Case study: M2M Telematics Solution - Happiest Minds
•
2 likes•468 views
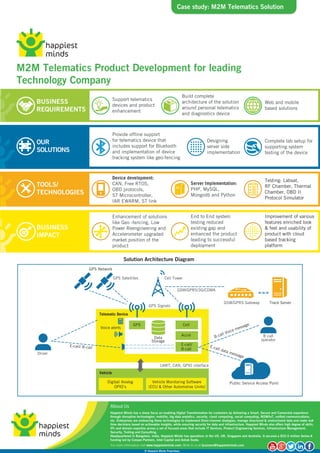
This case study explains, how our M2M Telematics Product Development for leading technology company enhanced the product leading to successful deployment.
Report
Share
Report
Share
Download to read offline
Recommended
Digital Experience: An Overview of Our Competency in Digital Transformation a...

Digital Experience: An Overview of Our Competency in Digital Transformation a...Embitel Technologies (I) PVT LTD
Leverage our competency in Cloud Technology, mobile app development, UI/UX design to build an impeccable Digital Experience for your business. Check out our services and expertise in AEM, WP Engine, Drupal and more.ISOBUS Software Stack Solution

The primary goal of the ISOBUS software stack is to standardize communication between the tractor Control Unit (tractor ECU) , the implement control unit (automotive Electronic Control Unit), Virtual Terminal and Web-based or Mobile Application.
ISOBUS stack is a software protocol complaint to ISO 11783 standard.
https://www.embitel.com/blog/embedded-blog/what-is-isobus-learn-about-its-architecture-and-diagnostic-applications
ISOBUS Software Stack Integration Services

ISOBUS software stack is a pre-packaged software solution developed in compliance with ISO 11783 standard.
This software stack enables and manages the in-vehicle network communication between the agricultural tractor ECUs and implements ECUs.
https://www.embitel.com/isobus-software-stack-integration-services
ECU Reprogramming Software Service

Bootloader software development advancement administrations for car ECU re-programming. Use the advantages of our restrictive blaze bootloader arrangement. Car programming administrations organization in Bangalore.
https://www.embitel.com/flash-bootloader-solutions-for-ecu-re-programming
J1939 Stack Source Code

Our J1939 software development team has shared a placid walk-through of the basic functions that needs to be tested, of each layer of the protocol stack to ensure that you purchase a quality J1939 source code.
J1939 stack is a software solution developed to support seamless communication and diagnostic services within the in-vehicle network (based on CAN bus protocol).
https://www.embitel.com/blog/embedded-blog/how-to-test-quality-of-j1939-source-code
ECU Flashing: Flash Bootloaders that Facilitate ECU Reprogramming

When Automotive Electronics was in its nascent stage, software engineers had not fully utilized the capabilities of a Flash Bootloader software. One Flash Bootloader design doesn’t fit the bill for different business use-cases & automotive applications.
https://www.embitel.com/blog/embedded-blog/different-types-of-flash-bootloader-that-facilitate-ecu-reprogramming
Recommended
Digital Experience: An Overview of Our Competency in Digital Transformation a...

Digital Experience: An Overview of Our Competency in Digital Transformation a...Embitel Technologies (I) PVT LTD
Leverage our competency in Cloud Technology, mobile app development, UI/UX design to build an impeccable Digital Experience for your business. Check out our services and expertise in AEM, WP Engine, Drupal and more.ISOBUS Software Stack Solution

The primary goal of the ISOBUS software stack is to standardize communication between the tractor Control Unit (tractor ECU) , the implement control unit (automotive Electronic Control Unit), Virtual Terminal and Web-based or Mobile Application.
ISOBUS stack is a software protocol complaint to ISO 11783 standard.
https://www.embitel.com/blog/embedded-blog/what-is-isobus-learn-about-its-architecture-and-diagnostic-applications
ISOBUS Software Stack Integration Services

ISOBUS software stack is a pre-packaged software solution developed in compliance with ISO 11783 standard.
This software stack enables and manages the in-vehicle network communication between the agricultural tractor ECUs and implements ECUs.
https://www.embitel.com/isobus-software-stack-integration-services
ECU Reprogramming Software Service

Bootloader software development advancement administrations for car ECU re-programming. Use the advantages of our restrictive blaze bootloader arrangement. Car programming administrations organization in Bangalore.
https://www.embitel.com/flash-bootloader-solutions-for-ecu-re-programming
J1939 Stack Source Code

Our J1939 software development team has shared a placid walk-through of the basic functions that needs to be tested, of each layer of the protocol stack to ensure that you purchase a quality J1939 source code.
J1939 stack is a software solution developed to support seamless communication and diagnostic services within the in-vehicle network (based on CAN bus protocol).
https://www.embitel.com/blog/embedded-blog/how-to-test-quality-of-j1939-source-code
ECU Flashing: Flash Bootloaders that Facilitate ECU Reprogramming

When Automotive Electronics was in its nascent stage, software engineers had not fully utilized the capabilities of a Flash Bootloader software. One Flash Bootloader design doesn’t fit the bill for different business use-cases & automotive applications.
https://www.embitel.com/blog/embedded-blog/different-types-of-flash-bootloader-that-facilitate-ecu-reprogramming
FAQs’ for Unit, Integration and Functional Testing Services

Support for Unit Testing, Integration Testing and Functional (HIL, MIL, SIL) Testing. Our Software & Hardware Testing teams have in-depth Automotive Domain expertise.
https://www.embitel.com/automotive-ecu-testing-and-verification-services
What is Telematics & How Does It Work?

Telematics is a disruptive automotive technology that utilizes IT and communication protocols to send, receive and store information pertaining to remote vehicles.
Telematics can be effectively used in various industries such as agriculture & forestry, construction, manufacturing, freight & delivery, retail, finance/insurance, mining, etc.
https://www.embitel.com/iot-insights/what-is-telematics
Why ignoring firmware over the-air (fota) updates in automotive ecu can be a ...

