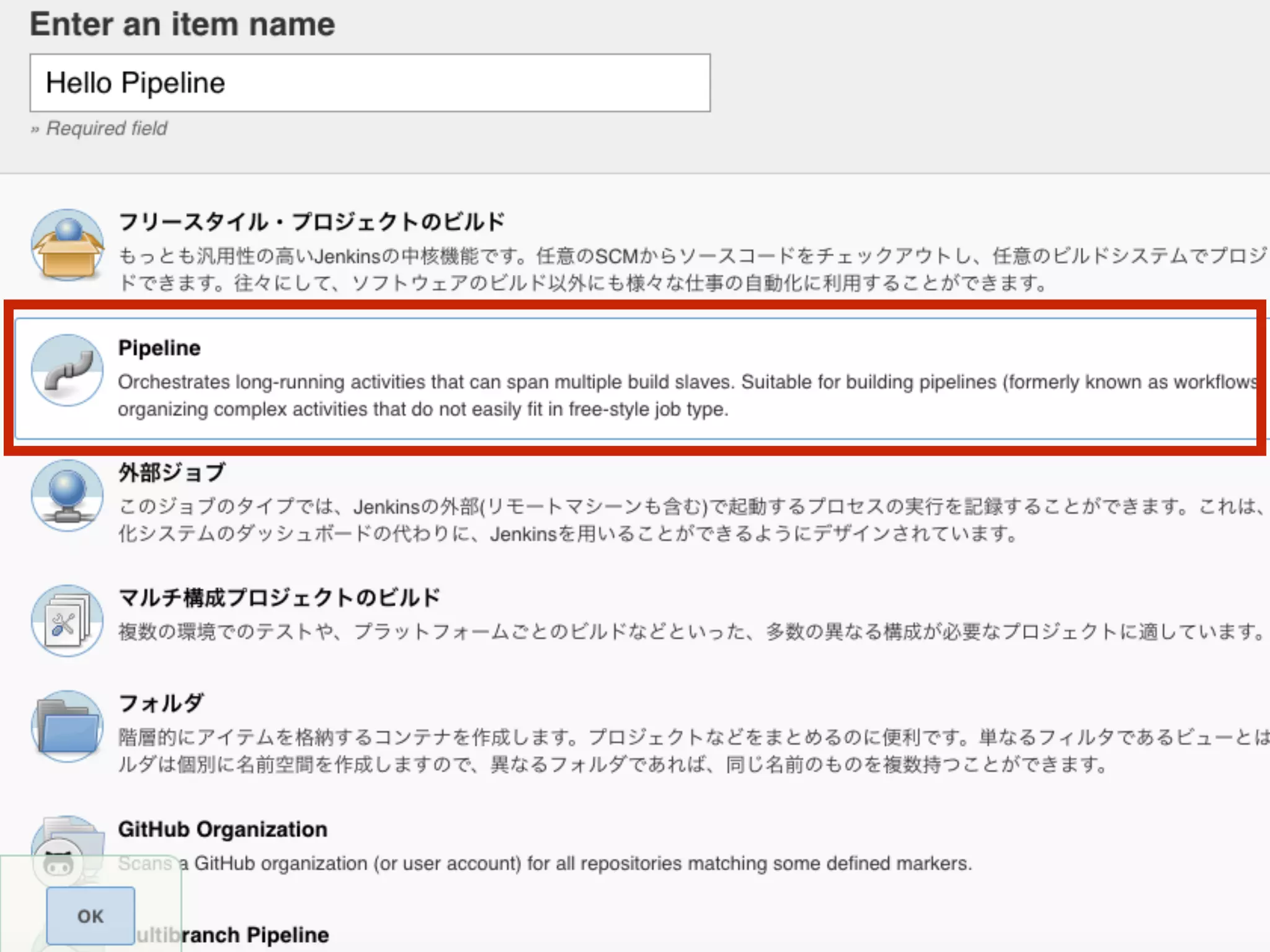
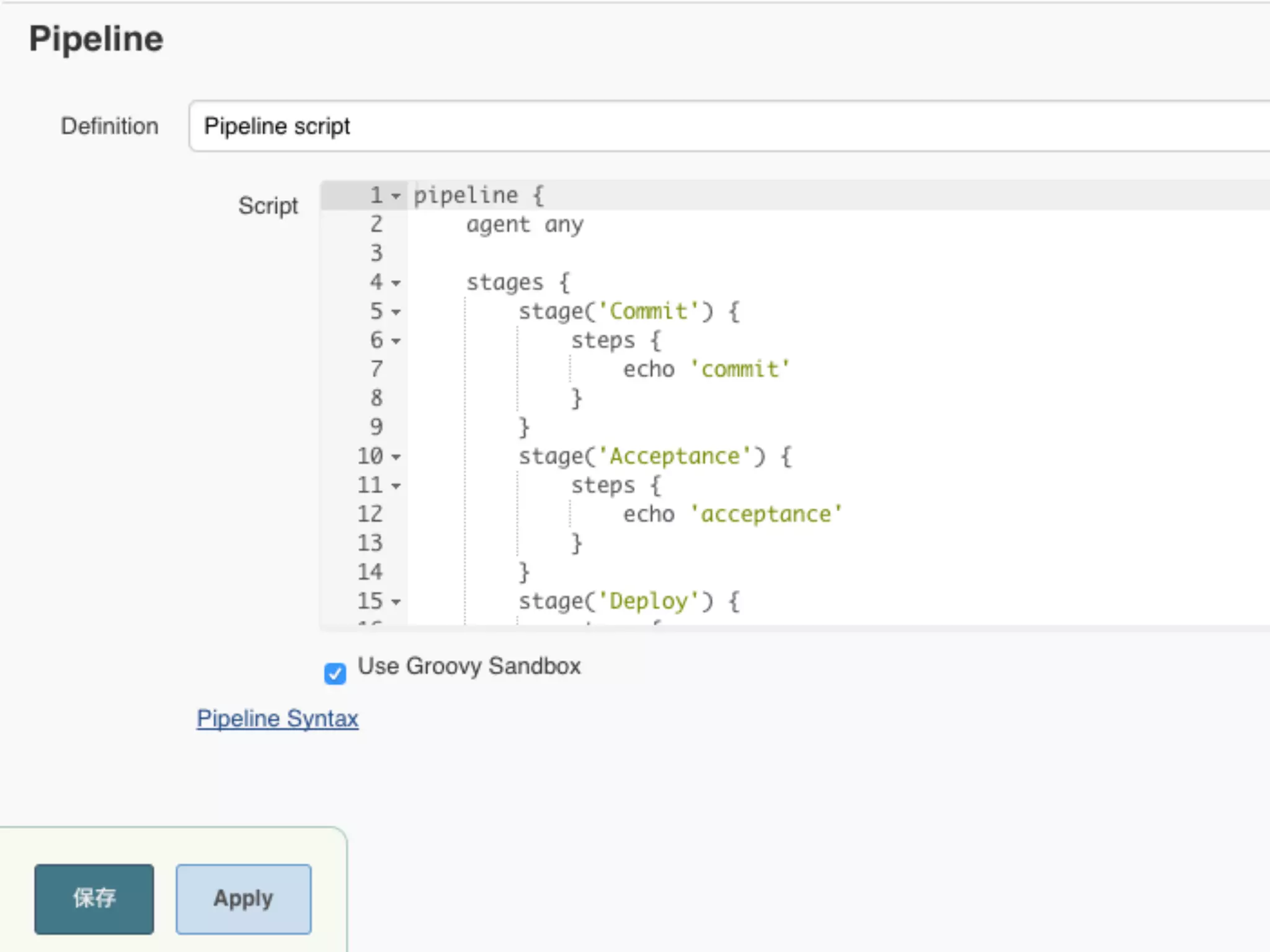
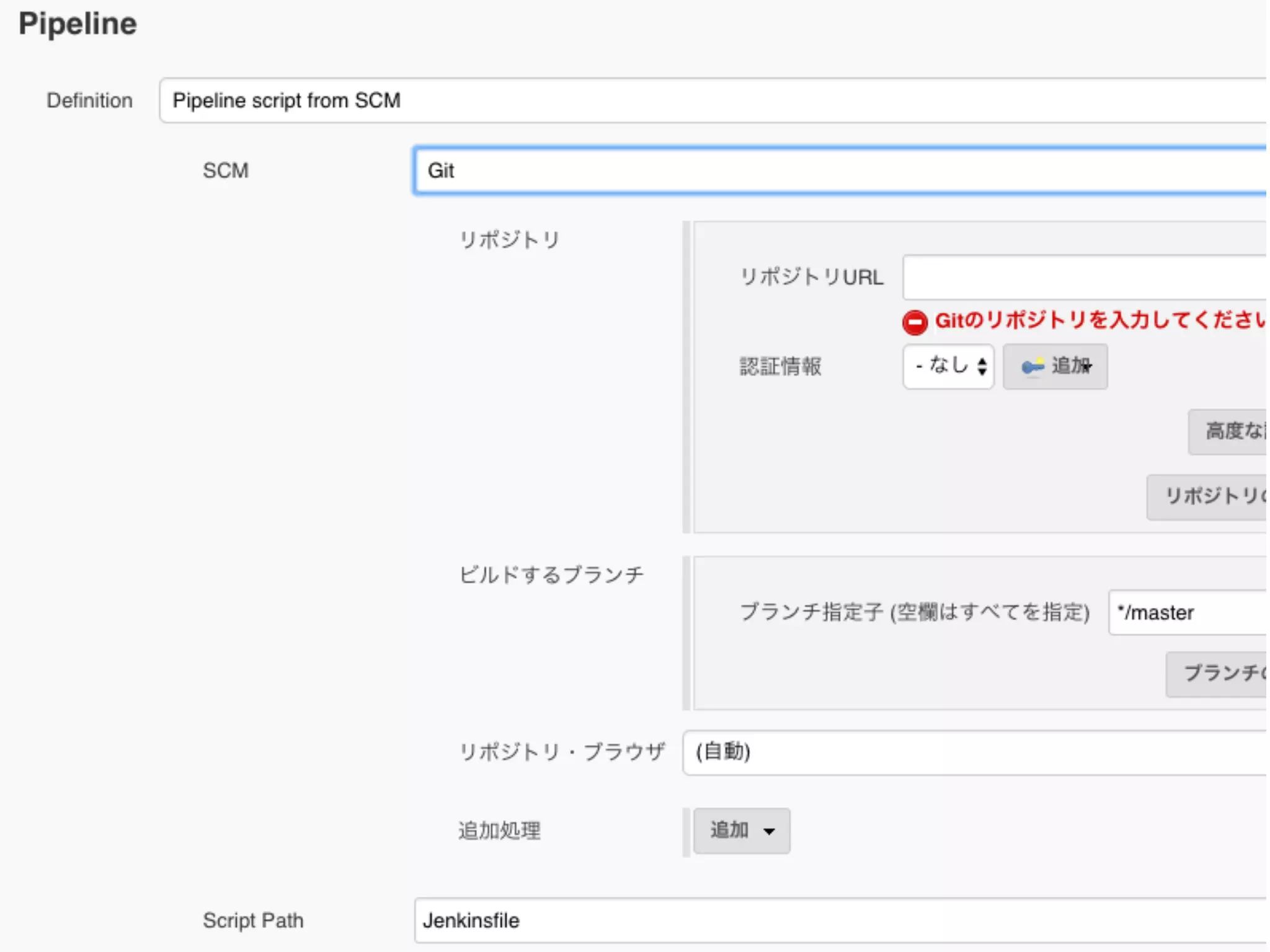
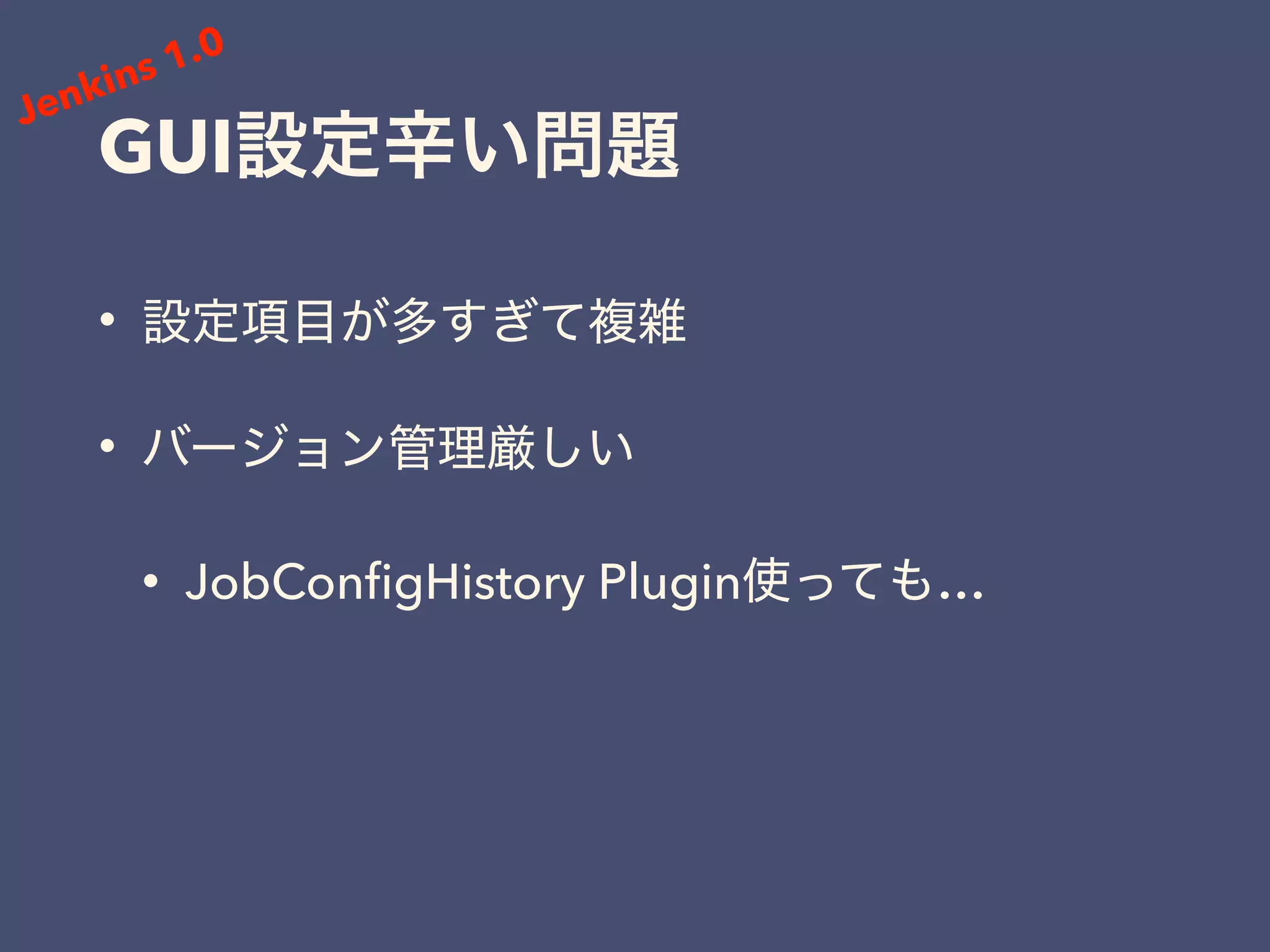
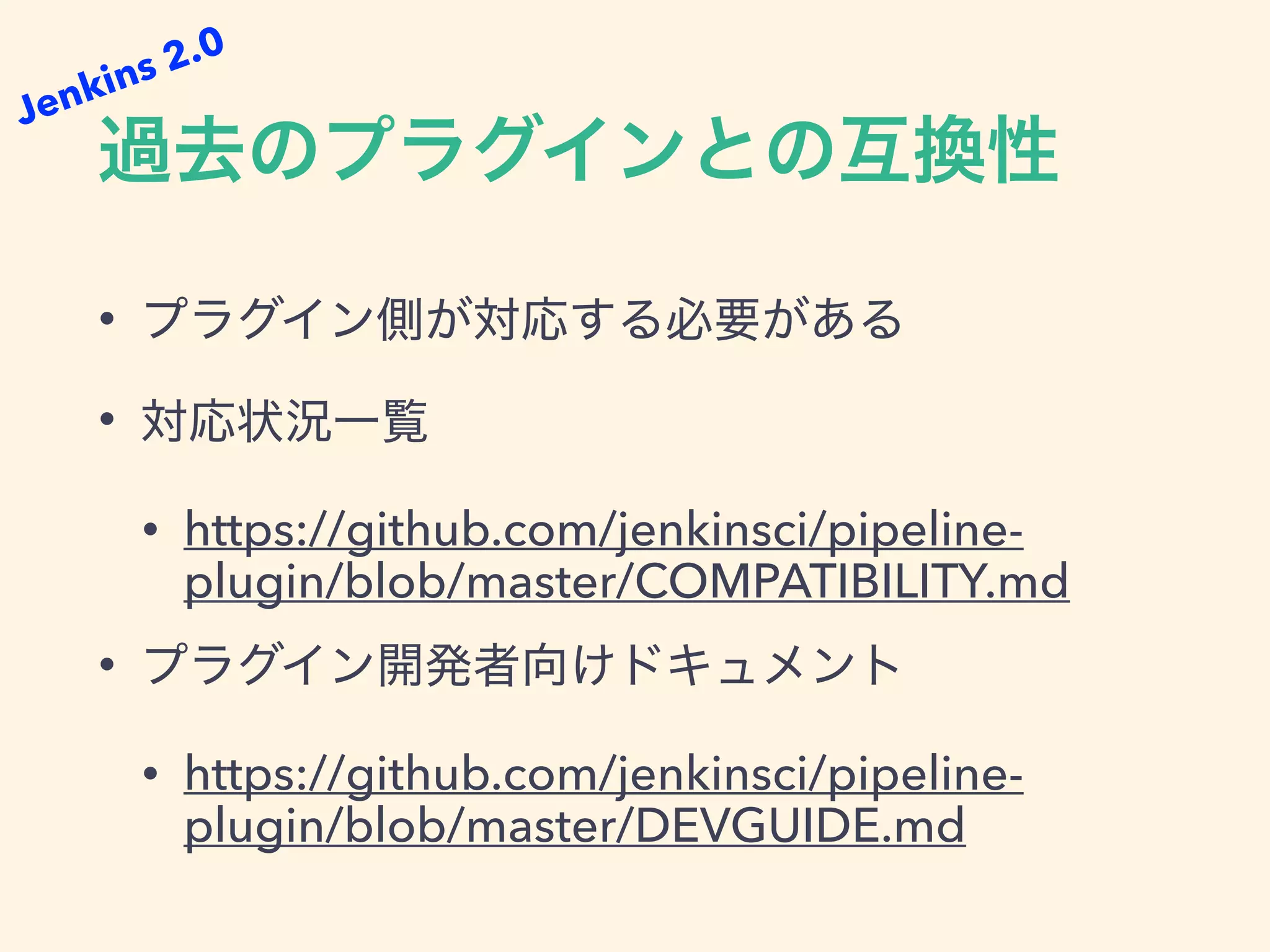
