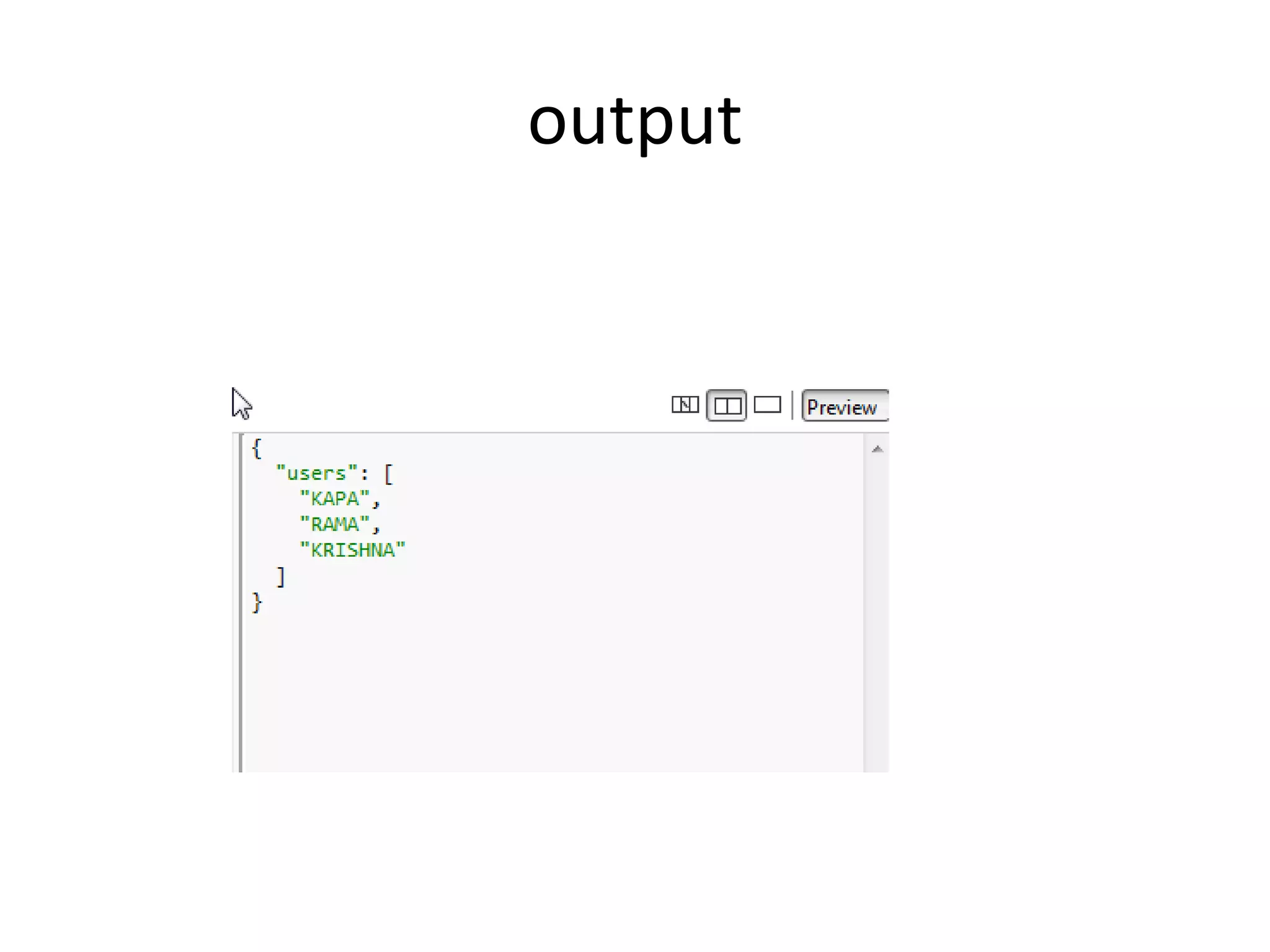
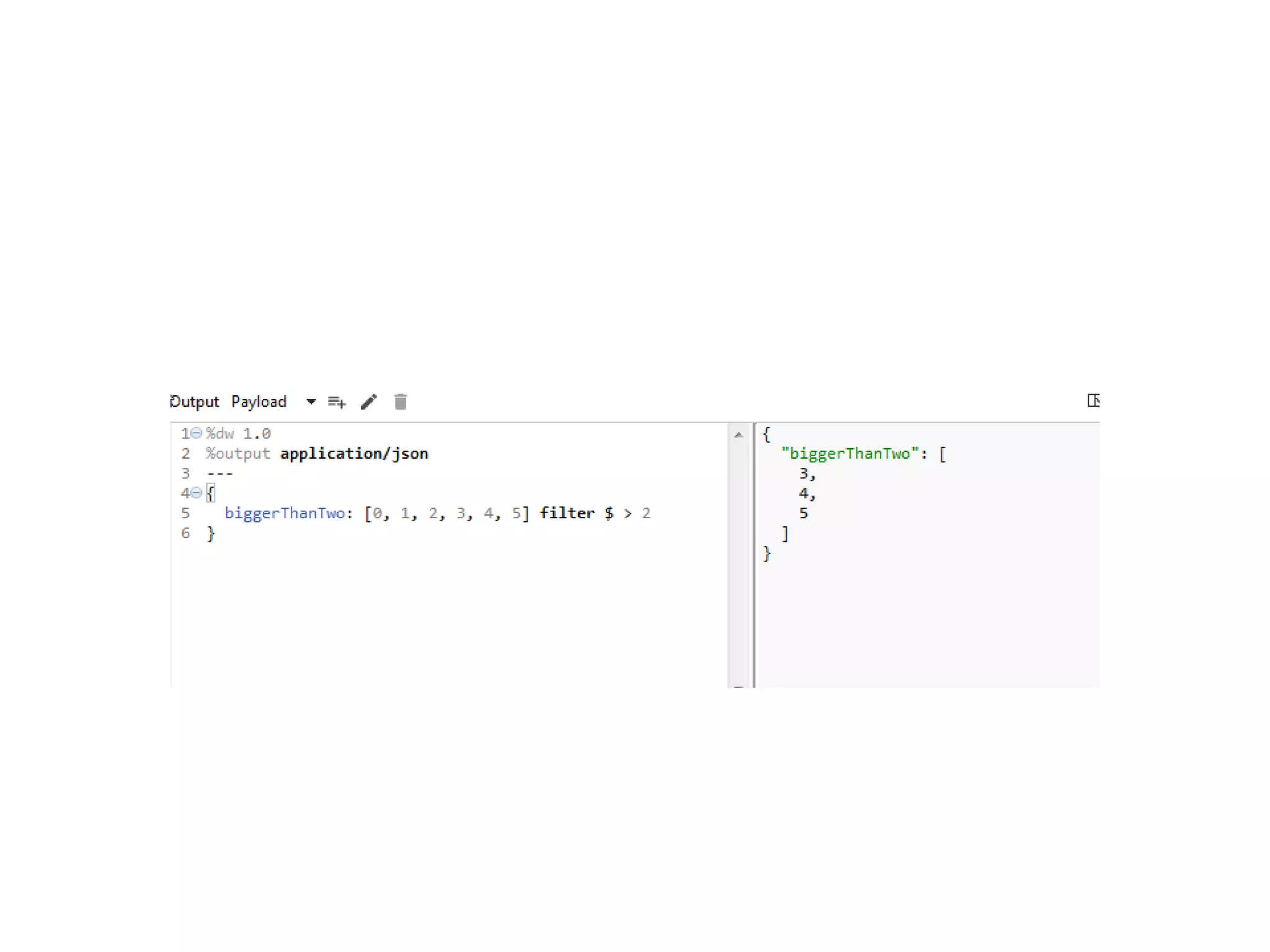
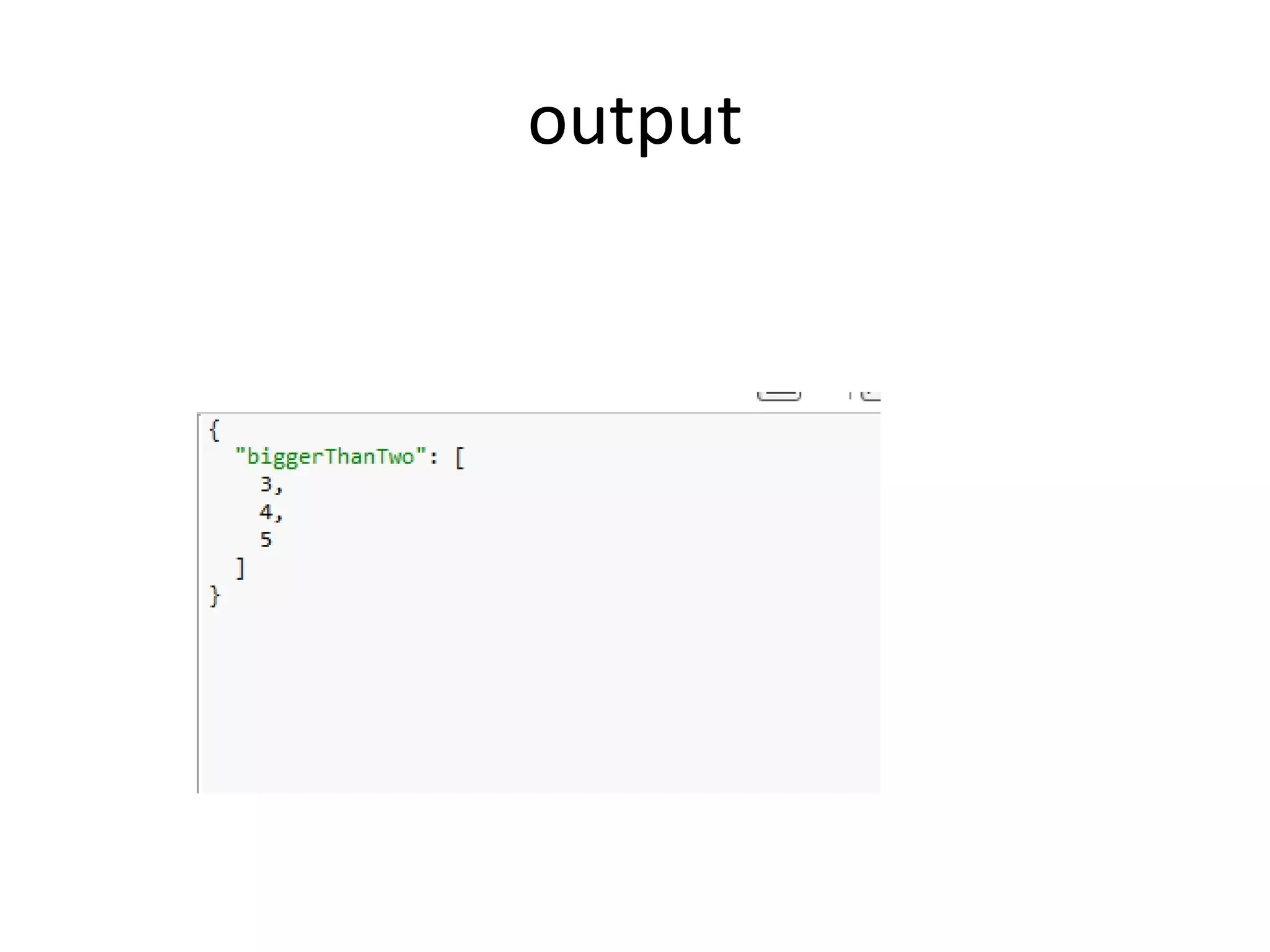