Why ignoring firmware over the-air (fota) updates in automotive ecu can be a ...Embitel Technologies (I) PVT LTD
FOTA Automotive: With Firmware Over-The-Air (FOTA) Upgrade module in place, a vehicle recall to replace a faulty software can be avoided. We discuss other benefits of FOTA update & also show its criticality with the help of some car recall instances.In-Vehicle Infotainment (IVI) System for Two-Wheelers

The much awaited In-Vehicle Infotainment system in Two-Wheelers has been taking long technology strides . In this blog, we will share with you how an infotainment in two-wheelers works, the various applications in electric bikes and the future trends to look for.
https://www.embitel.com/blog/embedded-blog/a-curious-case-of-in-vehicle-infotainment-system-for-two-wheelers
J1939 and OBD2 Stack Integrations With IoT Platform for Fleet Safety

J1939 and OBD2 Stack Integrations With IoT Platform for Fleet SafetyEmbitel Technologies (I) PVT LTD
Our automotive software developers implemented integration of SAE J1939 and OBD2 stacks with Freescale/NXP MCS9S12G controller. Our customer was looking for an automotive embedded systems partner with expertise in vehicle diagnostics, J1939 and OBD2 stacks integration and CAN/LIN interface development.
https://www.embitel.com/product-engineering2/embedded-casestudies/j1939-and-obd2-stack-integrations-with-iot-platform-for-fleet-safety
Migration from CAN 2.0 to CAN FD

CAN 2.0 to CAN FD: Realize for what reason CAN FD underpins bigger payload than CAN 2.0 and how might you conquer the difficulties identified with relocation from CAN 2.0 to CAN FD. This blog reveals some insight into Mixed Networks and External CAN FD controller.
https://www.embitel.com/blog/embedded-blog/challenges-your-automotive-team-may-confront-during-migration-from-can-2-0-to-can-fd
The Current State of Automotive Security by Chris Valasek

Automotive computers, or Electronic Control Units (ECU), were originally introduced to help with fuel efficiency and emissions problems of the 1970s but evolved into integral parts of in-car entertainment, safety controls, and enhanced automotive functionality. This presentation will examine some controls in two modern automobiles from a security researcherís point of view. We will first cover the requisite tools and software needed to analyze a Controller Area Network (CAN) bus. Secondly, we will demo software to show how data can be read and written to the CAN bus. Then we will show how certain proprietary messages can be replayed by a device hooked up to an ODB-II connection to perform critical car functionality, such as braking and steering. Finally, weíll discuss aspects of reading and modifying the firmware of ECUs installed in todayís modern automobile.
Chris Valasek
Christopher Valasek is the Director of Security Intelligence at IOActive, an industry leader in comprehensive computer security services. Valasek specializes in offensive research methodologies with a focus in reverse engineering and exploitation. Valasek is known for his extensive research in the automotive field and his exploitation and reverse engineering of Windows. Valasek is also the Chairman of SummerCon, the nation’s oldest hacker conference. He holds a B.S. in Computer Science from the University of Pittsburgh.
UDS: Vehicle Diagnostics in AUTOSAR Software Architecture 

UDS Vehicle Diagnostics: This blog encourages you comprehend the AUTOSAR software standard consistence for car applications. Here we share with you the points of interest of the usage of UDS based Vehicle Diagnostics in AUTOSAR Base Software module.
External ppt

M.tech Project on NOVEL SECURITY ENABLED ZONE SENSING SYSTEM FOR VEHICLE USING WIRELESS TECHNOLOGY
Improvised functional tests for automotive testing 

Best practices paper on "Improvised functional tests for automotive testing (TRACK III –Embedded Application Testing)" By Prasad Kumaran & Vijesh Kumar Bhupathi Raju from Logica.Paper submitted during QAI's 12th International Software Testing Conference
Network Security for Automotive Embedded Systems

In the past decade, the automotive industry has undergone tremendous technological changes in terms of connectivity and personal mobility.
Modern cars are more and more like computers rather than mechanical products. It is not uncommon for modern cars to have remote connectivity and high-tech features, such as touch-sensitive dashboards, which can keep themselves up to date through regular software updates.
In the automotive industry, the consequences can be severe-if safety-related functions are compromised, it can cause injury or death, and if a large number of vehicles are threatened or required to be recalled, it can cause serious damage to reputation.
In the new digital age, due to the vehicle’s wireless communication capabilities, mobile devices (such as cellular phones or tablets connected to the vehicle via USB, Bluetooth or Wi-Fi) may have vulnerabilities inside or inside, and this problem is becoming more and more disturbing Third-party equipment connected through the vehicle diagnostic port.
Tonex's Automotive Cybersecurity Training
Automotive Cyber Security Training (Network Security for Automotive Embedded Systems) is a 3-day course. Participants will discuss the basic principles of embedded systems and the application of cyber security in vehicles to illustrate unique vulnerabilities that are commonly exploited.
Who Should Attend:
Chief Product Security Officers (CPSO)
Control Platform
Developers working with embedded systems
Embedded software engineers and testers
Ethernet and CAN Bus Software Engineers and Testers, Hardware Testers
Functional Safety Electrical Engineering
Information security professionals
Machine Learning Platform Engineers and Managers
Mechatronics Engineer, Sensor Cleaning Engineers and PMs
The Main Points of This Course Include:
Check how to adapt to network security in automotive embedded systems
The basics of automotive network security.
Automotive network security, threats, threat agents/vectors, vulnerability and risk assessment; defense in depth, etc.
Embedded system foundation
Basic knowledge of automotive embedded system product design cycle, project management, production design, V&V and O&M.
And many more.
Course Outline:
Cybersecurity Applied to Automotive
Introduction to Embedded Systems and their Applications in Automotive
Automotive Cybersecurity Strategies
Automotive Embedded System Vulnerability Analysis
Automotive Cybersecurity and Layers of Protection
Cybersecurity Best Practices for Modern Vehicles
Standards Development and Best Practices
Securing Automotive Embedded Systems Interfaces and Protocols
Cybersecurity Attacks and Best Mitigation Practices for Automotive Embedded Systems
Evaluating Cybersecurity Practices for Modern Vehicles
Learn More:
https://www.tonex.com/training-courses/automotive-cybersecurity-training-course/
Inteliģentās transporta sistēmas: Britu pieredze, Latvijas plāni

