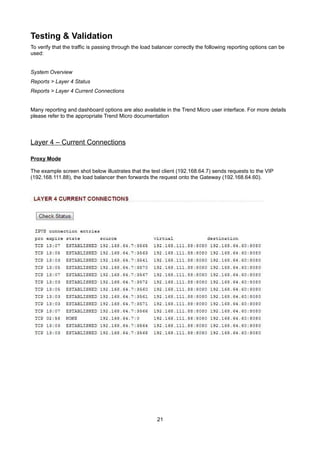
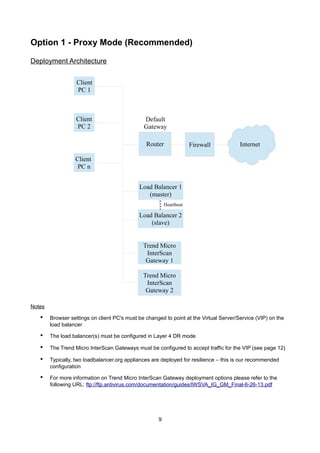
This guide outlines the deployment of loadbalancer.org appliances with Trend Micro's Interscan Web Gateway, detailing the configuration process for various deployment modes and load balancing options. It emphasizes the benefits, such as high availability and system performance, and provides step-by-step instructions for setting up both proxy and transparent modes. Additionally, network configuration, web user interface access, and testing procedures are included to ensure effective implementation and operation.






![Load Balancer Configuration
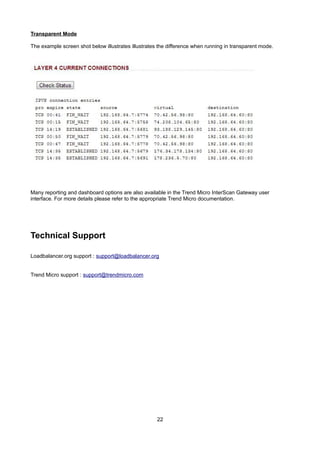
Create the Virtual Server/Service (VIP)
NOTE: Prior to v7.5 a VIP is known as a 'Virtual Server', from v7.5 onwards it's known as a 'Virtual
Service'. For simplicity the configuration steps below refer to 'Virtual Service' for both.
•
v7.5 & later – using the WUI go to Cluster Configuration > Layer 4 – Virtual Services
•
v7.4.3 – using the WUI go to Edit Configuration > Layer 4 – Virtual Servers
•
Click [Add a New Virtual Service]
•
Enter the following details:
•
Enter an appropriate label (name) for the VIP, e.g. Proxy
•
Set the Virtual Service IP address field to the required IP address, e.g. 192.168.2.202
•
Set the Virtual Service Ports field to the required port (the same as the InterScan Gateways) , e.g.
8080
•
Ensure that Forwarding Method is set to Direct Return
•
Set Persistent to yes
•
Ensure that Protocol is set to TCP
•
Click Update
10](https://image.slidesharecdn.com/load-balancer-deployment-guide-fr-trend-micro-interscan-webgateway-140203103605-phpapp02/85/Load-Balancing-des-Trend-Micro-InterScan-Web-Security-WebGateway-Webfilter-das-Handbuch-10-320.jpg)
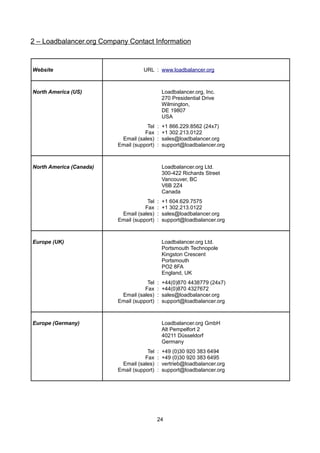
![Create the Real Servers (RIPs)
•
v7.5 & later – using the WUI go to Cluster Configuration > Layer 4 – Real Servers
•
v7.4.3 – using the WUI go to Edit Configuration > Layer 4 – Real Servers
•
Click [Add a new Real Server] next to the newly created VIP
•
Enter the following details:
•
Enter an appropriate label (name) for the first Proxy Server, e.g. Proxy1
•
Change the Real Server IP Address field to the required IP address, e.g. 192.168.2.210
•
Click Update
•
Repeat the above steps to add your other InterScan Gateways
11](https://image.slidesharecdn.com/load-balancer-deployment-guide-fr-trend-micro-interscan-webgateway-140203103605-phpapp02/85/Load-Balancing-des-Trend-Micro-InterScan-Web-Security-WebGateway-Webfilter-das-Handbuch-11-320.jpg)




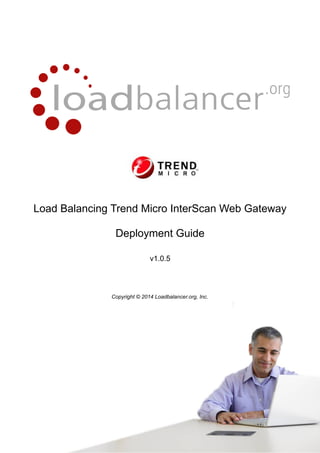
![Load Balancer Configuration
Create the Virtual Server/Service (VIP)
NOTE: Prior to v7.5 a VIP is known as a 'Virtual Server', from v7.5 onwards it's known as a 'Virtual
Service'. For simplicity the configuration steps below refer to 'Virtual Service' for both.
•
v7.5 & later – using the WUI go to Cluster Configuration > Layer 4 – Virtual Services
•
v7.4.3 – using the WUI go to Edit Configuration > Layer 4 – Virtual Servers
•
Click [Add a New Virtual Service]
•
Enter the following details:
•
Enter an appropriate label (name) for the VIP, e.g. Proxy
•
Change the Virtual Service IP address field to 1
N.B. This is the reference number for the 'Firewall Mark' which is required for VIPs with multiple
ports – in this case, ports 80 & 443 are required. This reference is also used when configuring the
firewall rules.
•
Leave Virtual Service Ports blank
•
Ensure that Forwarding Method is set to Direct Routing
•
Set Persistent to yes
•
Ensure that Protocol is set to Firewall Marks
•
Click Update
•
Now click [Modify] next to the newly created VIP
•
Change Check Type to Ping Server
•
Click Update
16](https://image.slidesharecdn.com/load-balancer-deployment-guide-fr-trend-micro-interscan-webgateway-140203103605-phpapp02/85/Load-Balancing-des-Trend-Micro-InterScan-Web-Security-WebGateway-Webfilter-das-Handbuch-16-320.jpg)

![Create the Real Servers (RIPs)
•
v7.5 & later – using the WUI go to Cluster Configuration > Layer 4 – Real Servers
•
v7.4.3 – using the WUI go to Edit Configuration > Layer 4 – Real Servers
•
Click [Add a new Real Server] next to the newly created VIP
•
Enter the following details:
•
Enter an appropriate label (name) for the first Proxy Server, e.g. Proxy1
•
Change the Real Server IP Address field to the required IP address, e.g. 192.168.2.210
•
Click Update
•
Repeat the above steps to add your other InterScan Gateways
18](https://image.slidesharecdn.com/load-balancer-deployment-guide-fr-trend-micro-interscan-webgateway-140203103605-phpapp02/85/Load-Balancing-des-Trend-Micro-InterScan-Web-Security-WebGateway-Webfilter-das-Handbuch-18-320.jpg)