Java is a high-level programming language developed by James Gosling and his team at Sun Microsystems in the early 90s, originally intended for digital devices but evolving for internet use. It features ease of use, reliability, security, and platform independence, making it popular among developers. The document further explains Java comments, their importance for code readability, and highlights Java's case sensitivity and data type classifications.


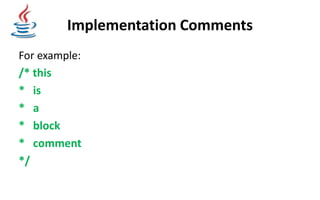
![Example Code with comment
/*This is my first program in java
* Another line here
*/
public static void main(String[] args)
{
System.out.println ("Hello World!");
}](https://image.slidesharecdn.com/learnjavatheorypresentation-181108015212/85/Learn-java-theory-presentation-21-320.jpg)