Embed presentation
Downloaded 17 times







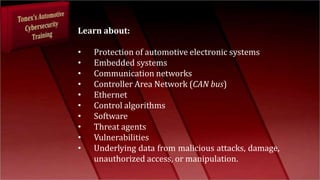
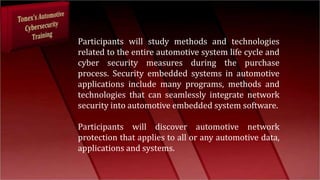
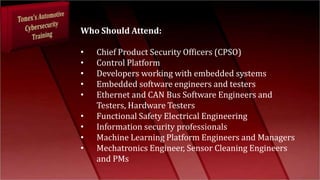
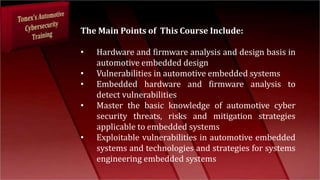
The document discusses cybersecurity challenges facing the automotive industry as vehicles become more connected and software-defined. As modern cars now resemble computers and receive over-the-air software updates, they are vulnerable to cyber attacks which could compromise safety systems or require large recalls. A 3-day training course is described that covers vulnerabilities in automotive embedded systems, network security best practices, and methods for securing interfaces and protocols to protect vehicles from cyber threats. The training is intended for professionals across automotive engineering, product development, and information security fields.