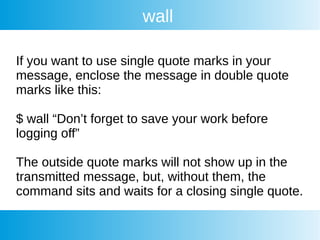
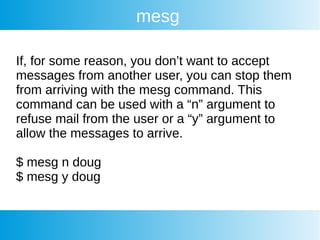
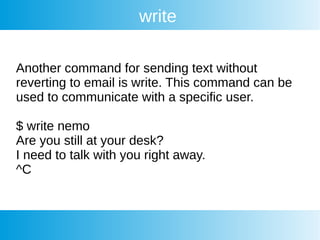
This document provides information on Linux communication tools including wall, talk, write, mesg, and systemctl. It discusses how wall broadcasts messages to logged in users. It explains how talk and ytalk allow interactive chats between users. It covers how write sends text without email. It also discusses how mesg blocks or allows messages from other users. Finally, it provides an in-depth overview of the systemctl command for managing systemd services and units.



![Systemctl
Example of status output:
[root@host ~]# systemctl status httpd
● httpd.service - The Apache HTTP Server
Loaded: loaded (/usr/lib/systemd/system/httpd.service; enabled; vendor preset:
disabled)
Active: active (running) since Fri 2020-05-08 14:15:54 EDT; 1 weeks 2 days ago
Docs: man:httpd(8)
man:apachectl(8)
Process: 3767 ExecReload=/usr/sbin/httpd $OPTIONS -k graceful (code=exited,
status=0/SUCCESS)
Main PID: 1321 (httpd)
Status: "Total requests: 0; Current requests/sec: 0; Current traffic: 0 B/sec"
CGroup: /system.slice/httpd.service
├─1321 /usr/sbin/httpd -DFOREGROUND
├─3769 /usr/sbin/httpd -DFOREGROUND](https://image.slidesharecdn.com/linuxclass10-15oct2021-6-211016125349/85/Linux-class-10-15-oct-2021-6-24-320.jpg)

![Systemctl
Here is the example of the output of that command.
root@host [~]# systemctl list-units
UNIT LOAD ACTIVE SUB DESCRIPTION
crond.service loaded active running Command Scheduler
dovecot.service loaded active running Dovecot IMAP/POP3 email server
firewalld.service loaded active running firewalld - dynamic firewall daemon
httpd.service loaded active running The Apache HTTP Server
mariadb.service loaded active running MariaDB database server
named.service loaded active running Berkeley Internet Name Domain (DNS)](https://image.slidesharecdn.com/linuxclass10-15oct2021-6-211016125349/85/Linux-class-10-15-oct-2021-6-31-320.jpg)

![Systemctl
Next, we will open the newly created unit file in a text editor (like vim or nano) and add the service
configuration options. Below, we can see a basic example of the unit file.
[Unit]
Description=This is the manually created service
After=network.target
[Service]
ExecStart=/path/to/executable
[Install]
WantedBy=multi-user.target](https://image.slidesharecdn.com/linuxclass10-15oct2021-6-211016125349/85/Linux-class-10-15-oct-2021-6-39-320.jpg)
![Systemctl
Viewing Dependencies
Just like we can see inside a unit file, we can also use the following command to display the
dependency tree of that unit.
systemctl list-dependencies servicename.service
[root@host ~]# systemctl list-dependencies httpd.service
httpd.service
● ├─-.mount
● ├─system.slice
● └─basic.target
● ├─microcode.service
● ├─rhel-dmesg.service
● ├─selinux-policy-migrate-local-changes@targeted.service
● ├─paths.target
● ├─slices.target
● │ ├─-.slice
● │ └─system.slice](https://image.slidesharecdn.com/linuxclass10-15oct2021-6-211016125349/85/Linux-class-10-15-oct-2021-6-43-320.jpg)

![Systemctl
View Properties
Additionally, we can see the properties of a unit by using the show command.
systemctl show servicename.service
This will give you output similar to the one below.
[root@host ~]# systemctl show httpd.service
Type=notify
Restart=no
NotifyAccess=main
RestartUSec=100ms
TimeoutStartUSec=1min 30s
TimeoutStopUSec=1min 30s
WatchdogUSec=0
WatchdogTimestamp=Thu 2020-06-25 05:43:53 EDT](https://image.slidesharecdn.com/linuxclass10-15oct2021-6-211016125349/85/Linux-class-10-15-oct-2021-6-45-320.jpg)
![Systemctl
In case you are looking for a single setting, you can use -p flag with the setting name. For example,
to get the PID of a running service, use this command.
[root@host ~]# systemctl show httpd.service -p MainPID
MainPID=4004](https://image.slidesharecdn.com/linuxclass10-15oct2021-6-211016125349/85/Linux-class-10-15-oct-2021-6-46-320.jpg)