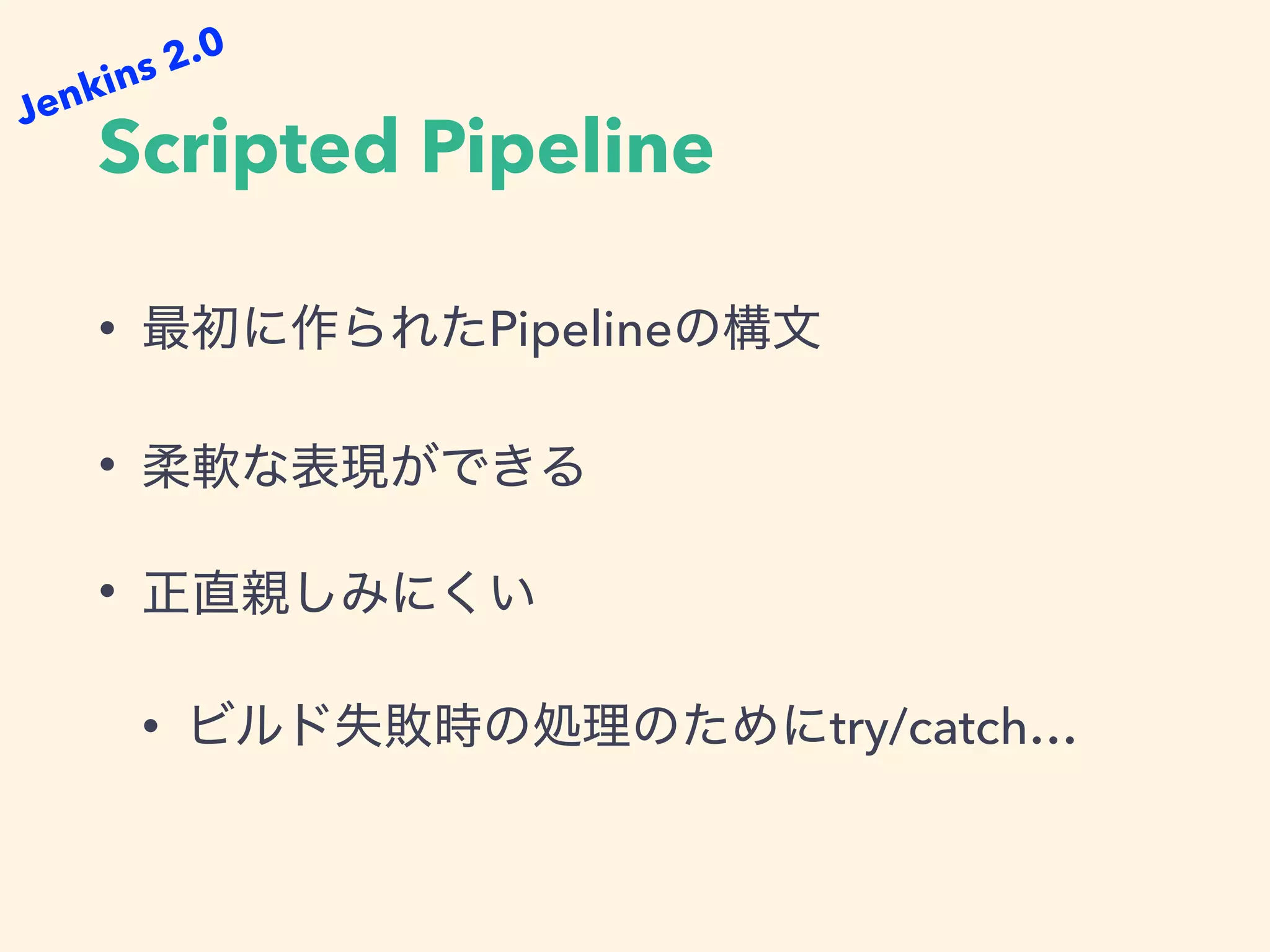
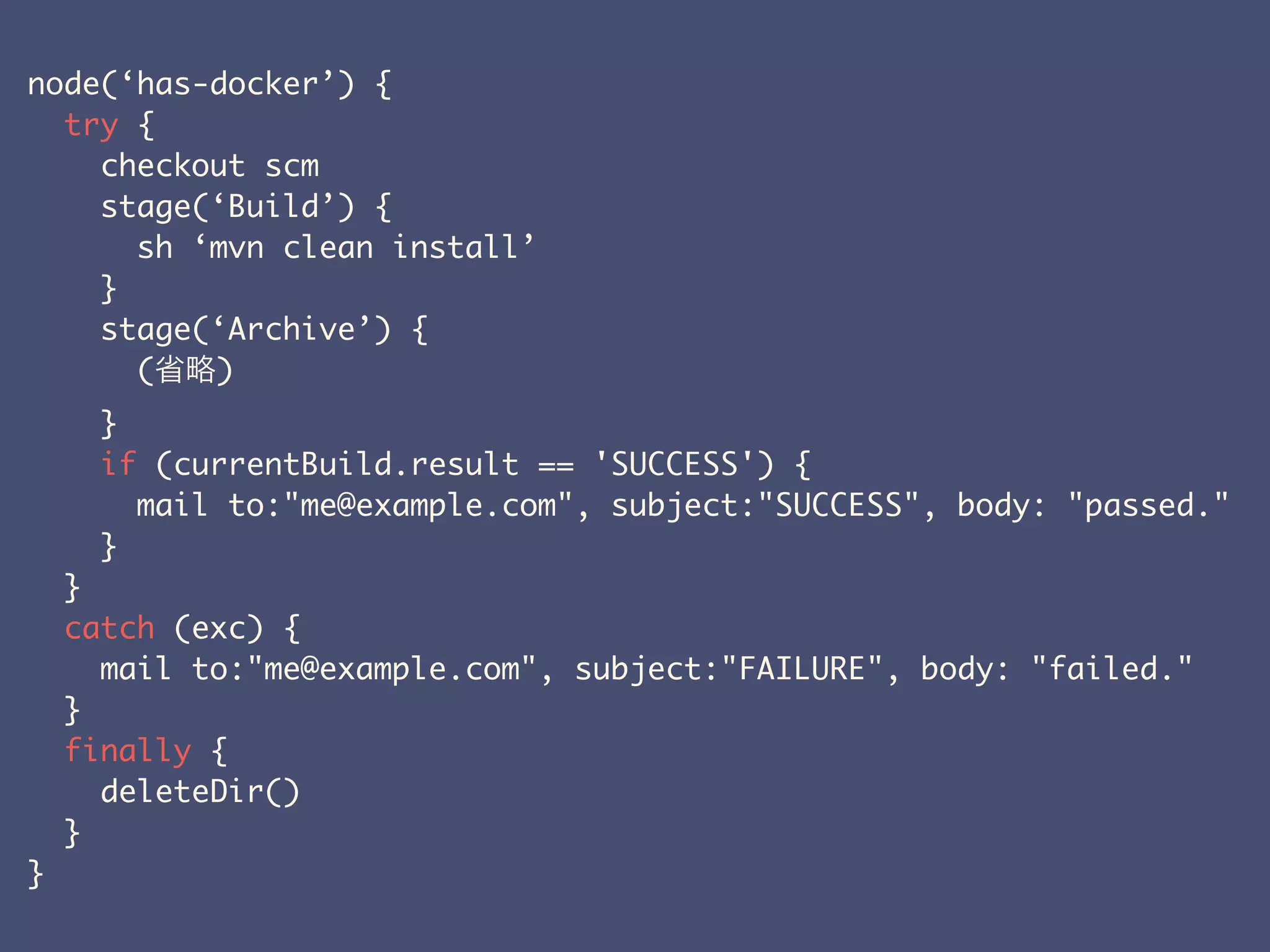
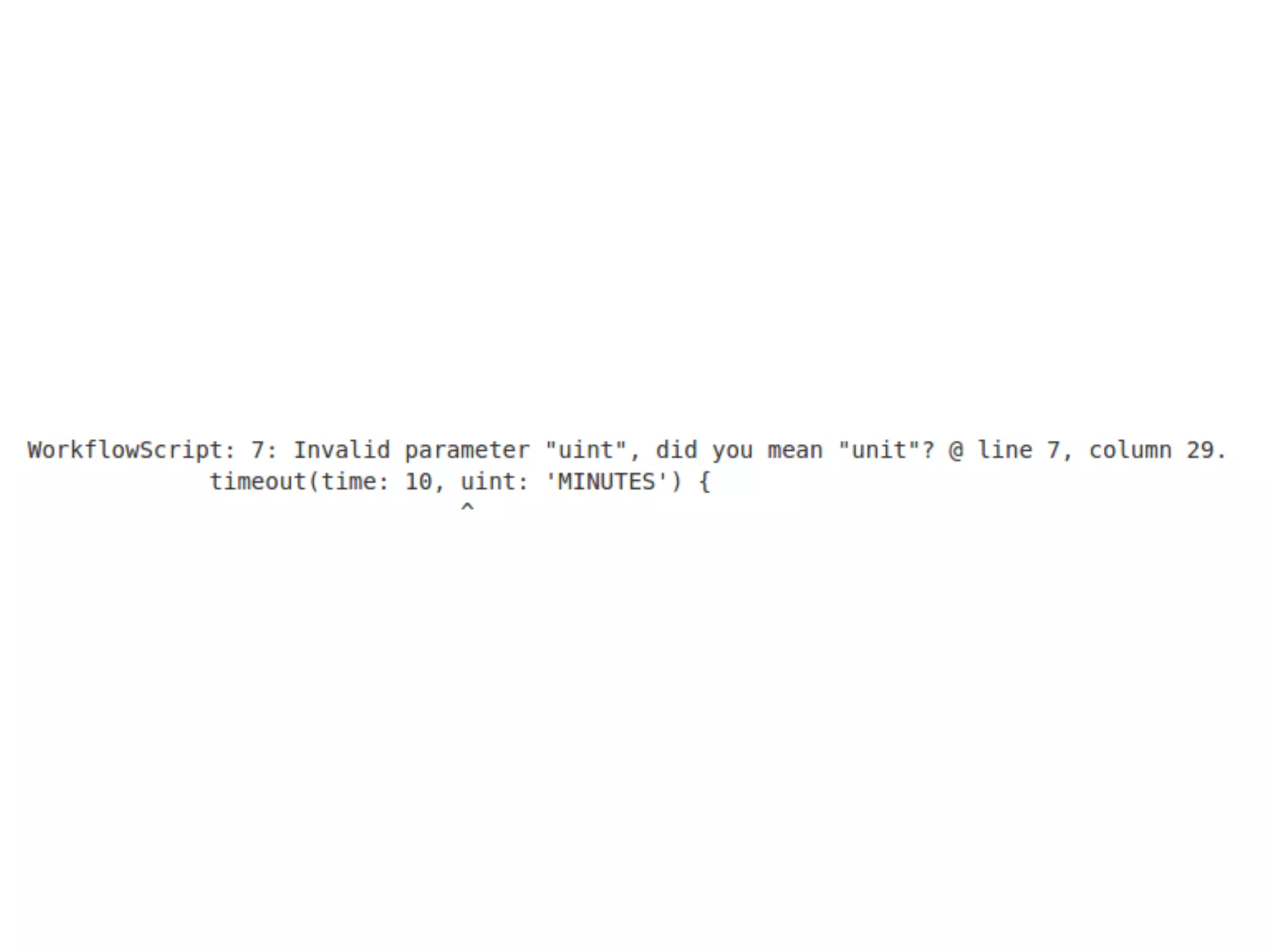
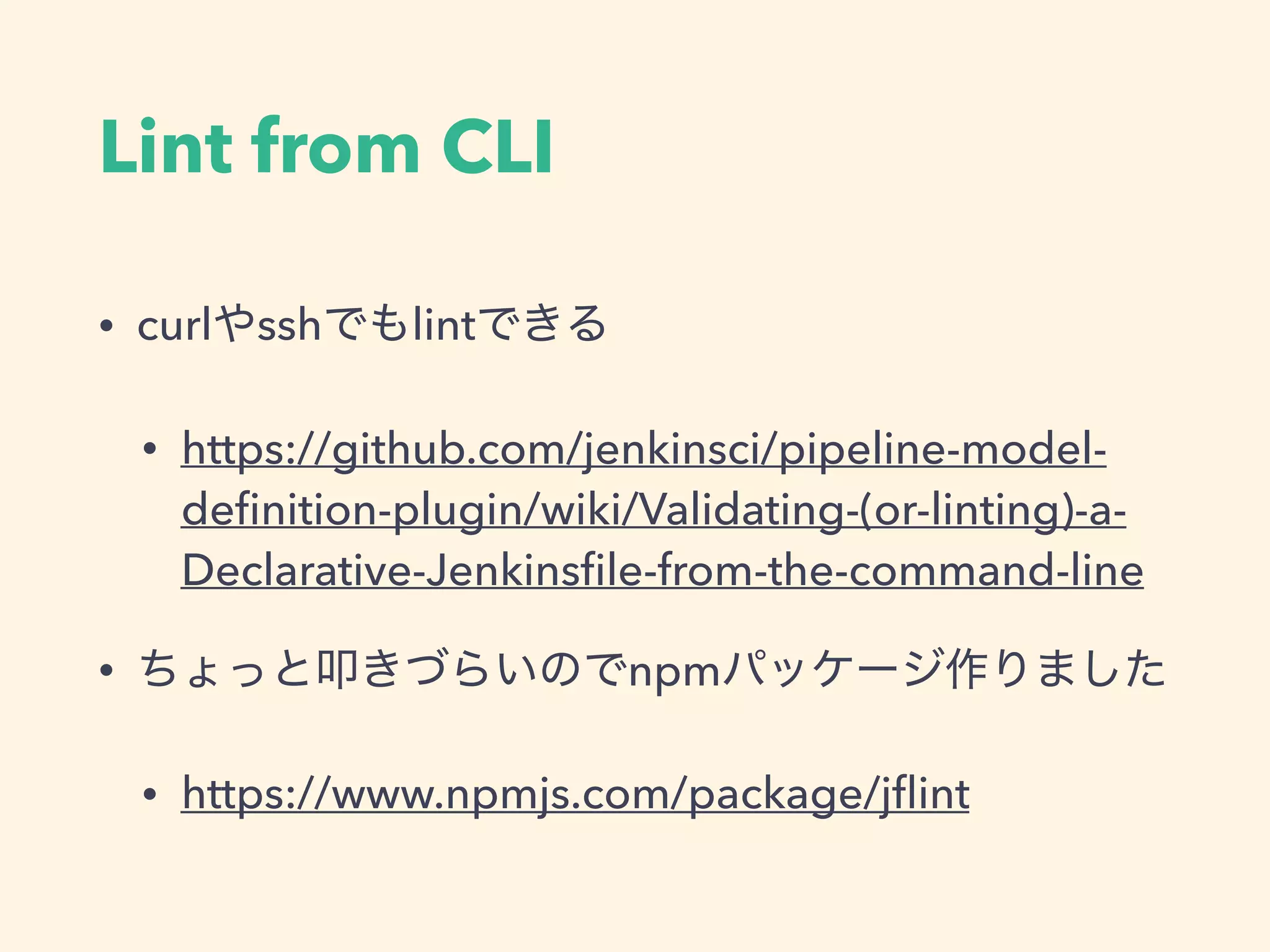
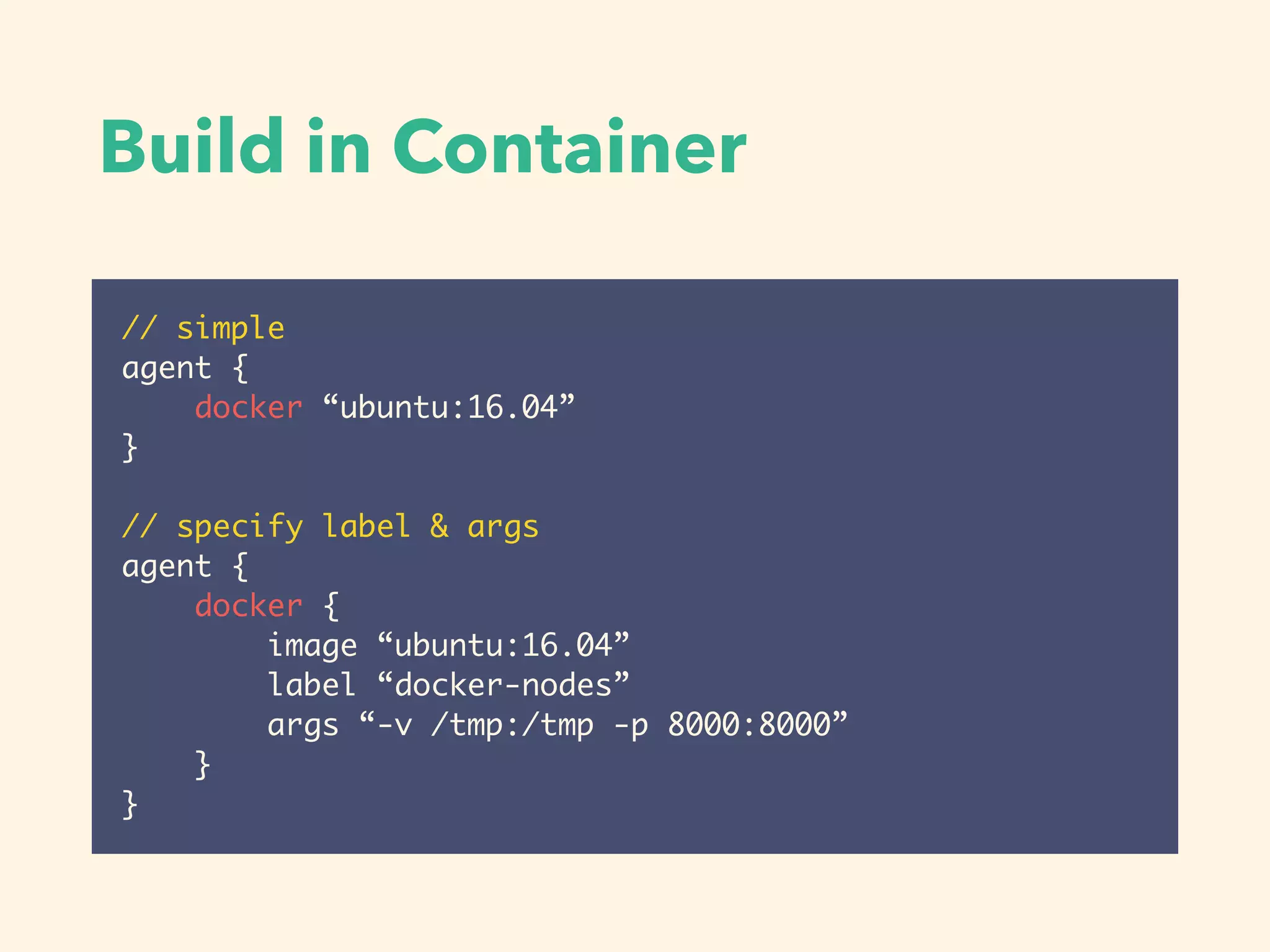
