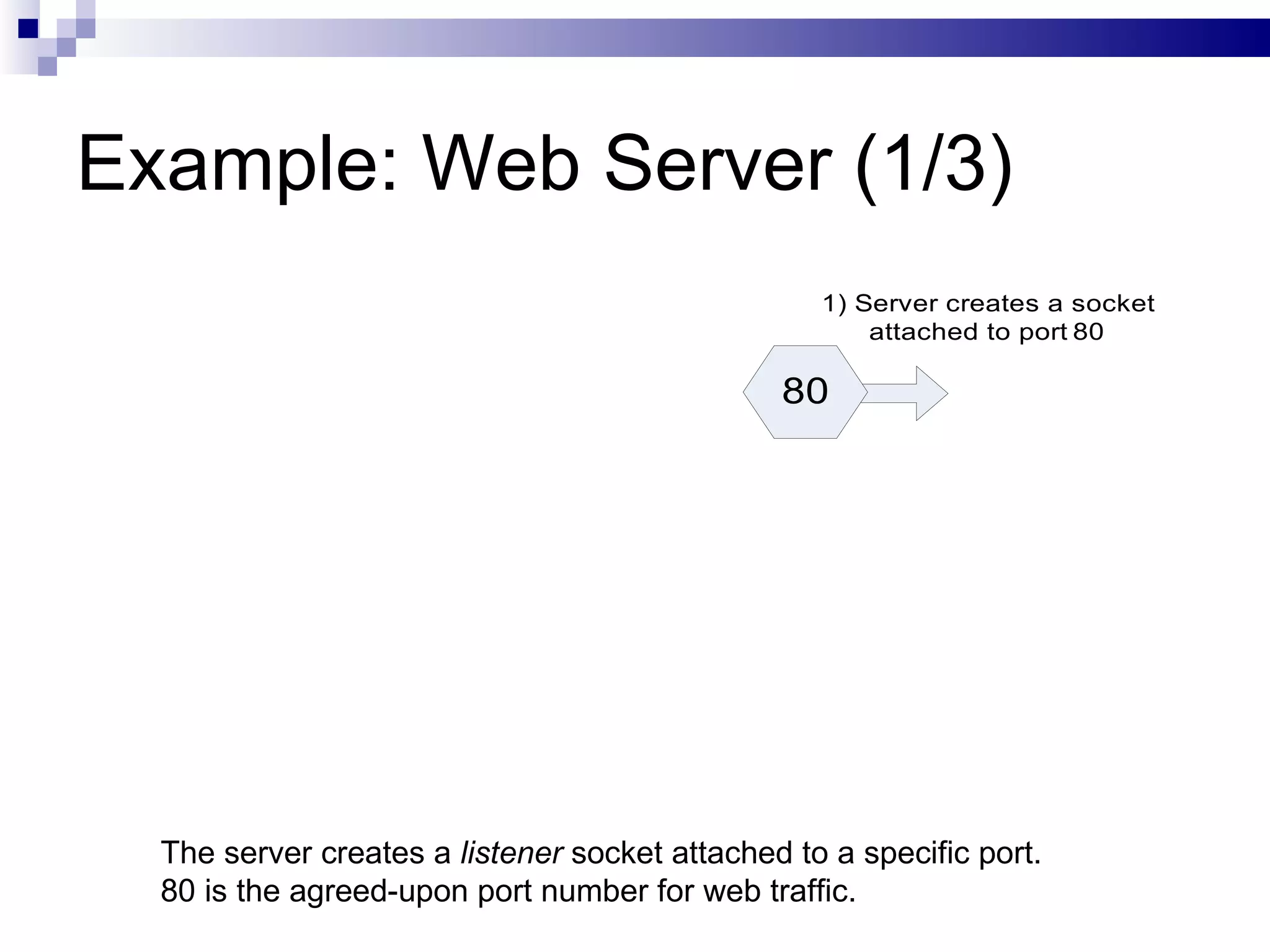
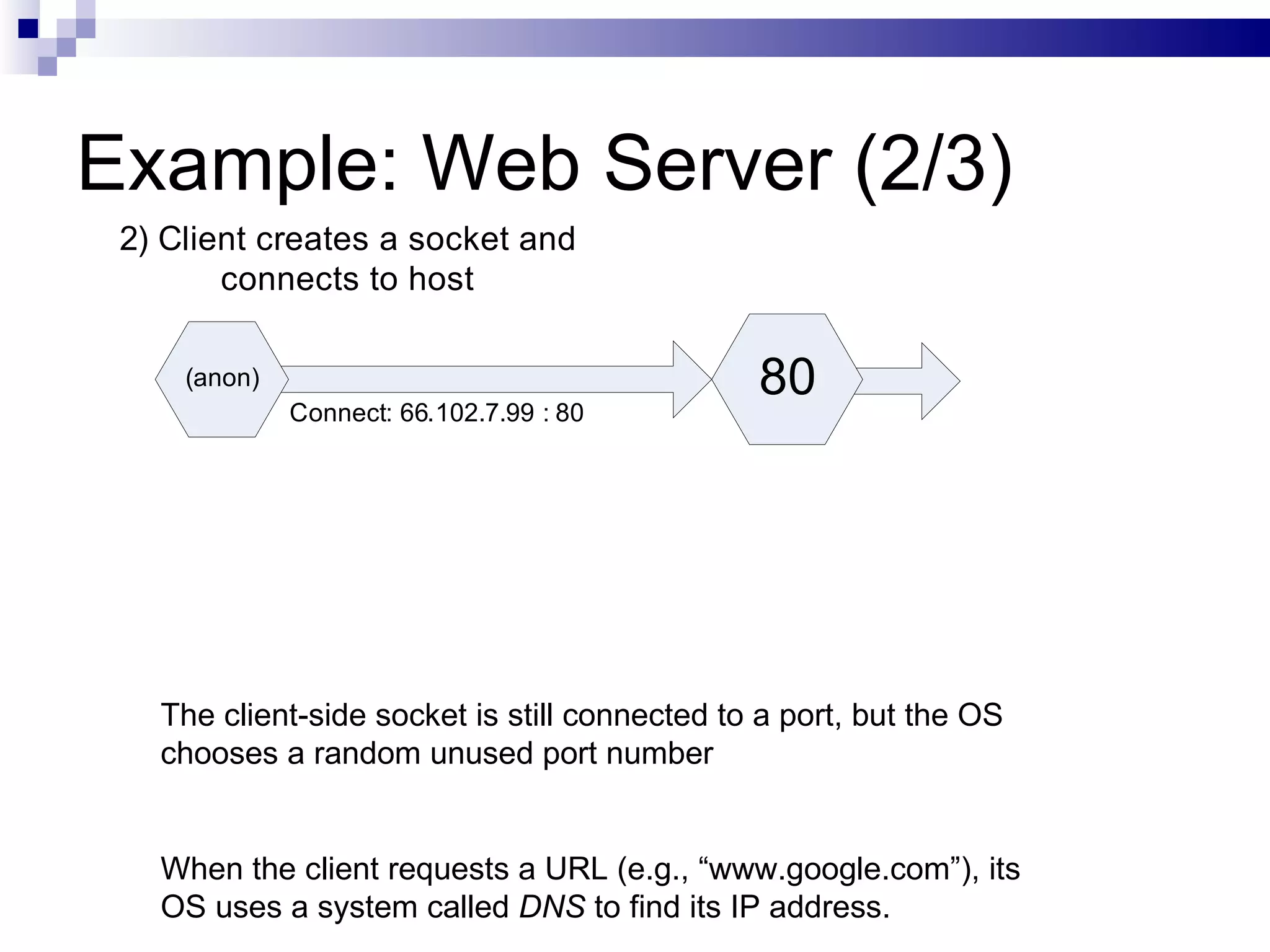
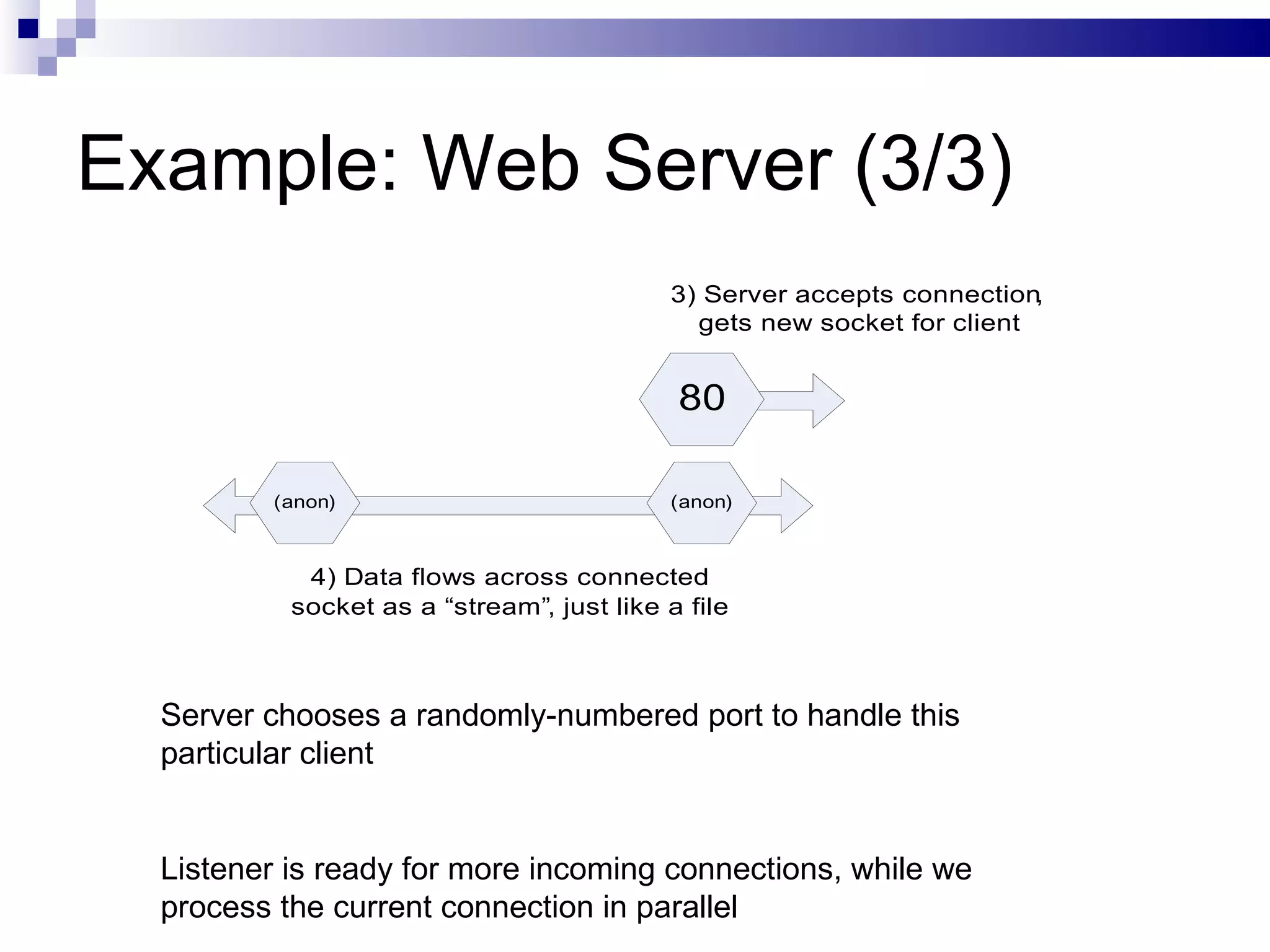
