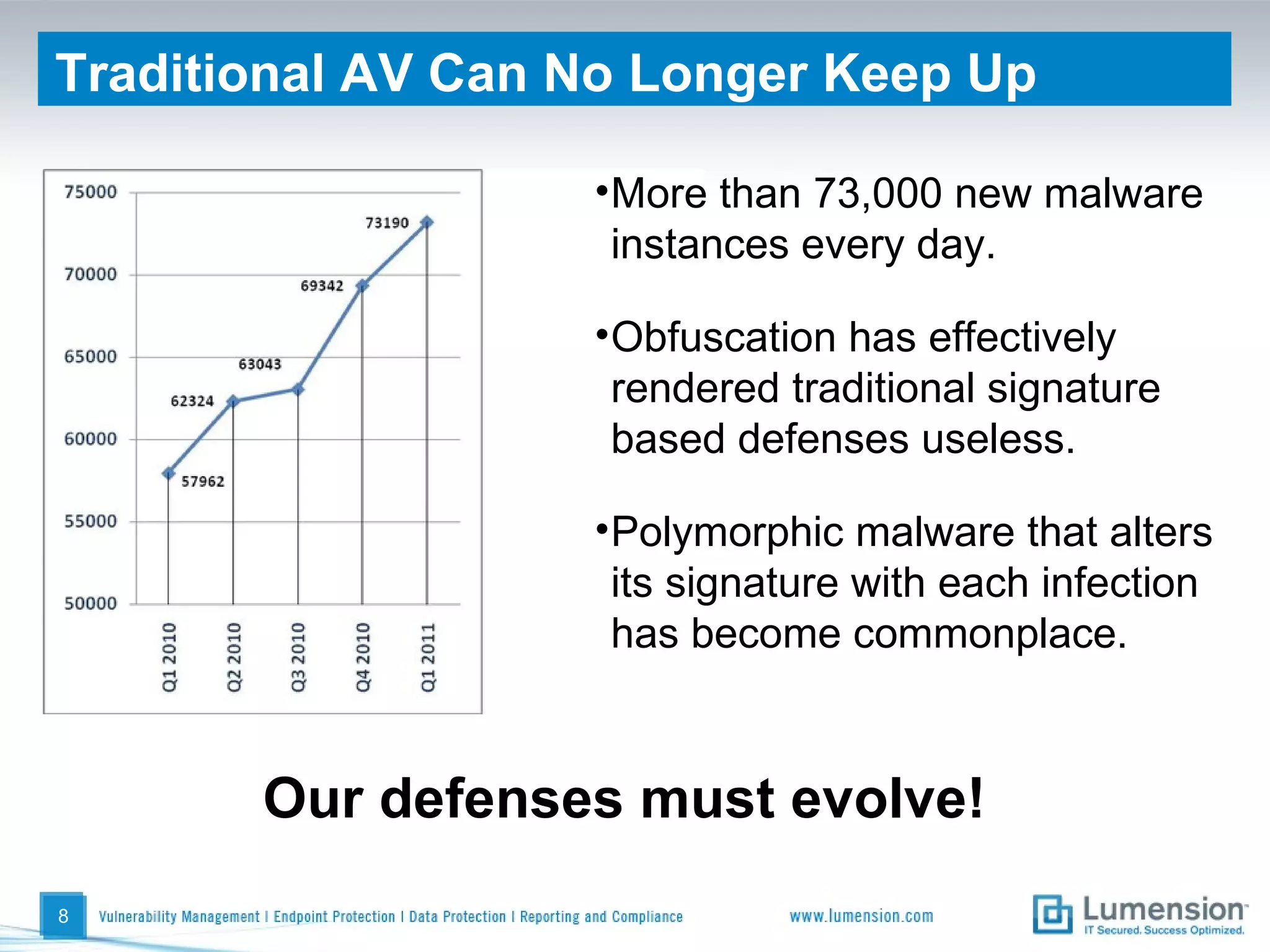
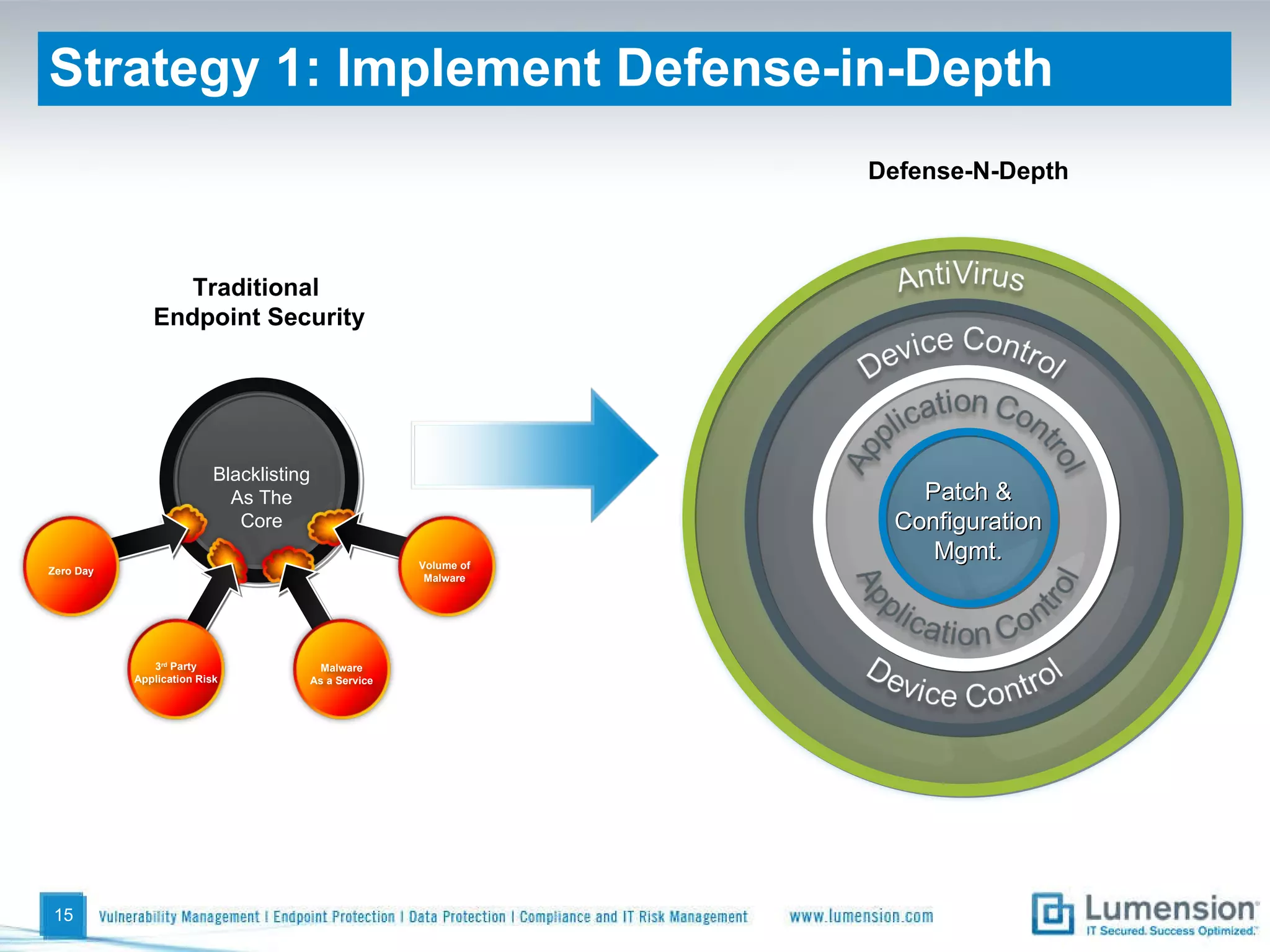
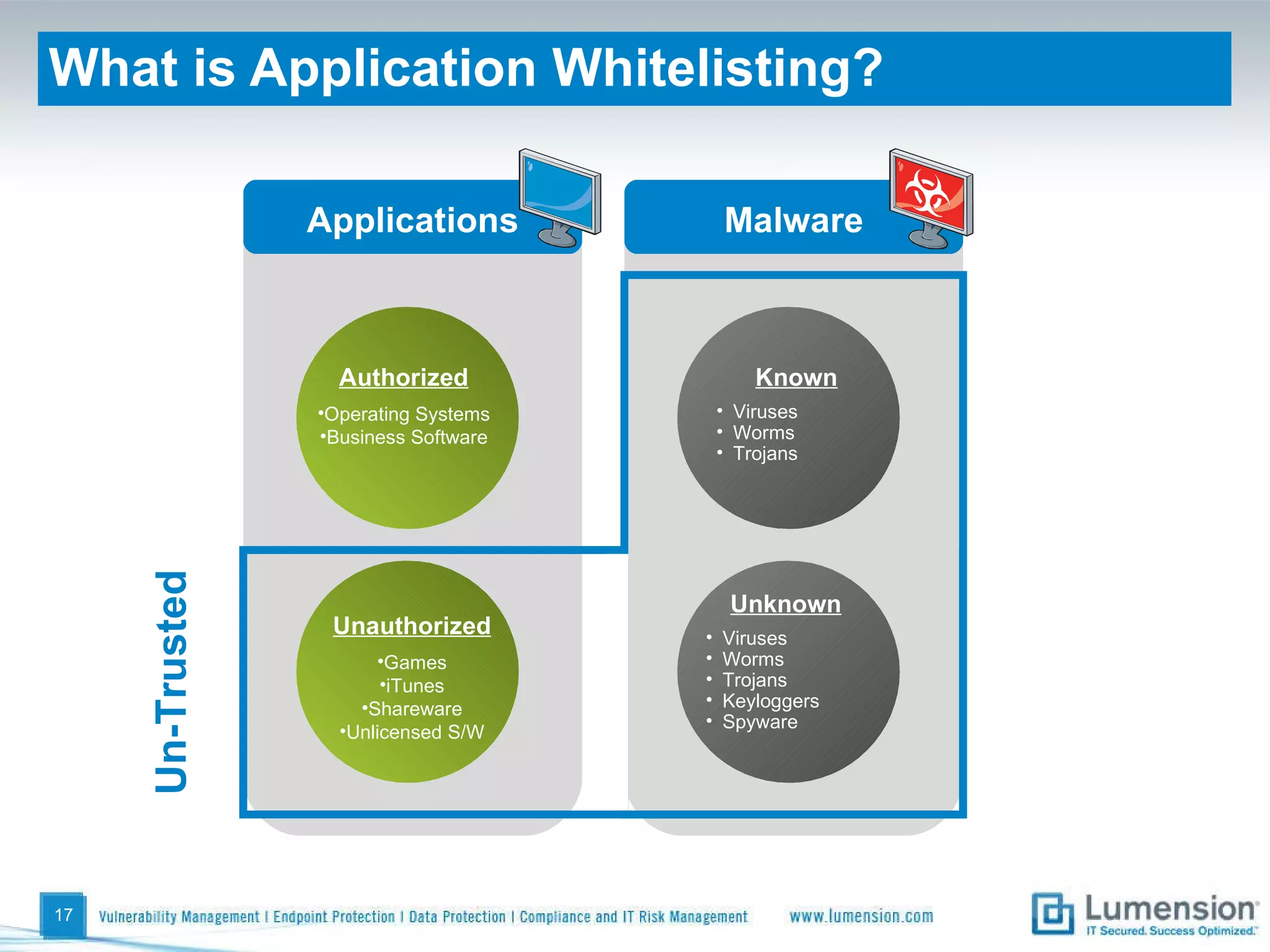
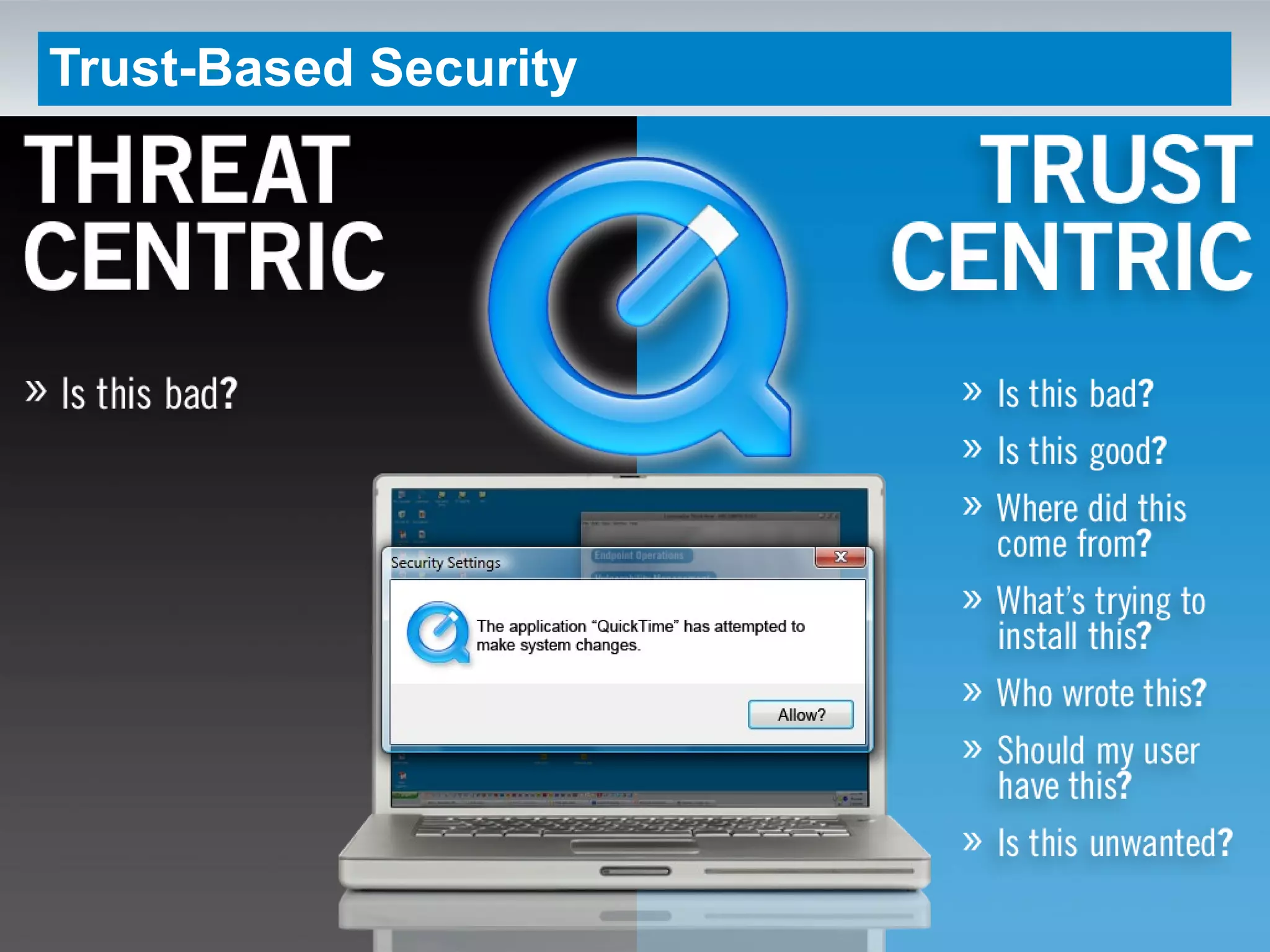
