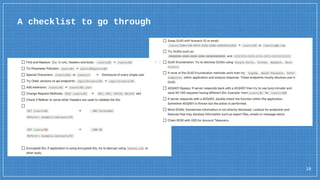
The document discusses Insecure Direct Object References (IDOR), a security vulnerability that allows attackers to access unauthorized data through predictable web objects. It explains how these vulnerabilities can arise when manipulating input parameters in web requests and highlights the importance of implementing proper access controls to prevent such exploits. Additionally, it touches on testing practices and provides examples of both compliant and non-compliant code related to access control issues.