Lielbritānija novērtē Latvijas potenciālu kā inteliģento transporta tehnoloģiju attīstības centram un uzsāk semināru ciklu pieredzes apmaiņai šajā jomā, atklājot semināru ciklu “Inteliģentās transporta sistēmas”, apliecināja Lielbritānijas vēstnieka Latvijā vietniece Sāra Hārpere.
Current state of automotive network security

Many electronic devices have been used by automobiles.These devices are connected each other and communicate to control automobile. Recent years, automotive network has been connected to smartphones and the internet. It makes new threats turn up. This slides summarizes how automotive network security have been and what is expected as incoming threats.
5 Things to Know about the Railway Data Center menRDC

menRDC is an open computer platform based on modern IT standards that covers all data processing and communication on a train and in train-land communication, and meets all the requirements of EN 50155. In the spirit of “Mobility 4.0”, the menRDC is a “connected device” that interacts with the participants in the IoT (Internet of Things).
Singapore Electronic Road Pricing System

This is about...
1.Introduction on the electronic toll system generally.
2.Brief introduction to what is ERP system in Singapore(brief),How it is working in our Road?
3.About Singapore Land Transport Authority.
4.About The old system before ERP- called Singapore Area licensing Scheme
5.Change after the implementation of ERP
5 Things to Know about the Train Control System menTCS

menTCS is an open computer platform based upon modern IT standards that covers all safety-critical applications on a train and wayside. It is SIL 4 certifiable and comes with pre-certified hardware in combination with pre-certified software and corresponding certificates from TÜV SÜD, drastically reducing the time of the certification process.
Telematics and Big Data: Next Generation Automotive Technology

This whitepaper explores the telematics ecosystem and the key players within it. It also delves into some challenges and road ahead for LTE technology and Big Data Analytics as two key enablers that will drive the success of telematics.
Insurance Telematics Study

With 2 million customers worldwide, Usage-based Insurance has passed its tipping point, and is revolutionizing the insurance industry.
The 405-page Insurance Telematics Study is set to become the reference document for the industry. It describes how the changes impact each part of the value chain and the strategic implications.
More Related Content
What's hot
FAQs’ for Unit, Integration and Functional Testing Services

Support for Unit Testing, Integration Testing and Functional (HIL, MIL, SIL) Testing. Our Software & Hardware Testing teams have in-depth Automotive Domain expertise.
https://www.embitel.com/automotive-ecu-testing-and-verification-services
What is Telematics & How Does It Work?

Telematics is a disruptive automotive technology that utilizes IT and communication protocols to send, receive and store information pertaining to remote vehicles.
Telematics can be effectively used in various industries such as agriculture & forestry, construction, manufacturing, freight & delivery, retail, finance/insurance, mining, etc.
https://www.embitel.com/iot-insights/what-is-telematics
Why ignoring firmware over the-air (fota) updates in automotive ecu can be a ...

Why ignoring firmware over the-air (fota) updates in automotive ecu can be a ...Embitel Technologies (I) PVT LTD
FOTA Automotive: With Firmware Over-The-Air (FOTA) Upgrade module in place, a vehicle recall to replace a faulty software can be avoided. We discuss other benefits of FOTA update & also show its criticality with the help of some car recall instances.In-Vehicle Infotainment (IVI) System for Two-Wheelers

The much awaited In-Vehicle Infotainment system in Two-Wheelers has been taking long technology strides . In this blog, we will share with you how an infotainment in two-wheelers works, the various applications in electric bikes and the future trends to look for.
https://www.embitel.com/blog/embedded-blog/a-curious-case-of-in-vehicle-infotainment-system-for-two-wheelers
J1939 and OBD2 Stack Integrations With IoT Platform for Fleet Safety

J1939 and OBD2 Stack Integrations With IoT Platform for Fleet SafetyEmbitel Technologies (I) PVT LTD
Our automotive software developers implemented integration of SAE J1939 and OBD2 stacks with Freescale/NXP MCS9S12G controller. Our customer was looking for an automotive embedded systems partner with expertise in vehicle diagnostics, J1939 and OBD2 stacks integration and CAN/LIN interface development.
https://www.embitel.com/product-engineering2/embedded-casestudies/j1939-and-obd2-stack-integrations-with-iot-platform-for-fleet-safety
Migration from CAN 2.0 to CAN FD

CAN 2.0 to CAN FD: Realize for what reason CAN FD underpins bigger payload than CAN 2.0 and how might you conquer the difficulties identified with relocation from CAN 2.0 to CAN FD. This blog reveals some insight into Mixed Networks and External CAN FD controller.
https://www.embitel.com/blog/embedded-blog/challenges-your-automotive-team-may-confront-during-migration-from-can-2-0-to-can-fd
The Current State of Automotive Security by Chris Valasek

Automotive computers, or Electronic Control Units (ECU), were originally introduced to help with fuel efficiency and emissions problems of the 1970s but evolved into integral parts of in-car entertainment, safety controls, and enhanced automotive functionality. This presentation will examine some controls in two modern automobiles from a security researcherís point of view. We will first cover the requisite tools and software needed to analyze a Controller Area Network (CAN) bus. Secondly, we will demo software to show how data can be read and written to the CAN bus. Then we will show how certain proprietary messages can be replayed by a device hooked up to an ODB-II connection to perform critical car functionality, such as braking and steering. Finally, weíll discuss aspects of reading and modifying the firmware of ECUs installed in todayís modern automobile.
Chris Valasek
Christopher Valasek is the Director of Security Intelligence at IOActive, an industry leader in comprehensive computer security services. Valasek specializes in offensive research methodologies with a focus in reverse engineering and exploitation. Valasek is known for his extensive research in the automotive field and his exploitation and reverse engineering of Windows. Valasek is also the Chairman of SummerCon, the nation’s oldest hacker conference. He holds a B.S. in Computer Science from the University of Pittsburgh.
UDS: Vehicle Diagnostics in AUTOSAR Software Architecture 