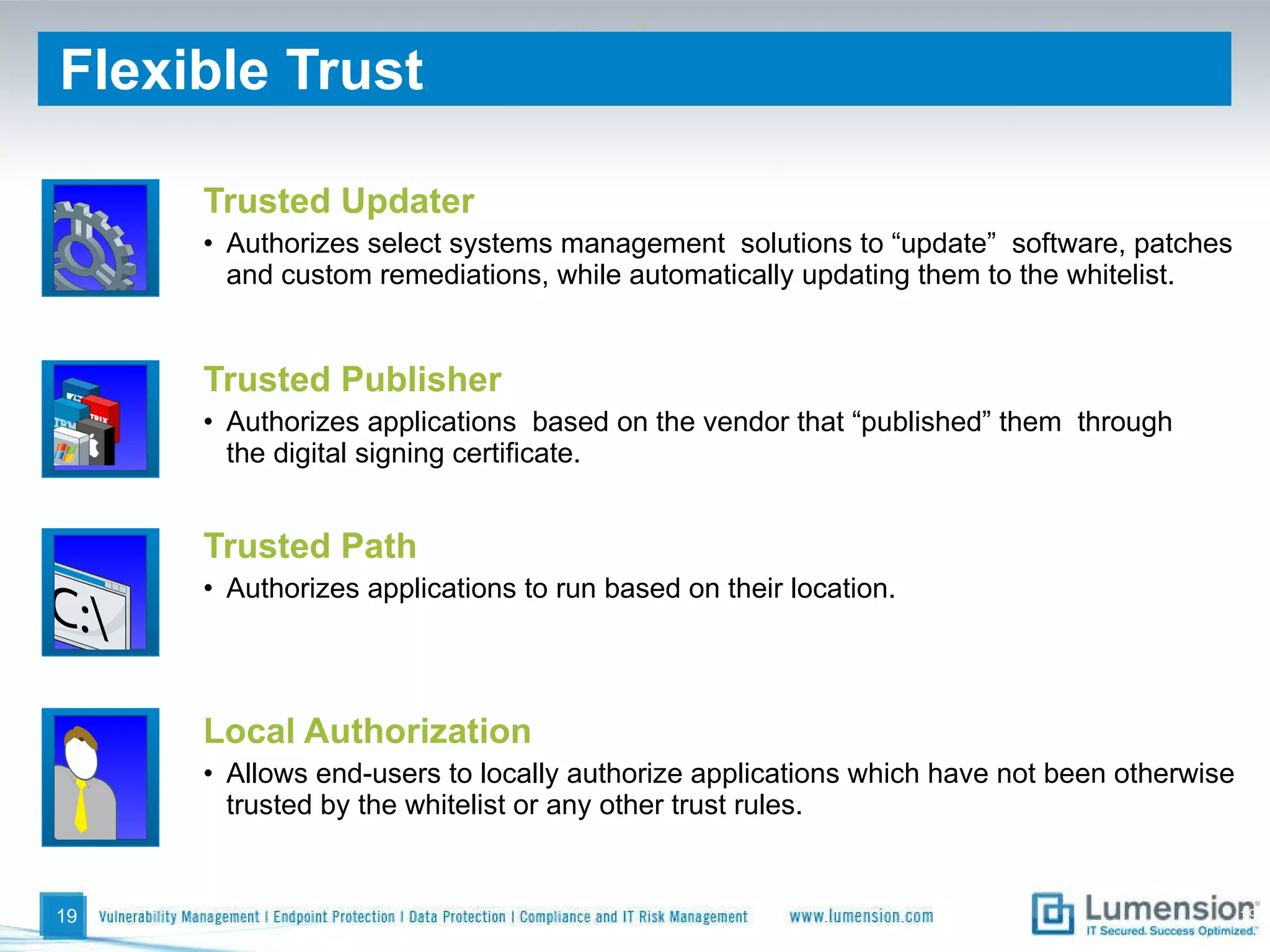
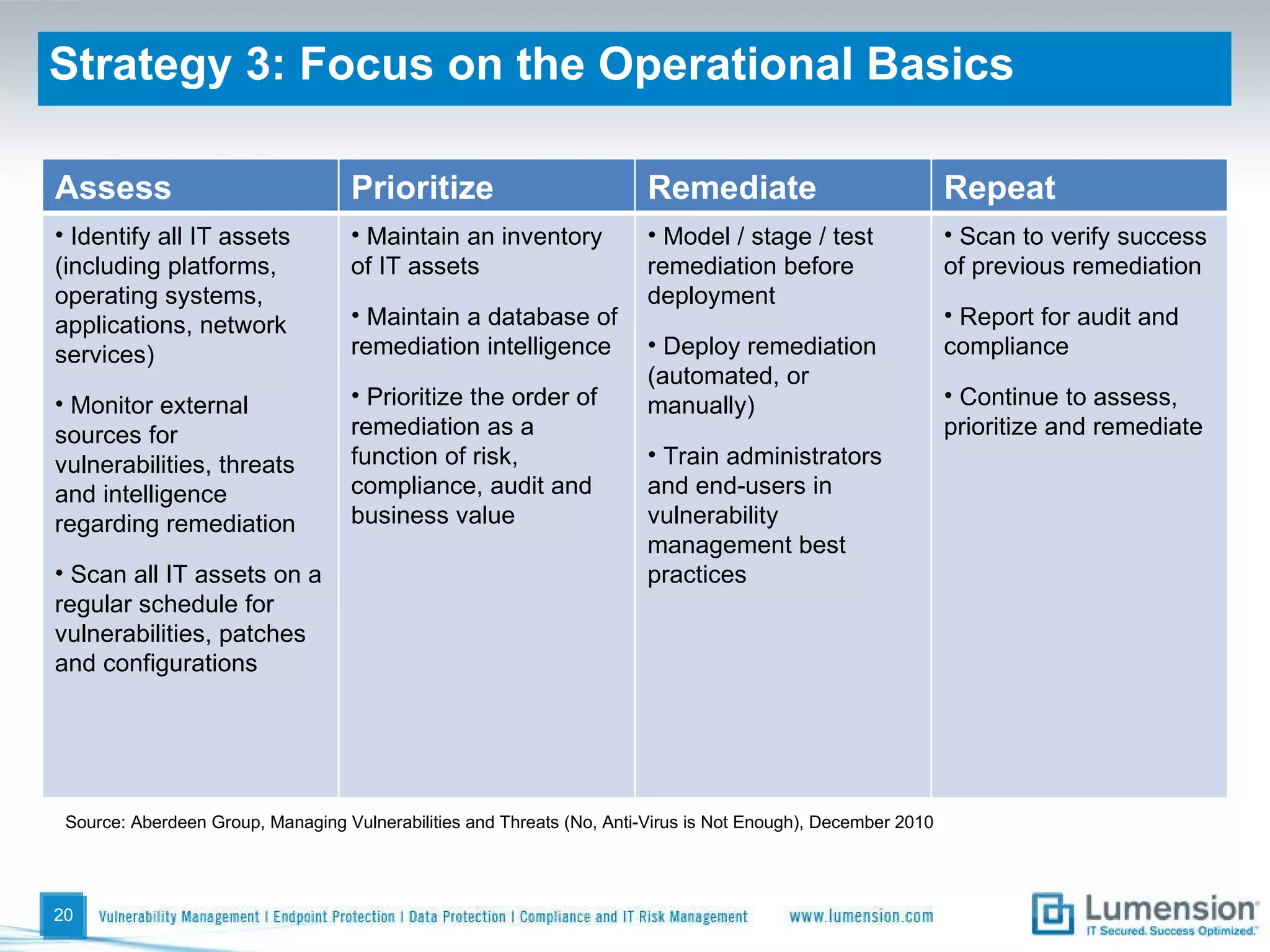
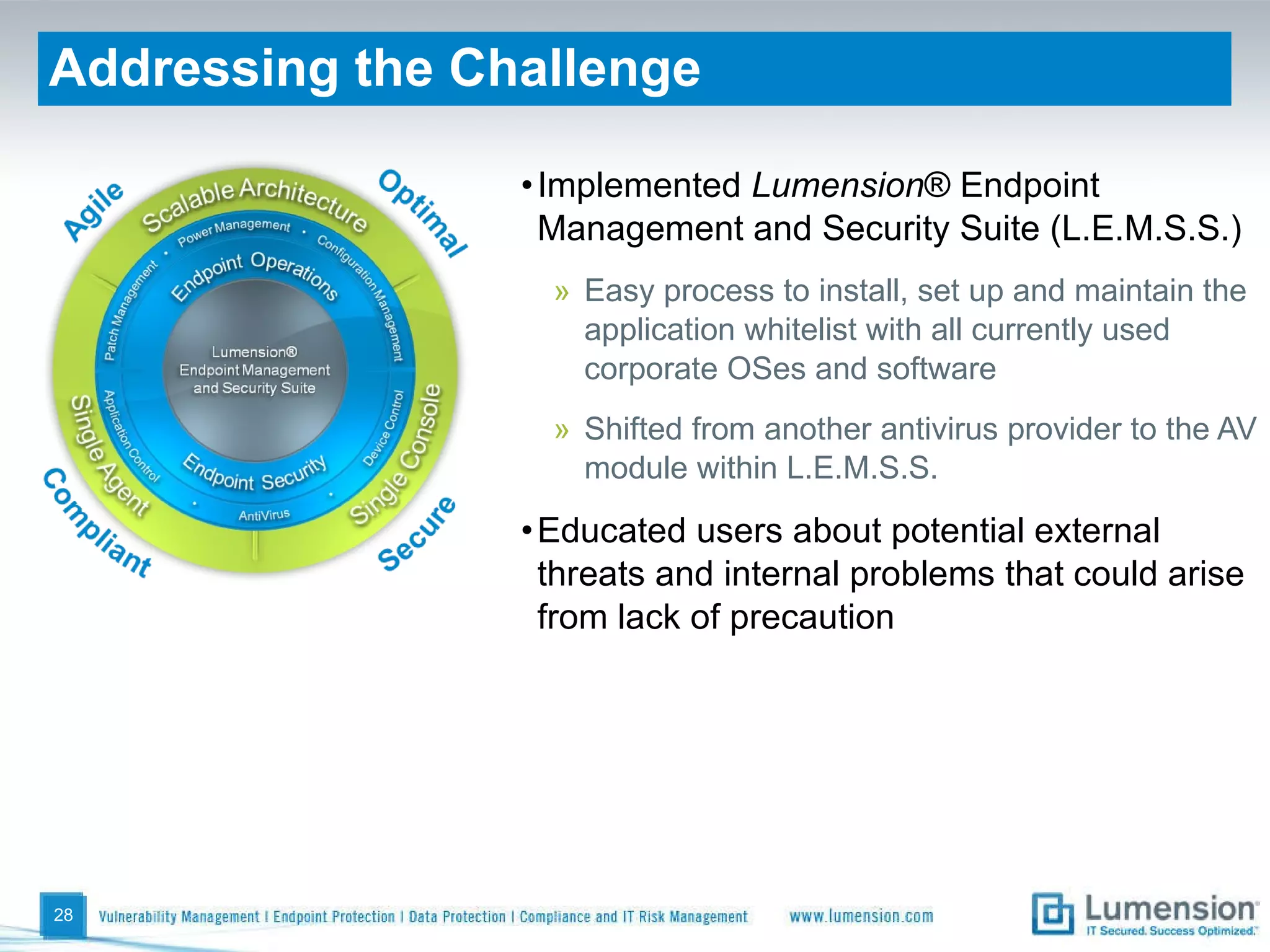
The document discusses challenges in modern endpoint security and strategies to address them. It outlines how attackers have changed their tactics to take advantage of outdated defenses. The key moves discussed to regain control include implementing defense-in-depth endpoint security, shifting to trust-based security focused on preventing execution rather than detection, focusing on operational basics like patching and asset management, and managing devices to limit local admin risks and unwanted applications. It also provides an example of how one company addressed their security issues by implementing the Lumension Endpoint Management and Security Suite.






![Global Headquarters 8660 East Hartford Drive Suite 300 Scottsdale, AZ 85255 1.888.725.7828 [email_address] http://blog.lumension.com](https://image.slidesharecdn.com/itsyourmoveendpointsecurityv4-110901124150-phpapp02/75/It-s-Your-Move-The-Changing-Game-of-Endpoint-Security-31-2048.jpg)