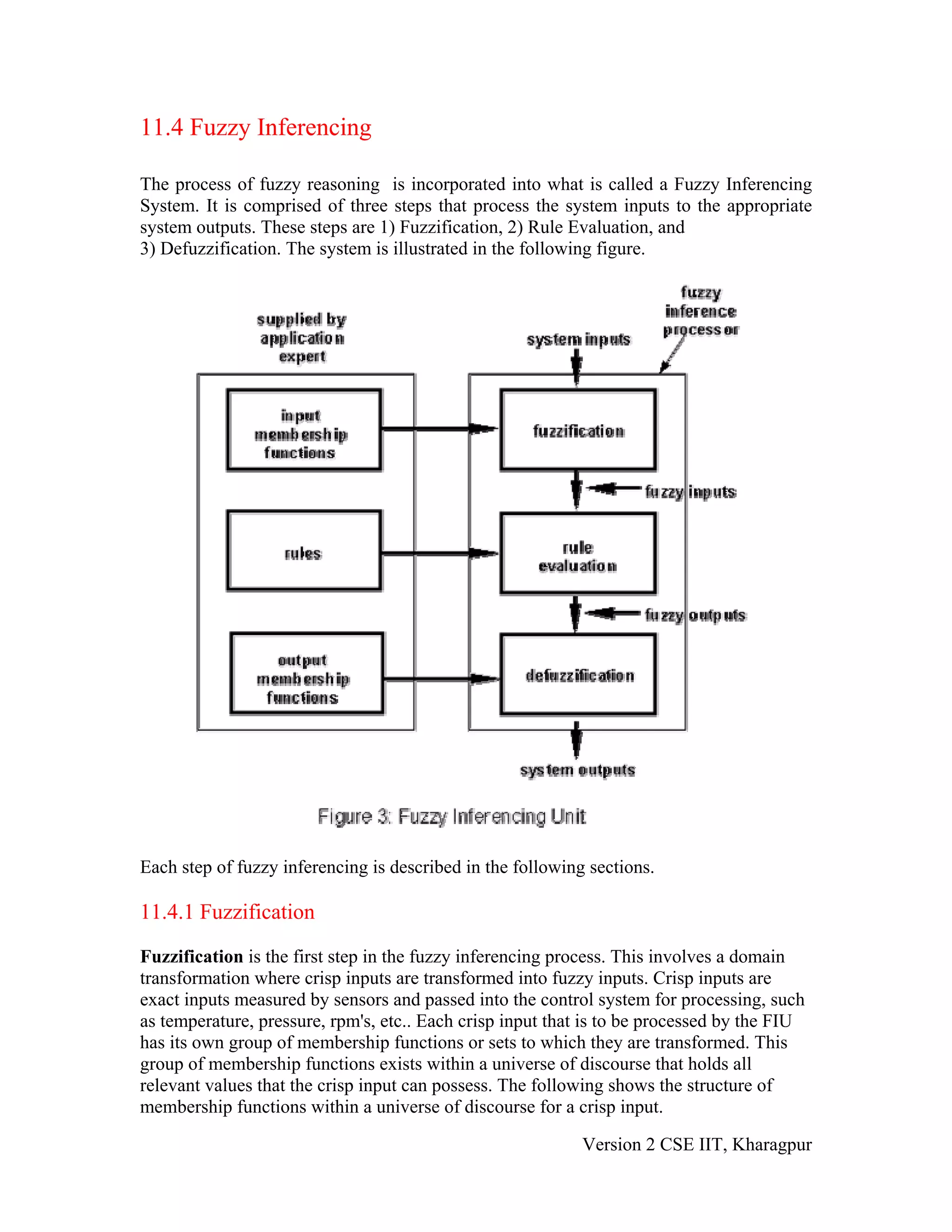
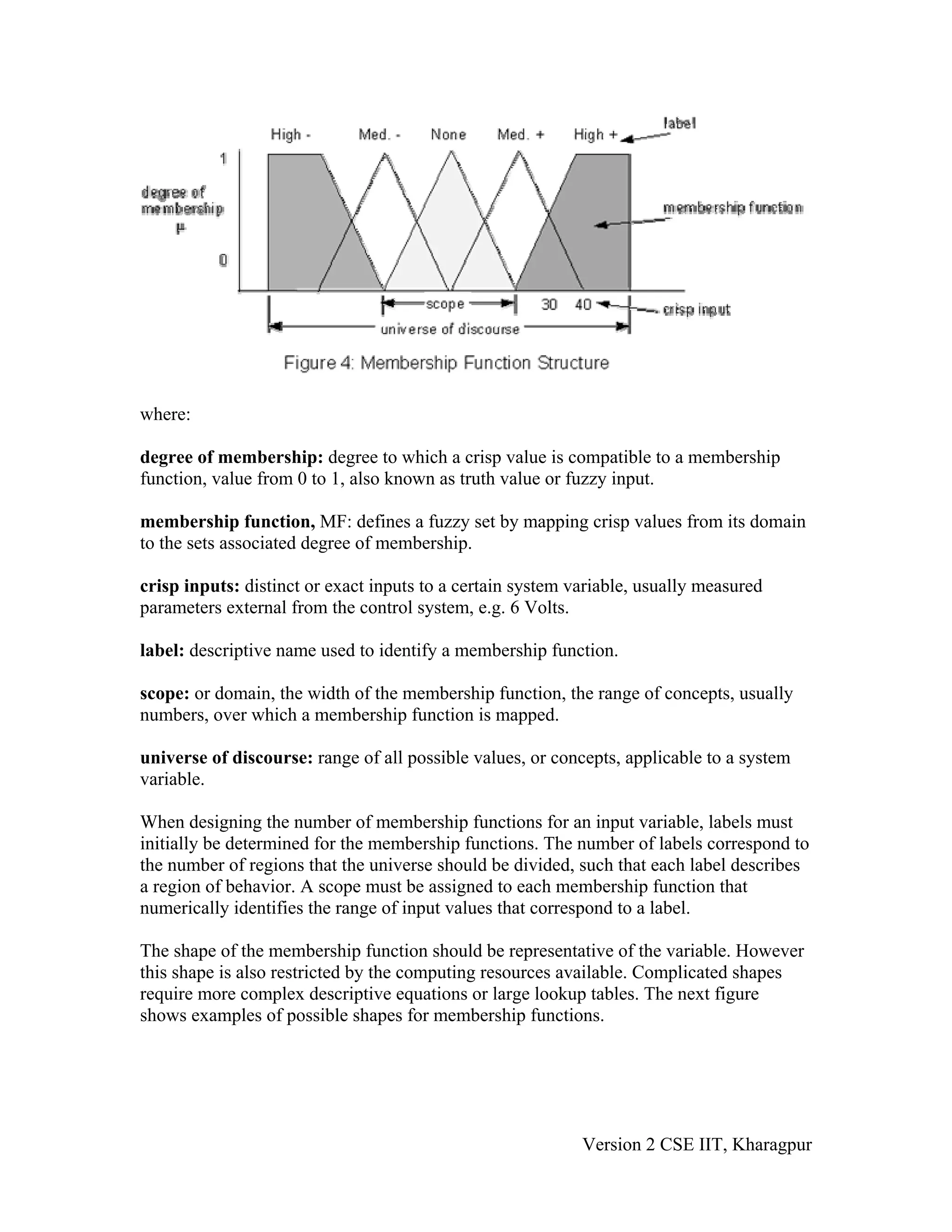
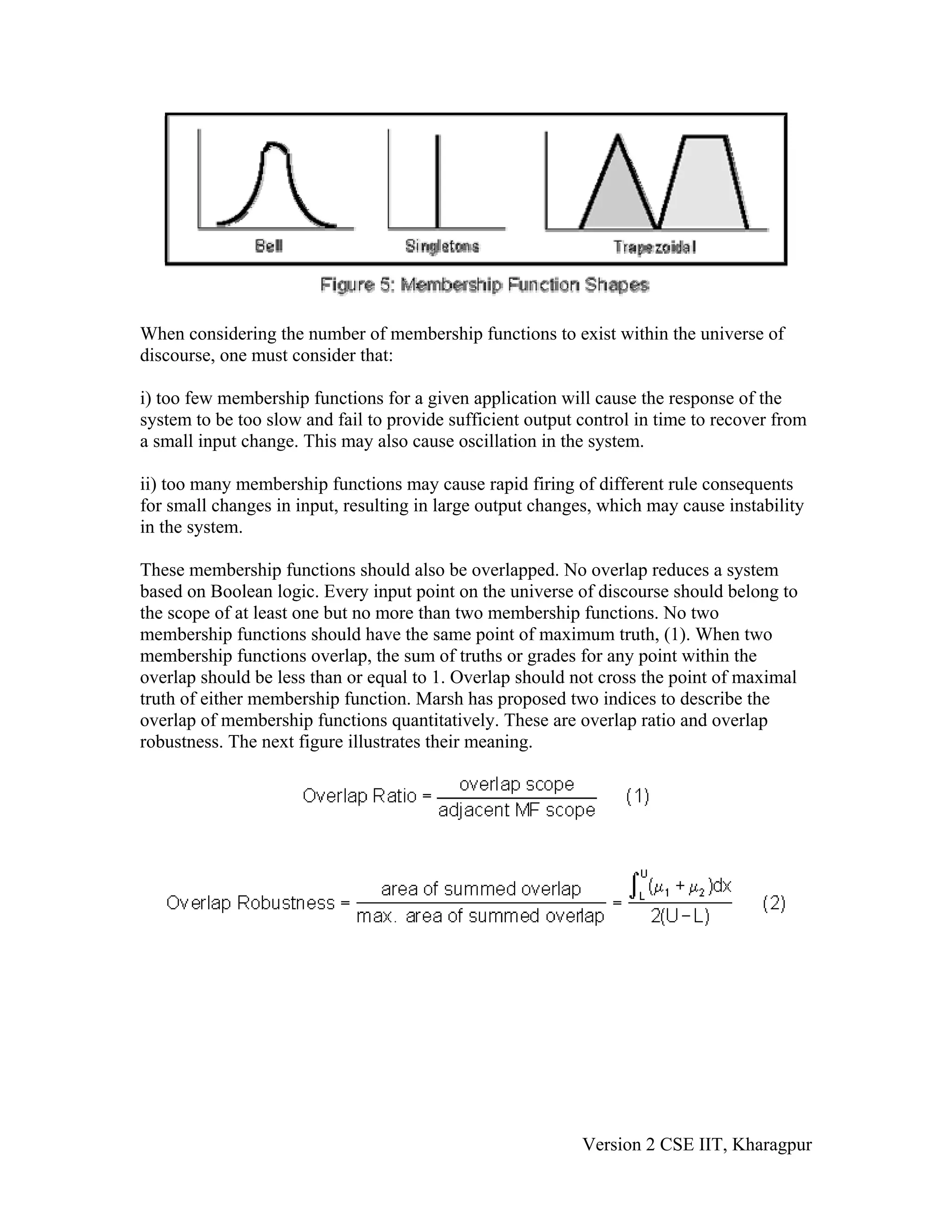
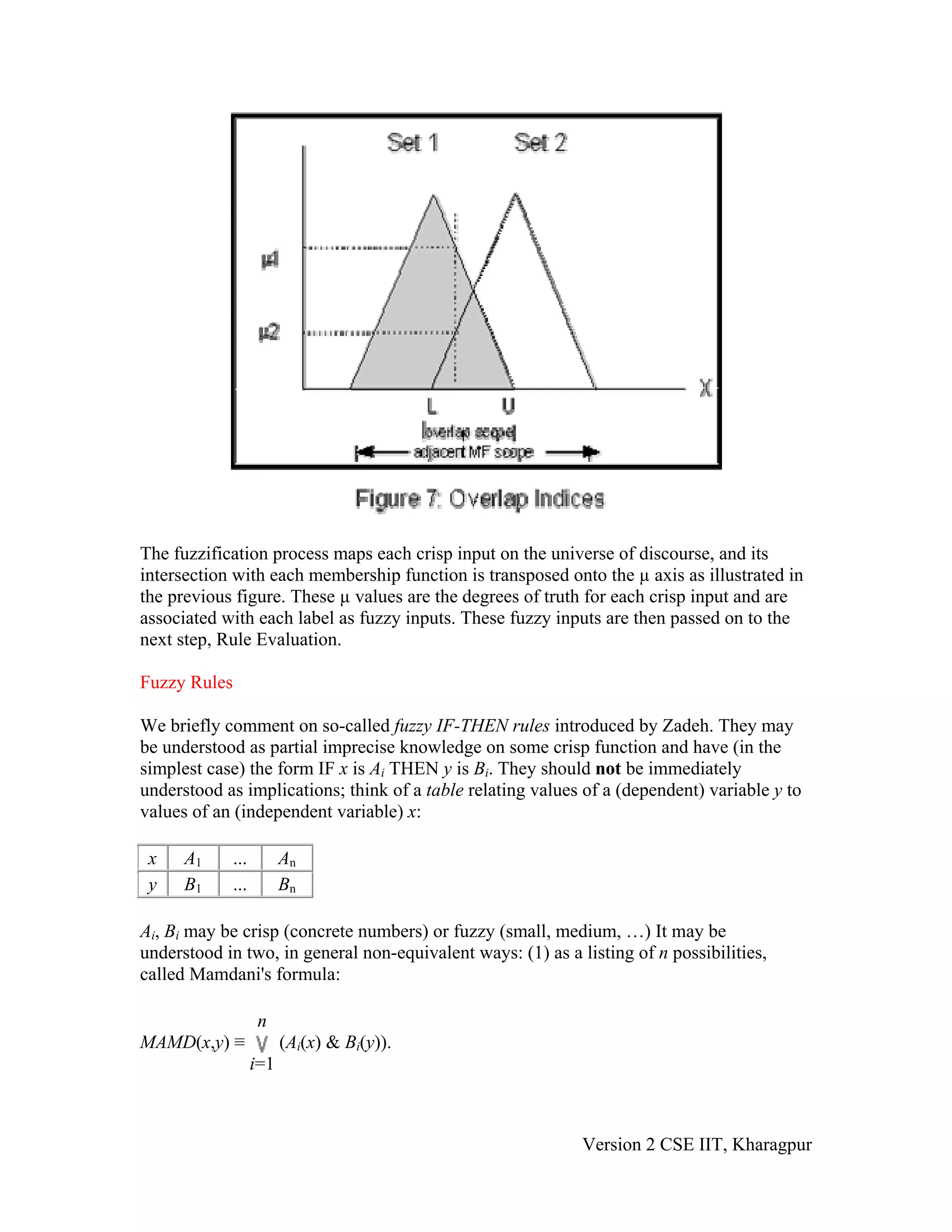