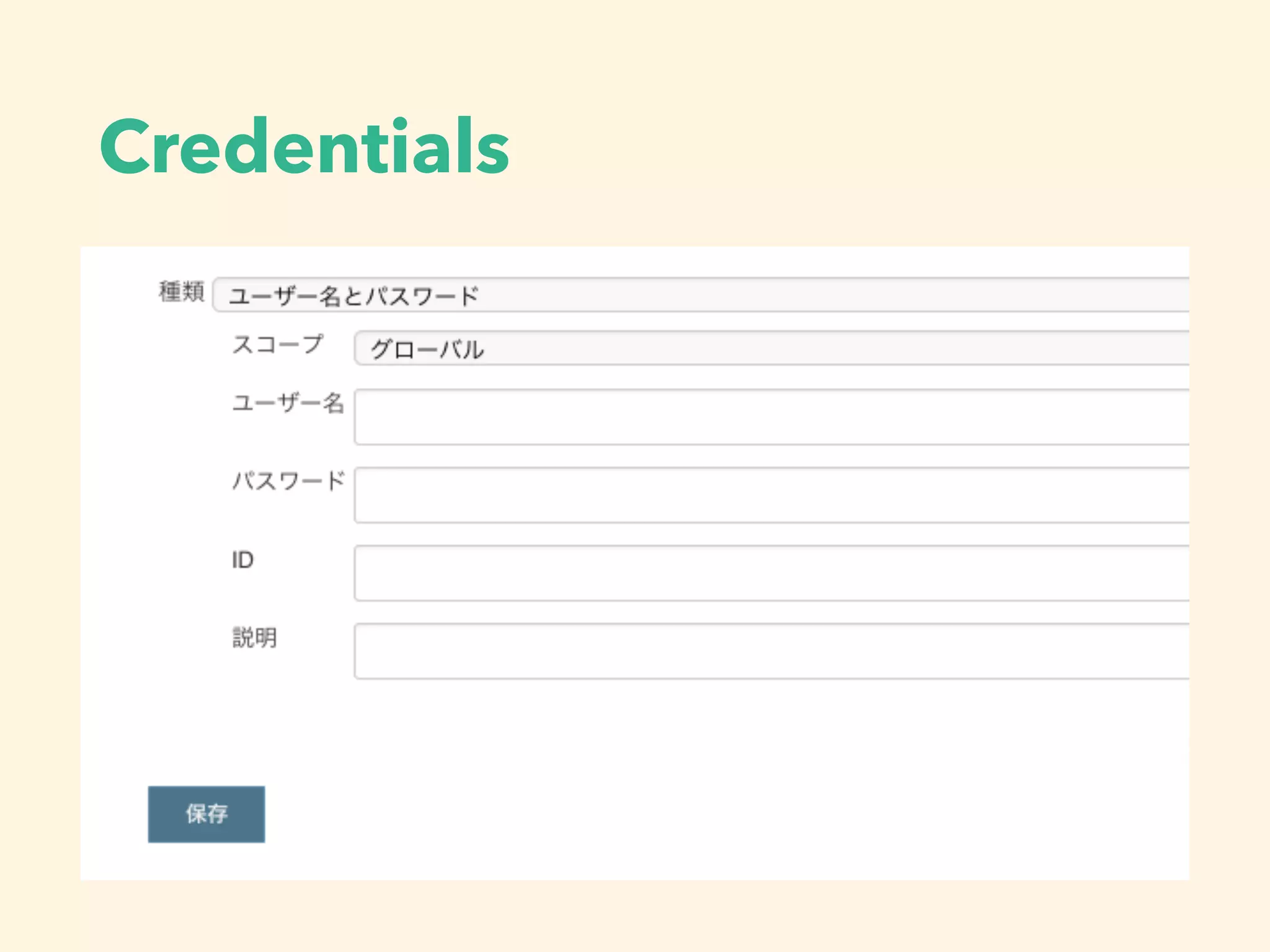
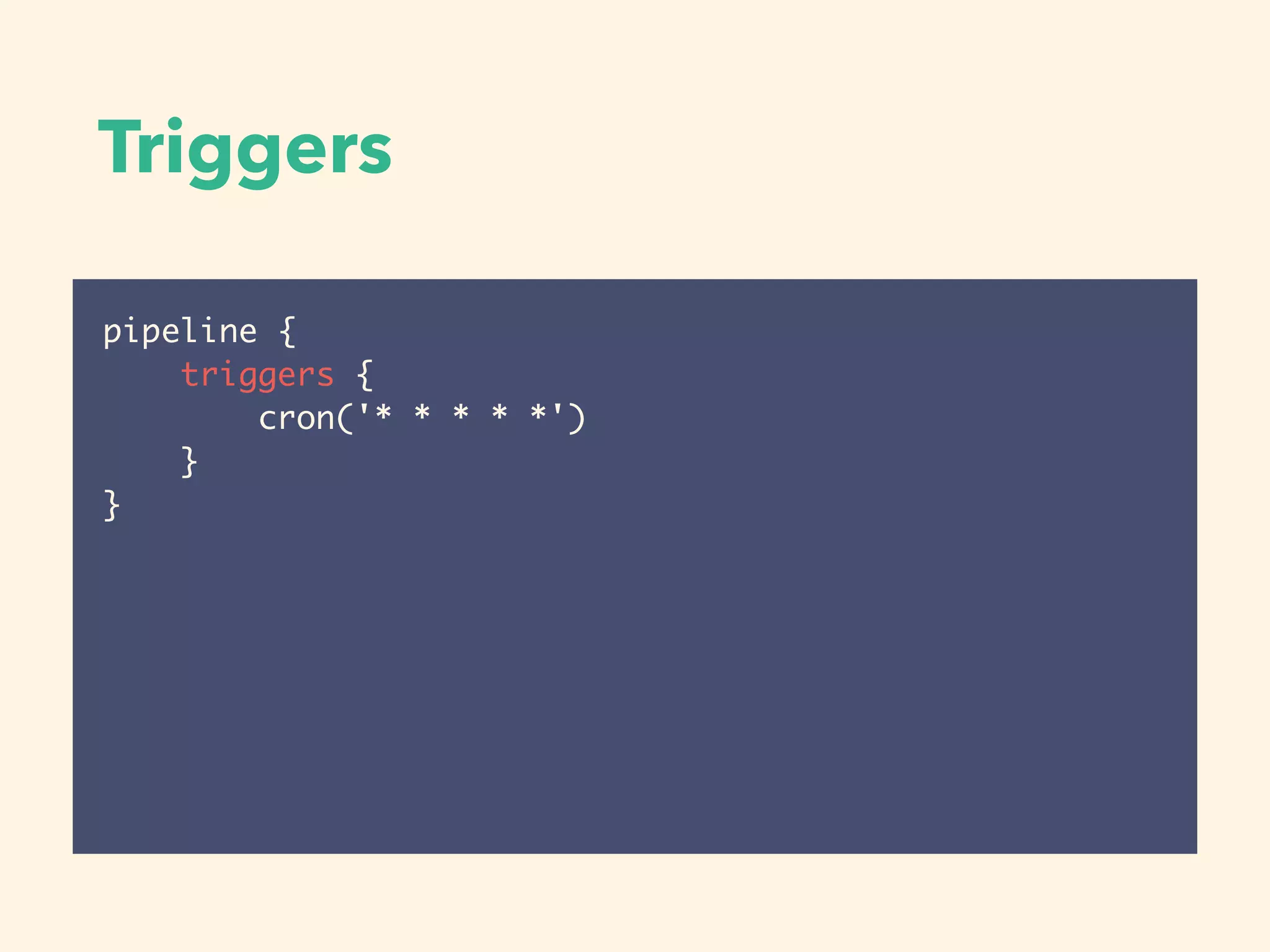
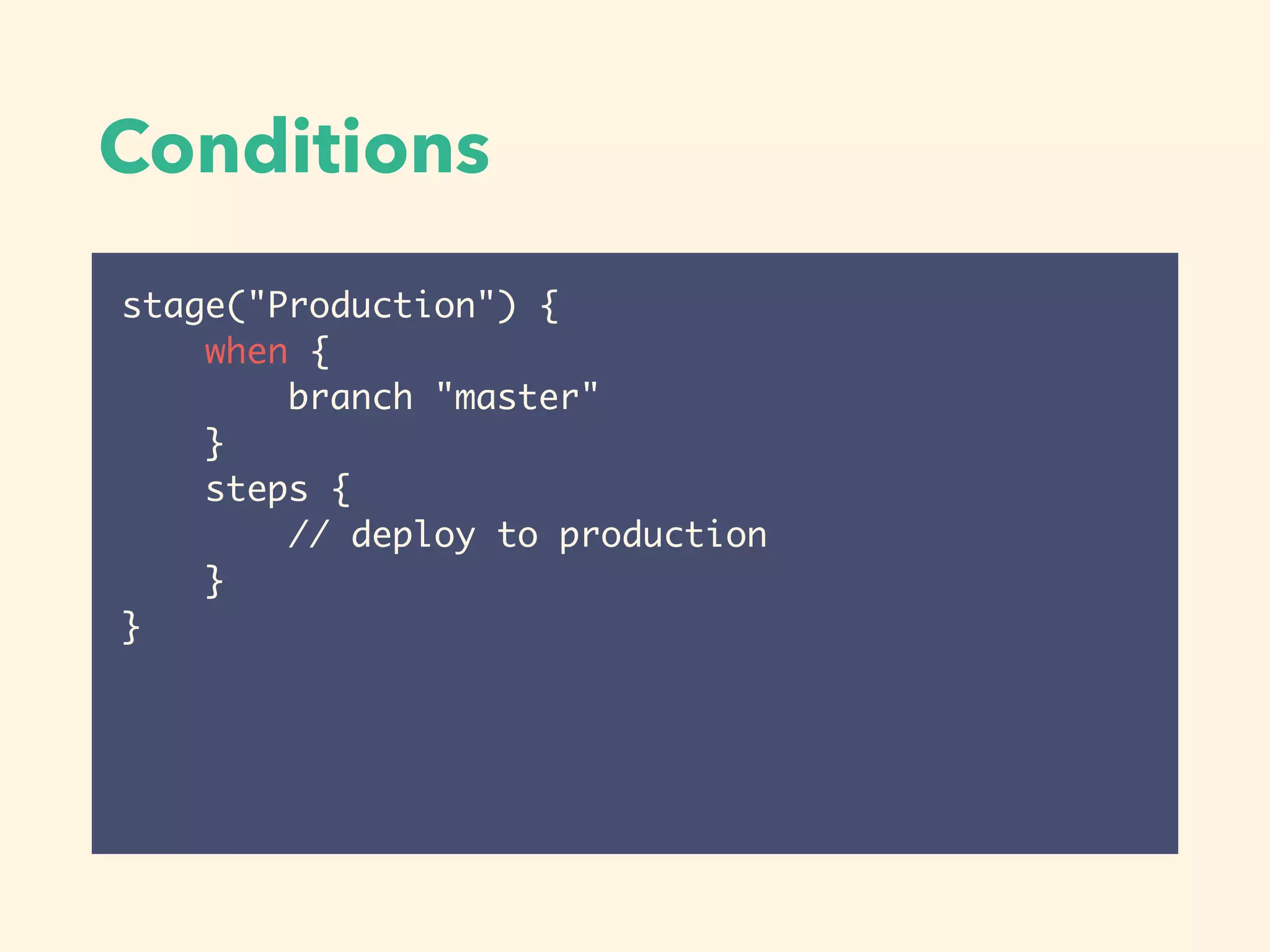
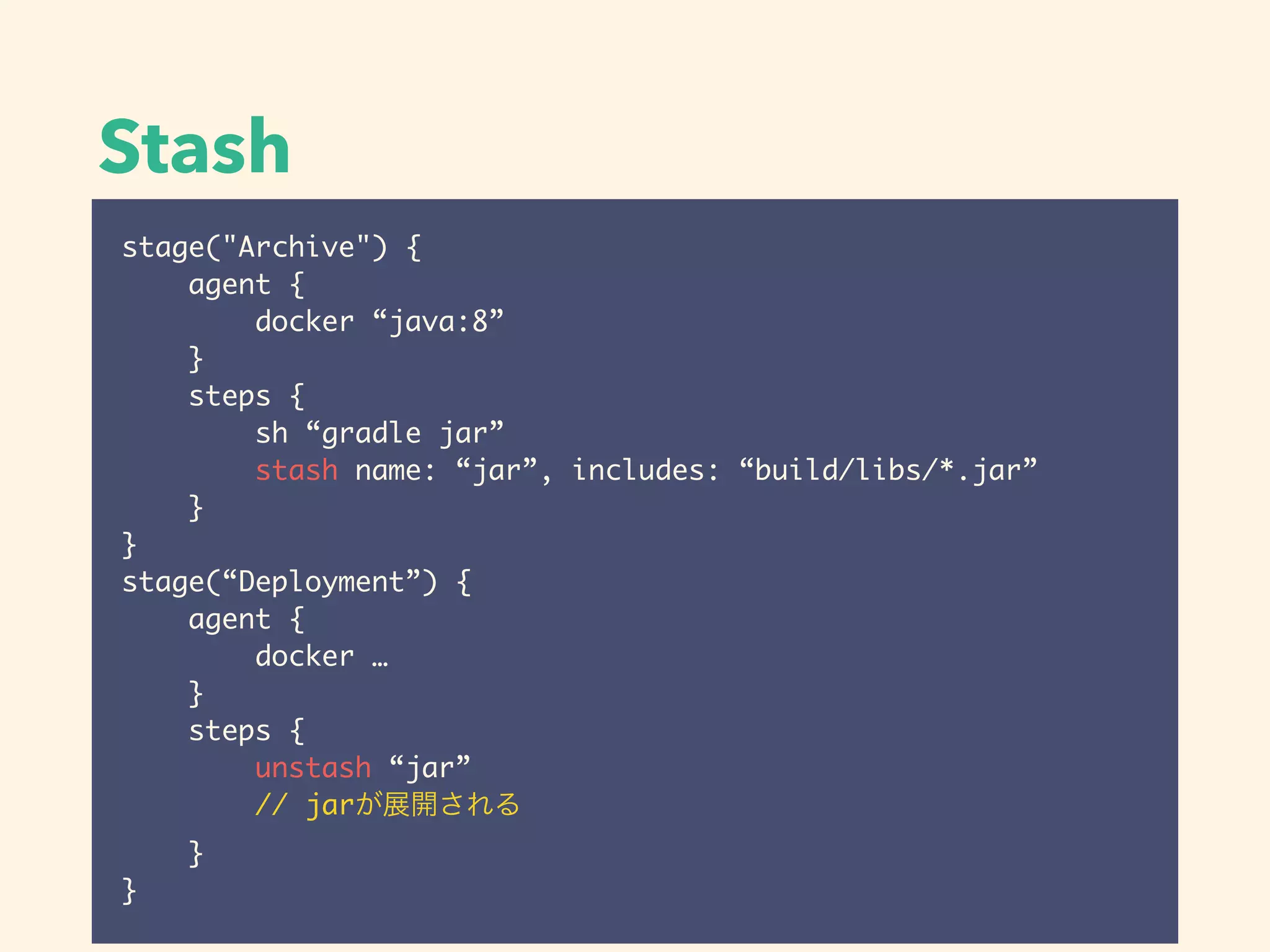
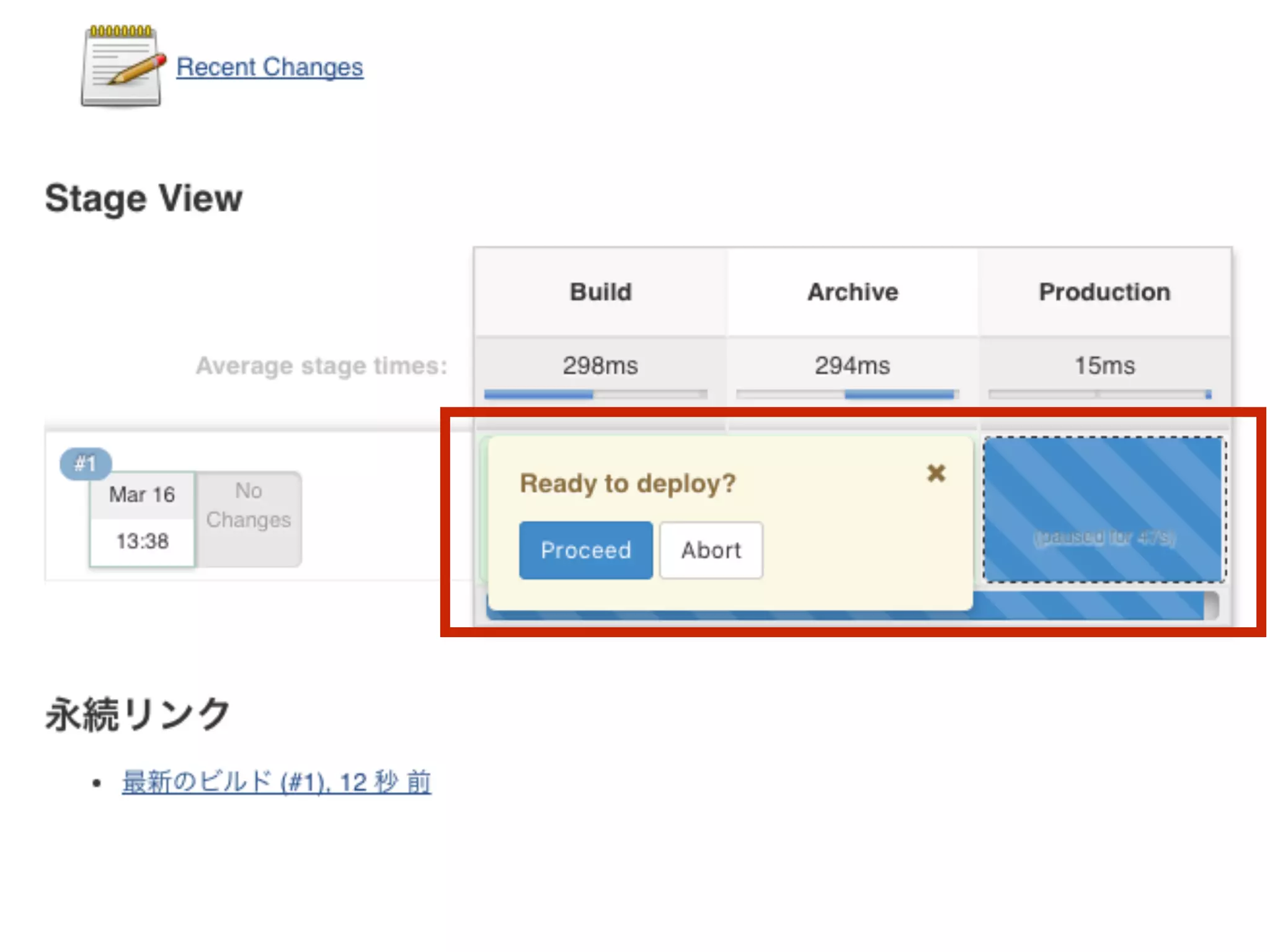
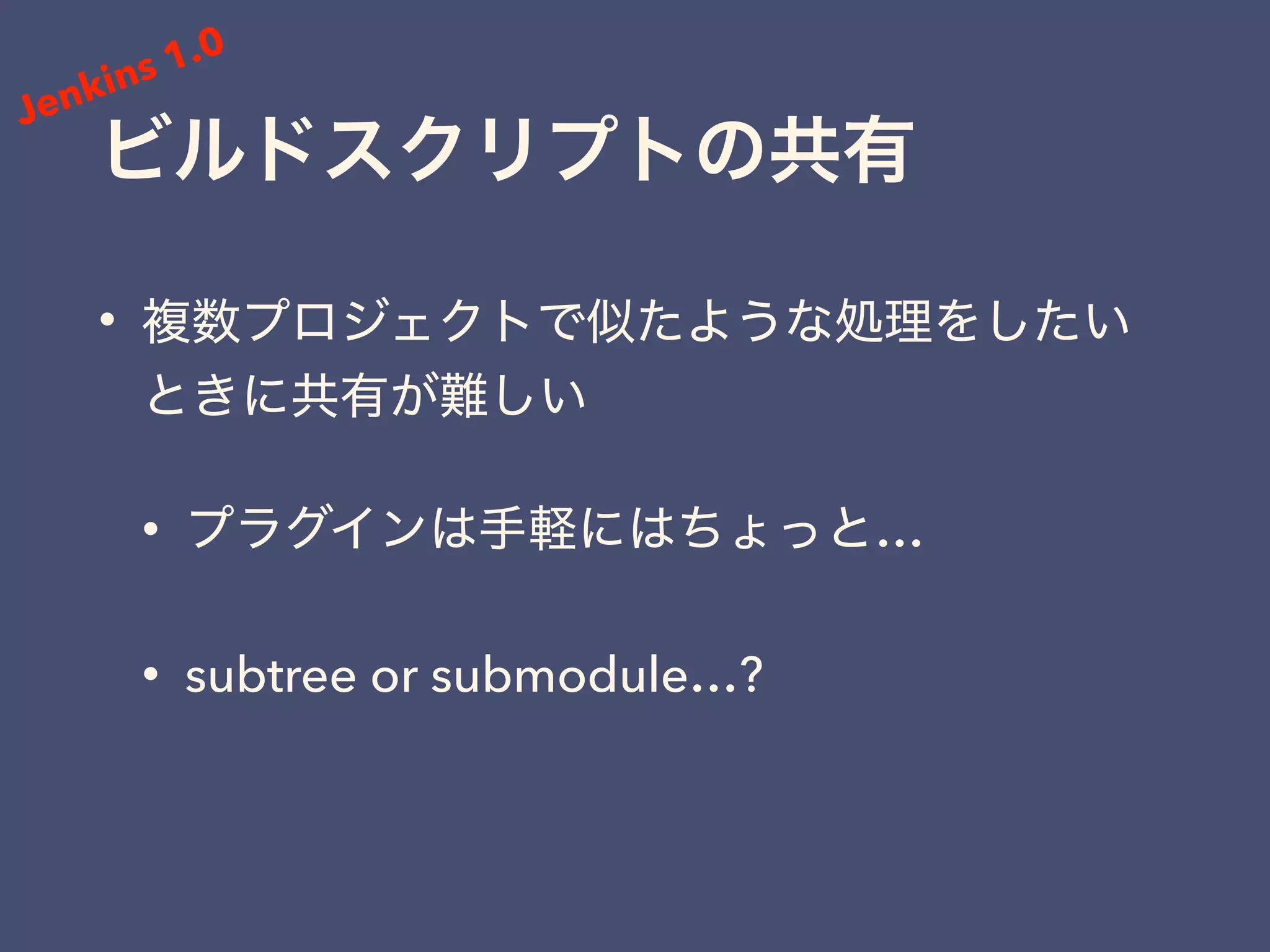