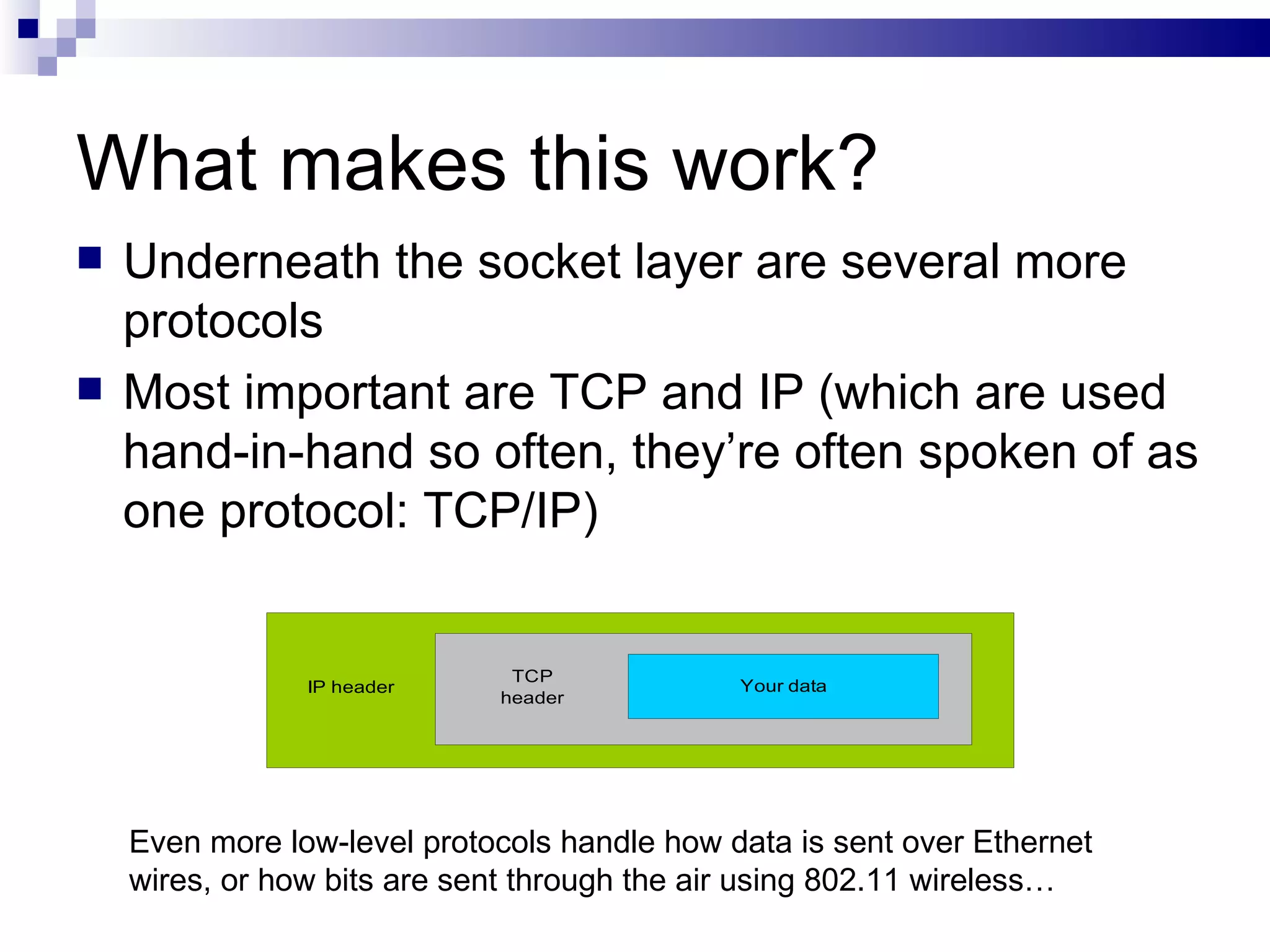
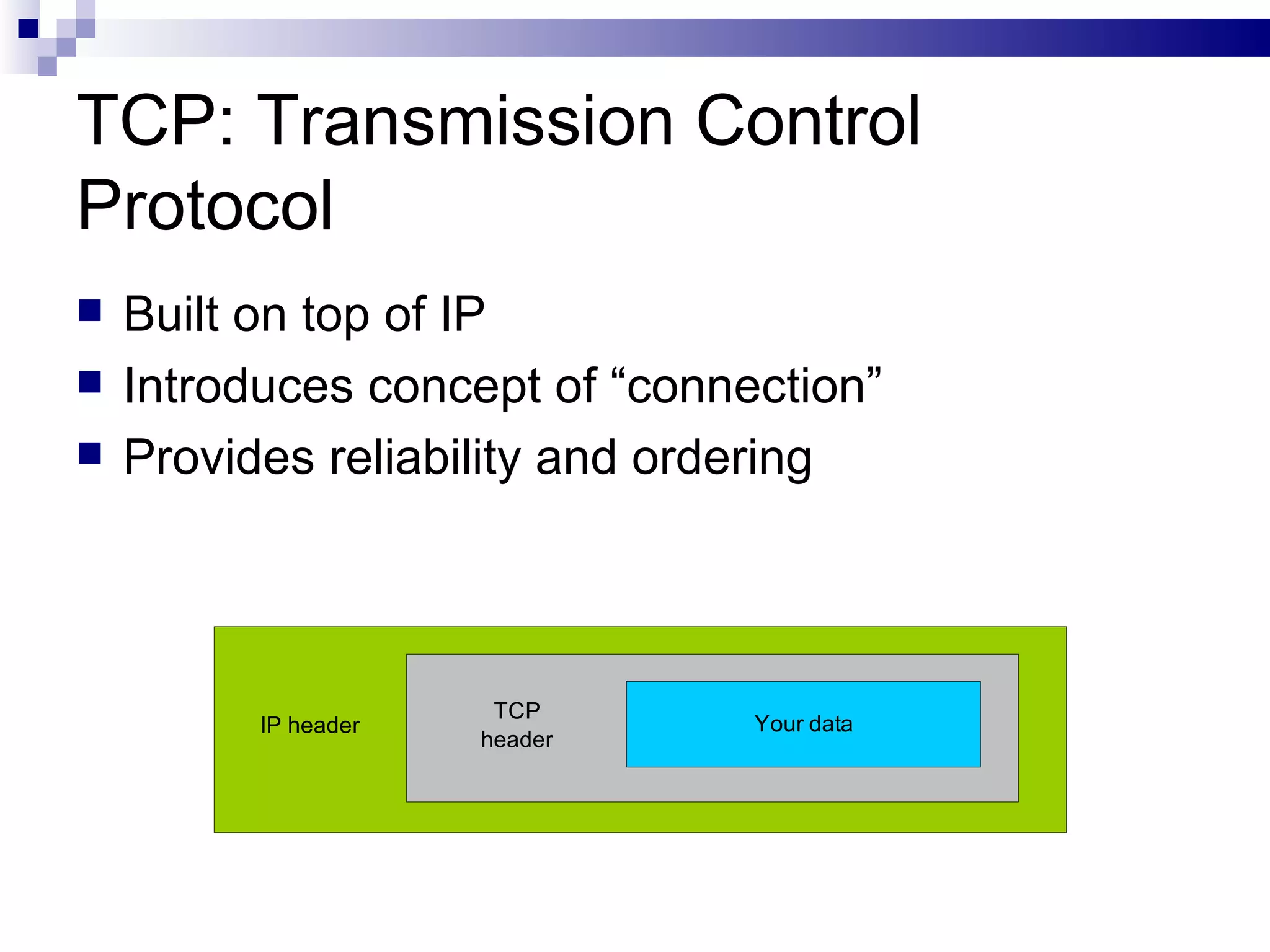
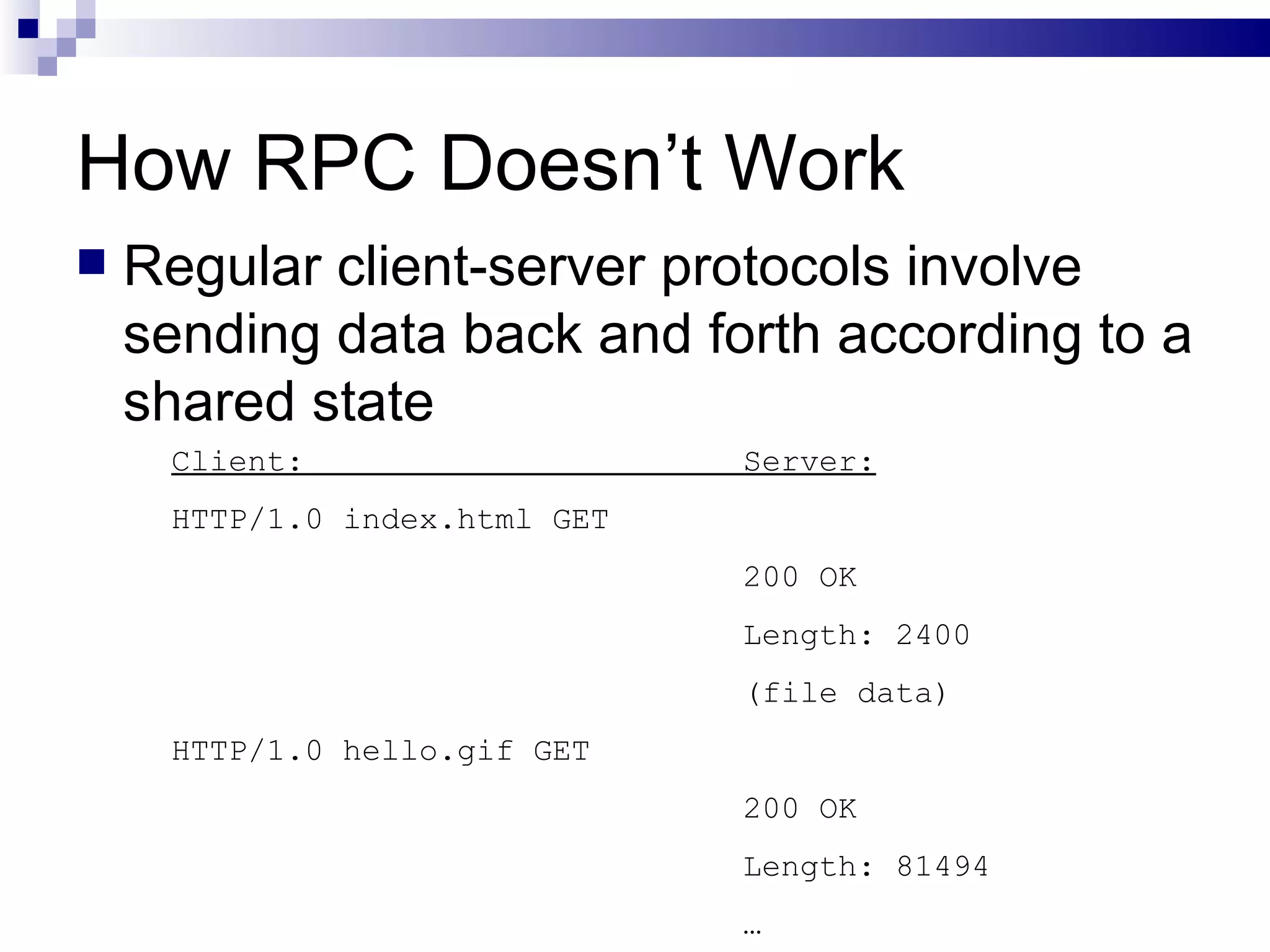
