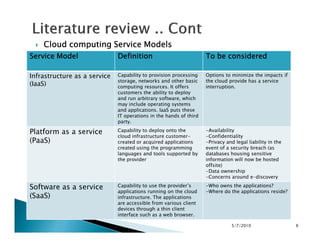
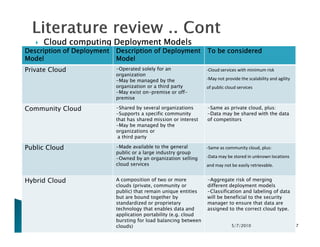
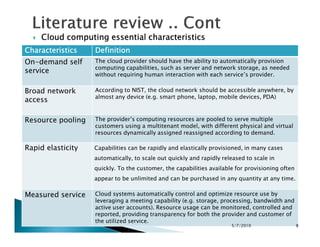
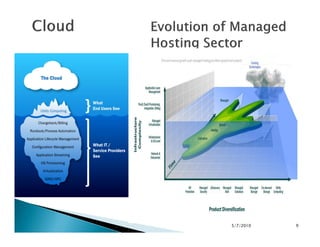
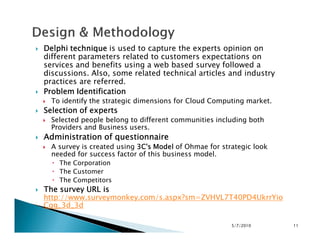
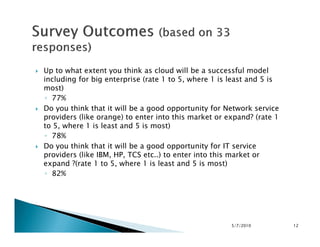
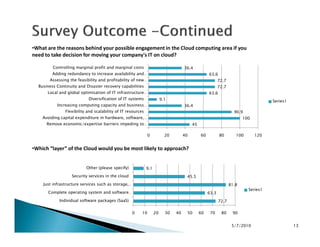
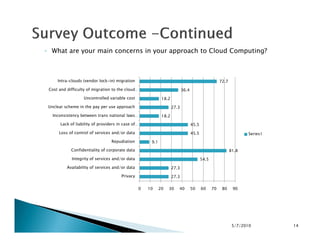
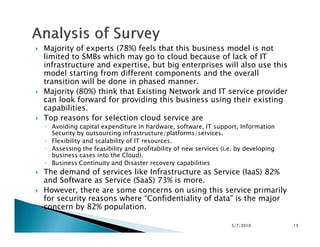
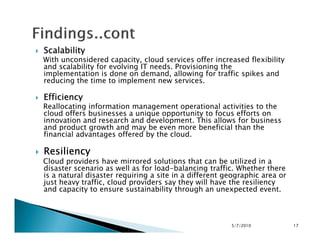
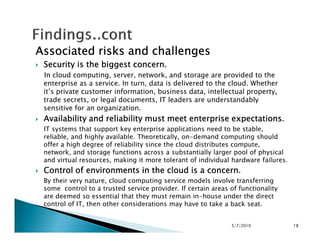
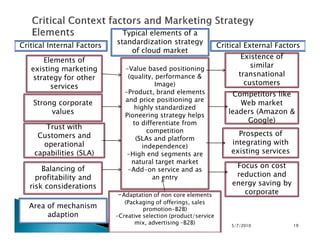
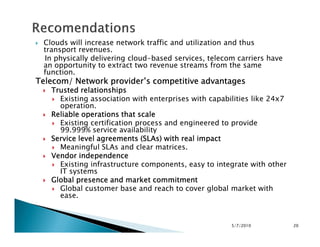
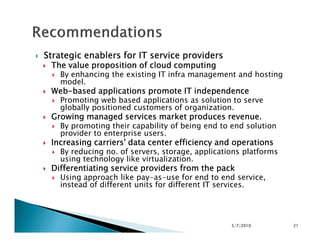
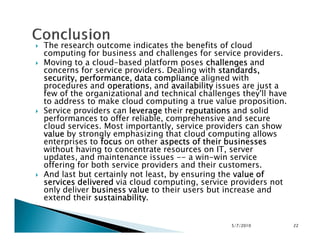
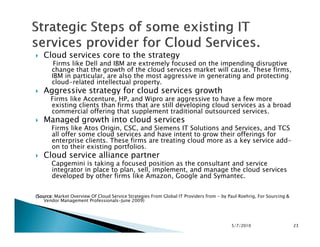
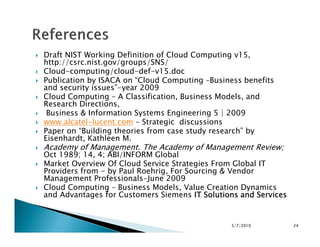
This document discusses strategic dimensions for network and IT service providers entering the cloud computing market. It conducted a survey of experts on both the demand and supply sides of the industry. The survey found that cloud computing is seen as a good opportunity for both network and IT service providers to expand into. Experts said the top benefits of cloud computing are flexibility, scalability, cost savings, and business continuity. However, security and data confidentiality were cited as major concerns. The document provides recommendations on strategic positioning in areas like value proposition, branding, and customization to differentiate in the cloud computing market.