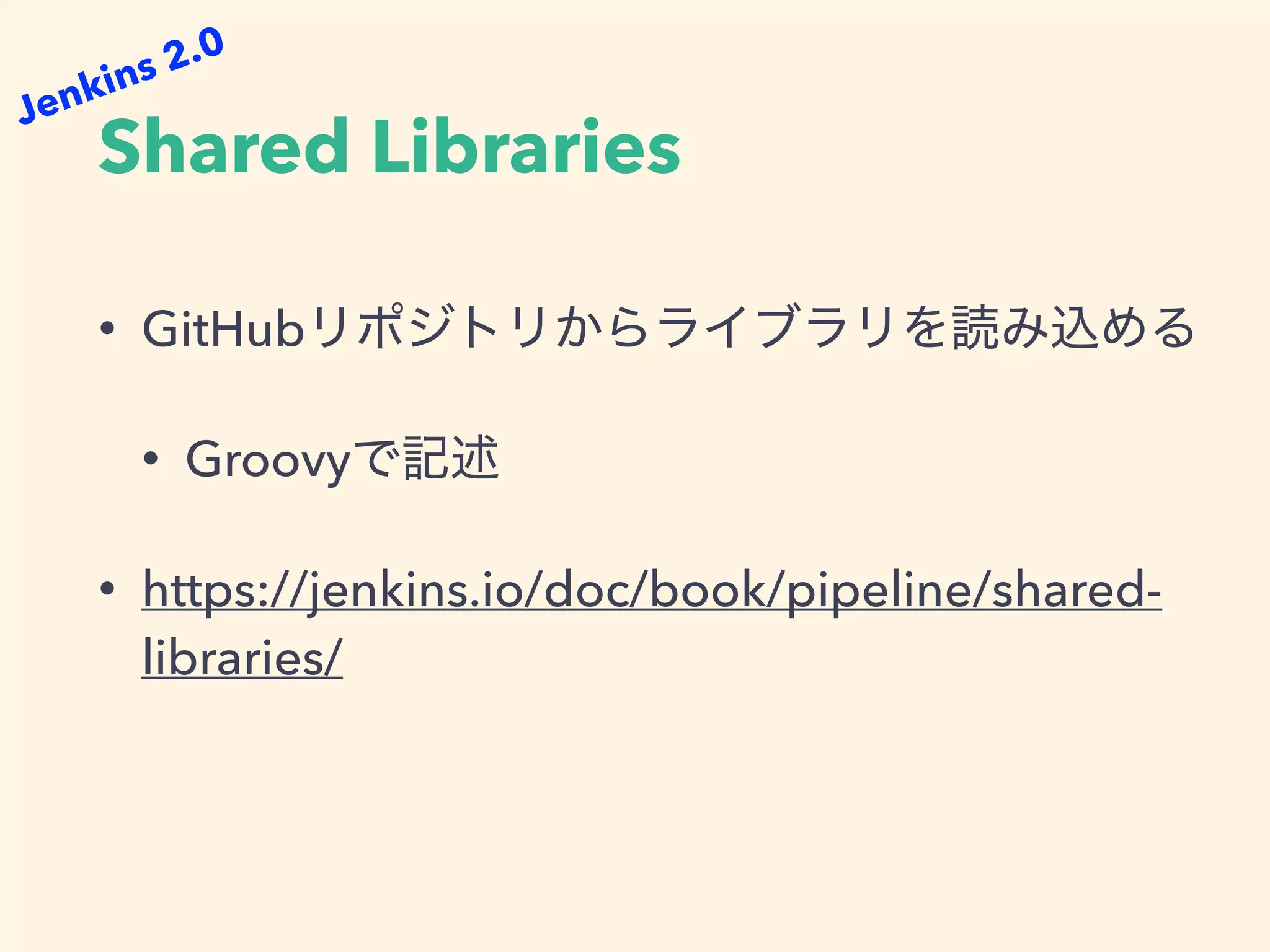
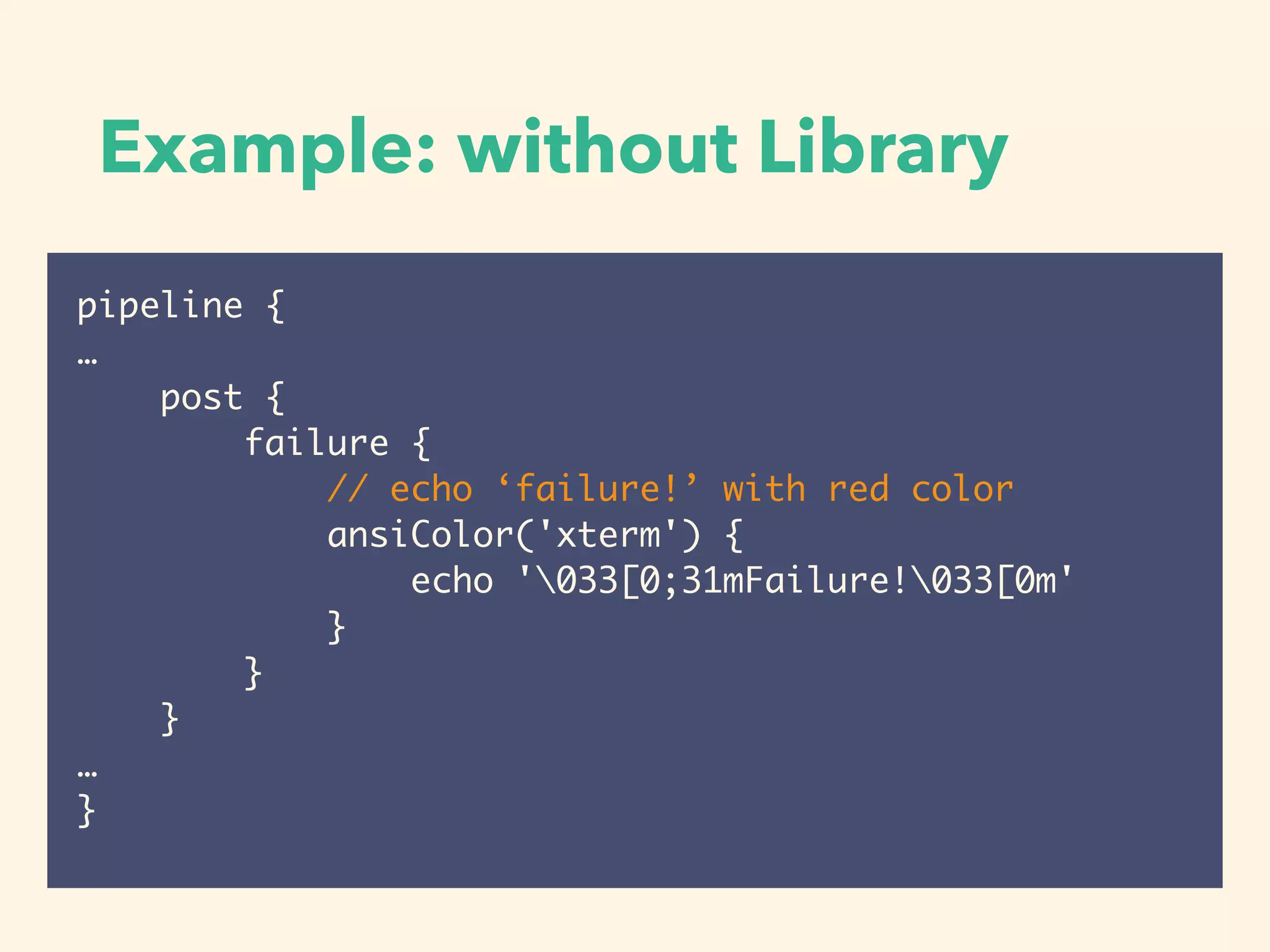
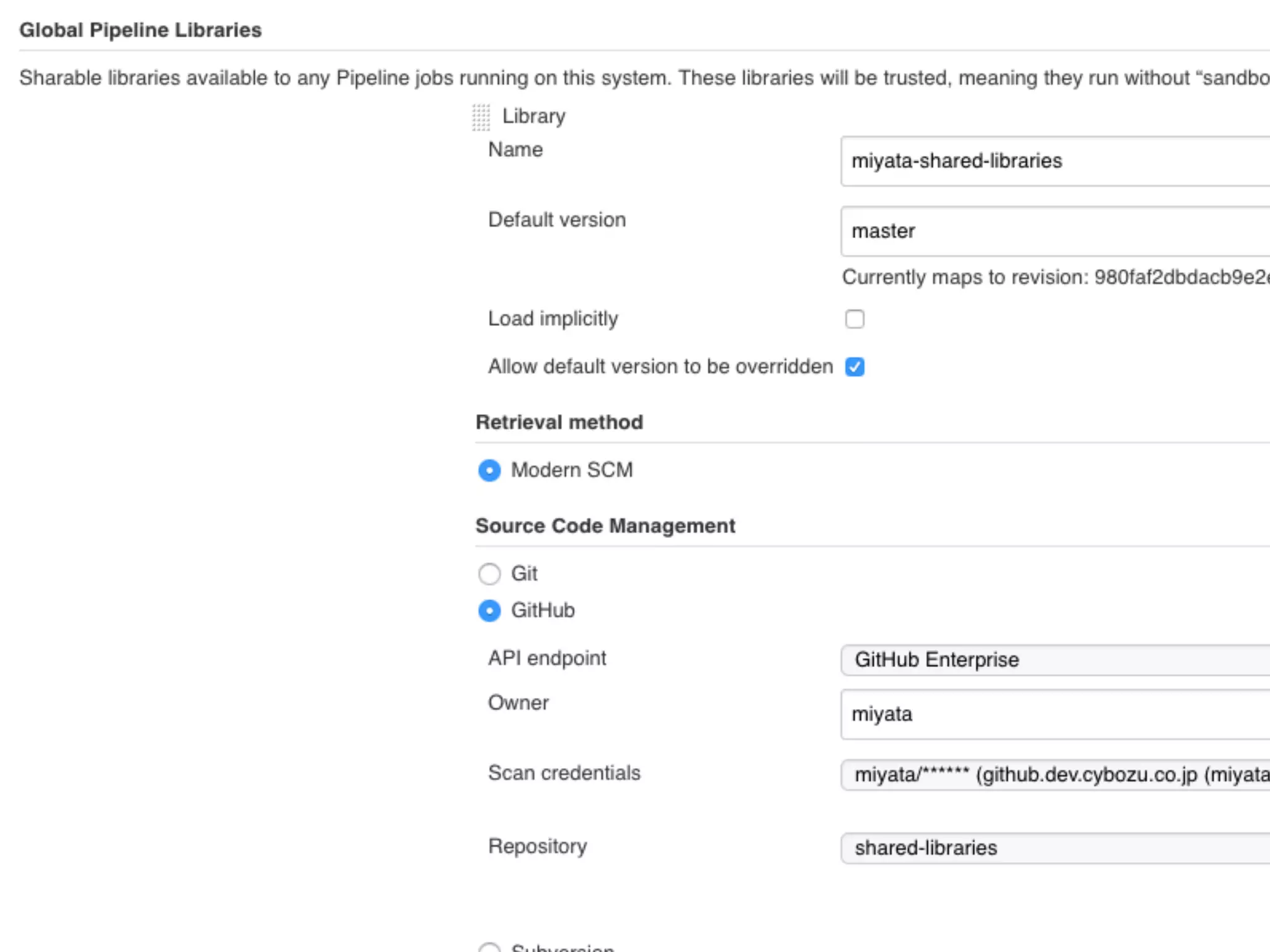
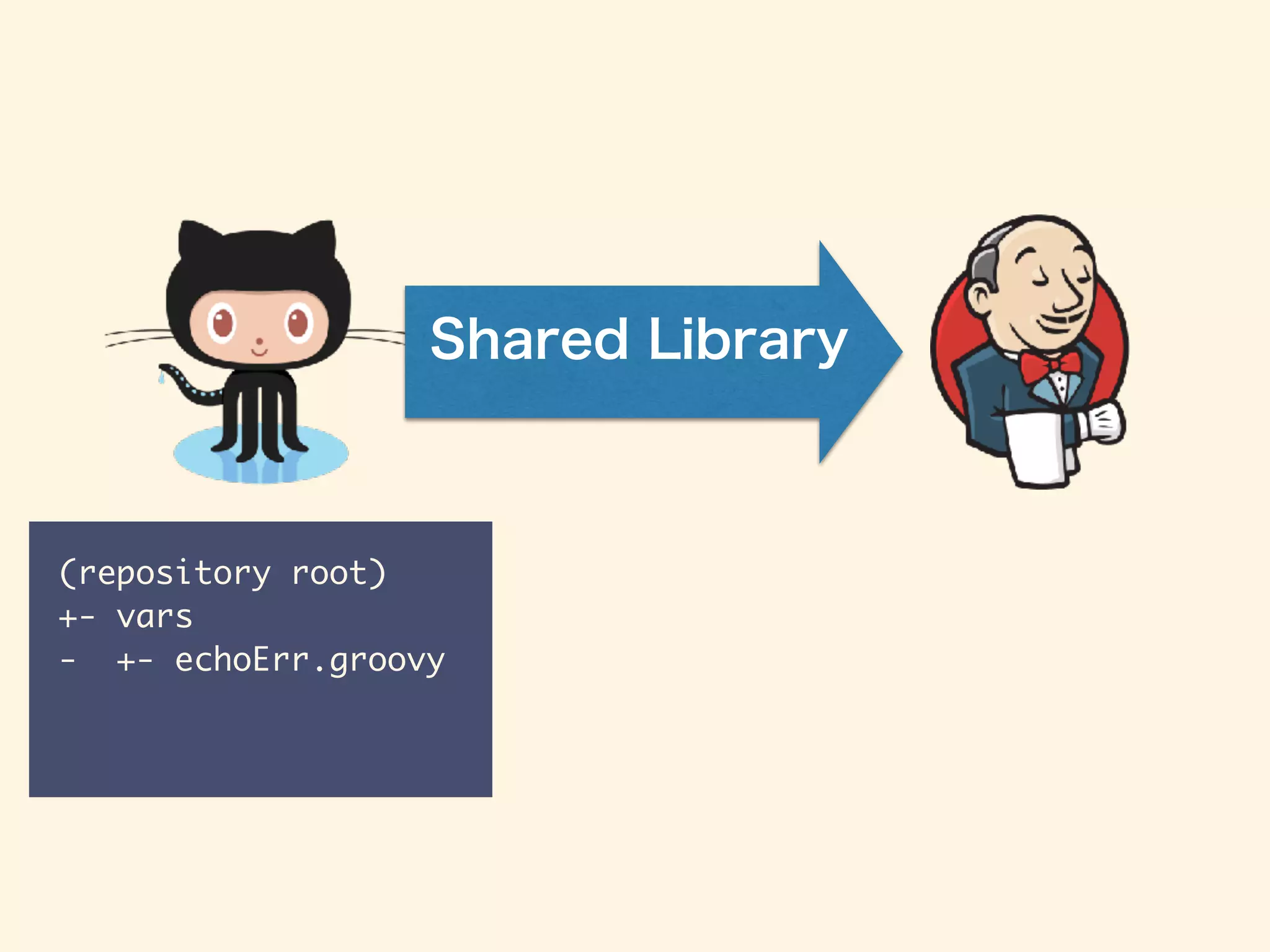
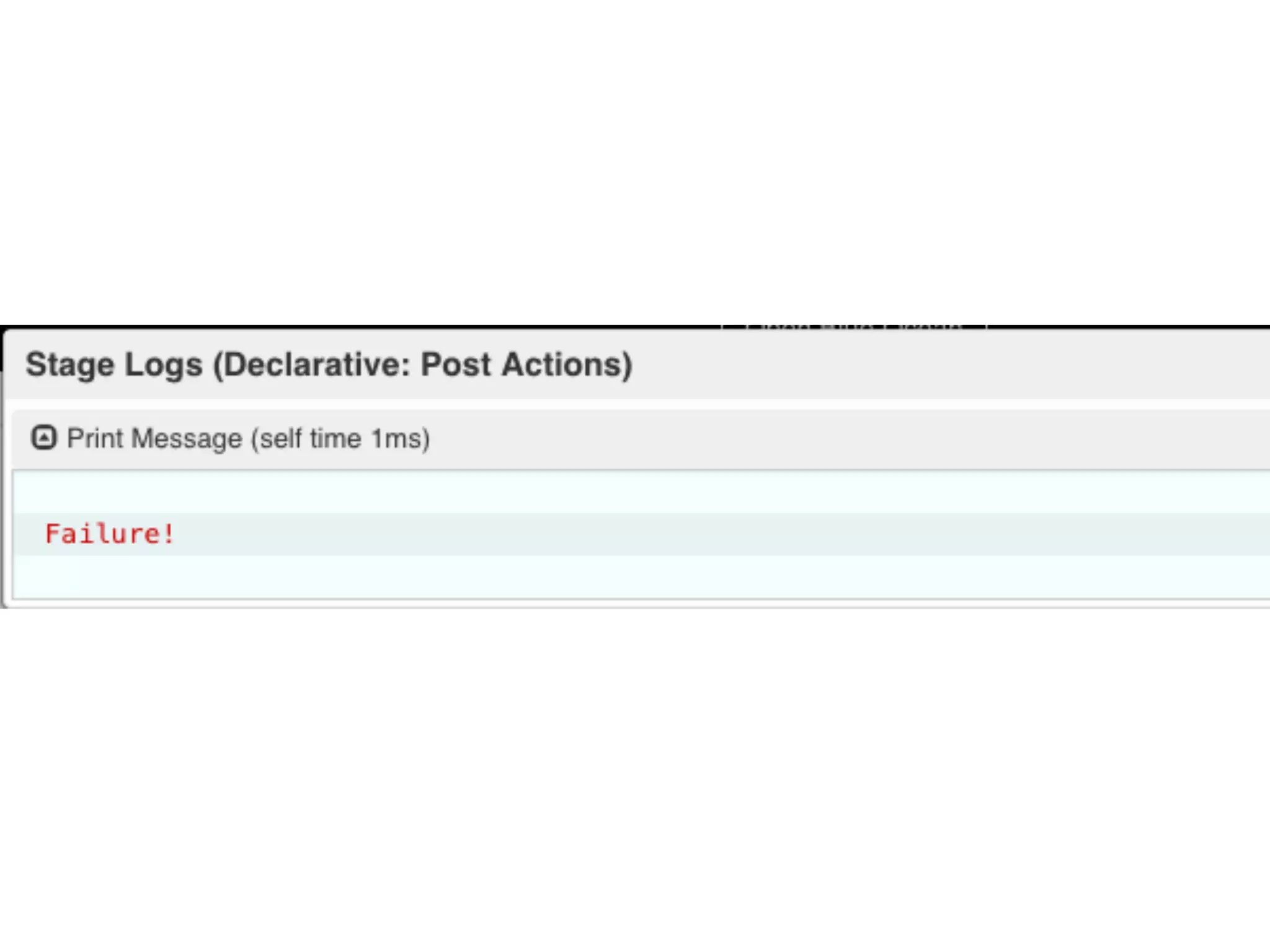