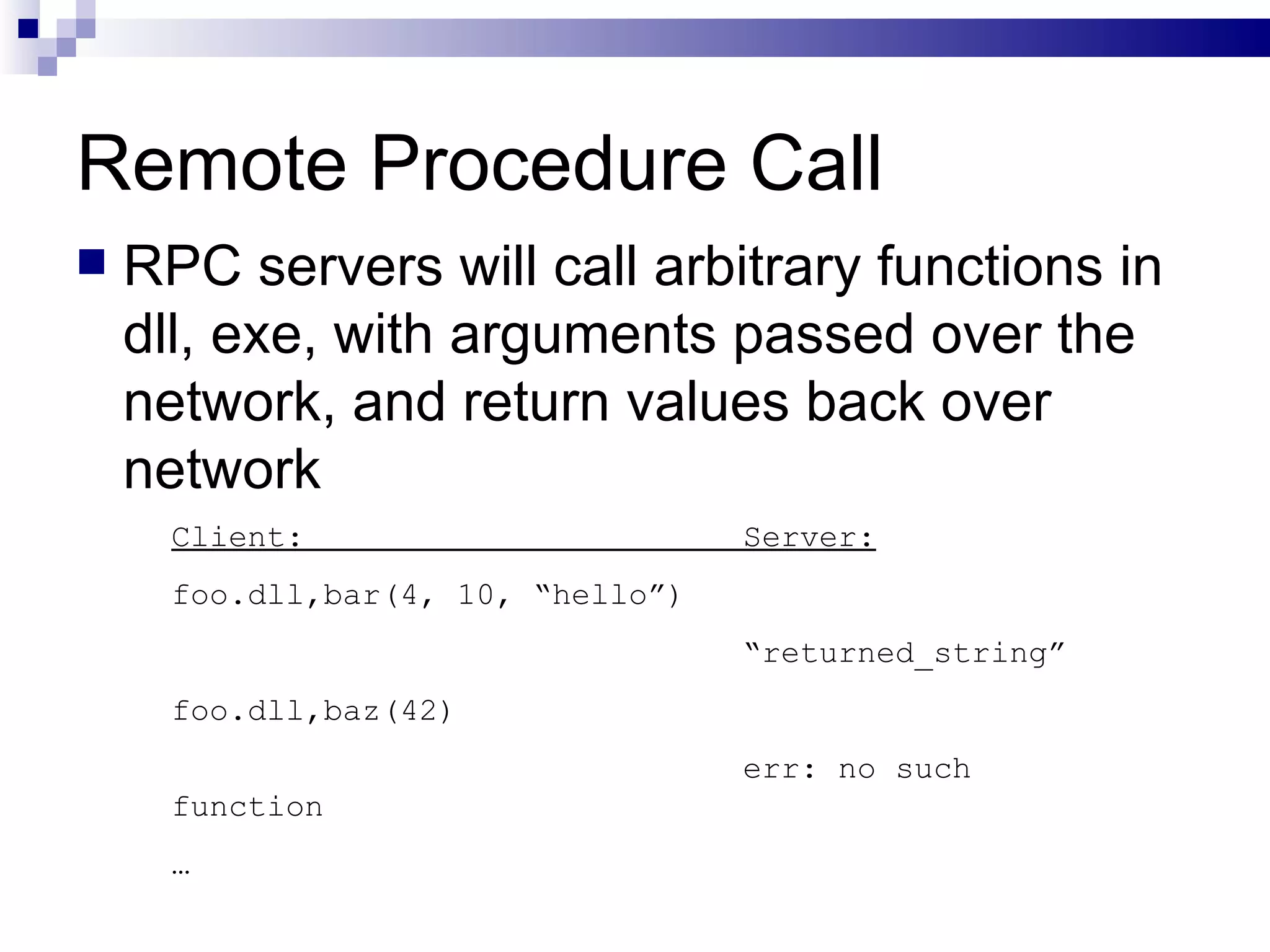
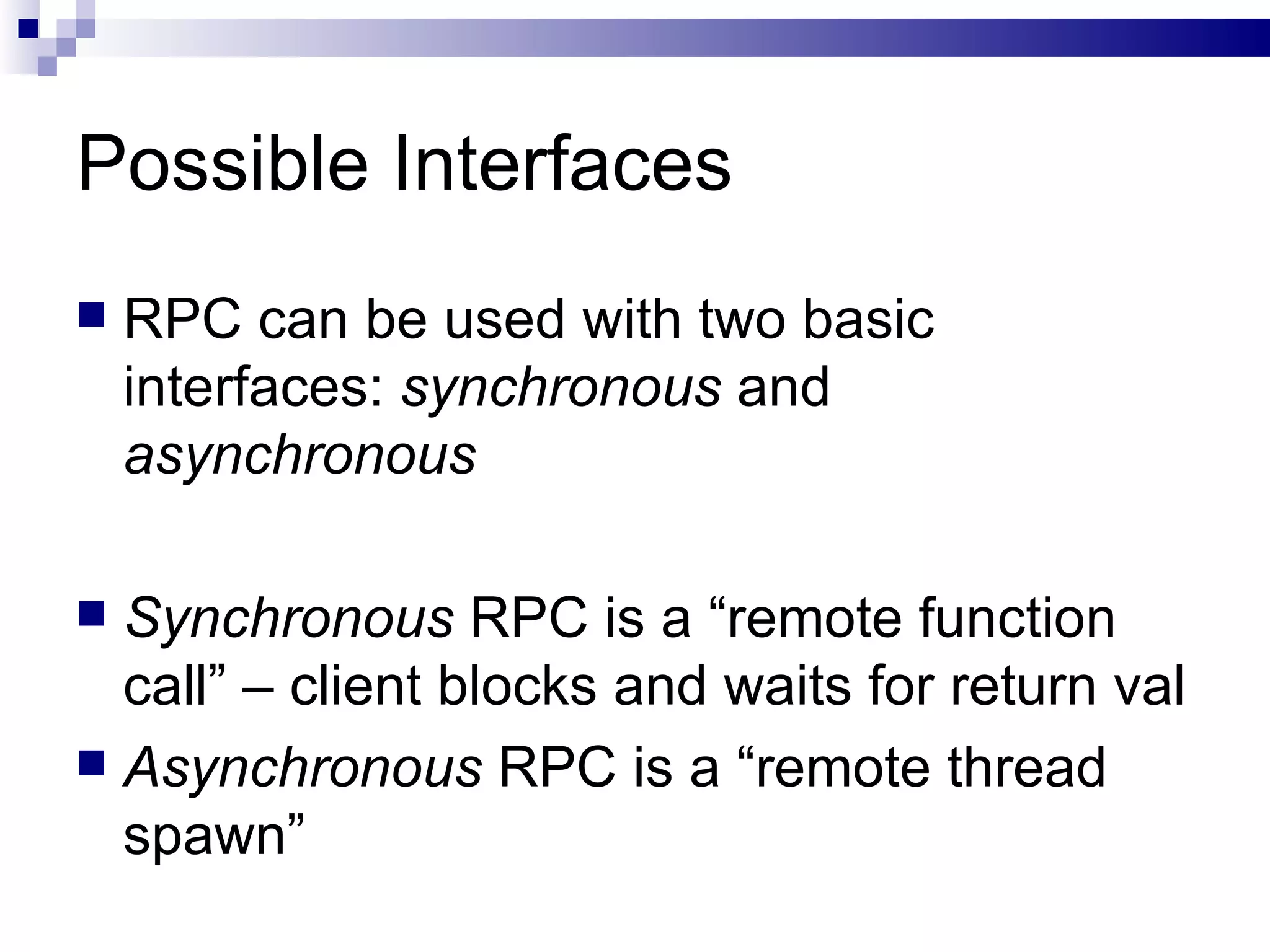
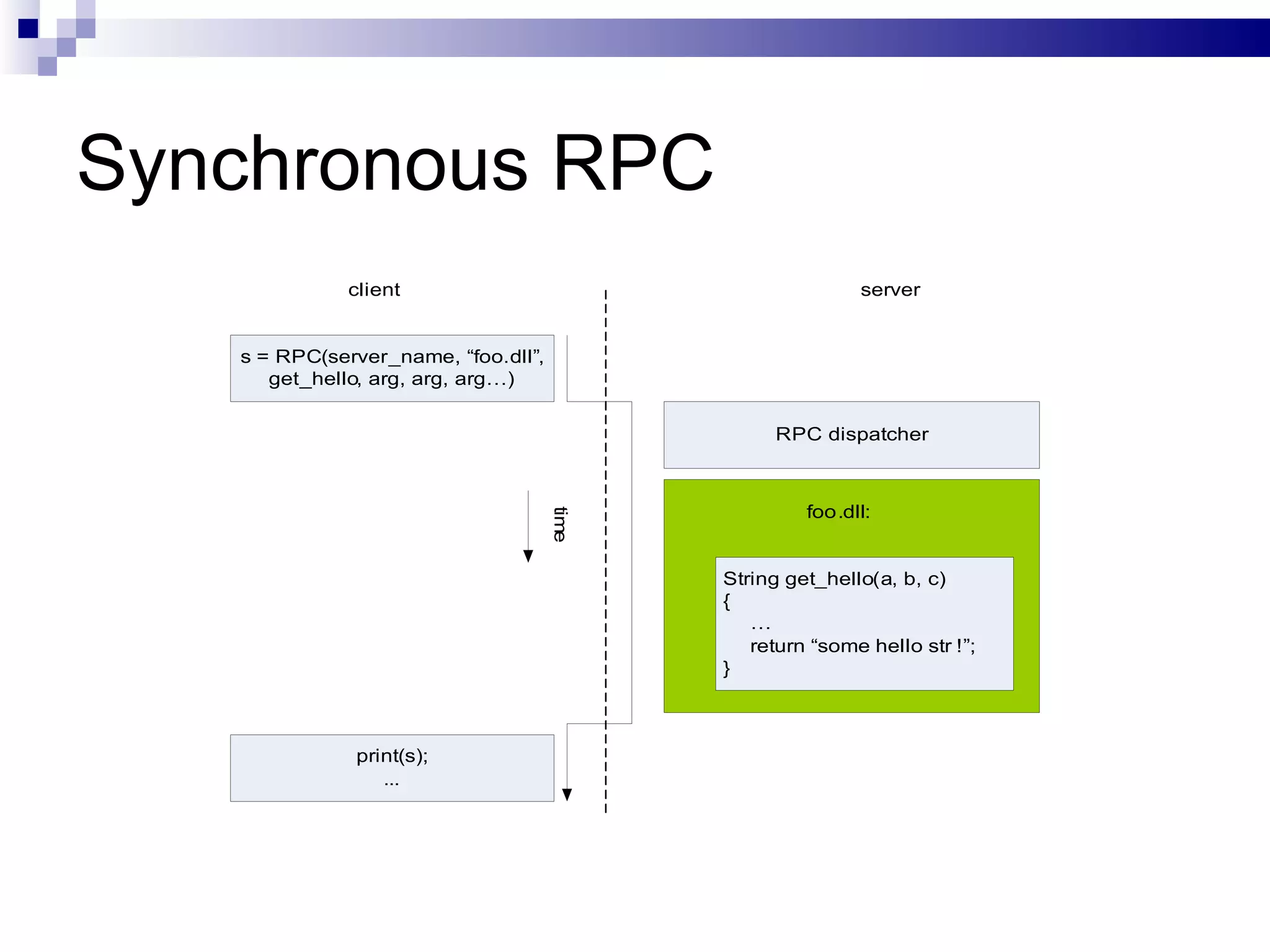
