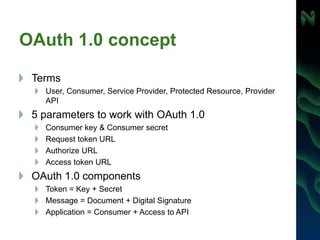
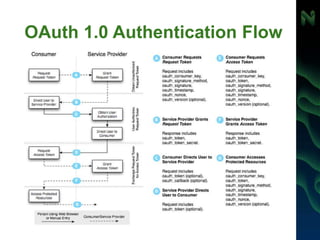
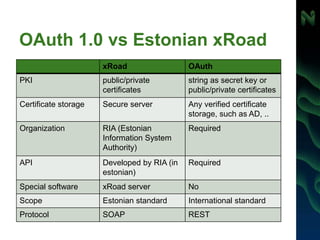
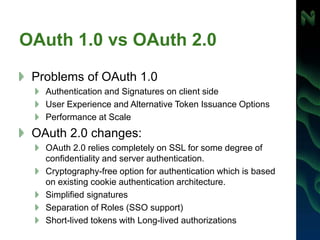
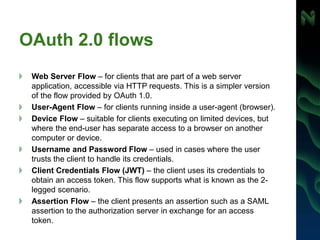
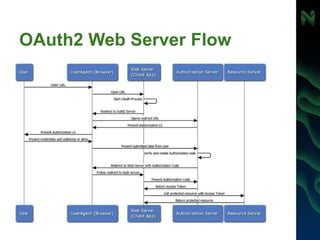
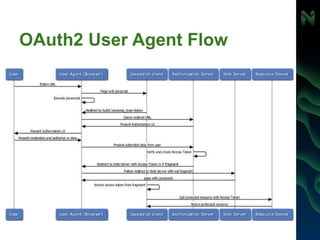
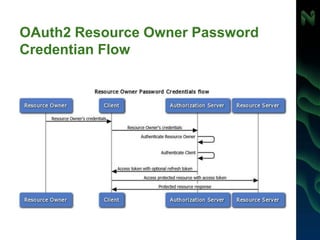
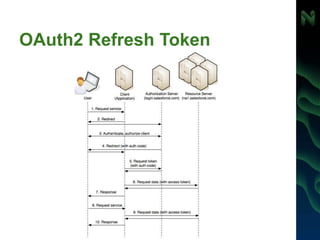
The document discusses various authentication and authorization methods for REST APIs, including API keys, signatures, OAuth 1.0, and OAuth 2.0. It provides details on implementing authentication with an API key, secret key, or signature for identity and authorization. The document contrasts OAuth 1.0 and 2.0, covering their concepts, authentication flows, and differences. It also discusses using OAuth for SSO, refreshing tokens, and consuming secured RSS/ATOM feeds, as well as validating state, data consistency, and enforcing authorization with REST services.

![HATEOAS
Data and links content separated one from another
Server may store allowed links and refuse all other
REST queries
A simple JSON presentation is traditionally rendered as:
{
"name" : "Alice"
}
A HATEOAS-based response would provide relevant links like this:
{
"name": "Alice",
"links": [ {
"rel": "self",
"href": "http://localhost:8080/customer/1"
} ]
}](https://image.slidesharecdn.com/spajarestsecurity-140527091501-phpapp02/85/Single-Page-Application-REST-security-40-320.jpg)
![HATEOAS and the PayPal REST Payment API
[
{
"href": "https://api.sandbox.paypal.com/v1/payments/payment/PAY-6RV70583SB702805EKEYSZ6Y",
"rel": "self",
"method": "GET"
},
{
"href": "https://www.sandbox.paypal.com/webscr?cmd=_express-checkout&token=EC-60U79048BN7719609",
"rel": "approval_url",
"method": "REDIRECT"
},
{
"href": "https://api.sandbox.paypal.com/v1/payments/payment/PAY-6RV70583SB702805EKEYSZ6Y/execute",
"rel": "execute",
"method": "POST"
}
]
https://developer.paypal.com/docs/integration/direct/paypal-
rest-payment-hateoas-links/](https://image.slidesharecdn.com/spajarestsecurity-140527091501-phpapp02/85/Single-Page-Application-REST-security-41-320.jpg)