UDS Vehicle Diagnostics: This blog encourages you comprehend the AUTOSAR software standard consistence for car applications. Here we share with you the points of interest of the usage of UDS based Vehicle Diagnostics in AUTOSAR Base Software module.
External ppt

M.tech Project on NOVEL SECURITY ENABLED ZONE SENSING SYSTEM FOR VEHICLE USING WIRELESS TECHNOLOGY
Improvised functional tests for automotive testing 

Best practices paper on "Improvised functional tests for automotive testing (TRACK III –Embedded Application Testing)" By Prasad Kumaran & Vijesh Kumar Bhupathi Raju from Logica.Paper submitted during QAI's 12th International Software Testing Conference
Network Security for Automotive Embedded Systems

In the past decade, the automotive industry has undergone tremendous technological changes in terms of connectivity and personal mobility.
Modern cars are more and more like computers rather than mechanical products. It is not uncommon for modern cars to have remote connectivity and high-tech features, such as touch-sensitive dashboards, which can keep themselves up to date through regular software updates.
In the automotive industry, the consequences can be severe-if safety-related functions are compromised, it can cause injury or death, and if a large number of vehicles are threatened or required to be recalled, it can cause serious damage to reputation.
In the new digital age, due to the vehicle’s wireless communication capabilities, mobile devices (such as cellular phones or tablets connected to the vehicle via USB, Bluetooth or Wi-Fi) may have vulnerabilities inside or inside, and this problem is becoming more and more disturbing Third-party equipment connected through the vehicle diagnostic port.
Tonex's Automotive Cybersecurity Training
Automotive Cyber Security Training (Network Security for Automotive Embedded Systems) is a 3-day course. Participants will discuss the basic principles of embedded systems and the application of cyber security in vehicles to illustrate unique vulnerabilities that are commonly exploited.
Who Should Attend:
Chief Product Security Officers (CPSO)
Control Platform
Developers working with embedded systems
Embedded software engineers and testers
Ethernet and CAN Bus Software Engineers and Testers, Hardware Testers
Functional Safety Electrical Engineering
Information security professionals
Machine Learning Platform Engineers and Managers
Mechatronics Engineer, Sensor Cleaning Engineers and PMs
The Main Points of This Course Include:
Check how to adapt to network security in automotive embedded systems
The basics of automotive network security.
Automotive network security, threats, threat agents/vectors, vulnerability and risk assessment; defense in depth, etc.
Embedded system foundation
Basic knowledge of automotive embedded system product design cycle, project management, production design, V&V and O&M.
And many more.
Course Outline:
Cybersecurity Applied to Automotive
Introduction to Embedded Systems and their Applications in Automotive
Automotive Cybersecurity Strategies
Automotive Embedded System Vulnerability Analysis
Automotive Cybersecurity and Layers of Protection
Cybersecurity Best Practices for Modern Vehicles
Standards Development and Best Practices
Securing Automotive Embedded Systems Interfaces and Protocols
Cybersecurity Attacks and Best Mitigation Practices for Automotive Embedded Systems
Evaluating Cybersecurity Practices for Modern Vehicles
Learn More:
https://www.tonex.com/training-courses/automotive-cybersecurity-training-course/
Inteliģentās transporta sistēmas: Britu pieredze, Latvijas plāni

Lielbritānija novērtē Latvijas potenciālu kā inteliģento transporta tehnoloģiju attīstības centram un uzsāk semināru ciklu pieredzes apmaiņai šajā jomā, atklājot semināru ciklu “Inteliģentās transporta sistēmas”, apliecināja Lielbritānijas vēstnieka Latvijā vietniece Sāra Hārpere.
Current state of automotive network security

Many electronic devices have been used by automobiles.These devices are connected each other and communicate to control automobile. Recent years, automotive network has been connected to smartphones and the internet. It makes new threats turn up. This slides summarizes how automotive network security have been and what is expected as incoming threats.
5 Things to Know about the Railway Data Center menRDC

menRDC is an open computer platform based on modern IT standards that covers all data processing and communication on a train and in train-land communication, and meets all the requirements of EN 50155. In the spirit of “Mobility 4.0”, the menRDC is a “connected device” that interacts with the participants in the IoT (Internet of Things).
Singapore Electronic Road Pricing System

This is about...
1.Introduction on the electronic toll system generally.
2.Brief introduction to what is ERP system in Singapore(brief),How it is working in our Road?
3.About Singapore Land Transport Authority.
4.About The old system before ERP- called Singapore Area licensing Scheme
5.Change after the implementation of ERP
5 Things to Know about the Train Control System menTCS

menTCS is an open computer platform based upon modern IT standards that covers all safety-critical applications on a train and wayside. It is SIL 4 certifiable and comes with pre-certified hardware in combination with pre-certified software and corresponding certificates from TÜV SÜD, drastically reducing the time of the certification process.
What's hot (20)
FAQs’ for Unit, Integration and Functional Testing Services

FAQs’ for Unit, Integration and Functional Testing Services
Why ignoring firmware over the-air (fota) updates in automotive ecu can be a ...