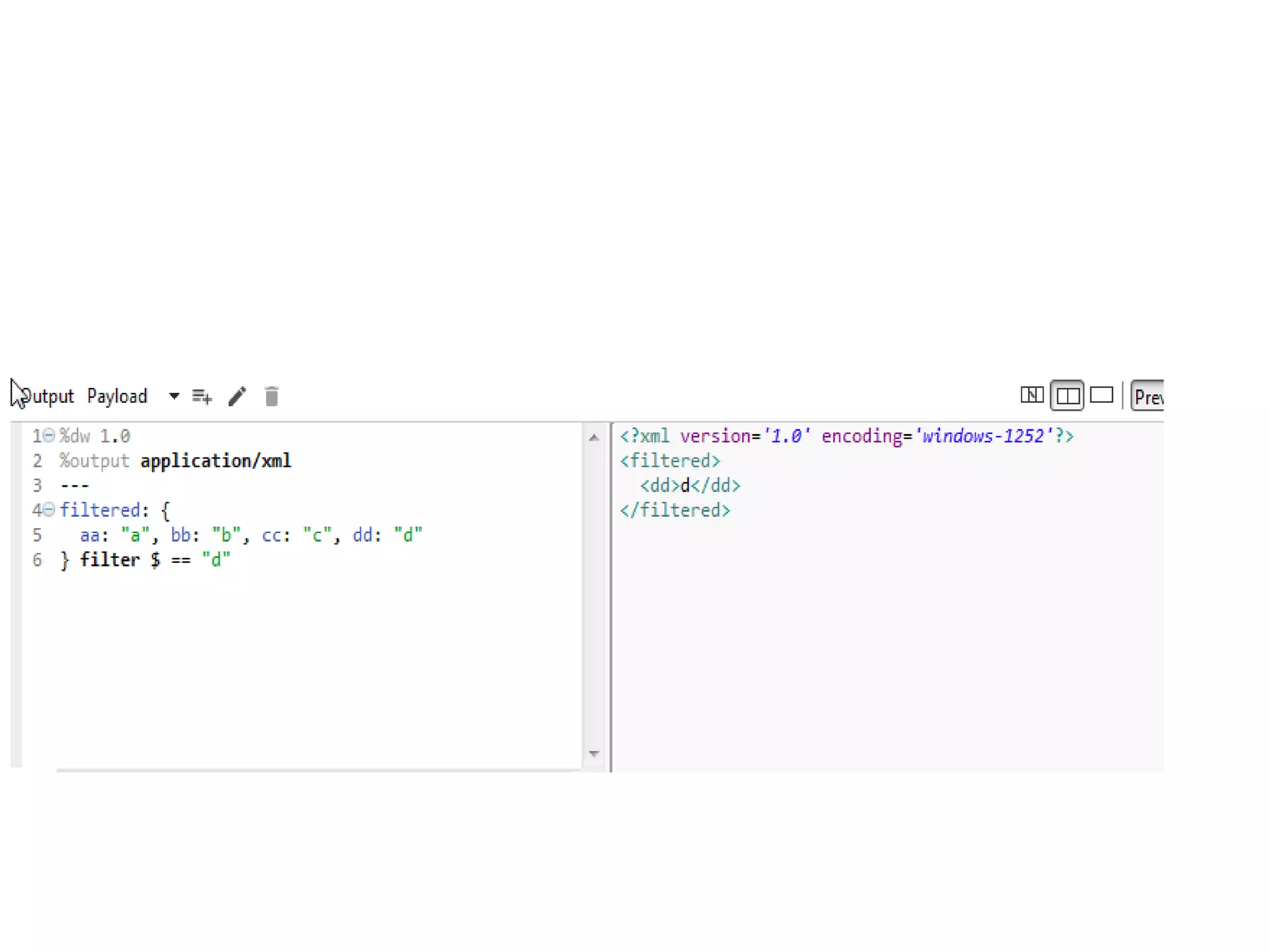
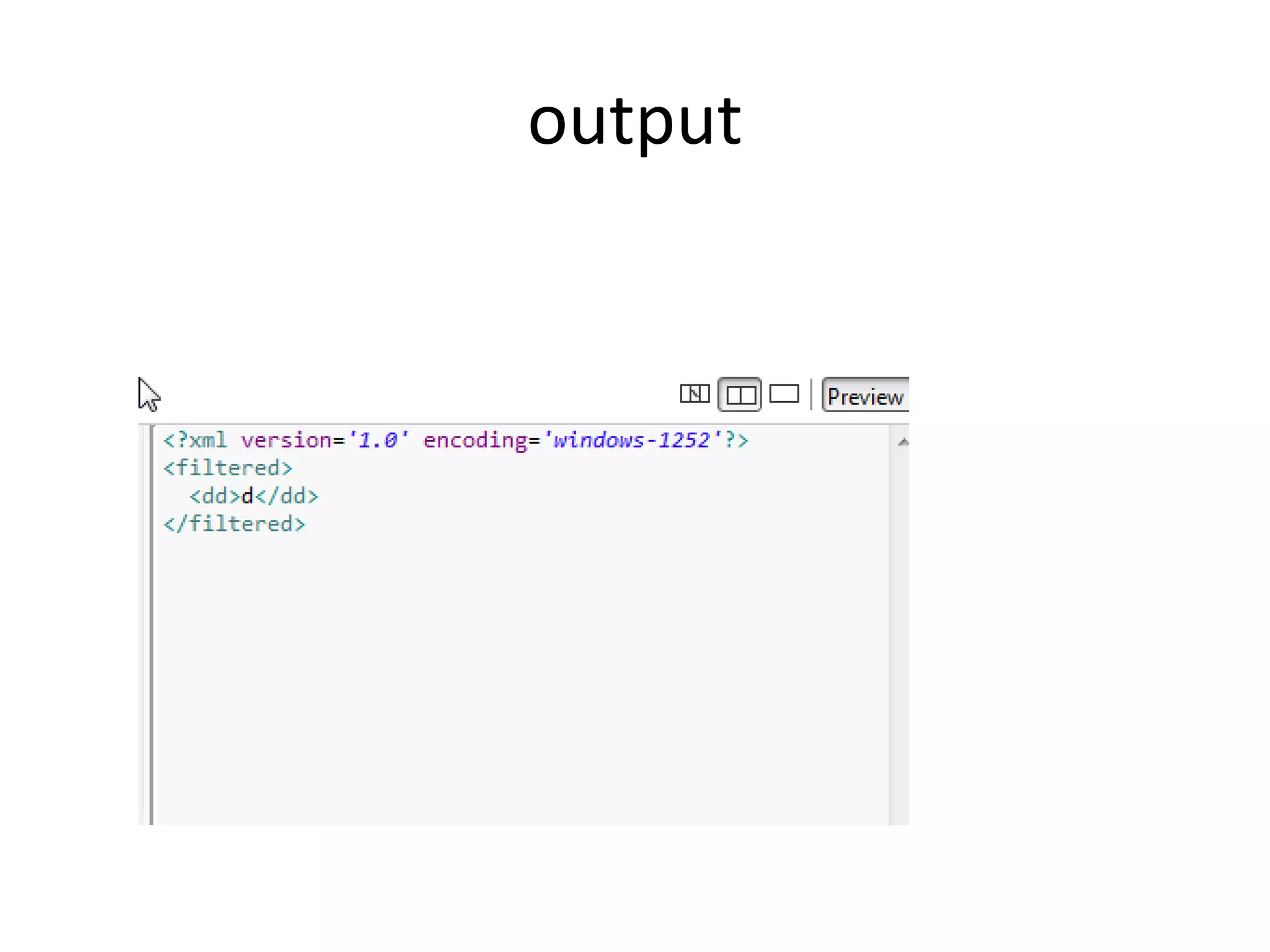
This document discusses common operations in Mule Dataweave including map, pluck, filter, and remove. Map applies a function to each element of an array and returns a new array. Pluck maps an object to an array by applying a function to each key-value pair. Filter returns an array or object containing only elements that pass the criteria in the provided function. Remove returns an array with specified indexes removed.