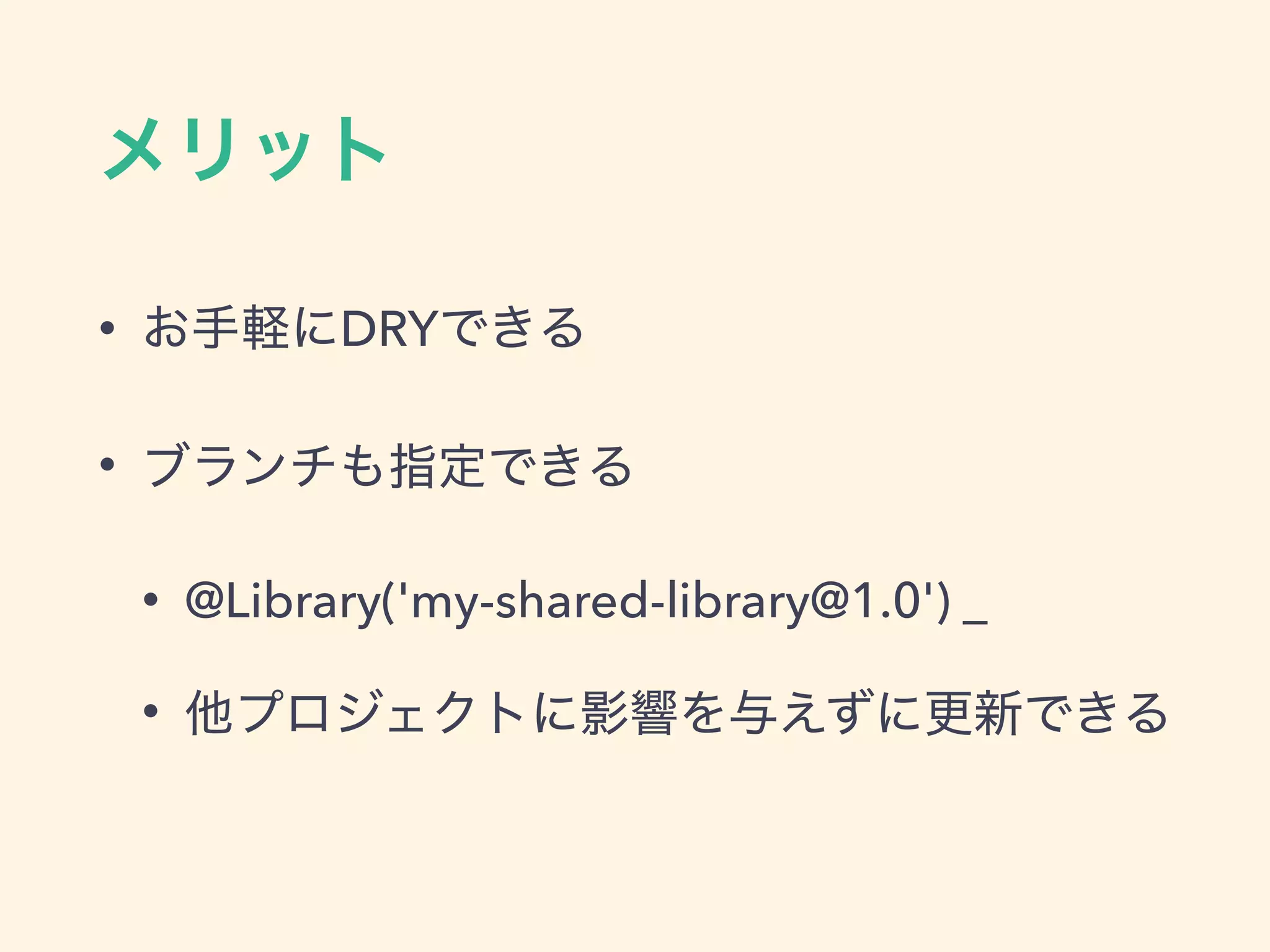
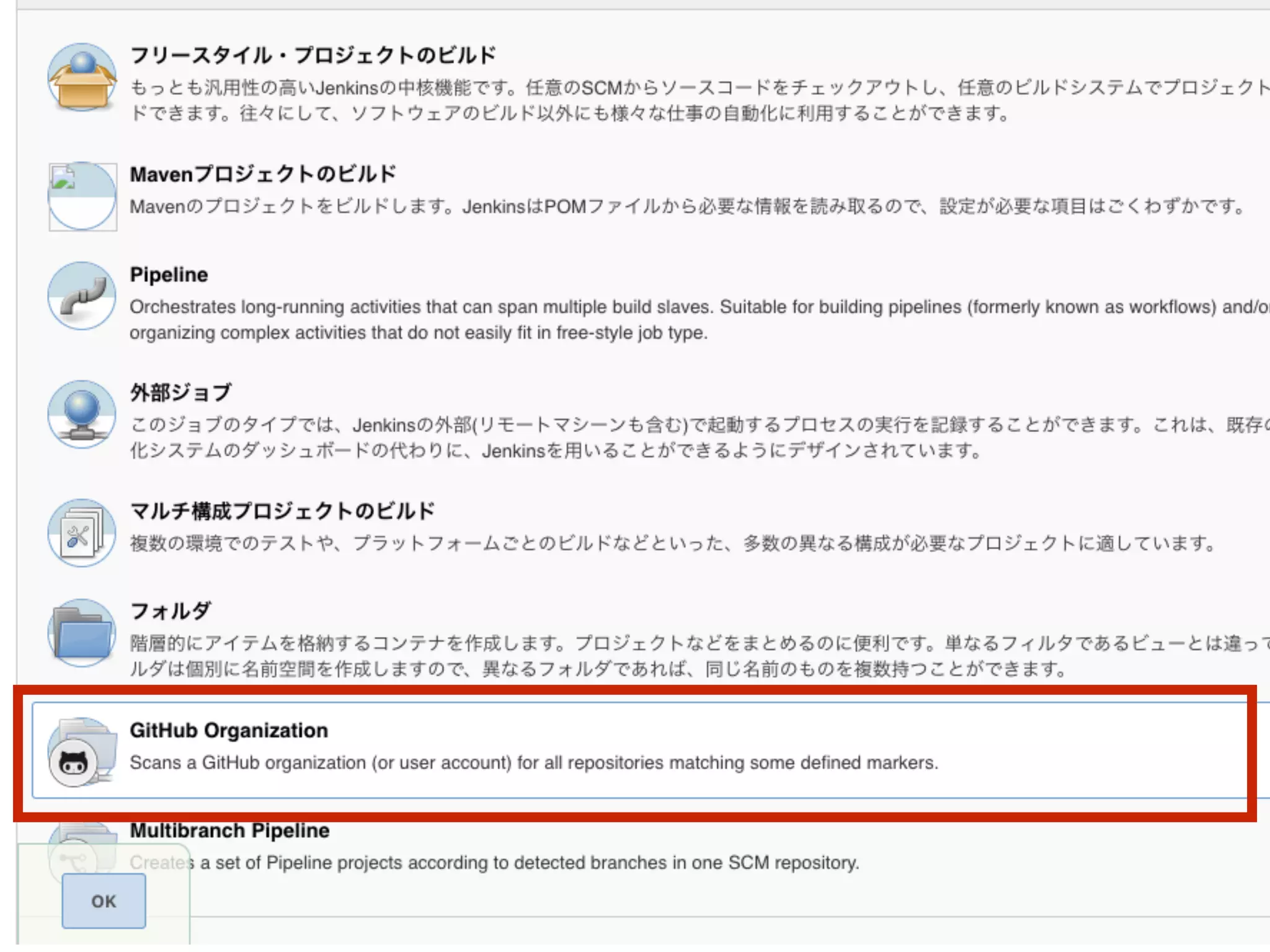
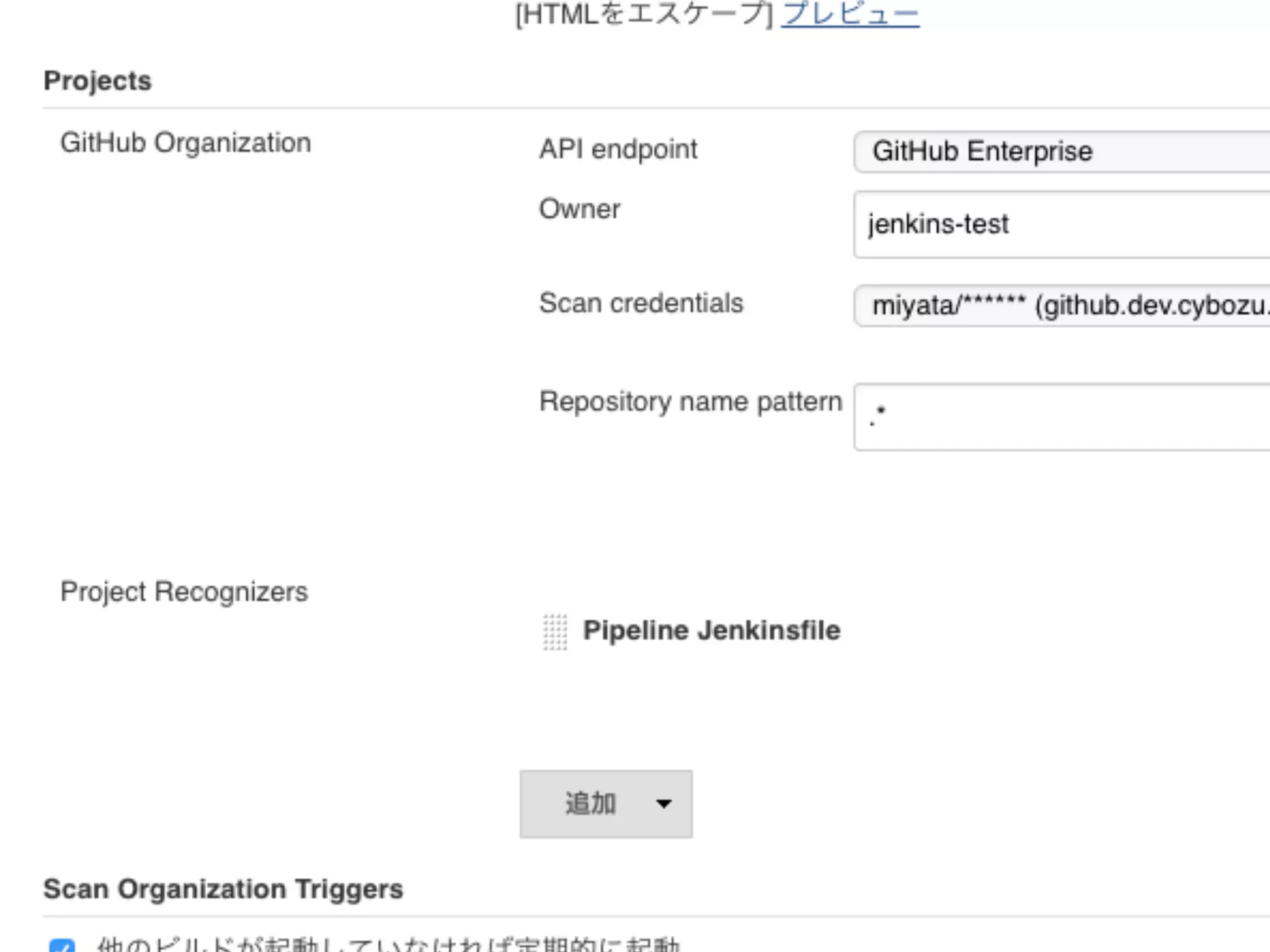
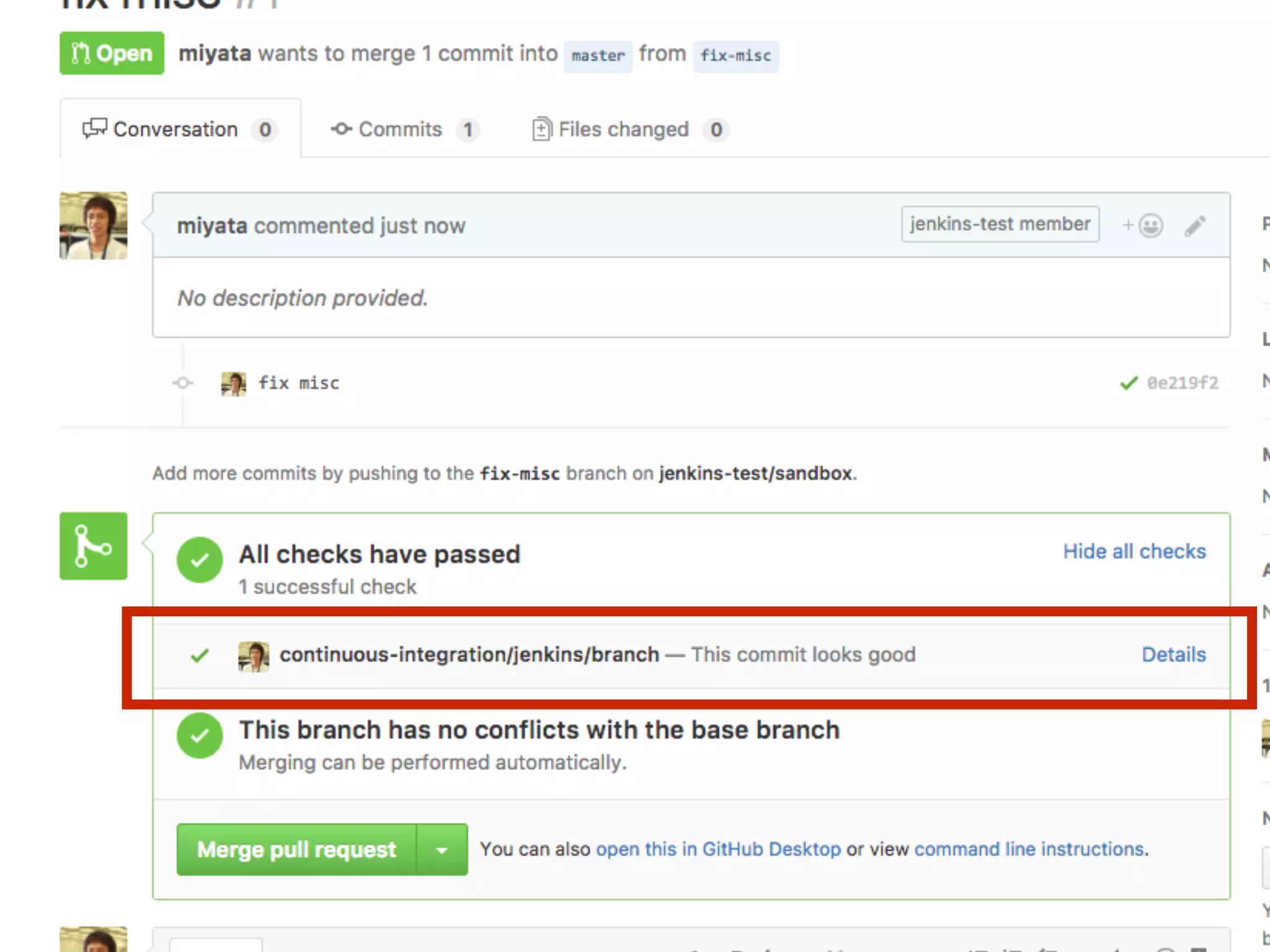
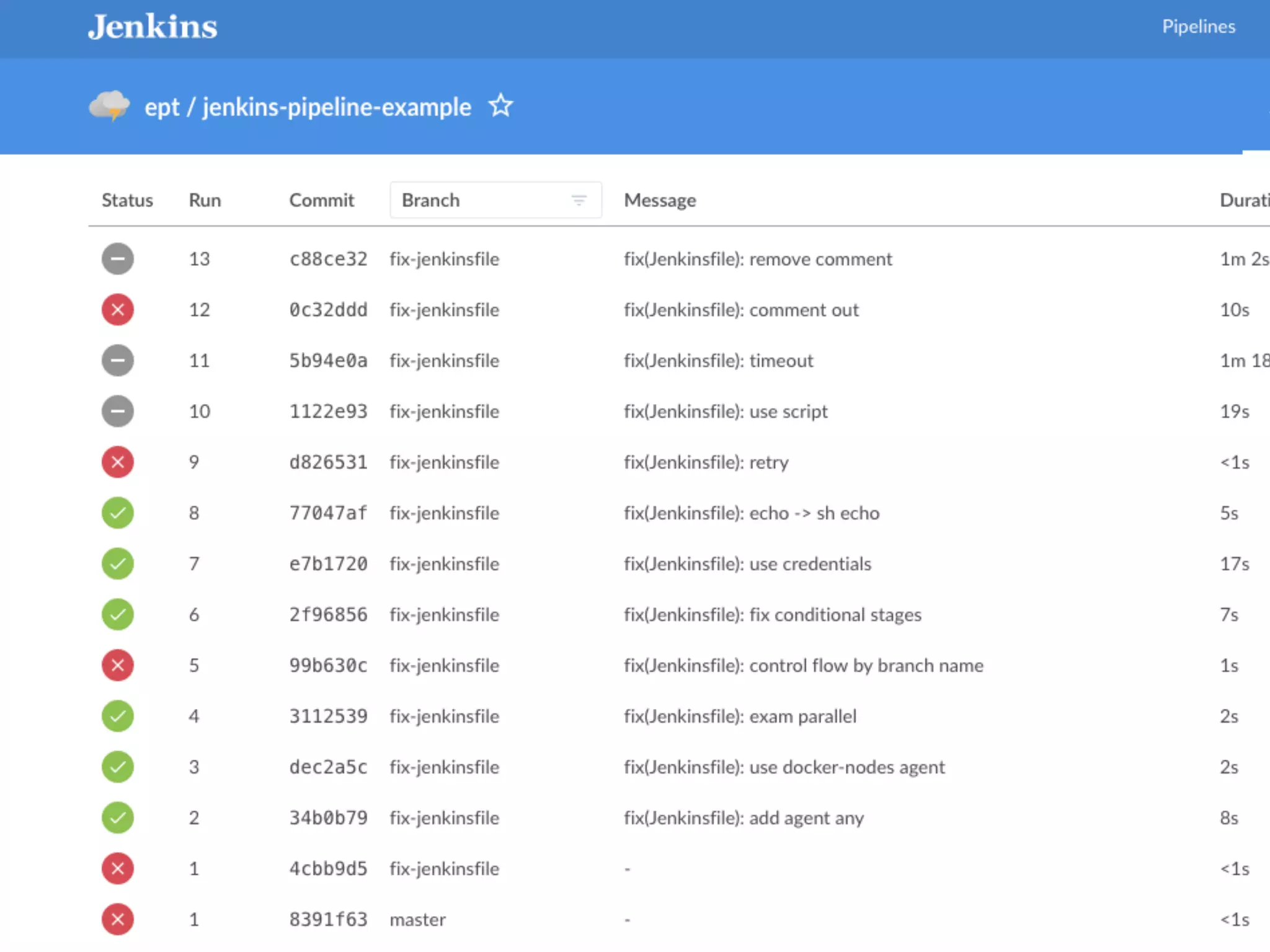
