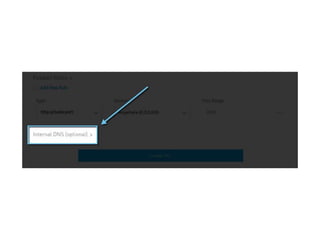
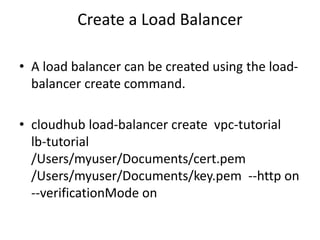
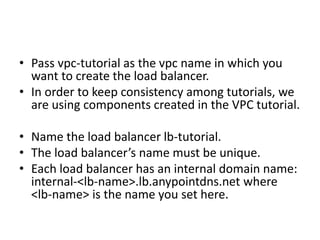
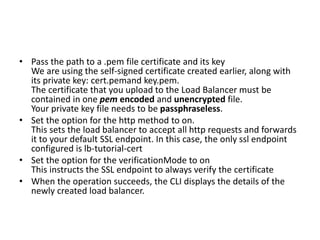
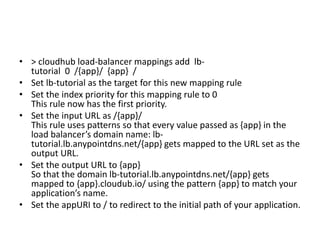
This document provides instructions for creating a load balancer and virtual private cloud (VPC) on MuleSoft's Anypoint Platform. It describes how to create a VPC with a specified name, region, and CIDR block. It then explains how to create a load balancer within that VPC, associating it with an SSL certificate and setting firewall rules. It also discusses how to add mapping rules and update an existing load balancer's configuration via the API.