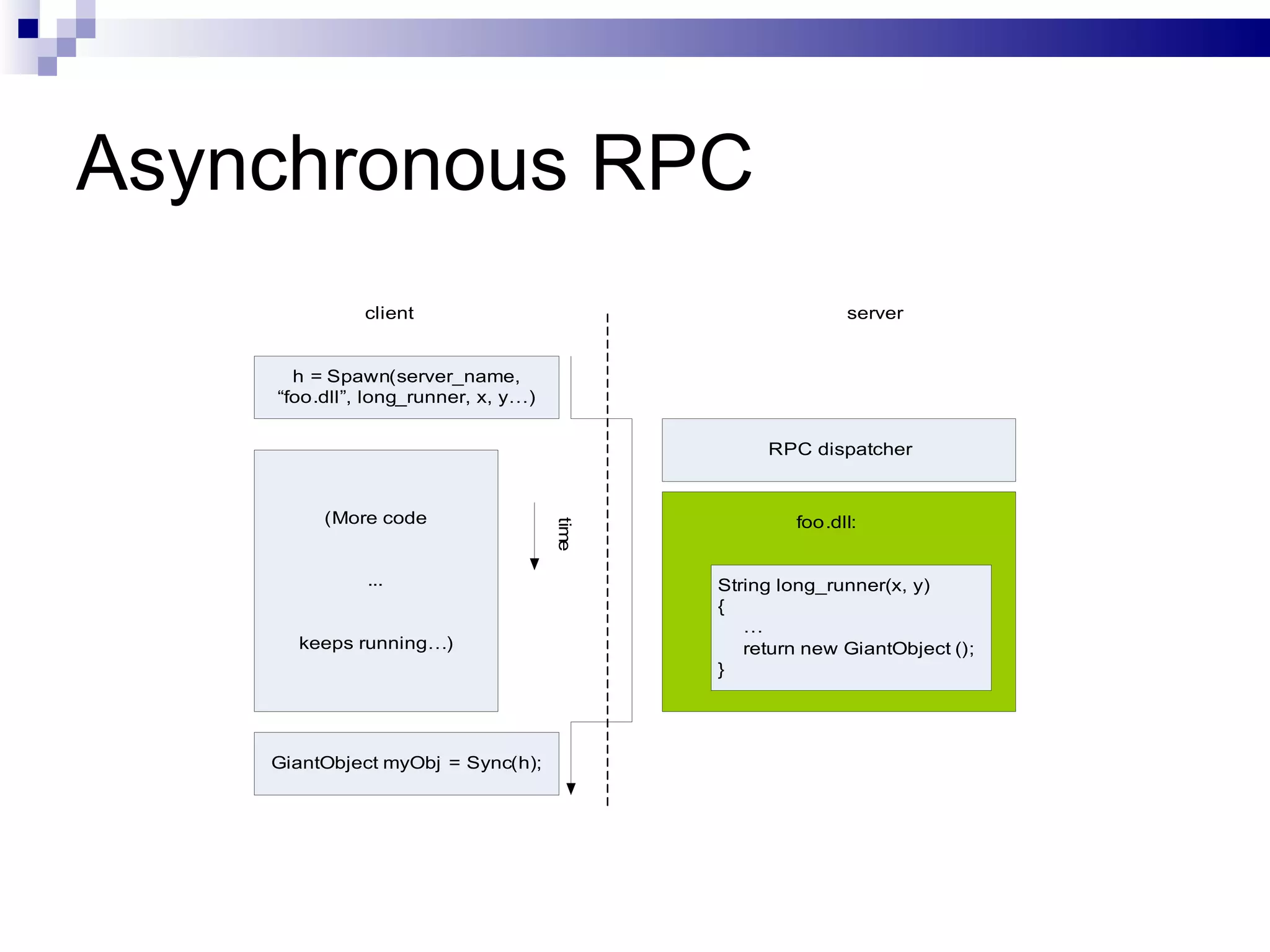
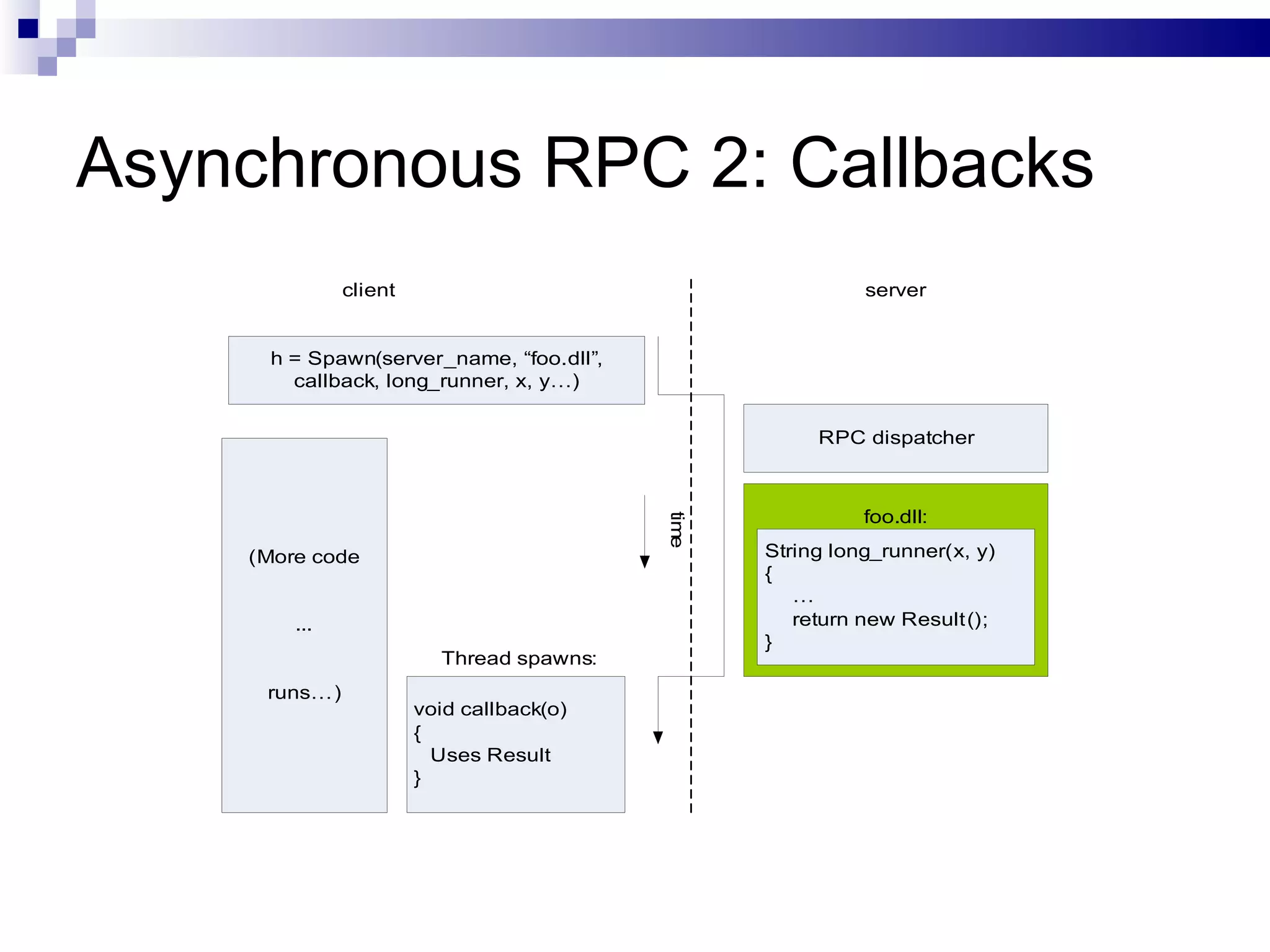
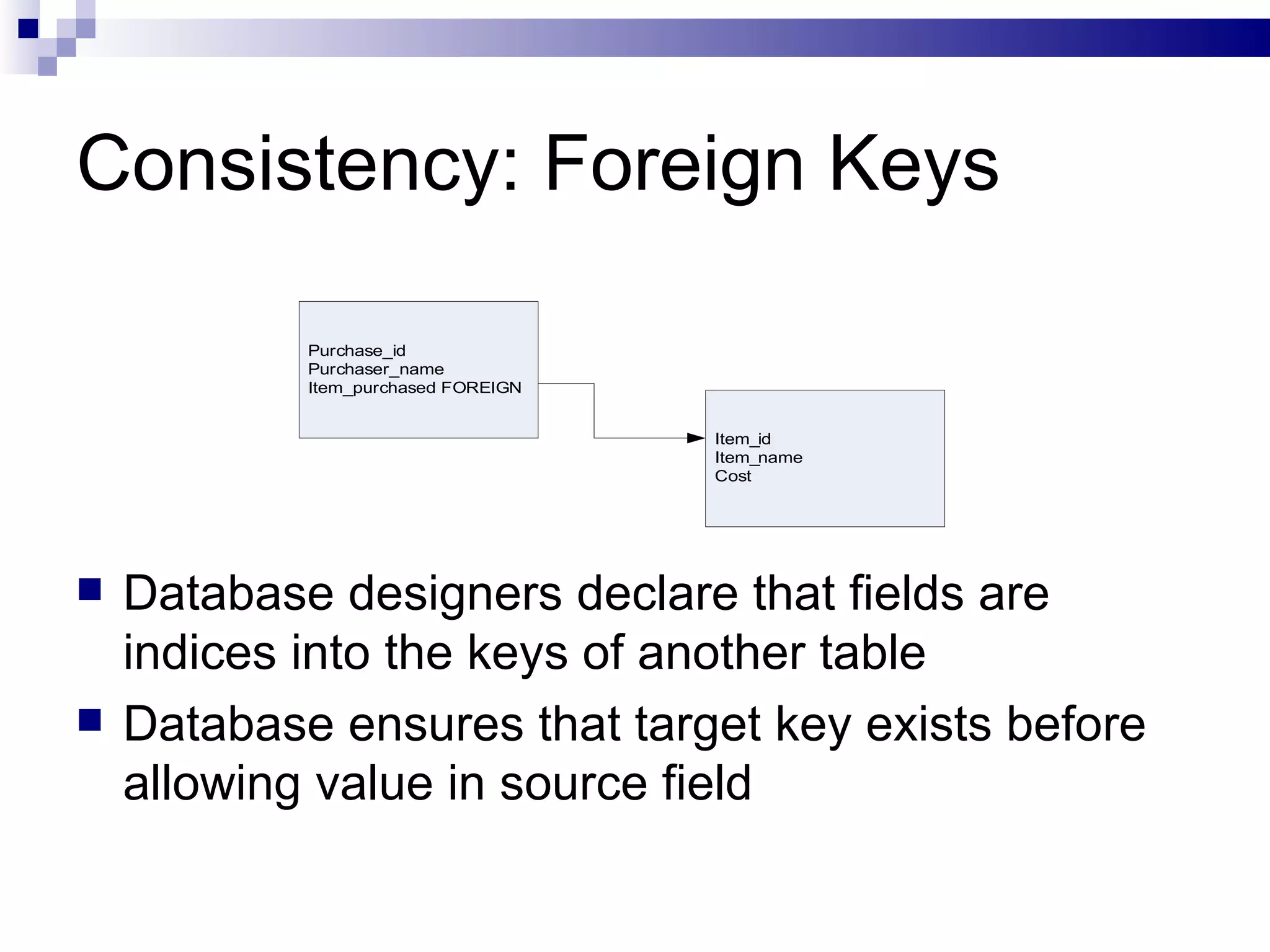