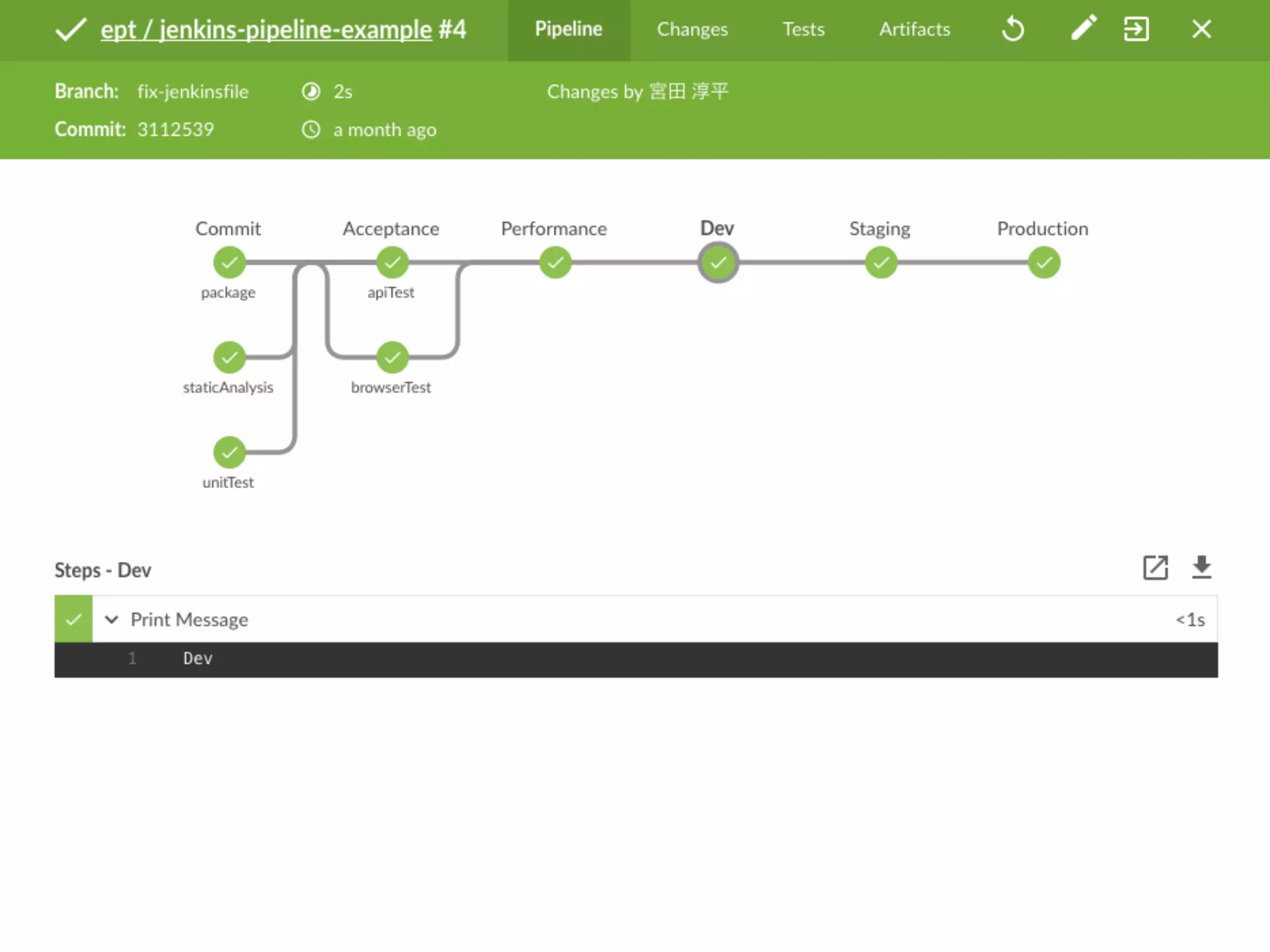
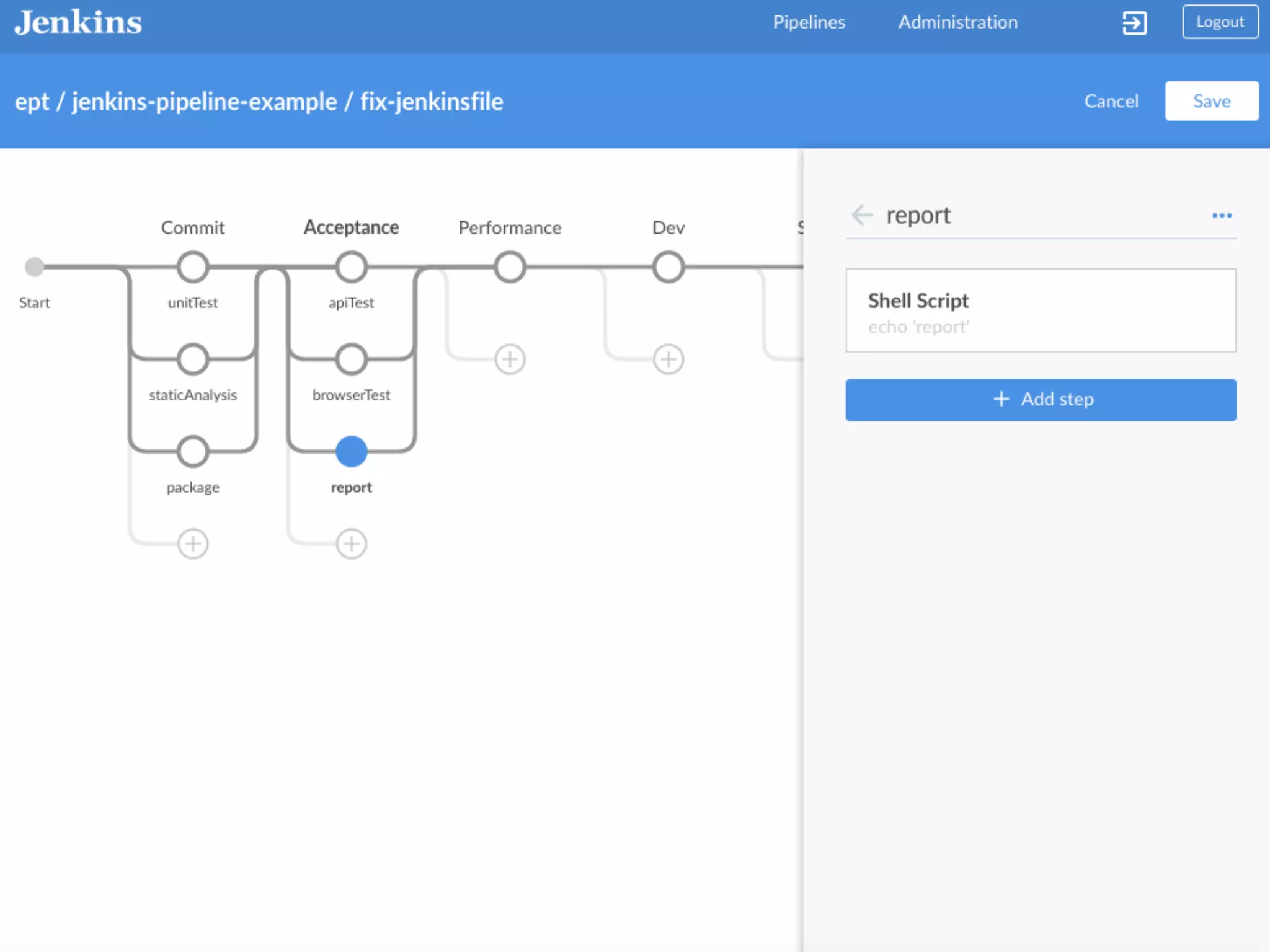
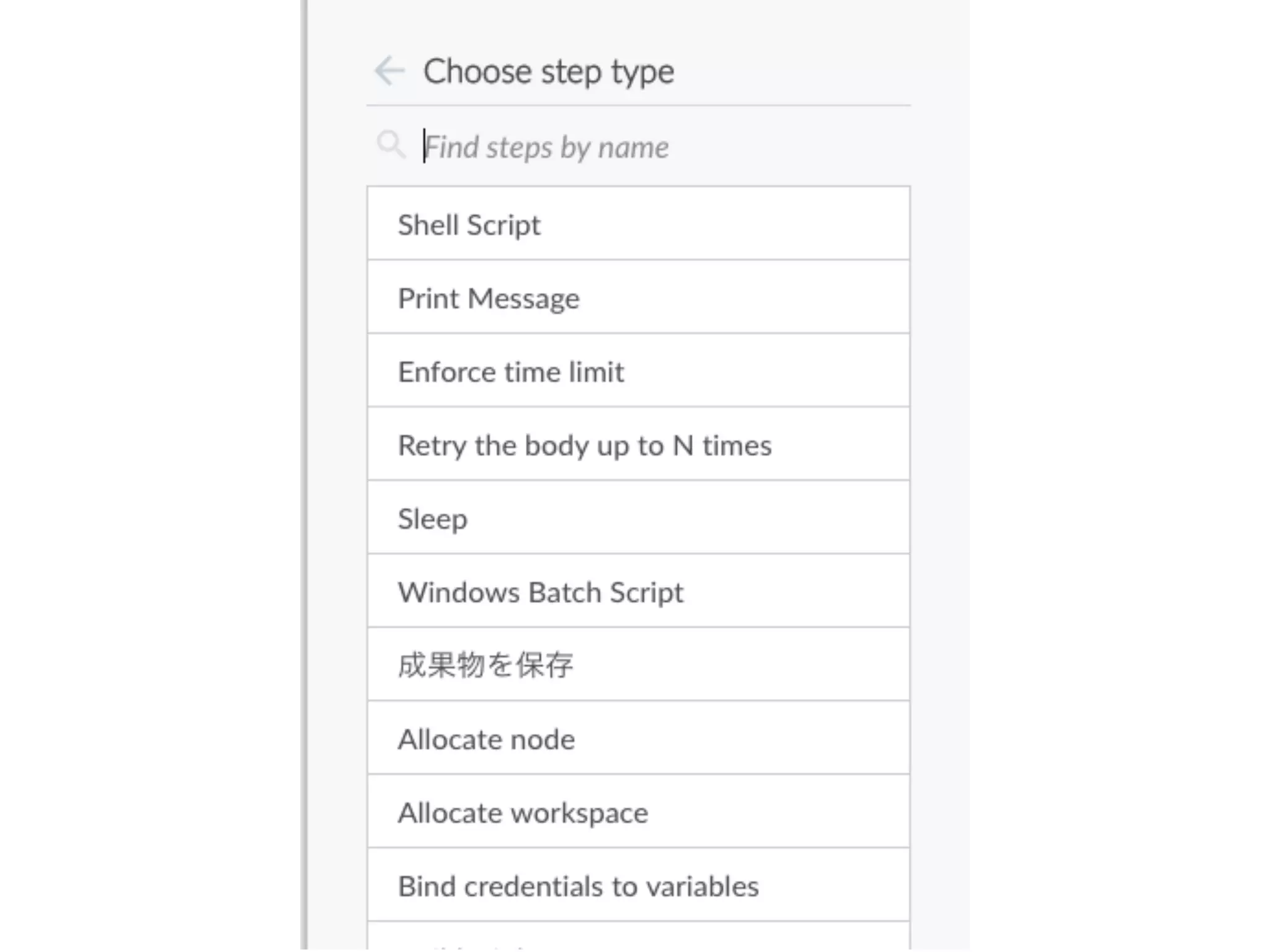
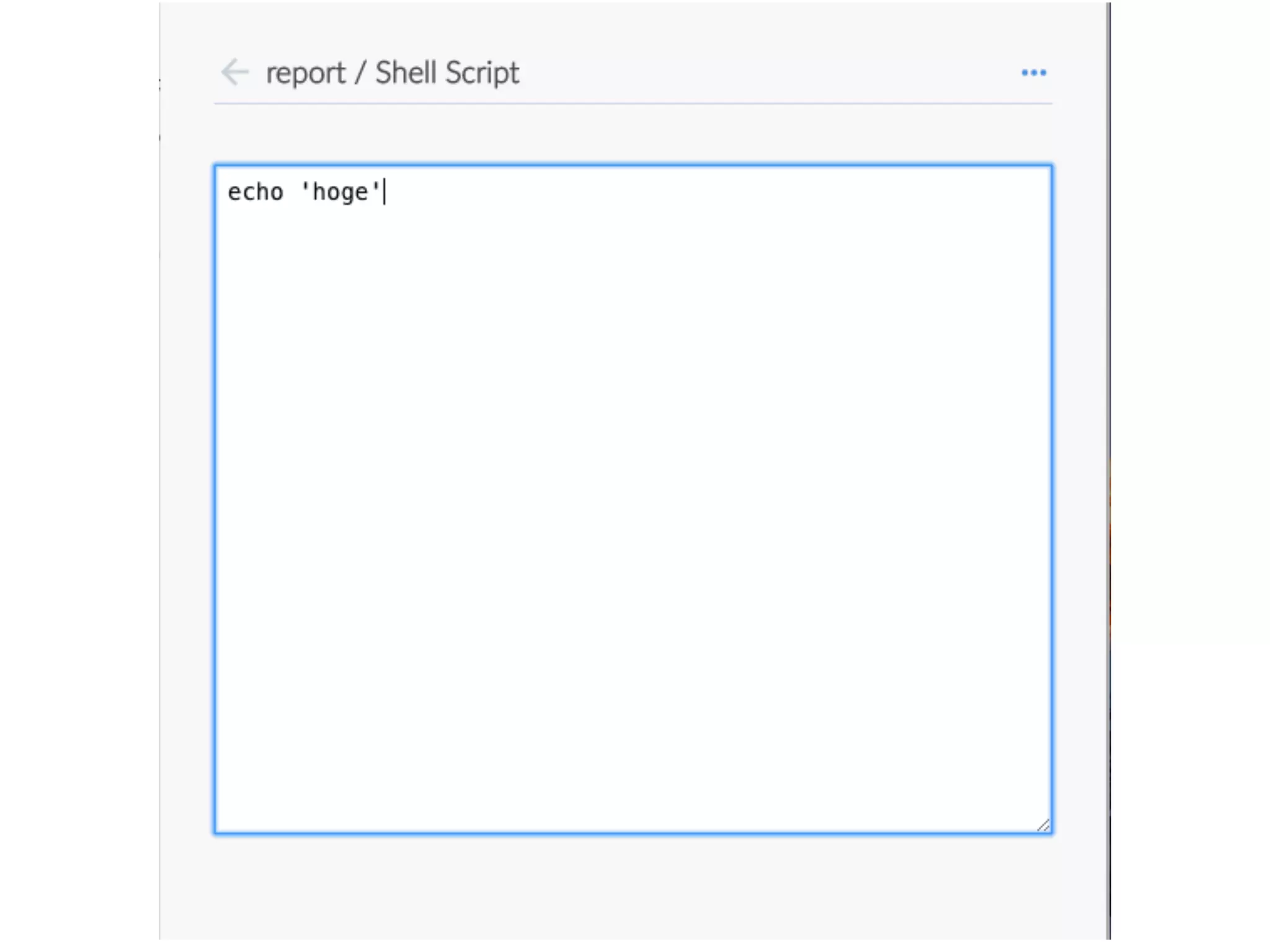
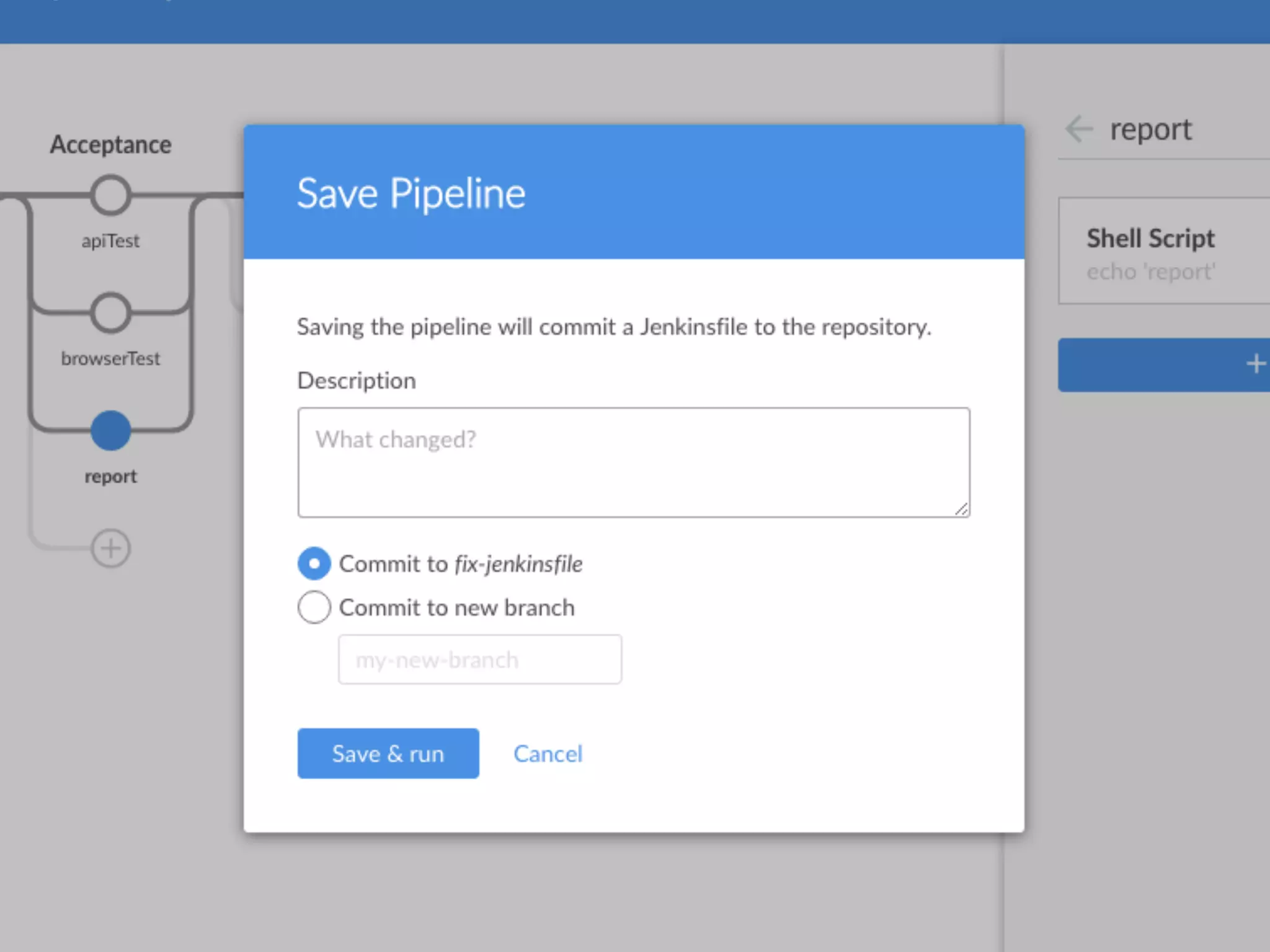
The document discusses Jenkins 2.0, highlighting its history, features, and advancements over Jenkins 1.0, including the introduction of pipelines and improved user experience. Key functionalities like scripted and declarative pipelines are elaborated with syntax examples, along with integrations and best practices. It also mentions the community resources and tools available for Jenkins users to enhance productivity and collaboration.