Why ignoring firmware over the-air (fota) updates in automotive ecu can be a ...
In-Vehicle Infotainment (IVI) System for Two-Wheelers

In-Vehicle Infotainment (IVI) System for Two-Wheelers
J1939 and OBD2 Stack Integrations With IoT Platform for Fleet Safety

J1939 and OBD2 Stack Integrations With IoT Platform for Fleet Safety
The Current State of Automotive Security by Chris Valasek

The Current State of Automotive Security by Chris Valasek
UDS: Vehicle Diagnostics in AUTOSAR Software Architecture 

UDS: Vehicle Diagnostics in AUTOSAR Software Architecture
Improvised functional tests for automotive testing 

Improvised functional tests for automotive testing
Inteliģentās transporta sistēmas: Britu pieredze, Latvijas plāni

Inteliģentās transporta sistēmas: Britu pieredze, Latvijas plāni
5 Things to Know about the Railway Data Center menRDC

5 Things to Know about the Railway Data Center menRDC
5 Things to Know about the Train Control System menTCS

5 Things to Know about the Train Control System menTCS
ERM Advanced Telematics - Company Presentation 2018

ERM Advanced Telematics - Company Presentation 2018
Viewers also liked
Telematics and Big Data: Next Generation Automotive Technology

This whitepaper explores the telematics ecosystem and the key players within it. It also delves into some challenges and road ahead for LTE technology and Big Data Analytics as two key enablers that will drive the success of telematics.
Insurance Telematics Study

With 2 million customers worldwide, Usage-based Insurance has passed its tipping point, and is revolutionizing the insurance industry.
The 405-page Insurance Telematics Study is set to become the reference document for the industry. It describes how the changes impact each part of the value chain and the strategic implications.
Using FIWARE and Microsoft Azure for the development of IoT solutions

The presentation on the topic: application of FIWARE and Microsoft Azure platform on the example of the smart city based IoT solutions made by DunavNET and comparative analysis of the services and the corresponding components of the platforms.
Presentation by Nebojša Stojanović at DaFED.
Case study: In-Vehicle Telematics Solution - Happiest Minds

Learn more in this case study about Consumer Vehicle Accessories Solution for Leading Semiconductor Company.
CONNECTED CAR OUTLOOK by THOMAS GRONES

The IoT is growing fast in interest and here is an updated Outlook on connected car vehicles and connected car scenario. it's not the Whole picture but just an Outlook on some areas of personal interest where focus might need more attention on the market.
The UAE Telematics System- A Flexible End-to-End Solution - Thomas Walz, IT A...

OSGi World Congress 2005
End-to-End and e-Business Value from the Telematics Reference Implementation ...

OSGi World Congress 2004
Big Data Expo 2015 - TomTom The intenet of things

Big Data use case by TomTom Telematics
TomTom Telematics is een afdeling binnen TomTom die zich bezig houdt met connetced vehicle technology voor B2B toepassingen. Niet alleen voor brandstof besparingen en minder schades maar ook voor een efficienter en papierloos business process.
In deze presentatie vertelt George de Boer over hoe gaat TomTom om gaat met het verwerken van miljarden datapunten voor het maken van een accurate bezorgtijd voor uw boodschappen. Daarnaast hoe big data helpt bij het goedkoper maken van autoverzekering. Een presentatie over het succesvol en dagelijks gebruik van connected vehicle data.
How can Insights on Sustainable Transport Solutions Lead to Customer Value? -...

A Volvo case on pioneering Big data, telematics and multi-modal mobility management.
Presenter: Dr. Magnus Kuschel, Head of Service Innovation, Volvo Group Telematics and Robert Valton, Project Manager Big Data, Volvo IT.
Har du frågor eller vill du ha en kopia av presentationen? Kontakta Jesper Carlsten på bit.ly/SB13Jesper
Mer från dagen på http://bit.ly/sb13se
Evolution of a Connected Business 

What is a Connected Business? Its a business where all parts of the value chain can interact digitally.
This presentation talks about how to create a Connected Business, how APIs, Cloud and Mobile can create and enhance new business models.
Covered in the session is:
* The importance of APIs to your organization
* How Cloud development can be transformative
* How to integrate Mobile and IoT to create a Connected Business
* How companies have connected their ecosystems
IoT for V2V and Connected Car - AW Megatrends `14 panel

IoT for V2V and the connected car from my panel with Intel, SEMA, CVTA, GENIVI at AW Megatrends `2014 March 18th.
Case study: Building a business case for cloud, migration in practice and spr...

A talk delivered by Rocco Labellarte, Head of Technology and Change Delivery, Corporate Services at Royal Borough of Windsor and Maidenhead. This presentation was given at Cloud Control: Implementing Cloud Computing, a seminar hosted by Civil Service World and Eduserv.
Topics covered include the process of building a case for cloud, the benefits and lessons learnt.
Constructing the Case for Cloud

How do you construct the case for Cloud Computing?
Not only is Cloud the technology du jour- but it is delivered on a Pay-as-you-go basis, shifting the payment from Capital Expenditure to Operational Expenditure (capex to opex).
But that's only the initial attraction of the Cloud and isn't the true benefit of Cloud. Build your case on the financial shift, and your initiative could fail.
If you understand the real, transformational benefits of Cloud you'll understand how to sell it into your organisation.
Because Cloud computing has the ability to re-align IT into business enabling superheroes!
REST-Enabling Enterprise Data in the Mobile Era 

Ben Busse, product lead at DreamFactory, covers the importance of reusable REST APIs for enterprise mobile app development. Why are reusable APIs important, what are reusable APIs, and how do you use reusable APIs in practice. Ben gave this talk at the 2015 International PHP Conference in Berlin, Germany.
The Digital Enterprise

Booz Allen explains how Federal agencies can tap into the digital ecosystem to better connect with our citizens, warriors, and workforce.
Why You Should Move to the Cloud

Building the business case for Cloud Services ...
Total Cost of Ownership
Resource Costs
Time to value and ease of implementation
Access to innovation
Ability to try before you buy
Ongoing vendor accountability and engagement
Attractive commercial models
The Enterprise Business Case for Cloud Transformation: Introducing Everest Gr...