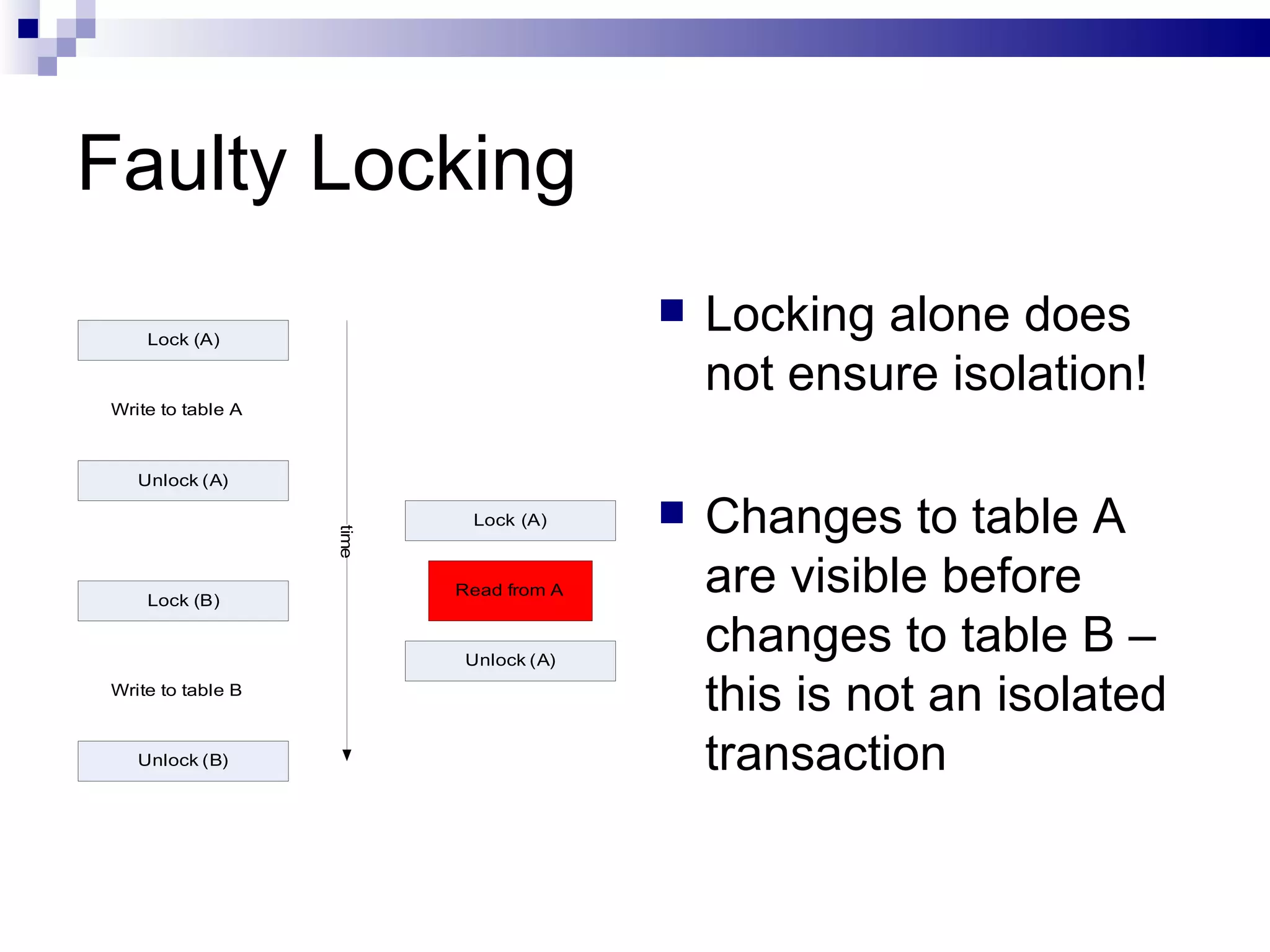
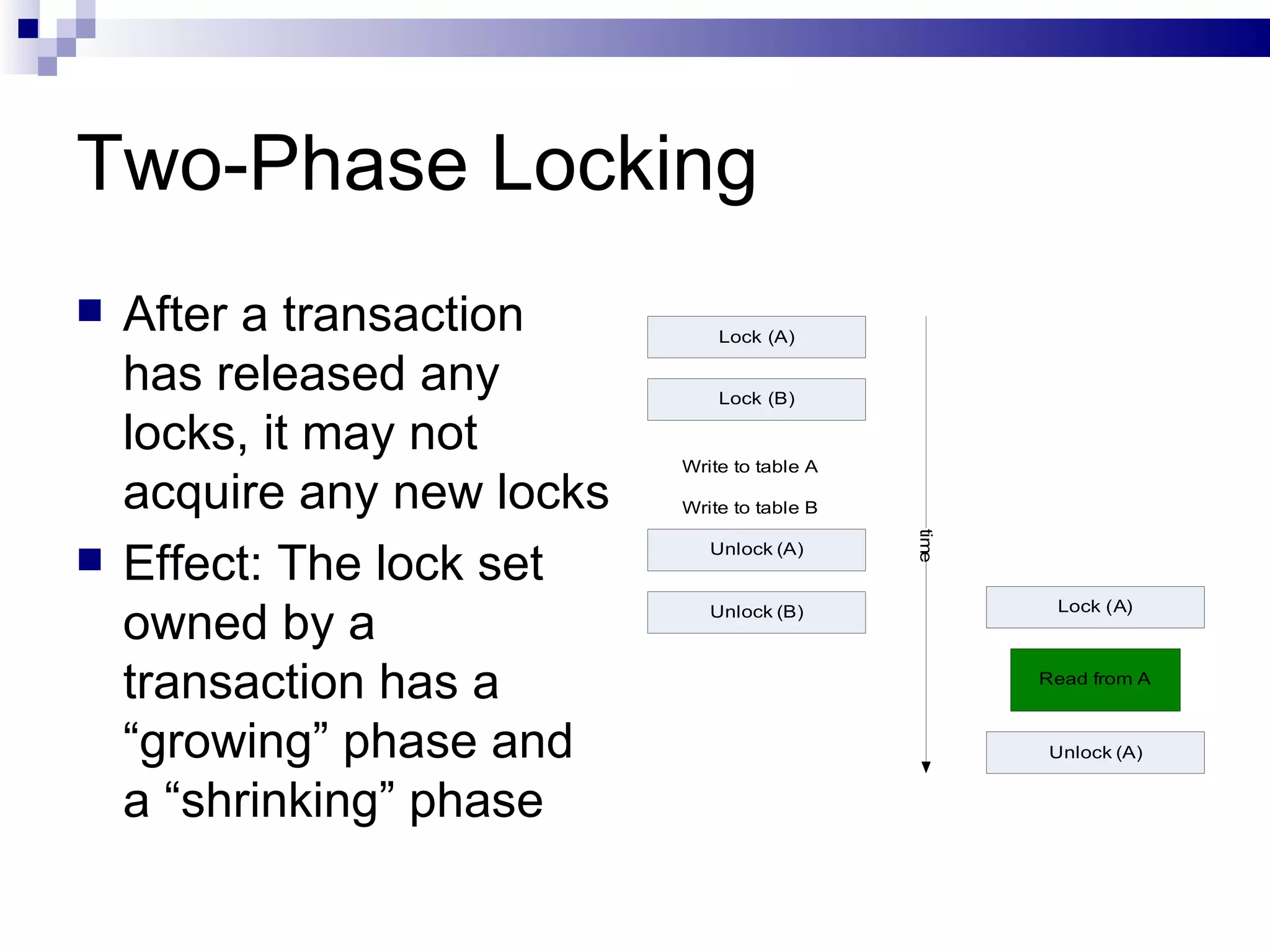
The document discusses key concepts in distributed systems including networking, remote procedure calls (RPC), and transaction processing systems (TPS). It covers networking fundamentals like sockets and ports. It describes how RPC works by allowing functions to be called remotely. It explains the ACID properties that TPS must support for atomicity, consistency, isolation, and durability of transactions processed across distributed systems.