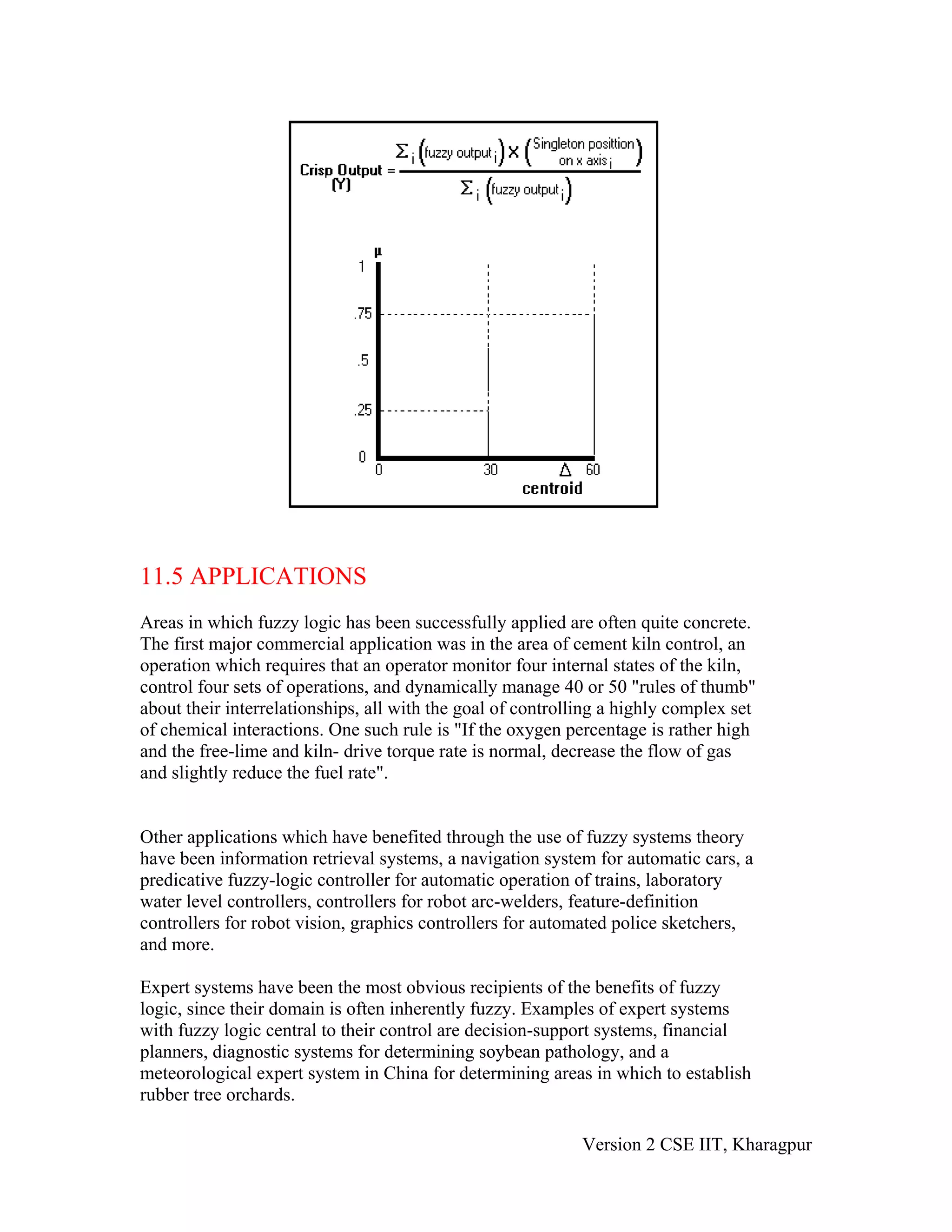
The document discusses fuzzy reasoning and fuzzy inferencing. It describes the three main steps in fuzzy inferencing: 1) fuzzification, which transforms crisp inputs into fuzzy inputs using membership functions, 2) rule evaluation using IF-THEN rules with fuzzy logic operators, and 3) defuzzification to produce crisp outputs from fuzzy outputs using methods like center of gravity. It provides examples of applications that have benefited from fuzzy systems like cement kiln control and expert systems. Finally, it presents some questions related to fuzzy logic concepts.