Everest Group is committed to helping leading enterprises navigate the opportunities and challenges associated with transformation and cloud migration. Based on extensive work with leading enterprises and cloud vendors, Everest Group has developed the first comprehensive set of analytics, frameworks and fact-based economic models for enterprise IT transformation and cloud migration. In this webinar, learn how Everest Group’s new Next Generation IT advisory services leverage these capabilities to help you.
Connected Car opportunities from a Telco’s Perspective

Dr. Bernhard Kirchmair - „Thesen und Tatsachen - Das vernetzte Fahrzeug aus Telko-Sicht"
Viewers also liked (20)
Telematics and Big Data: Next Generation Automotive Technology

Telematics and Big Data: Next Generation Automotive Technology
Using FIWARE and Microsoft Azure for the development of IoT solutions

Using FIWARE and Microsoft Azure for the development of IoT solutions
Case study: In-Vehicle Telematics Solution - Happiest Minds

Case study: In-Vehicle Telematics Solution - Happiest Minds
The UAE Telematics System- A Flexible End-to-End Solution - Thomas Walz, IT A...

The UAE Telematics System- A Flexible End-to-End Solution - Thomas Walz, IT A...
CASE STUDY: The evolution of the personal telematics market: Building a solut...

CASE STUDY: The evolution of the personal telematics market: Building a solut...
End-to-End and e-Business Value from the Telematics Reference Implementation ...

End-to-End and e-Business Value from the Telematics Reference Implementation ...
How can Insights on Sustainable Transport Solutions Lead to Customer Value? -...

How can Insights on Sustainable Transport Solutions Lead to Customer Value? -...
IoT for V2V and Connected Car - AW Megatrends `14 panel

IoT for V2V and Connected Car - AW Megatrends `14 panel
Case study: Building a business case for cloud, migration in practice and spr...

Case study: Building a business case for cloud, migration in practice and spr...
The Enterprise Business Case for Cloud Transformation: Introducing Everest Gr...

The Enterprise Business Case for Cloud Transformation: Introducing Everest Gr...
Connected Car opportunities from a Telco’s Perspective

Connected Car opportunities from a Telco’s Perspective
Similar to Case study: M2M Telematics Solution - Happiest Minds
M2M in Transportation, Mining and Agriculture

Eurotech's M2M Offering for Transportation and Mobility
Rugged Devices and Solutions for Vehicles
Vertical Market Applications for Transportation, Agriculture and Mining.
Voip automation framework

To build an automation framework for testing VOIP devices against the Cloud based Unified Communication
solutions
ConnectM Corporate Overview (jan 2014)

ConnectM is a leading, global Machine-to-Machine (M2M) Technology Solutions, Business Intelligence (BI) and Services Company headquartered in Bangalore, India. With over 70,000 assets connected, ConnectM's Solution Delivery Platform(SDP) is a robust and proven technology. Our Pre-built applications are leveraged by over 40 customers to manage their assets/machines. ConnectM SDP and applications along with devices from its eco-system partners offer the customer a one-stop-shop for M2M needs.
ConnectM has delivered M2M solutions to various domains including Telecom, Energy, Utilities, Industrial, Construction, IT/ITES Enterprises and Transportation market segments.
ConnectM's solutions are powered by cutting edge M2M technology, and are designed to make significant, sustained and measurable business impact. ConnectM also offers services to its client to build complete solutions. ConnectM's strength is in its ability to offer domain specific analytics on the data collected and deliver actionable business intelligence.
Visiongain publishes report on: The 100 connected car companies to watch

: Analysis of Leading Suppliers & OEMs Involved in Tethered, Integrated & Embedded Solutions, In-Vehicle Technologies (IN-V), Telematics, Infotainment, Diagnostics, Connectivity, Safety, Navigation, UBI, Security & Vehicle to Everything (V2X) Communications
Happiest minds industrial iot capability

Internet of Things (IOT) – Our Focus
Contact:- narendra.kumar@happiestminds.com
Phone:- +44-7926102498
Company profile aeu-2011_q2

Founded in 1983, Advantech is a leader in providing trusted innovative embedded & automation products and solutions. Advantech offers comprehensive system integration, hardware, software, customer-centric design services, and global logistics support; all backed by industry-leading front and back office e-business solutions. We cooperate closely with our partners to help provide complete solutions for a wide array of applications across a diverse range of industries. Advantech has always been an innovator in the development and manufacturing of high-quality, high-performance computing platforms, and our mission is to empower these innovations by offering trustworthy ePlatform products and services. With Advantech, there is no limit to the applications and innovations our products make possible.
World-class Recognition
Advantech is an authorized alliance partner of both Intel® and Microsoft®. Our customers will find the technologies we use inside our products to be widely compatible with other products in the global marketplace. In 2008, Interbrand, the world renowned brand consulting firm, once again recognized Advantech as one of the Top 10 Taiwanese Global Brands. Advantech appreciates this recognition of our efforts to build a trusted, global brand; it also symbolizes a promise we gave to our business partners, which was to do our best to keep building a trustworthy brand that is recognized everywhere in the world.
How to bootstrap your IoT project

IoT is a green field of new business opportunities. The ran has started…..
Everyware Device Cloud (EDC) is a full set of Operational Technologies available also as a service, which represent the fastest way to start an IoT business.
You can connect a Device to Cloud in 15 minutes.
With EDC A typical IoT project would take 2 to 6 months to go live and the ROI is really fast
.
IoT Manufacturing Solutions For Industry-4.0

Happiest Minds is a digital technology leader in providing services & solution for enabling Industry 4.0 for global manufacturer.
Unique Value Proposition in M2M: Hardware, Software & Service Building Blocks...

