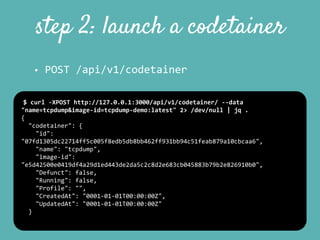
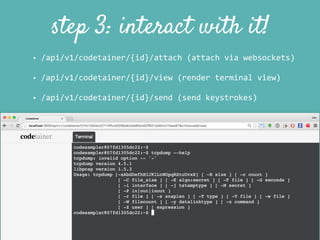
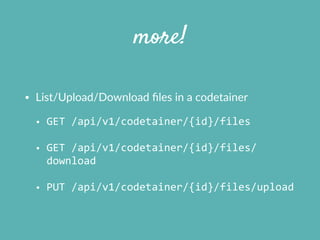
Codetainer is a browser-based sandbox for running Docker containers. It allows users to "try 'X' in your browser" for any X by running Docker containers in an isolated and programmable manner directly in the browser. Codetainer uses Docker APIs to launch and manage lightweight containers via a Go-based API server. Users can create and register Docker images, launch "codetainers" from those images, and interact with the codetainers through the browser via websockets, viewing terminals and sending keystrokes. Codetainer aims to provide a secure and flexible environment for use cases like tutorials, training, and remote management while addressing challenges around container introspection and security.







![starting the server
$
./bin/codetainer
server
Codetainer
10:34:16
[~INFO]
Initializing
Codetainer
(0.1.0)
Codetainer
10:34:16
[~INFO]
URL:
http://127.0.0.1:3000
$
./bin/codetainer
—help
usage:
Codetainer
[<flags>]
<command>
[<args>
...]
Flags:
-‐-‐help
Show
help
(also
see
-‐-‐help-‐long
and
-‐-‐help-‐man).
-‐v,
-‐-‐debug
Enable
debug
logging.
-‐-‐dev
Enable
dev
mode.
-‐q,
-‐-‐quiet
Remove
all
output
logging.](https://image.slidesharecdn.com/codetainertalkslides-150918165104-lva1-app6892/85/Codetainer-a-Docker-based-browser-code-sandbox-17-320.jpg)
![step 1: create an image
• Create your Docker image
• Register a Docker image for use in a codetainer
• POST
/api/v1/image
$
curl
-‐XPOST
http://127.0.0.1:3000/api/v1/image
-‐-‐data
"id=tcpdump-‐
demo:latest&description=hi"
2>
/dev/null
|
jq
.
{
"image":
{
"id":
"e5d42500e0419df4a29d1ed443de2da5c2c8d2e683cb045883b79b2e826910b0",
"command":
"",
"description":
"hi",
"Tags":
[
"tcpdump-‐demo:latest"
],
"CreatedAt":
"0001-‐01-‐01T00:00:00Z",
"UpdatedAt":
"0001-‐01-‐01T00:00:00Z",
"Enabled":
true
}](https://image.slidesharecdn.com/codetainertalkslides-150918165104-lva1-app6892/85/Codetainer-a-Docker-based-browser-code-sandbox-18-320.jpg)
![command-line too
$
./bin/codetainer
list
Found
2
codetainers.
-‐-‐
[4505c3c844a46f4966280cd6762d3512ba8c04ebd5cb550ba90732c11a5514ee]
lRf9QWOrhAYbNf4_PUdZ58DtKpfmTihu
(Running)
-‐-‐
[c2fce38a8ba86caf0e3f1462177809f14d905c26e3cd04ac907d7d18ad9a63f0]
R0bZK2O-‐1SWsoTp7a2gas1-‐cHjnFIlf_
(Running)
$
./bin/codetainer
image
register
ubuntu:14.04
Codetainer
08:01:31
[~INFO]
Registering
New
Image:
&{91e54dfb11794fad694460162bf0cb0a4fa710cfa3f60979c177d920813e
267c
[ubuntu:14.04]
0001-‐01-‐01
00:00:00
+0000
UTC
0001-‐01-‐01
00:00:00
+0000
UTC
true}
odetainer
08:01:31
[~INFO]
Registration
succeeded.](https://image.slidesharecdn.com/codetainertalkslides-150918165104-lva1-app6892/85/Codetainer-a-Docker-based-browser-code-sandbox-22-320.jpg)


![{
"Config":
{
"NetworkDisabled":
true
},
"HostConfig":
{
"Privileged":
false,
"ReadonlyRootfs":
true,
"Memory":
1000000000,
"Ulimits":
[{
"Name":
"nofile",
"Soft":
1024,
"Hard":
2048
}]
}
limiting a codetainer’s permissions using
profiles
$
./bin/codetainer
profile
register
./
secure.json
secure
2015/09/18
10:52:54
Created
profile
with
id=767653c7-‐8fb6-‐4f78-‐bfcf-‐3853bbe6df64:
2015/09/18
10:52:54
-‐-‐
2015/09/18
10:52:54
{
"Config":
{
"NetworkDisabled":
true
},
"HostConfig":
{
• pass
codetainer-‐profile-‐id
to
POST
/api/v1/
codetainer
when
creating
a
codetainer
secure.json](https://image.slidesharecdn.com/codetainertalkslides-150918165104-lva1-app6892/85/Codetainer-a-Docker-based-browser-code-sandbox-25-320.jpg)