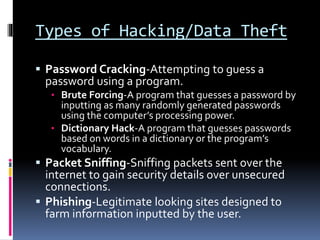
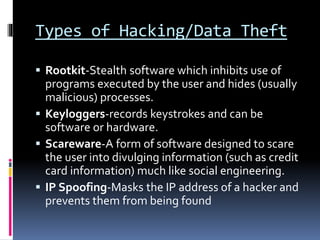
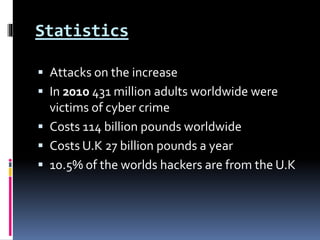
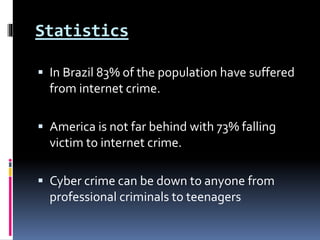
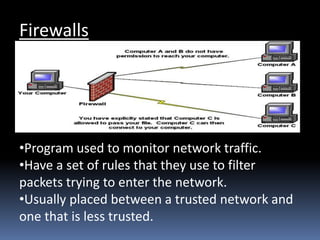
This document discusses types of malware like viruses, worms, and trojans, as well as different types of hacking such as password cracking, packet sniffing, and phishing. It describes black hat and white hat hackers, listing skills needed to prevent attacks like using antivirus software, firewalls, and encryption. Statistics show cybercrime is increasing and costs billions worldwide each year. The document provides examples of malware behaviors and outlines measures to enhance cybersecurity.