Eurotech Value Proposition in M2M:
- Higher value-add for Customers
- Providing enabling platforms, not just components
So, we help Customers focus on their core competences.
Dell NVIDIA AI Roadshow - South Western Ontario

IoT and AI presentation delivered in to companies in South Western Ontario
Sreda Software Solutions company information 

Presentation with Sreda Software Solutions company information and software development capabilities including Automotive electronics, telematics, V2x/C-ITS, Wireless communication, LTE Advanced Pro, Mobile applications, Back end services and data analytics
Developing Interoperable Components for an Open IoT Foundation 

In this presentation Eurotech and Red Hat present Kapua, a modular cloud platform that provides management for Internet of Things (IoT) gateways and smart edge devices. It represents a key milestone towards the development of a truly open, end-to-end foundation for IoT and its ecosystem of partners and solutions. Kapua provides a core integration framework with services for device registry, data and device management, message routing, and applications.
Similar to Case study: M2M Telematics Solution - Happiest Minds (20)
Visiongain publishes report on: The 100 connected car companies to watch

Visiongain publishes report on: The 100 connected car companies to watch
Unique Value Proposition in M2M: Hardware, Software & Service Building Blocks...

Unique Value Proposition in M2M: Hardware, Software & Service Building Blocks...
Developing Interoperable Components for an Open IoT Foundation 

Developing Interoperable Components for an Open IoT Foundation
More from Happiest Minds Technologies
Largest Electricity provider in the US- Case Study

We have partnered with the largest electricity
provider in the US to build centralized operations
and maintenance for power generation plants.
BFSI GLOBAL TRENDS FY 24

The financial volatility unleashed by the
pandemic has opened the doors of opportunity
for Banking and Financial Services (BFS)
companies. Technology-driven digital
transformation is expected to drive further shifts
in this new normal.
The industry will witness the adoption of
innovative technologies driven by emerging
trends. BFS organizations will increasingly
undertake digital transformation to broaden
their capabilities, and maturing FinTechs will
forge partnerships that drive disruptive growth
and customer-focused innovation.
Here, we explore some trends that will shape
the future of the BFS industry
ARTIFICIAL INTELLIGENCE IN DIGITAL BANKING

The most prevalent trend in today’s
financial services industry is the shift to
digital, specifically mobile and online
banking. In the era of unprecedented
convenience and speed, consumers don’t
want to trek to a physical bank branch to
handle their transactions. While on the one
hand, banks are releasing new features to
attract more customers and retain the
existing ones, on the other hand, startups
and neo banks with disruptive banking
technologies are breaking into the scene.
The use of Artificial Intelligence (AI) in the
banking industry can revolutionize the way
banks operate and provide services to
their customers, improving e
ciency,
productivity, and customer experience.
DIGITAL MANUFACTURING

In the age of disruption, manufacturers need to
constantly find innovative ways to overcome challenges
like data sitting in silos, downtime (which could be
prevented), rigid production and labor shortage issues.
Companies need to listen to their operators and
technicians and enable them to have a say in the
day-to-day processes. Issues like being unable to find a
product/part on the floor lead to unnecessary delays,
miscommunication, and dissatisfaction among workers
Exploring the Potential of ChatGPT in Banking, Financial SERVICES & Insurance

Exploring the Potential of ChatGPT in Banking, Financial SERVICES & InsuranceHappiest Minds Technologies
The banking, financial services, and insurance (BFSI)
sector has been at the forefront of adopting AI and
machine learning technologies. AI has enabled these
industries to automate processes, reduce costs, and
improve the customer experience. With the advent of
digitization and the increasing amount of data available,
banking, financial services, and insurance companies have
been leaders in using AI and machine learning.AN OVERVIEW OF THE METAVERSE

Metaverse has become ae buzzword in the tech industry. Not a single day goes by without a mention of it
in the media, especially around investments, startups building components, new platforms being
announced and large companies entering this world of digital engagement. There is undeniably a huge momentum of an almost real 3D virtual world, and the clarion call was perhaps Facebook rebranding itself
as Meta which will perhaps be remembered as a red letter moment in the evolution of the Metaverse.
VMware to AWS Cloud Migration

A leading financial organization providing business loans for the small-scale
industry and provided more than 200000 loans totaling $ 7.5 Billion.
Digital-Content-Monetization-DCM-Platform-2.pdf

Content is one of the most commonly consumed resources in online marketplace. Still,
most organizations struggle to effectively monetize it. Inability to implement viable
and scalable monetization methods not only keeps organizations from discovering
growth opportunities, but can also lead to poor customer experiences.
AUTOMATING CYBER RISK DETECTION AND PROTECTION WITH SOC 2.0

Digitalization has transformed the way business’s function. With the evolution of technologies, attackers are also evolving. They are finding innovative and more invasive ways to attack organizations. Due to this, the organization's security operations center (SOC) is expected to be
more agile and dynamic in detecting and responding to attacks. Most organizations' security operations and incident response teams are overworked due to high volumes of security threats and alerts that they need to manage every day.
Cloud Reshaping Banking

Cloud technology is no longer a new player in the market,
but it’s a mature and integral part of the IT landscape and a
key parameter in driving business growth. It is an
indispensable topic among CXOs. A research by Fraedon has
found that almost half of the banks find their legacy
systems to be the biggest hindrance in their growth.
Automating SOC1/2 Compliance- For a leading Software solution company in UK

Automating SOC1/2 Compliance- For a leading Software solution company in UKHappiest Minds Technologies
Client is the leader in work orchestration and observability. Software platform helps enterprises more effectively plan, orchestrate and audit the human and automated activities that drive critical events, such as technology releases, resilience testing, operational readiness and major incident recovery.PAMaaS- Powered by CyberArk

A Robust Privileged Access Management (PAM) forms the
cornerstone of an enterprise cybersecurity strategy, providing greater visibility and audibility of an organization's
overall credentials and privileges.
GUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...

GUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...Happiest Minds Technologies
The global disruption due to the pandemic has massively impacted organizations and the way they function.
Organizations are shifting towards a virtual environment by adopting cloud and automation to support,
monitor, and deploy exceptional service to their end-users. But how to keep the end-users connected to the
digital workplace securely during disruption is a big challengeSECURING THE CLOUD DATA LAKES

Let us understand some of the infrastructural and
security challenges that every organization faces today
before delving into the concept of securing the cloud
data lake platform. Though Data lakes provide scalability,
agility, and cost-effective features, it possesses a unique
infrastructure and security challenges.
Complete Guide to General Data Protection Regulation (GDPR)

European government in 2016 adopted General Data Protection Regulation (GDPR) and was
put into effect on May 25, 2018, replacing the 1995’s Data Protection Directive to protect the
personal information of EU citizens. GDPR aims to govern personal data processing and ensure
processing is fair and lawful. It is also designed to emphasize the fundamental right to privacy.
Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)

Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)Happiest Minds Technologies
Aure Bastion is a PaaS solution for your remote desktop which is more secure than the
jump server. It comes with web-based login, and never expose VM public IP to the
internet. This service will work seamlessly on your environment using VM’s private IP
address within your Vnet. Highly secure and trustable.REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDITHappiest Minds Technologies
The Retail industry today is dealing with the concerning challenge of rising costs of transportation,
driven by a shortage of trucks and truck drivers, availability of raw material and unprecedented
demand spikes across categories. Retailers like Bed Bath & Beyond have recently warned investors
about the impact of rising freight costs on earnings. As overall freight costs can constitute up to
10% of total expenditure, efficiency in freight invoice management is critical to managing
transportation budgetsREDUCING TRANSPORTATION COSTS IN CPG THROUGH INTELLIGENT FREIGHT AUDIT

The freight ecosystem is vast and complex with many interconnected functions starting from sourcing, manufacturing to bringing products to the consumer. Any organization dealing with
movement or purchase of freight (goods) needs a control mechanism to ensure accuracy of dealing with freight invoices received from carriers.
How to Approach Tool Integrations

Tool Integration is an effective technique of integrating tools of the same or different classes to build a robust tool framework to support various business operations.
REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDITHappiest Minds Technologies
The Retail industry today is dealing with the concerning challenge of rising costs of transportation,
driven by a shortage of trucks and truck drivers, availability of raw material and unprecedented
demand spikes across categories. Retailers like Bed Bath & Beyond have recently warned investors
about the impact of rising freight costs on earnings. As overall freight costs can constitute up to
10% of total expenditure, efficiency in freight invoice management is critical to managing
transportation budgets.
More from Happiest Minds Technologies (20)
Largest Electricity provider in the US- Case Study

Largest Electricity provider in the US- Case Study
Exploring the Potential of ChatGPT in Banking, Financial SERVICES & Insurance

Exploring the Potential of ChatGPT in Banking, Financial SERVICES & Insurance
AUTOMATING CYBER RISK DETECTION AND PROTECTION WITH SOC 2.0

AUTOMATING CYBER RISK DETECTION AND PROTECTION WITH SOC 2.0
Automating SOC1/2 Compliance- For a leading Software solution company in UK

Automating SOC1/2 Compliance- For a leading Software solution company in UK
GUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...

GUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...
Complete Guide to General Data Protection Regulation (GDPR)

Complete Guide to General Data Protection Regulation (GDPR)
Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)

Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)
REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT
REDUCING TRANSPORTATION COSTS IN CPG THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN CPG THROUGH INTELLIGENT FREIGHT AUDIT
REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT
Recently uploaded
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Recently uploaded (20)
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Case study: M2M Telematics Solution - Happiest Minds
- 1. Case study: M2M Telematics Solution M2M Telematics Product Development for leading Technology Company BUSINESS REQUIREMENTS BUSINESS IMPACT Support telematics devices and product enhancement Provide ofine support for telematics device that includes support for Bluetooth and implementation of device tracking system like geo-fencing Build complete architecture of the solution around personal telematics and diagnostics device Web and mobile based solutions Device development: CAN, Free RTOS, OBD protocols, ST Microcontroller, IAR EWARM, ST link Designing server side implementation Server Implementation: PHP, MySQL, Mongodb and Python Complete lab setup for supporting system testing of the device Testing: Labsat, RF Chamber, Thermal Chamber, OBD II Protocol Simulator OUR SOLUTIONS Enhancement of solutions like Geo -fencing, Low Power Reengineering and Accelerometer upgraded market position of the product End to End system testing reduced existing gap and enhanced the product leading to successful deployment Improvement of various features enriched look feel and usability of product with cloud based tracking platform Solution Architecture Diagram Driver B call operator GPS Satellites Cell Tower GPS Signals GSM/GPRS/3G/CDMA GPS Cell Data Storage GPS Network Voice alerts E-call/ B-call E-call/ B-call Digital/ Analog OPIO’s Vehicle Monitoring Software (ECU Other Automotive Units) Vehicle GSM/GPRS Gateway Track Server B-call Voice message UART, CAN, GPIO interface E-call data message Public Service Access Point Telematic Device Accel TOOLS/ TECHNOLOGIES Happiest Minds has a sharp focus on enabling Digital Transformation for customers by delivering a Smart, Secure and Connected experience through disruptive technologies: mobility, big data analytics, security, cloud computing, social computing, M2M/IoT, unied communications, etc. Enterprises are embracing these technologies to implement Omni-channel strategies, manage structured unstructured data and make real , time decisions based on actionable insights, while ensuring security for data and infrastructure. Happiest Minds also offers high degree of skills, IPs and domain expertise across a set of focused areas that include IT Services, Product Engineering Services, Infrastructure Management, Security, Testing and Consulting. Headquartered in Bangalore, India, Happiest Minds has operations in the US, UK, Singapore and Australia. It secured a $52.5 million Series-A funding led by Canaan Partners, Intel Capital and Ashok Soota. About Us For more information visit www.happiestminds.com. Write to us at business@happiestminds.com © Happiest Minds Proprietary
