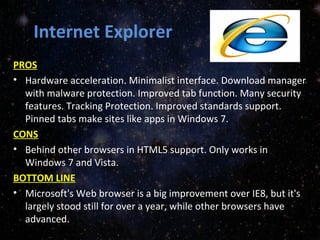
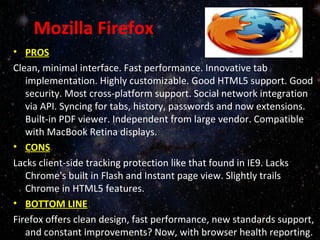
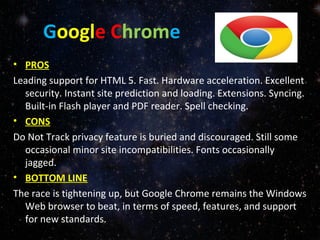
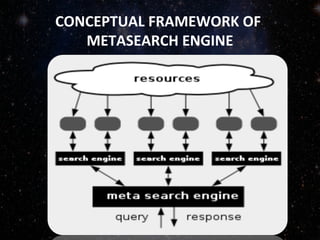
The document compares different internet browsers and search engines. It summarizes the key pros and cons of Internet Explorer, Firefox, and Google Chrome. It finds that the ideal browser depends on a user's preferences and needs. It also defines search engines and metasearch engines, describing their main components and functions. Search engines like Google, Yahoo and Bing are able to index web pages using spiders and return relevant results to user queries. Metasearch engines send search requests to multiple engines and aggregate the results into a single list.