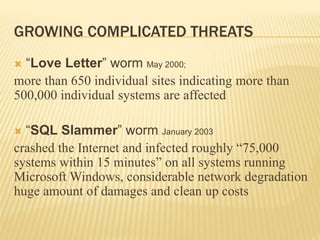
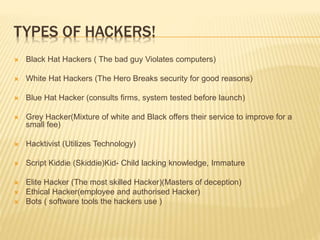
This document discusses internet security and hacking. It defines different types of hackers like black hat and white hat hackers. It also outlines common hacking methods like SQL injection, DDoS attacks, and social engineering. The document discusses types of malware like viruses, worms, and Trojan horses. It recommends security measures like using firewalls, antivirus software, and being cautious online. The conclusion suggests improving education on internet security and hiring more skilled cybersecurity professionals.